AI agents are no longer isolated curiosities; they are multiplying inside enterprise software, and the question now is how to stop a thousand useful assistants from becoming a thousand incompatible problems.
By spring 2025, enterprise adoption of AI had moved well past pilots: major industry surveys show roughly three‑quarters of organisations now use AI in at least one business function, and generative AI in particular has spread rapidly across departments. McKinsey’s Global Survey reported that about 78% of organisations use AI in at least one business function and that 71% report regular use of generative AI in at least one function. . PwC’s May 2025 executive survey found that 79% of surveyed organisations report AI‑agent adoption inside their companies and that many firms are already reporting measurable productivity gains from those agents. .
Those numbers explain the explosion of vendor-built assistants: Microsoft 365 Copilot, Salesforce Agentforce, SAP Joule, Notion AI, ServiceNow Copilot, and dozens more are now embedded where people work. The immediate upside is clear: employees get AI help in the flow of work, reducing context switching and speeding routine tasks. The less visible downside is fragmentation — a proliferation of agents, each with its own data view, permissions, and UI — producing inconsistent experiences, duplicated integration effort, and new operational risk.
This feature examines how organisations can orchestrate these agents into a single coherent system, the architecture and governance that makes that possible, vendor strategies to watch, and the practical steps IT leaders must adopt to capture value while avoiding the fragmentation trap.
Key manifestations:
The technical building blocks are emerging now: identity‑bound agents, model routers, shared memories, open protocols like MCP, and enterprise observability. The hard work is organisational and operational: instituting AgentOps, policy‑as‑code, and disciplined evaluation. Companies that build that operational muscle while keeping their architectures open will turn agentic promise into measurable, sustainable value; those that do not will see their AI estate fracture into a costly patchwork of isolated assistants.
Source: The AI Journal Orchestrating AI Agents into one System | The AI Journal
 Background / Overview
Background / Overview
By spring 2025, enterprise adoption of AI had moved well past pilots: major industry surveys show roughly three‑quarters of organisations now use AI in at least one business function, and generative AI in particular has spread rapidly across departments. McKinsey’s Global Survey reported that about 78% of organisations use AI in at least one business function and that 71% report regular use of generative AI in at least one function. . PwC’s May 2025 executive survey found that 79% of surveyed organisations report AI‑agent adoption inside their companies and that many firms are already reporting measurable productivity gains from those agents. .Those numbers explain the explosion of vendor-built assistants: Microsoft 365 Copilot, Salesforce Agentforce, SAP Joule, Notion AI, ServiceNow Copilot, and dozens more are now embedded where people work. The immediate upside is clear: employees get AI help in the flow of work, reducing context switching and speeding routine tasks. The less visible downside is fragmentation — a proliferation of agents, each with its own data view, permissions, and UI — producing inconsistent experiences, duplicated integration effort, and new operational risk.
This feature examines how organisations can orchestrate these agents into a single coherent system, the architecture and governance that makes that possible, vendor strategies to watch, and the practical steps IT leaders must adopt to capture value while avoiding the fragmentation trap.
The current landscape: proliferation and the fragmentation paradox
What’s driving agent sprawl
Enterprise software vendors are embedding specialised AI agents directly into their products because it increases stickiness and immediate user value. The combination of easy-to-use copilots and zero‑friction in‑app experiences has prompted rapid departmental uptake, especially in sales, marketing, customer service, and IT operations. Service vendors and system integrators are now packaging “agent ecosystems” so lines of business can spin up domain‑tuned assistants quickly. Microsoft’s Agent Framework, Copilot Studio, and Azure AI Foundry — and numerous partner offerings layered on top — illustrate how vendor stacks are evolving to make agent creation, deployment and scaling simpler for enterprise customers.The fragmentation paradox
The more agents an organisation deploys, the more intelligence becomes locked inside app-specific boundaries. The result is a paradox: after years of digital transformation aimed at breaking down silos, AI agents can re-create them — but now with the added complexity of model choice, conversational memory, and action permissions.Key manifestations:
- Inconsistent user experience — different assistants use different prompts, strengths, and UI metaphors; employees must learn many tiny tools instead of one coherent assistant.
- Onboarding & training overheads — each agent carries unique behaviors and guardrails; training scales poorly with the number of agents.
- Vendor lock‑in & strategic risk — embedding deep AI capabilities into a single vendor’s stack can accelerate adoption but also reduce flexibility and bargaining power over time.
- Data silos & lack of cross‑agent memory — agents usually only see their platform’s data; task hand‑offs across systems require bespoke integrations or manual intervention.
Why orchestration — and a “central AI front door” — matters
From many assistants to a coordinated team
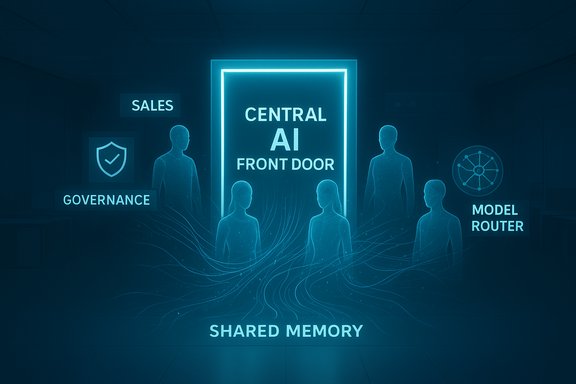
Orchestration is the design principle that turns isolated agents into a coordinated system. The idea is straightforward: instead of training users to pick the right assistant for each task, provide a single entry point (a central AI front door) that accepts intent and routes the work to the best‑suited agent behind the scenes. That front door can:- Normalize the conversational surface so employees use a consistent interface.
- Route requests dynamically to specialist agents or models based on task type, data sensitivity, or cost constraints.
- Maintain shared context and a persistent memory layer so agents can hand off tasks without losing state.
- Enforce common governance, auditing, and approval flows.
Two architecture patterns enterprises should consider
- Vendor‑anchored orchestration (the “Copilot as browser” model)
- Pros: rapid integration for customers already embedded in the vendor’s stack, consistent UX, first‑party governance primitives (identity, DLP, telemetry).
- Cons: risk of deep lock‑in; limited flexibility to mix best‑of‑breed agents when vendor controls connectors and runtime.
- Middleware / AgentOps control plane (the “AI mesh” model)
- Pros: vendor‑neutral orchestration, centralised policy and lifecycle management, easier multi‑model routing and third‑party marketplaces.
- Cons: requires additional integration work; introduces another operational plane to manage.
The technical foundations of a unified agent system
A usable, auditable, secure orchestration layer needs several concrete technical primitives. These are not theoretical — major platform announcements and solution blueprints emphasize these exact pieces.1) Identity-first agents
Treat agents like first‑class directory objects. Assign an identity, owner, cost centre and lifecycle to every agent so actions are attributable and revocable. Microsoft’s Entra Agent ID model and vendor integrations demonstrate why identity is the starting point for auditability and least‑privilege enforcement.2) Interoperability protocols
Open protocols such as the Model Context Protocol (MCP) are designed to let models discover and invoke tools in a standard way; they reduce bespoke connector work and enable third‑party services to be called consistently across agent runtimes. Anthropic’s MCP and the industry’s adoption narrative show that a common protocol materially lowers integration friction — but also introduces new security patterns that must be tested.3) Shared memory & data contracts
A central memory or contextual layer (a versioned, policy‑governed knowledge store) lets multiple agents share state and context. This avoids repeated retrieval work, enables coherent long‑running workflows, and supports traceable decisions. Vendors are building “Foundry IQ” or “Fabric IQ”-style semantic layers to provide that shared context.4) Model/router economics
Multi‑model routing lets the orchestration layer pick the right model for the job — small local models for high‑frequency tasks, larger models for reasoning or synthesis — reducing cost and latency while preserving capability. Microsoft and others are packaging model catalogs and routers in their runtimes to make this practical.5) Observability, tracing and tamper‑evidence
Every action an agent takes must be traceable from intent to tool call to final output. OpenTelemetry integration, immutable audit logs, and runtime traceability are now standard requirements in enterprise blueprints for agentic systems. These capabilities let security teams reconstruct incidents and compliance teams produce evidence for auditors.Governance, security and the human‑in‑the‑loop imperative
Policy-as-code and runtime enforcement
Policy should be expressed declaratively and enforced at runtime. That means using policy-as-code repositories, pre-deployment policy validation, and policy gates during agent execution (for example: “this action needs manager approval” or “redact PII before sending outside the tenant”). This approach turns governance into testable artifacts rather than manual checklists. ServiceNow, Microsoft and other ecosystem players are building control towers and CMDB integrations to make policy enforcement more visible at scale.Human oversight where it matters
Agents can be enabled to act autonomously for routine, low‑risk operations, but irreversible or high‑impact actions should retain human approvals. The consensus among enterprise playbooks is clear: human‑in‑the‑loop (HITL) gating for critical actions is mandatory until systems achieve robust, auditable, repeatable reliability.Attack surface and data leakage
Allowing agents to access multiple back‑end systems increases the attack surface. Key mitigations include: least‑privilege connectors, ephemeral credentials, session‑limited tokens, strict network egress controls, and runtime DLP checks. Independent research on MCP servers also highlights novel attack patterns and the need for MCP‑specific security scanning as part of agent pipelines. Treat vendor claims about “enterprise‑grade” safety as conditional on an organisation’s own controls and audits.A practical AgentOps playbook for enterprise IT
To move from theory to production, IT organisations need a phased, measurable program. The following numbered playbook synthesises vendor guidance, independent analysis and early enterprise best practice.- Inventory & classify
- Create an agent registry: list every agent, owner, scope, connectors, and business purpose. Treat agents like services in your CMDB from day one.
- Start with high‑value, low‑blast‑radius pilots
- Pick a repetitive, well‑measured process (ticket triage, meeting summarization, invoice classification) with clear KPIs before widening scope.
- Define data sensitivity and action-level guardrails
- Map what data each agent may access and what actions it may perform autonomously. Use policy-as-code to bake this into CI checks.
- Use identity & ephemeral access
- Bind agents to directory identities; require short‑lived tokens for tool invocations and enforce least privilege for connectors.
- Bake observability into ALM
- Store prompt templates, evaluation artifacts and telemetry in source control; run CI-driven tests on agent behavior before promoting to production.
- Implement staged autonomy
- Start with suggestion mode → supervised execution → limited autonomous execution for low-risk tasks; require human approval for high‑impact actions.
- Cost & model routing controls
- Implement hybrid routing, cache expensive outputs, and meter model usage to avoid runaway inference costs. Benchmarks and model choices must be part of procurement.
- Red team & adversarial testing
- Include prompt‑injection, tool poisoning and data‑poisoning tests in pre‑release checks; maintain a rotating program of adversarial review.
- Institutionalise deprovisioning
- Automate the retirement of unused agents and require cost‑centers to justify ongoing charges to limit sprawl.
- Measure business value
- Track bottom‑line metrics (MTTR, cost per incident, cycle time reductions, revenue impact) not just usage counts. Vendors’ pilot ROI claims exist — validate them in your context.
Vendor strategies and market implications
Microsoft: platform + distribution advantage
Microsoft is explicitly positioning Copilot and Foundry as an orchestration stack — a front door that can route intents to specialist agents, enforce identity and policy, and provide an enterprise catalog for agent discovery. For organisations already invested in Microsoft 365 and Azure, the Copilot model offers rapid time‑to‑value and built‑in governance — but it also concentrates strategic dependency in one vendor’s control plane. The industry sees this as analogous to how a browser once became the default gateway to the web: convenient, pervasive, and strategically consequential.Middleware and specialist AgentOps providers
Systems integrators and independent platform players (Neudesic, VAST, third‑party AgentOps vendors) are building control planes that sit on top of hyperscaler runtimes. These offerings aim to provide the governance, lifecycle and enterprise controls that big customers want while preserving multi‑cloud and multi‑model flexibility. For large regulated customers the appeal is clear: a neutral operations plane reduces business risk and preserves the option to switch model providers.Standards and the open agentic web
Open protocols such as MCP and emerging Agent‑to‑Agent (A2A) messaging are central to a vendor‑neutral future. Industry consolidation around these protocols — and nascent foundations intended to steward them — makes cross‑vendor composition realistic. That said, early adoption of any standard is always messy: incompatible extensions, fragmented implementations, and new security patterns will need coordinated remediation. Organisations should prefer MCP‑compatible connectors and demand the ability to swap model routers without rewiring business logic.Risks, blind spots and unresolved questions
- Operational debt & skills gap: Building and running orchestrated agent fleets requires new disciplines (AgentOps): policy engineers, prompt/version governance, model evaluators and trace analysts. Many organisations underestimate the skills and organisational change needed to scale safely.
- Overclaiming by vendors: Vendor ROI claims are frequently pilot‑based. Independent verification and careful measurement are necessary before broad rollouts. Treat vendor case studies as starting hypotheses to validate against internal benchmarks.
- Regulatory and legal exposure: Agents that act autonomously raise questions about liability, record keeping and accountability. How regulators will treat agent identities and the assignments of responsibility remains unsettled in many jurisdictions. Design for traceability and legal defensibility from day one.
- Standards uncertainty: MCP and related protocols show strong momentum, but competing specs or fragmented implementations could still emerge. Organisations should prefer protocol‑friendly architectures and keep a strategic abstraction layer to avoid single‑protocol lock‑in.
- Security of protocol ecosystems: MCP and agent protocols introduce new attack vectors (tool poisoning, MCP‑specific vulnerabilities). Security tooling, code scanning, and runtime enforcement need to mature to match traditional software supply chain practices.
- Specific vendor roadmap timelines and “general availability” dates announced at conferences should be treated as vendor signals, not as committed delivery dates unless documented in formal release notes. Some vendor feature claims are previewed at events and may change; those event claims were cross‑checked with vendor blogs and technical documentation where available.
Final assessment: pragmatic orchestration beats reflexive consolidation
The path to a coherent enterprise agent system is not about destroying embedded copilots — it is about connecting them. Organisations should aim for a pragmatic middle path: keep the productivity of in‑app copilots, but unify identity, context, policy, and observability through an orchestration plane or trusted vendor control plane. That unified layer should:- Provide a consistent conversational front end so users don’t have to choose the “right” bot;
- Maintain a governed memory and semantic layer for shared context;
- Route work dynamically across models, balancing cost and capability;
- Make agents first‑class, auditable, identity‑bound services; and
- Treat AgentOps as a necessary operational discipline, not an optional checkbox.
Conclusion
AI agents are fundamentally changing how work gets done, but their sheer number creates a new systems problem. The solution is not fewer agents; it is better orchestration. A central AI front door — whether provided by a vendor platform like Copilot, a middleware AgentOps control plane, or an internally built AI mesh — is the foundational element organisations must implement to scale agentic productivity safely.The technical building blocks are emerging now: identity‑bound agents, model routers, shared memories, open protocols like MCP, and enterprise observability. The hard work is organisational and operational: instituting AgentOps, policy‑as‑code, and disciplined evaluation. Companies that build that operational muscle while keeping their architectures open will turn agentic promise into measurable, sustainable value; those that do not will see their AI estate fracture into a costly patchwork of isolated assistants.
Source: The AI Journal Orchestrating AI Agents into one System | The AI Journal