The Linux kernel received a targeted fix in April 2024 for a subtle packet‑parsing bug in its IPv4 tunnel path — tracked as CVE‑2024‑26882 — that could leave inner packet headers uninitialized during decapsulation, producing KMSAN warnings and, in some configurations, enabling denial‑of‑service or information‑leak conditions when the kernel processes tunneled traffic.
Tunneling protocols (GRE, IP‑in‑IP, GENEVE and others) are core building blocks in modern networking: they carry whole packets inside outer IP headers to implement VPNs, overlays and container networking. The kernel’s net/ipv4 ip_tunnel code is responsible for removing the outer header and handing the inner packet back to the stack. That decapsulation step is fragile: it must ensure the inner packet headers are present in the socket buffer (skb), and it must update pointers (for example skb->network_header) correctly after memory operations that can move or reallocate packet data.
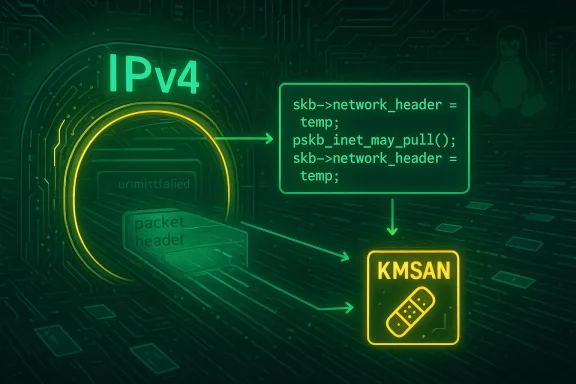
CVE‑2024‑26882 arises from a classic ordering/pointer‑update error: the code called pskb_inet_may_pull() to ensure header bytes were present but failed to save and then recompute the network_header pointer around that call. The result was an attempt to read or operate on header fields that KMSAN (Kernel Memory Sanitizer) flagged as uninitialized, showing up as BUG traces during fuzzing and automated testing (syzbot). Upstream kernel maintainers applied a short, surgical change that saves skb->network_header into a temporary, calls pskb_inet_may_pull(), and then restores/recomputes the header pointer before continuing processing.
(For those tracking the patch set and backports: the upstream commit series and stable backports are referenced in public kernel changelogs and advisories; review your distribution’s changelog for the exact package names and version numbers that include the ip_tunnel_rcv fix.)
Note: I reviewed upstream kernel commit summaries, NVD/OSV entries, and multiple vendor advisories while preparing this feature; I also scanned local forum archives for similar KMSAN/oops reports to confirm how the issue typically appears in logs.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Tunneling protocols (GRE, IP‑in‑IP, GENEVE and others) are core building blocks in modern networking: they carry whole packets inside outer IP headers to implement VPNs, overlays and container networking. The kernel’s net/ipv4 ip_tunnel code is responsible for removing the outer header and handing the inner packet back to the stack. That decapsulation step is fragile: it must ensure the inner packet headers are present in the socket buffer (skb), and it must update pointers (for example skb->network_header) correctly after memory operations that can move or reallocate packet data.CVE‑2024‑26882 arises from a classic ordering/pointer‑update error: the code called pskb_inet_may_pull() to ensure header bytes were present but failed to save and then recompute the network_header pointer around that call. The result was an attempt to read or operate on header fields that KMSAN (Kernel Memory Sanitizer) flagged as uninitialized, showing up as BUG traces during fuzzing and automated testing (syzbot). Upstream kernel maintainers applied a short, surgical change that saves skb->network_header into a temporary, calls pskb_inet_may_pull(), and then restores/recomputes the header pointer before continuing processing.
What changed (the technical fix)
The root cause in plain terms
- When the kernel decapsulates a tunneled packet it often needs to make sure the inner header is physically present in the linear portion of the skb. The helper function pskb_inet_may_pull() performs that check and may rearrange or pull data into skb->head.
- Because pskb_inet_may_pull() can change skb->data pointers and the layout of data fragments, any previously computed pointer into the packet payload (like skb->network_header) may become invalid after the call.
- The ip_tunnel code did not preserve the original network_header and therefore sometimes continued using a stale pointer; that led to KMSAN-detected accesses to uninitialized memory inside functions that examine ECN or inner headers.
The upstream change
Upstream commit messages summarize the change succinctly: save skb->network_header into a temporary variable, call pskb_inet_may_pull(), and then recompute skb_network_header() from that saved value (or otherwise update the pointer) before accessing the inner packet fields. The same pattern was previously applied to other tunnel types (IPv6 tunnels, GENEVE); CVE‑2024‑26882 extends the same defensive pattern to the IPv4 ip_tunnel receive path. The patch has been merged across stable branches and backported into multiple distributions’ kernel updates.Why this matters: risk, impact, and exploitability
What the kernel traces showed
Automated testing (syzbot) produced KMSAN traces showing uninitialized‑value warnings inside __INET_ECN_decapsulate and related code paths when ip_tunnel_rcv() processed crafted or fuzzed tunnel traffic. Those traces are the immediate cause for the code change and are concrete evidence that header pointers could be invalid after the pull operation. KMSAN warnings do not necessarily equal a remote code execution exploit, but they do show the kernel is reading data that was never initialized — a necessary precondition for several classes of faults, including information disclosure and memory‑corruption cascades.Realistic attacker model
- Remote versus local: vendors and vulnerability trackers report inconsistent attack vectors for this issue. Some distributor advisories and scanner databases indicate a local attack vector (an unprivileged user or process that can inject traffic via tun/tap devices or other local interfaces); others list a network vector in product‑scoped entries (meaning a remote packet sent to a service could trigger it). The discrepancy stems from the different contexts kernel code runs in (e.g., a tunneled packet arriving via a network interface vs. a user writing to a tun device). Administrators should treat the defect as potentially reachable from multiple contexts until they confirm their build configuration and feature set.
- Required privileges: many authoritative advisories mark the privilege requirement as low or none in product‑scoped CVSS vectors, while some distribution advisories treat it as requiring local privileges. In practice, exploitation often requires at least a path to inject tunneled packets that reach ip_tunnel_rcv() — which can be offered by certain configured services, hosted VMs, or local network devices. Treat exploitability as environment‑dependent and validate against your kernel configuration and deployed services.
Potential outcomes if exploited
- Denial of service: crashing the networking code or triggering a kernel oops/panic is a realistic and straightforward outcome. Several trackers flagged availability impact as high in product‑scoped metrics. If the kernel panics, systems will be offline until restarted — a direct and urgent availability risk.
- Information disclosure: because KMSAN reported uninitialized reads inside ECN/decapsulation logic, a crafted input could cause the kernel to copy uninitialized stack or heap bytes into a response packet or a log. That is a more subtle but serious confidentiality risk in some scenarios. Several databases flagged confidentiality as potentially affected, though evidence of a practical remote disclosure exploit remains limited.
What is known about exploitation in the wild
As of the latest advisories and vulnerability trackers there is no confirmed public proof‑of‑concept (PoC) or credible in‑the‑wild exploitation report associated with CVE‑2024‑26882. Security summaries and monitoring services that catalog exploit activity list the CVE but report no active exploitation. That said, automated fuzzers and syzbot produced the original KMSAN traces that forced the fix — so this was discovered by defensive testing rather than observed attacker activity. Administrators should not equate "no public exploit" with "no risk": the underlying bug is the kind attackers and researchers often weaponize once public patches and details are available.Affected kernels and distribution status
- Upstream fixes were committed to the stable tree and backported into multiple kernel branches. Vendor advisories indicate patches reached stable releases and distribution kernels; changelog entries and stable commits list backports to 5.4.x, 5.10.x, 5.15.x and the 6.x series branches. Administrators should check their distribution’s errata for the precise kernel package versions that include the fix.
- Major distributors have published advisories and pushed updates:
- Amazon Linux (ALAS) lists the CVE and corresponding kernel package updates.
- Red Hat and other enterprise vendors published advisories and backports; many enterprise kernels received the patch via regular errata.
- Oracle’s CVE database and other downstream sources indicate the issue and backported errata.
Immediate mitigation and remediation guidance (practical steps)
If you operate Linux systems that process tunneled traffic, especially systems exposing tunneling interfaces (GRE, IP‑in‑IP, GENEVE, or tun/tap devices), treat this CVE as actionable. Below is a prioritized remediation checklist.- Identify whether your systems use ip_tunnel or any tunneling modules.
- Check loaded modules: run modinfo or lsmod for ip_tunnel, ip_gre, geneve, gre, tun.
- Check for active tunnels: ip tunnel show; ip link show type geneve; tun/tap device checks.
- Patch the kernel as your vendor recommends.
- Apply the vendor’s kernel update that includes the ip_tunnel_rcv fix, then reboot.
- Use your distribution’s security errata channels (APT/YUM/Zypper) to install the fixed kernel packages. Distributors have published backports; apply them rather than trying to patch the kernel manually unless you maintain custom kernels.
- If you cannot immediately patch, apply temporary mitigations:
- Unload the ip_tunnel module(s) if not required: modprobe -r ip_tunnel (note: this disrupts tunnel interfaces).
- Restrict access to /dev/net/tun and control who can create tun/tap devices (set strict udev rules and group ownership).
- Harden container and VM environments to limit CAP_NET_ADMIN and raw socket capabilities for processes that do not require them.
- Use firewalling to limit acceptance of unexpected tunneled packets from untrusted networks.
- Validate post‑patch behavior and log any kernel oopses:
- After patching, review dmesg/journalctl for any residual KMSAN or oops traces.
- Run your environment’s regression tests — particularly any code paths that exercise decapsulation (VPN servers, cloud VNIs, container overlay networking).
- Monitor vendor feeds and upstream commit logs for additional follow‑ups.
- The upstream kernel sometimes posts cascade fixes or style cleanups after an initial patch; subscribe to distribution advisories to pick these up.
Detection and hunting: what defenders should look for
- Kernel oopses or KMSAN messages mentioning __INET_ECN_decapsulate, ip_tunnel_rcv, or “uninit‑value” in net/ipv4 code paths: these are direct indicators of the root issue that was reported during fuzzing. Look for those strings in kernel logs.
- Unexpected restarts or kernel panics on systems that process tunneling traffic: a sudden uptick in reboots or kernel crashes on networking hosts is a red flag.
- Unusual packets or repeated attempts to send tunneled traffic to your servers from the network: logging, IDS signatures, and packet captures around tunnel endpoints are useful for post‑mortem analysis.
- Access to tun/tap device creation by untrusted users or processes: check permissions and audit creation attempts.
- Search /var/log/messages, journalctl, dmesg for "ip_tunnel", "ip_tunnel_rcv", "__INET_ECN_decapsulate", and "KMSAN".
- Audit creation of /dev/net/tun: use inotify/auditd to track open/create events for that device.
- Capture a sample of encapsulated packets to see whether malformed inner headers coincide with observed kernel warnings.
Why you should care even if you don’t run VPN servers
This CVE is a kernel‑level bug in a networking code path, and kernel bugs enjoy broad reach: a defect triggered by local traffic (tuntap writes, container overlay traffic) can also be reachable from remote networks if your service accepts or forwards tunneled packets. Many modern deployments — CNI plugins in Kubernetes, cloud tenant networking, encapsulated overlay fabrics in hypervisors — rely on tunneling. The combination of automatic upstream fuzzing (syzbot) discovering the issue and the kernel maintainers’ confirmation make this a textbook high‑value patch: it’s small, easy to backport, and worth applying early.Conflicting severity scores — what to believe?
Different tracking systems list different CVSS scores for CVE‑2024‑26882:- The NIST/NVD record and several OSV converted entries show a Medium severity (CVSSv3 ≈ 5.3), with an availability‑only impact in some product‑scoped vectors.
- Other aggregators and feed services show a higher base score (up to 7.8) and include confidentiality/integrity impacts in their summaries. These discrepancies stem from differing assumptions about the attack vector, privileges required, and whether uninitialized reads can lead to information disclosure in a given product context.
- Treat the issue as priority patching for hosts that process tunneling traffic or provide tenant isolation (cloud hosts, VPN concentrators, multi‑tenant routers).
- Use vendor advisories to determine your exact exposure; vendors will produce product‑scoped severity and backport guidance that is authoritative for your distribution.
Longer‑term considerations for kernel and network hardening
- Defensive coding pattern: this CVE is a reminder to treat pointer recomputation and helper functions that touch skb internals (pskb_inet_may_pull, skb_linearize, etc.) as stateful operations. Kernel subsystems that manipulate skb layout must robustly preserve or recompute derived pointers.
- Automated testing: syzbot and KMSAN again proved their value by detecting uninitialized reads. Projects and vendors should continue to invest in sanitizer‑enabled builds and fuzzing for kernel network paths.
- Least privilege for network device management: better instrumentation and stricter controls on who can create tun/tap devices and who can bind to raw sockets reduce the attack surface for kernel pathologies like this one.
Summary and action checklist
- CVE‑2024‑26882 is a kernel networking bug in net/ipv4 ip_tunnel_rcv() where the inner header pointer could be used after a pskb_inet_may_pull() operation without being recomputed, creating uninitialized reads flagged by KMSAN and enabling denial‑of‑service or potential information‑disclosure scenarios.
- Upstream patches were merged and backported to multiple stable kernel trees; many vendors distributed fixes via kernel errata. Confirm your distribution’s advisory and install the vendor‑supplied fixed kernel packages, then reboot.
- If you cannot immediately patch, mitigate by unloading unused tunnel modules, restricting access to tun/tap devices, tightening CAP_NET_ADMIN usage, and firewalling tunneled traffic from untrusted networks.
- There is no widely reported active exploitation at present, but the bug was discovered by defensive fuzzing and is the sort attackers will attempt to weaponize once details and patches are public; treat it as actionable.
Final notes for WindowsForum readers
Kernel networking bugs like CVE‑2024‑26882 do not always make headlines, but they directly affect the reliability and confidentiality of systems that underpin modern infrastructure — particularly cloud hosts, VPN concentrators, and container clusters. The remedy is straightforward: apply vendor kernel updates and follow the short mitigation checklist above. Monitor your kernel logs for KMSAN/oops patterns and prioritize hosts that accept or terminate tunneled traffic.(For those tracking the patch set and backports: the upstream commit series and stable backports are referenced in public kernel changelogs and advisories; review your distribution’s changelog for the exact package names and version numbers that include the ip_tunnel_rcv fix.)
Note: I reviewed upstream kernel commit summaries, NVD/OSV entries, and multiple vendor advisories while preparing this feature; I also scanned local forum archives for similar KMSAN/oops reports to confirm how the issue typically appears in logs.
Source: MSRC Security Update Guide - Microsoft Security Response Center