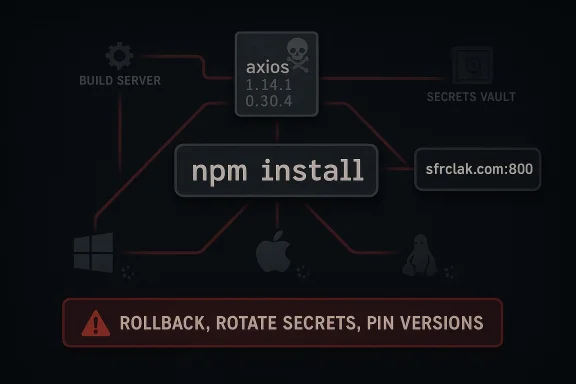
On March 31, 2026, one of JavaScript’s most widely used HTTP clients became the latest reminder that modern software supply chains are now a frontline security battlefield. Microsoft Threat Intelligence says two malicious npm releases tied to Axios were used to pull a second-stage remote access trojan from Sapphire Sleet, a North Korean state actor, affecting Windows, macOS, and Linux development environments and CI/CD systems alike. The campaign matters not only because Axios is common, but because it shows how a single poisoned package update can turn routine dependency management into a stealthy cross-platform intrusion. Microsoft is urging organizations to roll back to safe versions, rotate secrets, and harden npm update practices immediately. (microsoft.com)
Axios is not just another package in the JavaScript ecosystem. It is a promise-based HTTP client for both browser and Node.js environments, and Microsoft’s coverage reiterates that it is installed through the npm workflow many teams treat as routine infrastructure rather than a security-sensitive event. That trust is what made the compromise dangerous: the malicious release did not need to break the application’s visible behavior to do damage. (axios-http.com)
The core security lesson is that install-time execution remains one of the most underappreciated risks in npm-based builds. In this case, the malicious logic was inserted through a dependency and triggered by lifecycle scripts during install, which means the attack could fire during a developer’s local
Microsoft’s attribution to Sapphire Sleet also matters because it places the incident within a broader North Korean pattern of financially motivated and operationally opportunistic tradecraft. Microsoft has previously described Sapphire Sleet as active for years, focused on cryptocurrency and related targets, and willing to blend social engineering, malicious infrastructure, and living-off-the-land techniques to scale operations. This Axios incident fits that model unusually well, except the delivery vector was package publishing rather than direct phishing. (microsoft.com)
The other notable change is how aggressively the attack crosses platforms. Instead of building one malware family and hoping it lands, the operator used a shared command-and-control endpoint and selected payloads based on the victim OS. That design minimizes client-side complexity while maximizing downstream reach, which is exactly what makes supply chain attacks so attractive to well-resourced actors. (microsoft.com)
That “manifest-only” style of tampering is especially insidious because it gives casual reviewers very little to notice. A package can look legitimate at runtime while carrying a hidden install hook, and the installation process itself becomes the payload delivery mechanism. In practical terms, that means a build can appear healthy while the compromise is already underway in the background. (microsoft.com)
Microsoft also notes that the plain-crypto-js account used to seed the malicious chain was associated with Sapphire Sleet infrastructure and has now been disabled. That is an important disruption, but it is not a complete remedy because the poisoned versions may already exist in caches, lockfiles, mirrors, or build artifacts inside enterprise environments. Disabling one publishing account does not unwind every downstream installation that already happened. (microsoft.com)
The script also used obfuscation to hide what it was doing from quick inspection. By decoding paths, module names, and command templates at runtime, the loader reduced the usefulness of static scanning and casual package review. This is a classic example of why supply chain defenses increasingly need to observe behavior, not just signatures. (microsoft.com)
The second-stage payloads were different by operating system, but they all followed the same logic: drop a loader, establish persistence, and keep fetching remote instructions. On Windows, the chain used PowerShell and VBScript; on macOS, it used AppleScript and a native binary; on Linux, it used a Python loader. That approach makes the campaign more resilient and allows the threat actor to reuse the same C2 architecture across heterogeneous developer environments. (microsoft.com)
The macOS path was equally deliberate. It used
On Linux, the loader wrote a Python file to
Enterprise environments are especially vulnerable because build servers often have broader access than typical endpoint devices. CI/CD systems may hold signing keys, deployment tokens, cloud credentials, and source code access, so an attacker who reaches the build plane can potentially move from package compromise to broader environment compromise. That is why Microsoft’s guidance emphasizes secret rotation, log review, and exposure analysis rather than just uninstalling a package. (microsoft.com)
Consumer developers are not safe either, even if they are not part of a formal enterprise pipeline. A laptop used for open-source contribution, side projects, or testing can still cache credentials, access cloud dashboards, or sign commits. A malicious npm install on that machine can therefore become a stepping stone into production assets that the user can reach indirectly. (microsoft.com)
This is also consistent with the actor’s preference for adaptive tradecraft. Microsoft’s recent reporting on North Korean groups shows increasing use of varied infrastructure, cloud-hosted lure content, and evolving delivery mechanisms. Supply chain poisoning is a natural extension of that playbook because it offers scale, plausible legitimacy, and a path into organizations that are difficult to reach with direct phishing alone. (microsoft.com)
The threat actor’s use of a shared C2 and OS-specific second stages suggests a mature operator mindset rather than a one-off opportunistic script. One infrastructure endpoint can service a broad victim pool while the server tailors the payload by operating system, reducing maintenance burden and maximizing reach. That kind of engineering discipline is one reason nation-state supply chain activity can be so hard to contain. (microsoft.com)
Microsoft Defender coverage appears to span endpoint, cloud, and XDR workflows, with blocking detections mapped to the malicious script, downloader behavior, macOS artifacts, Linux loader, and Windows persistence chain. The company also highlights network protection and SmartScreen blocking malicious indicators tied to the campaign. The emphasis here is not just detection, but interruption of the attack path before persistence becomes durable. (microsoft.com)
That breadth matters because the attack touched multiple layers of the stack. A CI job, a developer workstation, a container build, or a signed release pipeline could all be affected differently, so defenders need telemetry across endpoints, identities, clouds, and repositories. Microsoft’s own framing of Exposure Management and advanced hunting reflects that the blast radius is not a single machine; it is the graph of everything that machine can reach. (microsoft.com)
Microsoft’s guidance calls out concrete indicators such as
Network monitoring is equally important. The campaign used a consistent route to
For consumers and independent developers, the issue is more personal but still serious. A laptop with cached cloud access, browser sessions, SSH keys, or personal wallet-related assets can become a pivot point, especially if the developer uses the same machine for side projects and production-adjacent work. In that sense, the line between personal and professional compromise is thinner than many people think. (microsoft.com)
The response should therefore differ by environment, even if the core guidance is the same. Enterprises need central visibility, automated hunting, and strict dependency controls; individuals need to assume any affected install might have touched credentials and re-establish trust from scratch. Treating both cases as “just update the package” would be a mistake. (microsoft.com)
The event also creates an opportunity for organizations to re-evaluate how they consume open-source dependencies. Many teams already know they should pin versions, but this incident shows why that advice is operationally urgent rather than theoretical. If a package can be weaponized with a single publish event, then update governance becomes a core security control. (microsoft.com)
A second concern is cleanup complacency. Removing the visible malicious package does not necessarily remove cached artifacts, lockfile references, hidden persistence, or harvested secrets. Because the attack explicitly tries to erase itself and restore a clean-looking manifest, defenders who only inspect
A third concern is that supply chain attacks can become self-reinforcing. If one compromised package infects build systems that then publish artifacts or deploy containers, the malicious code can spread through trusted channels faster than humans can manually verify each step. That is why build integrity and artifact provenance now matter as much as endpoint protection. (microsoft.com)
We should also expect more attention on package provenance and update governance. The combination of exact version pinning, trusted publishing, and script suppression is no longer a niche best practice; it is becoming the minimum viable defense for teams that depend on open-source ecosystems. That shift may be inconvenient, but it is a rational response to the scale of the threat. (microsoft.com)
Finally, this case will likely reinforce a broader industry lesson: attackers do not need to invent new distribution channels when they can hijack trusted ones. npm, PyPI, and other package ecosystems remain attractive because they already sit inside legitimate software workflows. The more organizations can verify provenance, constrain execution, and monitor egress, the harder it becomes for a malicious publish to become a full incident. (microsoft.com)
Source: Microsoft Mitigating the Axios npm supply chain compromise | Microsoft Security Blog
 Overview
Overview
Axios is not just another package in the JavaScript ecosystem. It is a promise-based HTTP client for both browser and Node.js environments, and Microsoft’s coverage reiterates that it is installed through the npm workflow many teams treat as routine infrastructure rather than a security-sensitive event. That trust is what made the compromise dangerous: the malicious release did not need to break the application’s visible behavior to do damage. (axios-http.com)The core security lesson is that install-time execution remains one of the most underappreciated risks in npm-based builds. In this case, the malicious logic was inserted through a dependency and triggered by lifecycle scripts during install, which means the attack could fire during a developer’s local
npm install, an automated dependency refresh, or a pipeline job that believed it was merely updating packages. That is precisely the kind of “quiet failure” that makes supply chain compromise so hard to detect early. (microsoft.com)Microsoft’s attribution to Sapphire Sleet also matters because it places the incident within a broader North Korean pattern of financially motivated and operationally opportunistic tradecraft. Microsoft has previously described Sapphire Sleet as active for years, focused on cryptocurrency and related targets, and willing to blend social engineering, malicious infrastructure, and living-off-the-land techniques to scale operations. This Axios incident fits that model unusually well, except the delivery vector was package publishing rather than direct phishing. (microsoft.com)
The other notable change is how aggressively the attack crosses platforms. Instead of building one malware family and hoping it lands, the operator used a shared command-and-control endpoint and selected payloads based on the victim OS. That design minimizes client-side complexity while maximizing downstream reach, which is exactly what makes supply chain attacks so attractive to well-resourced actors. (microsoft.com)
What Happened
Microsoft says the malicious releases were axios@1.14.1 and axios@0.30.4, both published on March 31, 2026, and both altered in a surgical way that left the visible Axios application code unchanged. The compromise relied on a fake dependency, plain-crypto-js@4.2.1, which existed only to trigger install-time execution and then fetch the next stage from attacker infrastructure. (microsoft.com)That “manifest-only” style of tampering is especially insidious because it gives casual reviewers very little to notice. A package can look legitimate at runtime while carrying a hidden install hook, and the installation process itself becomes the payload delivery mechanism. In practical terms, that means a build can appear healthy while the compromise is already underway in the background. (microsoft.com)
Microsoft also notes that the plain-crypto-js account used to seed the malicious chain was associated with Sapphire Sleet infrastructure and has now been disabled. That is an important disruption, but it is not a complete remedy because the poisoned versions may already exist in caches, lockfiles, mirrors, or build artifacts inside enterprise environments. Disabling one publishing account does not unwind every downstream installation that already happened. (microsoft.com)
Why this release pattern worked
The attack leveraged the fact that npm ecosystems often prefer convenience over strict pinning. If a project depends on Axios using a caret or tilde range, the package manager may resolve to a newly published version that the organization never explicitly reviewed. That makes dependency syntax a security control, not merely a developer preference. (microsoft.com)- The malicious versions were delivered as ordinary-looking package updates.
- The runtime behavior of Axios itself was not visibly altered.
- A fake dependency served as the hidden execution trigger.
- Install-time scripts did the real work.
- The payload path worked across multiple operating systems. (microsoft.com)
How the Payload Chain Worked
Once installation began, the injected dependency launched a Node.js setup script that reconstructed strings dynamically and connected tosfrclak[.]com over port 8000 to retrieve the next stage. Microsoft’s analysis shows the same endpoint and path were used across all variants, with the client indicating platform through request content so the server could return an OS-specific payload. That is a tidy operator design: one URL, many outcomes. (microsoft.com)The script also used obfuscation to hide what it was doing from quick inspection. By decoding paths, module names, and command templates at runtime, the loader reduced the usefulness of static scanning and casual package review. This is a classic example of why supply chain defenses increasingly need to observe behavior, not just signatures. (microsoft.com)
The second-stage payloads were different by operating system, but they all followed the same logic: drop a loader, establish persistence, and keep fetching remote instructions. On Windows, the chain used PowerShell and VBScript; on macOS, it used AppleScript and a native binary; on Linux, it used a Python loader. That approach makes the campaign more resilient and allows the threat actor to reuse the same C2 architecture across heterogeneous developer environments. (microsoft.com)
Cross-platform design in practice
The Windows path is the most elaborate because it aims for persistence and disguise. Microsoft says it created a startup artifact, wrote a hidden batch file, renamed PowerShell into something that looked benign, and used script hosts likecscript to reduce visible windows and user prompts. The result is a payload chain that behaves more like a stealthy administrative tool than obvious malware. (microsoft.com)The macOS path was equally deliberate. It used
osascript and background execution, stored a durable artifact in /Library/Caches/com.apple.act.mond, and applied executable permissions before launching the binary. That filename choice matters: it borrows Apple-like naming to blend with legitimate system behavior, which is a small but telling piece of social engineering for defenders and analysts. (microsoft.com)On Linux, the loader wrote a Python file to
/tmp/ld.py and ran it detached with nohup. That is simple but effective because Linux developers and build agents often tolerate temporary-file workflows during testing. In a CI context, that can make the initial compromise look like an ordinary transient job artifact unless egress monitoring is strong. (microsoft.com)Why Developer Workflows Are So Exposed
Modern JavaScript development depends heavily on transitive packages, automated updates, and repeatable install behavior. Those same conveniences create an attack surface where one compromised package can cascade through many projects that never intentionally chose the malicious version. In this incident, that risk was amplified by the assumption that npm install events are low-risk maintenance rather than high-risk execution. (microsoft.com)Enterprise environments are especially vulnerable because build servers often have broader access than typical endpoint devices. CI/CD systems may hold signing keys, deployment tokens, cloud credentials, and source code access, so an attacker who reaches the build plane can potentially move from package compromise to broader environment compromise. That is why Microsoft’s guidance emphasizes secret rotation, log review, and exposure analysis rather than just uninstalling a package. (microsoft.com)
Consumer developers are not safe either, even if they are not part of a formal enterprise pipeline. A laptop used for open-source contribution, side projects, or testing can still cache credentials, access cloud dashboards, or sign commits. A malicious npm install on that machine can therefore become a stepping stone into production assets that the user can reach indirectly. (microsoft.com)
The hidden danger of “helpful” automation
Automatic dependency refreshes often feel like a productivity win, but they can also erase the moment when human review should happen. If an attacker can publish a compromised package and wait for automation to ingest it, the environment has effectively volunteered to run attacker code on schedule. That is why supply chain security now increasingly starts with the question: who decides when software changes? (microsoft.com)- Caret and tilde ranges expand the blast radius of malicious releases.
- Dependency bots can move faster than human review.
- Lockfiles help, but only if they are honored consistently.
- CI/CD secrets create high-value targets for attackers.
- “Install” is often an execution event, not a file copy. (microsoft.com)
Attribution and Threat Actor Context
Microsoft attributes the infrastructure and the Axios compromise to Sapphire Sleet, a North Korean actor also tracked elsewhere as part of the broader Sleet naming family. Microsoft has previously described Sapphire Sleet as active since at least 2020, focused largely on cryptocurrency-related theft and intelligence collection around finance and blockchain ecosystems. That motive aligns neatly with the economics of modern supply chain abuse: access the toolchain, then harvest value from downstream victims. (microsoft.com)This is also consistent with the actor’s preference for adaptive tradecraft. Microsoft’s recent reporting on North Korean groups shows increasing use of varied infrastructure, cloud-hosted lure content, and evolving delivery mechanisms. Supply chain poisoning is a natural extension of that playbook because it offers scale, plausible legitimacy, and a path into organizations that are difficult to reach with direct phishing alone. (microsoft.com)
The threat actor’s use of a shared C2 and OS-specific second stages suggests a mature operator mindset rather than a one-off opportunistic script. One infrastructure endpoint can service a broad victim pool while the server tailors the payload by operating system, reducing maintenance burden and maximizing reach. That kind of engineering discipline is one reason nation-state supply chain activity can be so hard to contain. (microsoft.com)
Why attribution changes the response
Attribution is not just a label for the news cycle. When Microsoft ties an incident to a known state actor, defenders get a better model for likely follow-on activity, likely persistence methods, and likely exfiltration behavior. It also helps security teams prioritize detections and hunting around the actor’s established infrastructure and habits. (microsoft.com)Microsoft’s Defensive Posture
Microsoft says existing detections already alerted and protected customers, and the company has also added additional protections for malicious components observed in the attack. That is important because it shows layered defense can still pay off even when the package ecosystem is compromised. However, it also underscores a harsher truth: organizations cannot rely solely on package registries or publisher identity to keep them safe. (microsoft.com)Microsoft Defender coverage appears to span endpoint, cloud, and XDR workflows, with blocking detections mapped to the malicious script, downloader behavior, macOS artifacts, Linux loader, and Windows persistence chain. The company also highlights network protection and SmartScreen blocking malicious indicators tied to the campaign. The emphasis here is not just detection, but interruption of the attack path before persistence becomes durable. (microsoft.com)
That breadth matters because the attack touched multiple layers of the stack. A CI job, a developer workstation, a container build, or a signed release pipeline could all be affected differently, so defenders need telemetry across endpoints, identities, clouds, and repositories. Microsoft’s own framing of Exposure Management and advanced hunting reflects that the blast radius is not a single machine; it is the graph of everything that machine can reach. (microsoft.com)
What Microsoft wants defenders to do
Microsoft’s recommendations are pragmatic and immediate. The first step is to roll back to known safe versions, then force pinned dependencies, flush caches, and review install logs for the affected versions or theplain-crypto-js package. The broader message is to treat this as an environment-wide hygiene problem rather than a one-off package cleanup. (microsoft.com)- Roll back Axios to 1.14.0 or 0.30.3 or earlier.
- Rotate secrets and credentials exposed to affected systems.
- Review CI/CD logs for malicious install activity.
- Search for indicators such as
sfrclak[.]comand the associated IP. - Remove the malicious package chain from developer and build machines.
- Use
npm ci --ignore-scriptswhere operationally possible. (microsoft.com)
Detection, Hunting, and Investigation
The most useful hunting mindset here is to search for behavioral traces, not just package names. A simple list of installed dependencies may not be enough if the attacker cleaned up after execution, replaced manifests, or removed the installer stub. Instead, defenders should focus on network egress to the suspicious domain and port, script execution artifacts, and any evidence of persistence mechanisms. (microsoft.com)Microsoft’s guidance calls out concrete indicators such as
%TEMP%\6202033.vbs, %TEMP%\6202033.ps1, %PROGRAMDATA%\system.bat, C:\ProgramData\wt.exe, /Library/Caches/com.apple.act.mond, and /tmp/ld.py. Those are useful because they map to the attacker’s post-install workflow and may survive longer than the original package metadata. The more the actor tries to erase itself, the more valuable the residual artifact becomes. (microsoft.com)Network monitoring is equally important. The campaign used a consistent route to
hxxp://sfrclak[.]com:8000/6202033, which gives defenders a narrow but highly actionable search anchor. If that traffic appears in logs from developer laptops, runners, or package-build networks, the incident should be treated as more than a false positive. (microsoft.com)Practical incident-response priorities
Teams should assume that any machine that executed the malicious install hook may have exposed secrets, build tokens, or cloud credentials. That means triage should not stop at file removal; it should extend to identity and access review, repository access, and any environments reachable from the compromised host. In supply chain cases, the system that ran the package is often just the first victim. (microsoft.com)- Identify whether any installation or update resolved to Axios 1.14.1 or 0.30.4.
- Check CI/CD logs and developer shells for
[email]plain-crypto-js@4.2.1[/email]. - Hunt for the C2 domain, IP, and port 8000 traffic.
- Inspect persistence locations on Windows, macOS, and Linux.
- Revoke and rotate secrets that could have been present on affected hosts.
- Rebuild affected systems from known-good sources rather than cleaning in place. (microsoft.com)
Enterprise Versus Consumer Impact
For enterprises, the biggest concern is not a single infected endpoint but the possibility of pipeline contamination. If the malicious package was installed inside build infrastructure, it could have seen signing keys, deployment credentials, test secrets, and repository access. That creates a risk profile that is much broader than ordinary malware on an employee workstation. (microsoft.com)For consumers and independent developers, the issue is more personal but still serious. A laptop with cached cloud access, browser sessions, SSH keys, or personal wallet-related assets can become a pivot point, especially if the developer uses the same machine for side projects and production-adjacent work. In that sense, the line between personal and professional compromise is thinner than many people think. (microsoft.com)
The response should therefore differ by environment, even if the core guidance is the same. Enterprises need central visibility, automated hunting, and strict dependency controls; individuals need to assume any affected install might have touched credentials and re-establish trust from scratch. Treating both cases as “just update the package” would be a mistake. (microsoft.com)
Why secrets rotation matters
If a compromised machine had access to API keys, cloud tokens, or package publishing credentials, those secrets may remain valid long after the malware is removed. Rotating them closes the attacker’s easiest path to return and prevents hidden persistence from outlasting the visible infection. In modern supply chain incidents, credential hygiene is containment. (microsoft.com)- Build agents may have broader access than laptops.
- Personal machines can still hold production credentials.
- Shared dev boxes can expand exposure unexpectedly.
- Cached tokens often survive package removal.
- Reimaging is often safer than manual cleanup. (microsoft.com)
Strengths and Opportunities
Microsoft’s response highlights several strengths that defenders can build on. The first is that the company identified the infrastructure quickly enough to publish concrete indicators and platform-specific defenses. The second is that the detection story spans endpoint, cloud, and network layers, which is exactly what supply chain incidents require. (microsoft.com)The event also creates an opportunity for organizations to re-evaluate how they consume open-source dependencies. Many teams already know they should pin versions, but this incident shows why that advice is operationally urgent rather than theoretical. If a package can be weaponized with a single publish event, then update governance becomes a core security control. (microsoft.com)
- Pinned versions reduce exposure to surprise patch releases.
- Trusted Publishing with OIDC reduces credential storage risk.
- Ignore-scripts controls limit install-time execution.
- Hunting queries can turn threat intel into action.
- Cross-platform detections help catch blended attacks.
- Exposure graphs improve blast-radius assessment.
- Centralized logs make post-incident review faster. (microsoft.com)
Risks and Concerns
The biggest concern is that the compromise demonstrates how easily an attacker can weaponize normal developer trust. Package installs are frequent, automated, and widely dispersed, which means the attacker gets many opportunities to run code with minimal resistance. Once a build system or dev endpoint is touched, the downstream effect can be very hard to unwind. (microsoft.com)A second concern is cleanup complacency. Removing the visible malicious package does not necessarily remove cached artifacts, lockfile references, hidden persistence, or harvested secrets. Because the attack explicitly tries to erase itself and restore a clean-looking manifest, defenders who only inspect
node_modules may miss the real infection path. (microsoft.com)A third concern is that supply chain attacks can become self-reinforcing. If one compromised package infects build systems that then publish artifacts or deploy containers, the malicious code can spread through trusted channels faster than humans can manually verify each step. That is why build integrity and artifact provenance now matter as much as endpoint protection. (microsoft.com)
- Malicious updates can blend into normal patching.
- Lockfiles do not help if cache or update policy is weak.
- Hidden install scripts are hard to review manually.
- Secrets exposure can outlive malware removal.
- Cross-platform behavior complicates one-size-fits-all detection.
- Clean-looking manifests can mask compromised histories.
- CI/CD compromise can amplify the blast radius. (microsoft.com)
Looking Ahead
The most likely next phase is broader ecosystem hardening. Package publishers, registry operators, and enterprise defenders will all face renewed pressure to reduce reliance on implicit trust, especially where install-time code execution is allowed by default. This incident is a reminder that the supply chain is not just a distribution problem; it is an execution problem. (microsoft.com)We should also expect more attention on package provenance and update governance. The combination of exact version pinning, trusted publishing, and script suppression is no longer a niche best practice; it is becoming the minimum viable defense for teams that depend on open-source ecosystems. That shift may be inconvenient, but it is a rational response to the scale of the threat. (microsoft.com)
Finally, this case will likely reinforce a broader industry lesson: attackers do not need to invent new distribution channels when they can hijack trusted ones. npm, PyPI, and other package ecosystems remain attractive because they already sit inside legitimate software workflows. The more organizations can verify provenance, constrain execution, and monitor egress, the harder it becomes for a malicious publish to become a full incident. (microsoft.com)
- Expect more enforcement around exact version pinning.
- Expect stronger adoption of Trusted Publishing and OIDC.
- Expect broader use of ignore-scripts in CI pipelines.
- Expect more cross-platform detection coverage.
- Expect greater scrutiny of package provenance and maintainer identity. (microsoft.com)
Source: Microsoft Mitigating the Axios npm supply chain compromise | Microsoft Security Blog