PTC’s move to make Windchill and Codebeamer available in Microsoft’s mission cloud environments up to Department of Defense Impact Level 6 marks a meaningful step in modernizing engineering pipelines for the defense industrial base, but it also raises a new set of operational, security, and programmatic questions contractors must answer before moving classified engineering work to the cloud.
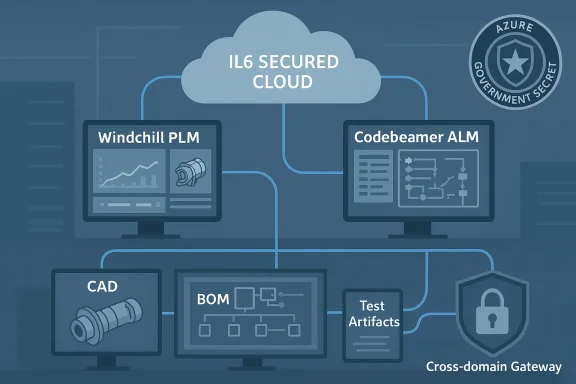
PTC announced that its flagship Windchill product lifecycle management (PLM) platform and the Codebeamer application lifecycle management (ALM) solution can now be deployed into Microsoft’s mission cloud environments that support DoD Impact Level 6 (IL6) workloads. That authorization — which aligns PTC’s digital engineering tools with Microsoft’s Azure Government Secret infrastructure — is intended to let defense primes and suppliers run end‑to‑end engineering workflows (software, firmware, systems engineering, configuration management and change control) inside cloud environments accredited for SECRET‑level data.
This development follows two parallel trends: (1) hyperscalers have invested heavily to certify and operate isolated government cloud regions that meet DoD Cloud Computing SRG IL6 requirements, and (2) platform vendors for PLM/ALM are cloud‑optimizing their suites, adding digital‑thread integrations and AI assistants to speed product development. Combining those trends promises faster iteration cycles, stronger traceability, and more responsive engineering change management — but it also introduces new governance, supply‑chain, and workforce challenges that program owners must manage deliberately.
However, the gains come with responsibilities: primes and subcontractors must invest in meticulous governance, verify accreditation and component scoping, plan for vendor portability, govern supply chains, and staff operations with cleared personnel who understand both engineering processes and classified cloud operations. Program offices should treat the cloud adoption decision as a programmatic design choice — one that changes contractual obligations, security architectures, and long‑term sustainment economics.
For program managers and CIOs evaluating this path, the immediate next steps are clear:
Source: ExecutiveBiz PTC Expands PLM, ALM Tools to Microsoft Cloud Up to IL6
 Background / Overview
Background / Overview
PTC announced that its flagship Windchill product lifecycle management (PLM) platform and the Codebeamer application lifecycle management (ALM) solution can now be deployed into Microsoft’s mission cloud environments that support DoD Impact Level 6 (IL6) workloads. That authorization — which aligns PTC’s digital engineering tools with Microsoft’s Azure Government Secret infrastructure — is intended to let defense primes and suppliers run end‑to‑end engineering workflows (software, firmware, systems engineering, configuration management and change control) inside cloud environments accredited for SECRET‑level data.This development follows two parallel trends: (1) hyperscalers have invested heavily to certify and operate isolated government cloud regions that meet DoD Cloud Computing SRG IL6 requirements, and (2) platform vendors for PLM/ALM are cloud‑optimizing their suites, adding digital‑thread integrations and AI assistants to speed product development. Combining those trends promises faster iteration cycles, stronger traceability, and more responsive engineering change management — but it also introduces new governance, supply‑chain, and workforce challenges that program owners must manage deliberately.
Why IL6 matters (a technical primer)
What “IL6” actually means
- Impact Level 6 (IL6) is the DoD Cloud Computing Security Requirements Guide designation for environments that may store, process, and transmit information up to the Collateral SECRET classification.
- An IL6 cloud must operate as a dedicated environment (physically and logically separated), have connections only into approved classified networks (for example, SIPRNet), and be staffed with cleared U.S. citizens where required by the SRG.
- IL6 accreditation imposes stricter personnel, physical, and architectural constraints than the unclassified or IL4/IL5 government clouds. This includes separation of management planes, constrained third‑party access, and tailored DoD FedRAMP+ controls.
The Microsoft context
Microsoft’s Azure Government Secret offering is an example of a hyperscaler‑run environment that has been architected and provisioned to meet or receive provisional authorizations for IL6. That environment provides services and tooling specifically scoped for classified and mission‑critical workloads, including options for dedicated regions, express private connectivity, and audited service lists suitable for defense missions.What PTC brings: Windchill and Codebeamer inside the IL6 boundary
Windchill — PLM for systems and configurations
- Windchill is PTC’s enterprise PLM offering. It centralizes product data (CAD models, bills of materials, specifications), manages configurations and variants, and automates engineering change processes. Windchill’s capabilities are important for regulated and safety‑critical sectors where traceability and configuration integrity are non‑negotiable.
- Key Windchill benefits for defense programs:
- Single source of truth for multi‑disciplinary engineering artifacts.
- Robust BOM and configuration management that maps hardware, firmware, and software components across variants.
- Change control workflows, approvals, and audit trails required for program certification and sustainment.
Codebeamer — ALM and traceability for software‑driven systems
- Codebeamer is PTC’s ALM solution focused on requirements management, traceability, test management, and release control for software and embedded systems.
- Codebeamer adds critical capabilities:
- Requirements engineering and bi‑directional traceability to tests and code.
- Test case generation, execution tracking, and evidence collection that support certification and compliance.
- Product line engineering features to manage variants and concurrent development streams.
Why the two together matter
When Windchill (PLM) and Codebeamer (ALM) run inside the same IL6 boundary they can deliver a true digital thread for defense systems. That integration enables:- Unified traceability across mechanical, electronic, and software artifacts.
- Faster, auditable engineering change execution across the enterprise.
- The ability to use governed AI assistants for requirements quality and test‑generation inside accredited environments, reducing manual bottlenecks.
Practical benefits for the Defense Industrial Base (DIB)
- Speed to secure engineering environments. Contractors can establish accredited engineering environments more quickly than building or renewing on‑premises classified datacenters, reducing setup lead time from months down to weeks for some tasks.
- End‑to‑end digital engineering. Connecting PLM and ALM inside an IL6 cloud enables end‑to‑end digital engineering workflows — requirements → design → code → test → sustainment — without forcing manual handoffs or disconnected tooling.
- Reduced dependence on legacy on‑prem systems. Many primes still run fragmented on‑prem stacks that are costly to maintain; IL6 cloud deployments let teams consolidate tooling on a managed platform.
- Facilitated teaming and supplier collaboration. When a controlled, accredited cloud tenancy is available, cleared suppliers can be onboarded formally into the same secure environment, enabling collaborative engineering while preserving separation requirements.
- Improved traceability for verification and certification. The PLM/ALM integration provides a stronger evidence trail for audits, verification, and safety/cybersecurity certification work that defense programs require.
Caveats, clarifications, and an important correction
- The recent reporting referenced a “Department of War” — that term is not accurate. The correct U.S. executive department for these designations is the Department of Defense (DoD) and the security framework is the DoD Cloud Computing SRG. Any public text that uses “Department of War” appears to be an error or shorthand; program documentation and procurement must reference DoD terminology precisely.
- I attempted to locate the primary PTC blog post cited in vendor coverage; some vendor statements and secondary reports paraphrase PTC executives. Program teams should treat vendor PR and trade coverage as a useful lead and always confirm technical and accreditation specifics directly from the vendor’s compliance documentation and the cloud provider’s IL6 audit scope before operational decisions.
Security, governance, and operational risks — what to watch closely
Running engineering tools for SECRET workloads in IL6 brings real benefits, but also new and heightened risks:1. Supply‑chain and vendor risk
- Deploying PLM/ALM in a single hyperscaler footprint can create concentration risk and potential vendor lock‑in. Programs should evaluate portability, export of data, and contractual rights to retrieve and migrate archived artifacts.
- Vendor updates, third‑party integrations, and embedded components (like open source libraries) increase the attack surface and must be governed by secure software supply‑chain processes.
2. Personnel and access controls
- IL6 environments require strict personnel controls: administrative and privileged access is often limited to cleared U.S. citizens. Prime contractors must confirm their staffing plans and vendor subcontractor access align with SRG personnel rules.
- Role‑based access and least privilege must be enforced rigorously, including multi‑factor authentication, enterprise identity federation (e.g., enterprise Entra/Active Directory patterns tailored to IL6), and privileged access management.
3. Data separation and connectivity
- IL6 controls often demand physical or virtual separation from non‑federal tenants and dedicated network connectivity into classified networks. Systems that support cross‑domain transfers (for example, moving build artifacts from IL5 to IL6) require validated cross‑domain solutions and documented transfer processes.
- Programs must design data flow diagrams that explicitly show where controlled/unclassified and classified data reside and how transitions are authorized and audited.
4. Auditability and evidence collection
- Defense acquisition requires precise evidence trails for verification. Teams must ensure PTC tooling captures immutable audit logs, tamper‑evident records, and exportable evidence packages to satisfy auditors and program offices.
- Logging, SIEM integration, and retention policies should be scoped to meet contract and DoD retention requirements.
5. Performance, latency, and operational resilience
- Running heavy CAD viewers, large BOM repositories, or automated test harnesses in an IL6 cloud can impose performance constraints if network connectivity to engineering sites is limited.
- Ensure the operational plan includes disaster recovery, offline build strategies, and network resilience for distributed engineering teams.
6. Cost and lifecycle economics
- Cloud economics for classified environments can be non‑trivial. Expect higher per‑unit compute and storage rates for dedicated regions and the cost of cleared personnel, private express routes, and cross‑domain tooling. Programs should produce realistic TCO models that include migration, validation, and sustainment.
Due diligence checklist for primes and subcontractors
Before approving a migration or standing up IL6 deployments for PLM/ALM, program owners should require the following from vendors and teammates:- Documentation that PTC Windchill and Codebeamer configurations and images have been tested and are supported in the specific Azure Government Secret regions being used.
- A complete list of PTC service components and dependent services (database engines, middleware, plug‑ins). For each component, confirm IL6 compliance or identify compensating controls if components remain IL5 or lower.
- Identity and access plan showing which accounts are in IL6, which are federated to enterprise directories, and who will hold privileged roles (with clearance level and citizenship demonstrated).
- Network and cross‑domain data transfer architecture that maps pathways to SIPRNet, appropriate cross‑domain solutions, and approval authority for transfers.
- Backup, archive, and e‑discovery policies aligned to contract requirements. Confirm where immutable backups are stored and the export process for evidentiary artifacts.
- Penetration testing, red‑team, and independent security assessment plans that reflect IL6 scope and include periodic cycles in production‑like environments.
- A rollback and data extraction plan that allows program owners to export full product and traceability data in a vendor‑neutral format in the event of termination or migration.
- SLA and incident response commitments tailored to classified operations, including 24/7 support with cleared personnel.
Migration and implementation: practical steps
- Inventory and classification
- Classify artifacts (requirements, designs, code, models) to determine which elements require IL6 and which can remain at lower impact levels.
- Pilot tenancy and smoke tests
- Begin with a narrow, cleared pilot: host a small project in IL6 to test integrations, workflows, and evidence collection end‑to‑end.
- Validate cross‑domain and transfer mechanisms
- Where artifacts must move between impact levels, validate cross‑domain solutions per DoD guidance and produce approved transfer rules.
- Harden configurations and baseline images
- Establish hardened golden images for Windchill, Codebeamer, and associated middleware with approved security baselines and automated provisioning.
- Integrate audit and SIEM
- Ensure logs, workflow artifacts, and change events are forwarded to an IL6‑authorized SIEM and are retained to contractual retention windows.
- Train cleared staff and lock down privileges
- Conduct role‑based training, simulate incident response, and implement strict PAM controls for administration.
- Execute phased cutover
- Migrate incrementally, maintaining a parallel on‑prem/legacy system for contingency.
- Continuous validation
- Maintain ongoing compliance testing, automatic policy checks, and periodic third‑party audits.
Strategic implications for program managers and CIOs
- The combination of enterprise PLM and ALM inside IL6‑accredited clouds redefines how defense systems are engineered: design reviews, test evidence, configuration control, and release packages can be consolidated and governed within a single secure digital thread.
- For acquisition program managers, the option to host classified engineering artifacts in accredited hyperscaler clouds shortens the path to collaborative engineering across cleared contractors, but it transfers a larger share of operational risk to cloud and platform vendors. Contract language, SLAs, and vendor accountability clauses must evolve to reflect that shift.
- For CIOs, the new model demands investments in cloud governance, cleared staffing, and continuous compliance automation. It also invites rethinking hardware and network architectures to minimize latency and ensure high‑integrity CI/CD pipelines for regulated products.
Strengths and opportunities
- Scalability and speed. Accredited cloud environments enable rapid scaling of compute for simulations, automated testing, and large‑scale baselining tasks that were previously constrained by on‑prem hardware.
- Improved traceability and audit readiness. Integrated PLM/ALM platforms inside IL6 can materially improve evidentiary posture for certification, safety, and cybersecurity audits.
- AI‑assisted engineering. When governed AI features are available inside accredited boundaries, teams can automate quality checks, assist requirements writing, and accelerate test generation — all within a controlled environment that mitigates data leakage risks.
- Supplier collaboration. A well‑designed IL6 tenancy can create a formal, auditable path for cleared suppliers to collaborate without ad‑hoc exchange mechanisms or insecure enclaves.
Risks and open questions
- Vendor lock‑in and portability. How easily can a program extract its digital thread and migrate to another vendor or environment? Portable, standards‑based exports are essential.
- Hidden dependencies. Many PLM/ALM ecosystems include third‑party connectors and services that may not be IL6 accredited. Programs must identify and eliminate or replace those dependencies.
- People and process. The cloud does not eliminate the need for disciplined engineering governance, configuration management, and human diligence — it amplifies the need.
- Cost predictability. Classified cloud consumption (compute, storage, private connectivity, cleared staffing) can be significantly more expensive than unclassified cloud; program accountants must plan for recurring IL6 costs over long system lifecycles.
- Transparency of vendor claims. Public reports and press coverage may summarize vendor statements; program teams should confirm vendor attestations and architecture descriptions with vendor compliance materials and the cloud provider’s IL6 audit scope.
Conclusion — a balanced assessment
PTC’s capability to run Windchill and Codebeamer in Microsoft’s IL6‑accredited mission clouds is a practical enabler for modern digital engineering in the defense sector. It can reduce the friction of collaborating across cleared teams, accelerate engineering cycles through stronger traceability and governed AI, and shift many infrastructure burdens to the cloud provider. Those are real advantages at a time when time‑to‑capability matters.However, the gains come with responsibilities: primes and subcontractors must invest in meticulous governance, verify accreditation and component scoping, plan for vendor portability, govern supply chains, and staff operations with cleared personnel who understand both engineering processes and classified cloud operations. Program offices should treat the cloud adoption decision as a programmatic design choice — one that changes contractual obligations, security architectures, and long‑term sustainment economics.
For program managers and CIOs evaluating this path, the immediate next steps are clear:
- Require vendor and cloud provider evidence of IL6 scoping for every service component you intend to use.
- Run a narrow, instrumented pilot that validates traceability, cross‑domain transfer, and evidence export.
- Build procurement language that preserves data portability and enforces timely incident response from vendors operating within the classified tenancy.
Source: ExecutiveBiz PTC Expands PLM, ALM Tools to Microsoft Cloud Up to IL6
