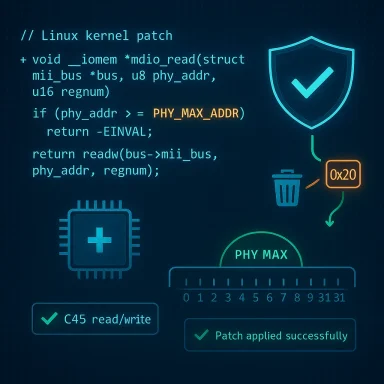
The Linux kernel patch that closed CVE-2025-38111 — a bounds‑check defect in net/mdiobus — is small in code but large in operational impact: it removes a user‑supplied MDIO address from an unchecked ioctl path that could be used to read or write beyond the kernel’s mdiobus statistics array, and operators should treat the fix as urgent for any systems that expose MDIO management to local users or tooling.
The MDIO (Management Data Input/Output) subsystem is the kernel layer that exposes PHY management to userland for Ethernet interfaces. Tools such as mdio‑tools rely on that interface to perform Clause 22 and Clause 45 MDIO reads/writes against PHY devices, typically for debugging, diagnostics, or device bring‑up tasks. Historically, the kernel limited PHY addresses to a small range (commonly 0–31, defined by PHY_MAX_ADDR), but the ioctl interface accepted an address parameter coming from userland without sufficiently verifying that it fell within that safe range. The result was an unchecked index into an internal statistics array used by the mdiobus implementation — a textbook out‑o.
Practically, this type of bug is notable because it sits at the intersection of privileged kernel code and userland tooling: a malformed or malicious ioctl originating from a process that can interact with MDIO could cause a read or write outside the intended stats array, with consequences ranging from information disclosure to memory corruption and crashes. Multiple public trackers ingested the upstream patch and classified the issue as significant; NVD documents the fix under CVE‑2025‑38111 and describes the change as an address verification added before MDIO C45 read/write operations.
Microsoft’s phased VEX rollout has improved clarity for Azure Linux and related artifacts, but defenders must still verify every Microsoft‑supplied image or kernel artifact they run (WSL kernels, Marketplace images, managed node images, custom vendor images). The operational recommendation is simple: if Micinux is affected, treat Azure Linux images as confirmed in‑scope; for other Microsoft artifacts, perform artifact‑level inventory and validation rather than assuming safety.
Action checklist (one page, actionable)
Conclusion: apply the kernel update, validate the fix, and harden MDIO access — the code change is small, but the protection it buys is decisive for hosts that expose PHY management to userland.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The MDIO (Management Data Input/Output) subsystem is the kernel layer that exposes PHY management to userland for Ethernet interfaces. Tools such as mdio‑tools rely on that interface to perform Clause 22 and Clause 45 MDIO reads/writes against PHY devices, typically for debugging, diagnostics, or device bring‑up tasks. Historically, the kernel limited PHY addresses to a small range (commonly 0–31, defined by PHY_MAX_ADDR), but the ioctl interface accepted an address parameter coming from userland without sufficiently verifying that it fell within that safe range. The result was an unchecked index into an internal statistics array used by the mdiobus implementation — a textbook out‑o.Practically, this type of bug is notable because it sits at the intersection of privileged kernel code and userland tooling: a malformed or malicious ioctl originating from a process that can interact with MDIO could cause a read or write outside the intended stats array, with consequences ranging from information disclosure to memory corruption and crashes. Multiple public trackers ingested the upstream patch and classified the issue as significant; NVD documents the fix under CVE‑2025‑38111 and describes the change as an address verification added before MDIO C45 read/write operations.
What went wrong — technical anatomy
At a technical level, the vulnerable sequence had three properties that made it dangerous:- The ioctl interface accepts a user‑supplied MDIO address parameter that is subsequently used as an index into kernel structures (the mdiobus stats array).
- The kernel historically limited PHY addresses conceptually via PHY_MAX_ADDR, but the ioctl did not enforce that limit before indexing.
- The mdiobus code exposes C45 read/write operations that may perform array accesses based on the supplied address; without a pre‑check, a high address value can cause an out‑of‑bounds read or write.
Exploitation profile and impact
Understanding who can exploit this bug and what it can achieve is essential to triage.- Attack vector: Local. Exploitation requires the ability to issue MDIO ioctls. That usually means local code execution or administrative tooling on the host (or a guest that has the relevant device access and ioctl surface). It is not a trivial remote network trigger in typical server configurations.
- Prerequisites: The system must run a kernel build that includes the vulnerable net/mdiobus code and expoces to the context that an attacker can control. Many server images and virtual NICs do not expose this interface to unprivileged users, but embedded devices and platform images used for network appliance management are more likely to.
- Potential impact: Out‑of‑bounds reads can disclose kernel memory content; out‑of‑bounds writes can corrupt kernel memory and cause crashes, stability failures, or, in chained scenarios with other vulnerabilities and particular kernel hardening configurations, more serious outcomes. Vendors and trackers focused the primary impact on availability and confidentiality risk depending on the operation (read vs write). Public scoring varied, with some sources reporting a CVSS in the mid‑6 to 7 range; NVD documents the defect and the upstream fix.
Where this bug matters most — exposure scenarios
Not every Linux host is equally at risk. The highest‑risk classes include:- Network appliances, embedded systems, and switch/router platforms that expose PHY management to userland or to remote management tooling.
- Hosts where local users (or guest VMs) can s — for example, management servers, build hosts, or developer machines with diagnostic tools installed.
- Custom images or marketplace artifacts that include kernel builds with the vulnerable code enabled (CONFIG_MDIO and associated drivers).
How the fix works (concise)
The upstream remedy is simple and correct:- Add an explicit check that any mdio address passed into the C45 read/write ioctl is <= PHY_MAX_ADDR (or otherwise within the configured bounds).
- Reject out‑of‑range requests before performing any index-based access into the statistics array. This prevents accidental or malicious indexing beyond the array bounds and isolates statistics tracking from user‑supplied parameters.
Detection, triage and immediate steps for operators
If you manage Linux hosts, follow these pr Inventory: Identify which systems run a kernel build that could include net/mdiobus and which hosts expose MDIO ioctl interfaces to users or untrusted tooling. Look for tools like mdio‑tools in images and the presence of MDIO‑related kernel modules.- Map: Determine whether the upstream commit that added the bounds check is present in your kernel version (or whether your vendor has backported a fix). Use vendor advisories and upstream commit IDs rather than relying on generic kernel version numbers when possible. Multiple distros published package advisories mapping this fix into specific kernels.
- Patch: Apply vendor-supplied kernel updates or install patched images as soon as practical. For supported distributions, use distribution security updates; cloud images should be replaced with vendor‑published patched images where available. If your vendor supplies livepatches for kernels in production, apply them per vendor guidance.
- Restrict: If immediate patching is impossible, restrict access to MDIO tooling and ioctl surfaces:
- Remion of mdio‑tools on production hosts that do not need them.
- Tighten file system permissions and capability controls for tools or device nodes that can issue MDIO ioctls.
- Use containers/namespaces to isolate any diagnostic toos.
- Monitor: Log invocations of MDIO operations (audit/ioctl logs), and set alerts for calls from unexpected users, processes, or contexts. Collect kernel logs (dmesg, journalctl -k) for oops traces that mention mdiobus or MDIO paths.
- Validate: In staging, reproduce the patmpting out-of-range MDIO ioctls against patched and unpatched kernels to confirm that the fixed kernel rejects invalid addresses instead of indexing the stats array. Exercise this only in controlled test environments.
Vendor attestations and Microsoft’s role — what the MSRC note means for you
Large vendors increasingly publish machine‑readable attestations (VEX/CSAF) that state whether a named product contains a given open‑source component. These attestations are powerful operational signals — when a vendor says "Product X includes this component and is therefore potentially affected," treat that as an authoritative inventory result for Product X. However, it is crucial to unde an attestation for one product is not a proof that other products from the same vendor are free of the component. The absence of an attestation is absence of attestation, not proof of absence.Microsoft’s phased VEX rollout has improved clarity for Azure Linux and related artifacts, but defenders must still verify every Microsoft‑supplied image or kernel artifact they run (WSL kernels, Marketplace images, managed node images, custom vendor images). The operational recommendation is simple: if Micinux is affected, treat Azure Linux images as confirmed in‑scope; for other Microsoft artifacts, perform artifact‑level inventory and validation rather than assuming safety.
Risk analysis — strengths and limitations of the fix
Strengths- The upstream patch is minimal, well-scoped, and follows best practice: validate inputs at the boundary. It removes the primary root cause (unchecked user-supplied index) without altering valid MDIO behavior.
- Because the change is straightforward, most vendors were able to backport or include it in stable kernel packages quickly; distribution advisories and cloud vendors published patches within typical security timelines.
- The mitigation is certifiable: testing that a patched kernel rejects out‑of‑range addresses is simple and deterministiesidual risks
- The attack vector is local but non‑trivial to completely eliminate without inventory: many environments do not expose MDIO ioctls, but those that do — especially embedded and network appliance images — remain high risk until patched. Inventory is the hard part.
- An out‑of‑bounds write can be more severe than a read; whether a particular build and kernel hardening configuration makes write-based exploitation feasible depends heavily on architecture, KASLR/SMEP/SMAP, and allocator behavior. Those environmental variables make precise exploitability statements brittle; treat claims of remote RCE from a single unchecked index as possible but unproven without proof‑of‑concepts. Flag such claims and insist on artifact‑specific verification.
- Vendor ecosystems are diverse: a patched upstream commit does not mean every vendor kernel is patched. Some vendors backport selectively, and others may not yet have released fixed packages for every supported kernel branch. Operators must rely on vendor advisories or their own mapping from kernel commits to package releases.
Detection and forensics — what to look for post‑incident
If you suspect this vulnerability was used against a host, prioritize capturing the folrnel oops/panic logs: a crash involving mdiobus or unexpected memory corruption traces in dmesg or journalctl -k. Preserve and collect kdump output if kernel cr.- Audit logs showing mdio ioctl invocations and which process/user issued them; correlate these with process execution records and any unusual local activity.
- mdio‑tools usage records and binary hashes from hosts thatt. If mdio‑tools or other diagnostic tooling is present, examine recent invocations and wrapper scripts that may automate bulk MDIO queries.
- Memory forensic captures from VMs or hosts suspected of being targeted; an out‑of‑bounds read may reveal adjacent kernel memory that could indicate exploitation attempts. Treat such disclosure carefully and consider engaging incident response specialists for high‑value hosts.
Recommended policy and long‑term controls
To reduce exposure to this and similar kernel interface bugs, adopt these policies:- Inventory-first security: ensure you have automated asset inventory that records kernel versions and module lists for every host and image, including vendor‑providedes, WSL kernels, Marketplace images). Vendor VEX/CSAF attestations are helpful, but do not replace artifact inventory.
- Principle of least privilege for hardware management: run MDIO/PHY management tooling only on designated management hosts with strict access control; do not install or expose such tools on general-purpose production nodes.
- Harden kernel configurations: enable available kernel hardening options appropriate for your workload; use livepatches where vendor support and maintenance windows require them.
- Integrate vendor attestations: consume CSAF/VEX feeds where available and feed attestation state into your vulnerability management process; when a vendor attests a product is affected, trigger focused inventory and patch cycles for artifacts that match.
Final assessment and practical takeaway
CVE‑2025‑38111 is a clear example of how a narrow, mechanistic bug — an unchecked index at the ioctl boundary — can translate into material operational risk when it touches privileged kernel code paths. The upstream fix (input validation before C45 read/write) is the right and final remedy; however, the practical job for operators is not fixed by a single commit: it requires inventory, mapping, patching, monive access controls to fully eliminate exposure across heterogeneous images and vendor kernels.Action checklist (one page, actionable)
- Inventory all images and hosts for MDIO support and presence of mdio‑tools.
- Map your running kernel versions to upstream/stable commits and vendor advis‑2025‑38111.
- Appeplace images with vendor‑published, patched images; use livepatches if supported and necessary.
- Restrict MDIO ioctl access and remove mdio‑tools where not needed.
- Monitor for MDIO ioctl activity and kernel oops traces; capture forensic artifacts if unusual activity is detected.
Conclusion: apply the kernel update, validate the fix, and harden MDIO access — the code change is small, but the protection it buys is decisive for hosts that expose PHY management to userland.
Source: MSRC Security Update Guide - Microsoft Security Response Center