The Linux kernel received a small but important fix for a scatterlist allocation error in the OMAP crypto driver that was tracked as CVE-2026-23222; the bug caused kmalloc_array() to allocate an array of pointers rather than an array of scatterlist objects, producing an allocation that was four times too small and risking memory corruption when the driver coerced data into the undersized buffer.
OMAP (Open Multimedia Applications Platform) silicon — the family of ARM-based SoCs historically produced by Texas Instruments — has long shipped platform-specific kernel drivers that expose hardware cryptographic accelerators to the kernel crypto API. Those drivers use scatter/gather lists (scatterlists) to map DMA-able pages for crypto engines that operate directly on memory fragments. When scatterlists are prepared and copied incorrectly, the result can be mis-sized buffers, out-of-bounds writes, kernel crashes, and in the worst case, exploitable memory corruption inside kernel context.
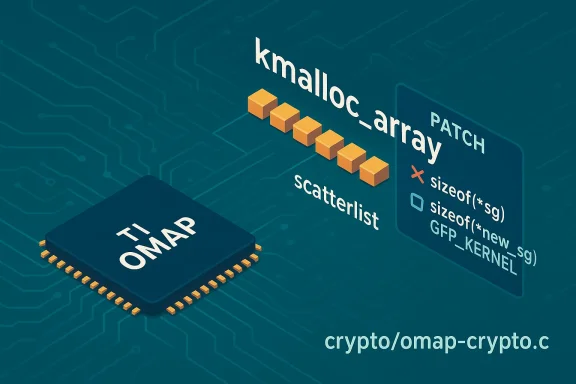
The recently disclosed CVE-2026-23222 is a textbook example of a subtle allocation mistake: the helper function omap_crypto_copy_sg_lists() used kmalloc_array(n, sizeof(sg), GFP_KERNEL) where it intended to allocate n entries of the scatterlist type pointed to by new_sg. In other words, the code allocated memory the size of n pointers instead of n scatterlist structures, yielding a buffer roughly 25% of the required size when scatterlist entries are full-sized. The upstream fix is to use sizeof(new_sg) with kmalloc_array so the allocation size matches the object type being stored.
This issue lives in the kernel’s crypto/omap code path and was patched in upstream trees; distribution and stable-tree patches were prepared and applied to multiple maintenance branches. Detection, mitigation, and quick patching are straightforward for most administrators — but this vulnerability still deserves careful treatment because it affects kernel code executed in privileged context and often runs on embedded and mobile platforms where updates are applied less frequently.
In omap_crypto_copy_sg_lists(), the code previously used sizeof(sg) where sg was declared as a pointer-to-pointer (struct scatterlist *sg) or otherwise referencing a different pointer type. The result: kmalloc_array allocated memory sized for n pointers rather than n struct scatterlist entries. That is a semantic mistake (wrong operand in sizeof) but has direct memory safety consequences: the subsequent code writes scatterlist entries into a buffer that is too small. The upstream correction replaces the wrong sizeof expression with sizeof(new_sg), making the allocation match the actual object type. The code change is intentionally minimal and surgical — a one-line fix that resolves the root cause.
This CVE is not a magical remote RCE vector on its own — its exploitability depends on the ability to exercise the omap crypto code path with attacker-controlled scatterlists and to arrange kernel memory in a way that an overflow can be turned into an advantage. Nevertheless, the kernel is sensitive territory: allocation mistakes should be fixed promptly and conservatively, even when the path to a practical exploit appears complex.
Because the OMAP crypto driver is platform-specific, exposure is concentrated on systems that actually include and load the OMAP crypto driver: embedded builds, older TI-based platforms, certain Android device kernels, and specialized appliances that rely on OMAP hardware. Mainline server distributions running on x86 or modern ARM platforms that do not include OMAP drivers are unaffected in practice. That said, the Linux kernel’s inclusion in many product stacks means operators should verify whether their deployed kernels contain the vulnerable code path and whether the corresponding drand loaded. The forum’s ongoing security tracking shows many kernel CVEs and corresponding patches across trees, and administrators should treat this one as part of regular kernel hardening and patch management hygiene.
This vulnerabilirecurring lessons for kernel and embedded system teams:
In short: CVE-2026-23222 is a correctable and low-risk-to-patch kernel bug that warrants prompt attention from operators of OMAP-based systems. Apply vendor-supplied kernel updates or backport the one-line fix to eliminate the undersized scatterlist allocation, validate the change on representative hardware, and monitor device logs to ensure the problem is resolved.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
OMAP (Open Multimedia Applications Platform) silicon — the family of ARM-based SoCs historically produced by Texas Instruments — has long shipped platform-specific kernel drivers that expose hardware cryptographic accelerators to the kernel crypto API. Those drivers use scatter/gather lists (scatterlists) to map DMA-able pages for crypto engines that operate directly on memory fragments. When scatterlists are prepared and copied incorrectly, the result can be mis-sized buffers, out-of-bounds writes, kernel crashes, and in the worst case, exploitable memory corruption inside kernel context.The recently disclosed CVE-2026-23222 is a textbook example of a subtle allocation mistake: the helper function omap_crypto_copy_sg_lists() used kmalloc_array(n, sizeof(sg), GFP_KERNEL) where it intended to allocate n entries of the scatterlist type pointed to by new_sg. In other words, the code allocated memory the size of n pointers instead of n scatterlist structures, yielding a buffer roughly 25% of the required size when scatterlist entries are full-sized. The upstream fix is to use sizeof(new_sg) with kmalloc_array so the allocation size matches the object type being stored.
This issue lives in the kernel’s crypto/omap code path and was patched in upstream trees; distribution and stable-tree patches were prepared and applied to multiple maintenance branches. Detection, mitigation, and quick patching are straightforward for most administrators — but this vulnerability still deserves careful treatment because it affects kernel code executed in privileged context and often runs on embedded and mobile platforms where updates are applied less frequently.
What exactly was wrong (technical detail)
Scatterlists, kmalloc_array, and the off-by-type allocation
Scatterlists are the kernel’s canonical representation for noncontiguous I/O pages. A scatterlist entry (struct scatterlist) contains page, offset and length metadata; arrays of such structures represent full I/O buffers. The typical idiom to allocate an array in kernel code is kmalloc_array(n, sizeof(array), GFP_KERNEL) — so the element size is taken from the dereferenced pointer that will be used to store elements.In omap_crypto_copy_sg_lists(), the code previously used sizeof(sg) where sg was declared as a pointer-to-pointer (struct scatterlist *sg) or otherwise referencing a different pointer type. The result: kmalloc_array allocated memory sized for n pointers rather than n struct scatterlist entries. That is a semantic mistake (wrong operand in sizeof) but has direct memory safety consequences: the subsequent code writes scatterlist entries into a buffer that is too small. The upstream correction replaces the wrong sizeof expression with sizeof(new_sg), making the allocation match the actual object type. The code change is intentionally minimal and surgical — a one-line fix that resolves the root cause.
Why sizeof mistakes are dangerous in kernel code
In user space, heap overflows may be somewhat contained by process isolation. In kernel space, the stakes are higher: a write past an allocation can corrupt kernel data structures, overwrite function pointers or metadata, and cause immediate system instability (panic/oops) or, in the worst case, become a vector for privilege escalation if an attacker can carefully craft the memory layout.This CVE is not a magical remote RCE vector on its own — its exploitability depends on the ability to exercise the omap crypto code path with attacker-controlled scatterlists and to arrange kernel memory in a way that an overflow can be turned into an advantage. Nevertheless, the kernel is sensitive territory: allocation mistakes should be fixed promptly and conservatively, even when the path to a practical exploit appears complex.
Scope and affected platforms
OpenCVE and other vulnerability trackers list the issue as a Linux kernel flaw in the crypto: omap subsystem and note the upstream patches and stable-tree backports. The fix was applied to multiple stable branches and to upstream kernels; distributions that ship the affected OMAP drivers in their kernels should pick up the stable backport or a distribution-specific kernel update.Because the OMAP crypto driver is platform-specific, exposure is concentrated on systems that actually include and load the OMAP crypto driver: embedded builds, older TI-based platforms, certain Android device kernels, and specialized appliances that rely on OMAP hardware. Mainline server distributions running on x86 or modern ARM platforms that do not include OMAP drivers are unaffected in practice. That said, the Linux kernel’s inclusion in many product stacks means operators should verify whether their deployed kernels contain the vulnerable code path and whether the corresponding drand loaded. The forum’s ongoing security tracking shows many kernel CVEs and corresponding patches across trees, and administrators should treat this one as part of regular kernel hardening and patch management hygiene.
Patch, disclosure timeline and provenance
- The upstream commit that corrected the allocation idiom was authored by Kees Cook and was included in stable and upstream trees; Greg Kroah-Hartman shepherded the stable backport. The patch message explicitly states the root cause and the corrected sizeof use. The change is minimal and was accepted into stable branches.
- Public vulnerability trackers such as OpenCVE and PT Security (dbugs) have summarized the fix and its implications; those pages describe the allocation error and list the kernel versions or commit hashes that indicate the patched-versus-unpatched boundary. When CVE pages do not yet publish CVSS scores, assume maintainers prioritized a rapid, minimal fix over a long public discussion about severity and ratings.
- The stable-tree backport and the commit metadata include fix tags such as “Fixes: 74ed87e7e7f7 (crypto: omap - add base support library for common routines)”, which helps maintainers identify which historical change introduced the regression. That in turn simplifies cherry-picking fixes into specific long-term maintenance branches.
Realistic impact and attack surface
It helps to separate three questions when assessing real-world impact:- Is the flaw a remote, easily chainable exploit?
No — the defect is a local kernel memory issue in a platform-specific driver. Exploitation requires interacting with the OMAP crypto code path and often requires local or privileged access to supply scatterlist inputs that trigger the flawed allocation and subsequent writes. - Can the bug cause high-impact system failures (availability)?
Yes — at minimum the bug can cause deterministic kernel panics (oops) and instability when the driver writes past the undersized allocation. That makes this a clear availability risk for affected devices. - Could it realistically be turned into a privilege-escalation or information-disclosure exploit?
Possible but non-trivial. Kernel memory corruption primitives are powerful, yet converting a scatterlist allocation overflow into an arbitrary write or controlled corruption typically requires favorable heap layout and other preconditions. On some embedded devices with predictable memory layouts, determined attackers — especially those with local code execution or access to native apps and drivers — could attempt to leverage the bug. Given the privileged nature of kernel vulnerabilities, administrators should not treat exploitability as hypothetical; instead, they should apply the fix quickly. PT Security’s dbugs entry and OpenCVE correctly refrain from definitive exploitability judgments and instead document the technical fix.
How to determine if you are affected
Use the following checklist to confirm exposure and prioritize remediation:- Kernel version and branch: check your running kernel’s version string (uname -r). The upstream notes and stable-tree messages list the fixed commits and the minimum patched versions; Cross-reference those commits against your distribution’s kernel changelog. OpenCVE reports which stable branches include the fix.
- Module presence: verify whether the OMAP crypto driver is built into your kernel or available as a loadable module. On a running system:
- Run: 1.) uname -r 2.) lsmod | grep omap 3.) zgrep -i omap /proc/config.gz (if kernel config is available)
If the driver is not built or loaded, your attack surface is significantly smaller. - Device fleet profile: identify any devices in your inventory that use TI OMAP SoCs. Embedded appliances, older Android phones, and legacy industrial devices are the most likely places to find the driver.
- Dmesg and logs: watch for panic/oops logs that mention crypto/omap or scatterlist-related failures. The bug commonly triggers memory or boundary-related errors when the flawed helper is exercised.
Remediation and mitigation guidance
Patch management is straightforward here: install a kernel update that contains the upstream fix or apply the stable backport for the kernel branch you run. Specific guidance:- Install vendor or distribution kernel updates as soon as they become available. Many mainstream Linux distributions will roll the upstream fix into their stable kernel packages; apply them through your standard package and image management process.
- If a vendor patch is not immediately available, apply the stable-tree patch or cherry-pick the upstream commit into your internal kernel trees and rebuild. The upstream change is intentionally small and limited to a single-line correction in drivers/crypto/omap-crypto.c, making it a low-risk backport candidate for experienced kernel maintainers. The stable patch chain and commit text are available via kernel mailing lists and stable-tree announcements.
- If you cannot patch quickly, mitigate risk by:
- Blacklisting or disabling the omap-crypto module if your workload does not require hardware crypto acceleration on OMAP devices. Add the module to /etc/modprobe.d/blacklist.conf or rebuild kernels without the driver.
- Restricting local access to vulnerable systems; ensure applications cannot pass arbitrary scatterlist entries into kernel crypto channels from untrusted contexts.
- Monitoring kernel logs for oops/panic patterns referencing omap/crypto and setting up alarms for indicators of misuse or stress.
- Validate after patch: reboot into the new kernel or reload the patched module and verify that previously failing operations no longer trigger allocation size or sg-table errors. Run any vendor-provided test suites that exercise hardware crypto paths.
Detection and monitoring recommendations
- Add a security check to kernel image build pipelines that verifies the fix commit or the presence of the corrected source line in drivers/crypto/omap-crypto.c. Automate this check in CI to prevent shipping vulnerable builds.
- For managed device fleets, include kernel version and module configuration checks in your asset inventory system. Automated scripts can identify vulnerable kernels and flag devices in need of updates.
- Watch for the following signs in system logs:
- Frequent kernel oops whose backtrace references omap_crypto_copy_sg_lists or drivers/crypto/omap-crypto.c.
- Unexpected crypto engine failures when using hardware acceleration on OMAP-based devices.
- User-space failures that correlate with periodic attempts to use hardware crypto features.
Why this fix matters even if exploitability seems limited
- Kernel code runs in the most privileged context. Even seemingly minor memory-safety mistakes can be the difference between a stable system and one where persistent or evasive exploitation becomes possible.
- Embedded and IoT devices often have long patch cycles. Code that is benign on server distributions can persist for years in vendor kernels and custom images. Ensuring a fix is included in vendor builds — or disabled where unnecessary — reduces the long tail of device vulnerability.
- The patch demonstrates best-practice kernel hygiene: prefer precise type-based sizeof usage and prefer helper patterns that minimize manual memory-size computation. The change also shows the importance of code review and of stable-tree oversight; a single-type mismatch was caught, fixed and propagated across trees quickly.
What vendors and vendors’ customers should do now
- Vendors and OEMs shipping OMAP-based images: integrate the upstream fix into your kernel build trees and push updated images through your QA and distribution channels. Given the small and low-risk nature of the patch, aim to include it in the next maintenance image as a high-priority stability/security fix.
- Enterprise admins and device managers: audit your inventories for OMAP hardware and confirm whether the distribution kernel includes the crypto: omap driver. If yes, prioritize testing and deploying the patched kernel image.
- Security operations teams: ensure kernel-level monitoring is enabled and correlate any unusual device reboots or panic messages with the presence of unpatched OMAP kernels.
- For embedded device development teams: add unit and integration tests that exercise the crypto driver code paths under heavy load and with malformed scatterlists to catch similar mistakes earlier in development.
Caveats, uncertainties, and cautionary notes
- Public trackers (as of the time of writing) do not yet assign a CVSS score or clearly state exploit maturity; operators should not interpret a lack of a severity score as a sign of low priority. Kernel memory corruption bugs should be treated as high-priority fixes by default because of their privileged scope.
- The real-world attack surface for CVE-2026-23222 is constrained by platform: only devices with OMAP hardware and the relevant driver enabled are meaningfully exposed. Still, because many embedded devices do not receive frequent updates, the practical risk for unpatched devices can be substantial.
- Verification that a given kernel build is patched often requires either comparing source trees/commits or testing on a representative device. If you cannot update quickly, consider fallback mitigations such as module blacklisting or limiting untrusted local inputs.
- Some vendors maintain custom kernel trees that lag upstream; these vendors must explicitly backport the fix. Stable-tree backports have been prepared (including a 5.15-stable backport), but it remains the vendor’s responsibility to ship tested images. Administrators should confirm with their vendor timelines and support notes.
Practical, step-by-step remediation checklist
- Identify affected devices:
1.) Run uname -r on devices.
2.) Check whether drivers/crypto/omap is built or the omap-crypto module is present.
3.) Confirm hardware family (TI OMAP). - Acquire a patched kernel:
- Prefer vendor-supplied kernel updates. If none exist, obtain the upstream/stable patch and backport to your local kernel tree. The patch is a single-line fix and is tracked across stable branches.
- Test the patched kernel on representative hardware:
- Exercise crypto calls that use the hardware engine and run stress or IAM-style tests that simulate heavy I/O and varied scatterlist patterns.
- Deploy following your standard change-control process:
- Rollout to pilot groups, monitor, then full fleet.
- If immediate patching is impossible:
- Temporarily disable omap-crypto via module blacklisting or kernel rebuild without the driver; restrict local access and monitor logs closely.
Final analysis: small patch, meaningful impact
CVE-2026-23222 is an example of how a terse, human-level mistake in C — choosing the wrong operand in a sizeof expression — can translate into a kernel memory-safety issue. The good news is the fix is small, well-understood, and already merged into stable trees; the operational work is ensuring the fix reaches the devices that need it.This vulnerabilirecurring lessons for kernel and embedded system teams:
- Type-aware allocation: always express allocation sizes in terms of the dereferenced target pointer (sizeof(*ptr)) to reduce the chance of this class of bug.
- Rapid propagation: small fixes should still be propagated through vendor trees and stable branches with urgency, because embedded devices often maintain long-lived kernels.
- Inventory discipline: maintain an accurate device and kernel inventory so platform-specific fixes are not overlooked.
In short: CVE-2026-23222 is a correctable and low-risk-to-patch kernel bug that warrants prompt attention from operators of OMAP-based systems. Apply vendor-supplied kernel updates or backport the one-line fix to eliminate the undersized scatterlist allocation, validate the change on representative hardware, and monitor device logs to ensure the problem is resolved.
Source: MSRC Security Update Guide - Microsoft Security Response Center