After more than a decade of being labeled “unhackable,” the original Xbox One—the bulky 2013 “VCR” Durango model bundled with Kinect—has finally been shown to run unsigned code thanks to a hardware-level attack demonstrated at RE//verse 2026, a development that lands squarely at the intersection of hardware security, game preservation, and the old-school console-modding ecosystem.
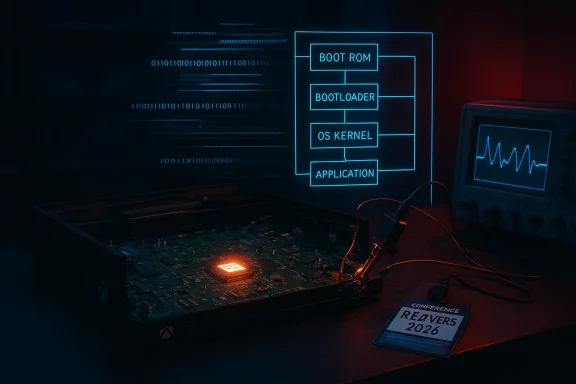
The Xbox One’s security model was designed around a layered chain of trust that puts cryptographic checks and a minimal, hardened boot ROM at the absolute root of the platform. That boot ROM is burned into the console’s custom AMD system-on-chip and is responsible for verifying every component that loads afterward. Microsoft deliberately kept it tiny and conservative to minimize attack surface; for years that decision made the console one of the toughest mainstream targets for jailbreaks and custom firmware.
At launch in 2013 the original Xbox One (codename Durango) shipped as a very particular hardware revision—the model many collectors call the “VCR” Xbox One because of its long, boxy chassis and original power brick design. Over the console’s life Microsoft deployed internal revisions and firmware updates, and the developer ecosystem matured to the point where Microsoft now offers an official Developer Mode that allows unsigned UWP-style applications in a sanctioned environment. That reality has reduced the practical incentives for large-scale jailbreaks compared with older eras, but a true boot‑ROM compromise still represents a major technical milestone for researchers and preservationists.
The talk explained that the attack is not a single, brute-force interruption. It’s a patient, instrumented process of probing, timing, and refinement—what Gaasedelen described as stacking “scraps of signal” and weaponizing subtle side effects to pry open a fortress designed to resist exactly this kind of manipulation. The demonstration reportedly required multiple, carefully timed glitch pulses in sequence; when both were delivered correctly the research team was able to achieve code execution at the boot ROM level and break the chain of trust that had protected the platform for years.
Community reporting and thread-level reactions have been brisk: enthusiasts and scene sites have flagged the RE//verse presentation as a watershed because it attacks the smallest, most trusted piece of Xbox One silicon rather than merely an updatable firmware component. Independent coverage and scene commentary place the talk and the demo in the conference’s hardware-attacks track, and community threads confirm the general outline of the technique and the presenter.
For players and collectors, the immediate effect is modest: expect community discussion, careful analysis from preservation groups, and a slow trickle of technical write-ups rather than a sudden flood of consumer-facing jailbreak tools. For Microsoft and other console vendors, this is another reminder that hardware-level security is a moving target: a design that looks impenetrable on paper can still be vulnerable to time, talent, and a laboratory’s worth of patience. The conversation that follows—about disclosure, stewardship of dumped data, and how to balance preservation with intellectual property protection—will be the real legacy of this breakthrough.
Source: Windows Central The original Xbox One was reportedly jailbroken — 13 years later
 Background / Overview
Background / Overview
The Xbox One’s security model was designed around a layered chain of trust that puts cryptographic checks and a minimal, hardened boot ROM at the absolute root of the platform. That boot ROM is burned into the console’s custom AMD system-on-chip and is responsible for verifying every component that loads afterward. Microsoft deliberately kept it tiny and conservative to minimize attack surface; for years that decision made the console one of the toughest mainstream targets for jailbreaks and custom firmware.At launch in 2013 the original Xbox One (codename Durango) shipped as a very particular hardware revision—the model many collectors call the “VCR” Xbox One because of its long, boxy chassis and original power brick design. Over the console’s life Microsoft deployed internal revisions and firmware updates, and the developer ecosystem matured to the point where Microsoft now offers an official Developer Mode that allows unsigned UWP-style applications in a sanctioned environment. That reality has reduced the practical incentives for large-scale jailbreaks compared with older eras, but a true boot‑ROM compromise still represents a major technical milestone for researchers and preservationists.
What happened at RE//verse 2026
During RE//verse 2026, researcher Markus Gaasedelen presented a full hardware attack on the Xbox One’s earliest boot stage. The core technique used is a form of fault injection known as voltage glitching: by deliberately and precisely disrupting the console’s power rail at well-timed instants during early boot, the attacker causes the processor to mis-execute critical instructions in the boot ROM. This can defeat signature checks and chain-of-trust enforcement long before the main operating system ever loads.The talk explained that the attack is not a single, brute-force interruption. It’s a patient, instrumented process of probing, timing, and refinement—what Gaasedelen described as stacking “scraps of signal” and weaponizing subtle side effects to pry open a fortress designed to resist exactly this kind of manipulation. The demonstration reportedly required multiple, carefully timed glitch pulses in sequence; when both were delivered correctly the research team was able to achieve code execution at the boot ROM level and break the chain of trust that had protected the platform for years.
Community reporting and thread-level reactions have been brisk: enthusiasts and scene sites have flagged the RE//verse presentation as a watershed because it attacks the smallest, most trusted piece of Xbox One silicon rather than merely an updatable firmware component. Independent coverage and scene commentary place the talk and the demo in the conference’s hardware-attacks track, and community threads confirm the general outline of the technique and the presenter.
How the exploit works (high-level, non-actionable)
Below is a technical, but non-actionable, summary of the steps the researchers described. This is intended to explain the attack for informed readers, not to provide a recipe for misuse.- Identify the boot ROM entry points and the CPU state transitions during the earliest microseconds of boot. This requires hardware instrumentation and patience.
- Attach a fault-injection rig capable of delivering sub-microsecond voltage glitches to selected rails, while observing power, clock, and memory signals.
- Deliver a sequence of precisely timed voltage glitches that cause the processor to transiently misfetch or mis-decode instructions at the moment the boot ROM performs signature checks.
- Detect the timing window where instruction mis-execution yields a bypass (for example, skipping a conditional branch or corrupting a comparison).
- Use the transient bypass to move execution into a controlled region (often by influencing an exception path or corrupting a pointer), then persist control—commonly by patching a boot stage in RAM or by redirecting execution to a small payload.
- Once code execution in an early stage is available, instrument and extract internal state, dump protected regions, and stage persistent modifications where possible.
Why this matters: technical significance and practical impact
- Root-level compromise: The boot ROM is the earliest, most trusted code on the platform. Running unsigned code at that level means you can study and manipulate later stages without needing any vendor signatures. That’s a leap beyond user-mode or kernel exploits.
- Research and preservation: For historians, preservationists, and reverse engineers, this unlocks the ability to extract internal firmware and inspect proprietary formats—vital steps for dumping game assets, documenting system internals, and enabling future emulation or archival work. The community around console preservation has long argued that true hardware-level access is essential for accurate archival of closed platforms; this work delivers exactly that capability for the original Xbox One, at least on units amenable to the attack.
- Proof-of-concept, not mass jailbreak: Early reports suggest the exploit is highly targeted, physically invasive, and expensive to reproduce at scale. Unlike userland hacks that can be spread as files, this attack requires hardware fault-injection setups and deep timing calibration—barriers that keep the technique firmly in the domain of researchers and specialized modders for now. Where the exploit lands on the practical/political spectrum depends on whether participants publicize detailed instructions or produce turnkey hardware tools.
- Preservation vs. piracy debate: A year of community dialogue separates legitimate preservation goals (archival, enabling emulation, saving abandonware) from the risk that such capabilities enable piracy. The research community typically frames hardware attacks like this as a route to knowledge and preservation, but platform owners and rights holders will rightly raise alarms if the paths provided are co-opted for distributing pirated content.
Limitations, caveats, and unverifiable claims
- Revision-dependent: Multiple early signals from the hobbyist community suggest the vulnerability may only exist in the very first Xbox One motherboard revisions, and later hardware revisions patched the vulnerable behavior—either by silicon re-spin or minor design changes. That pattern is common with hardware faults: a design quirk in launch silicon can be fixed in subsequent runs. I could not independently verify the exact revision numbers or the proportion of retail units affected; until lower-level data (chip batch info, motherboard IDs) is published, treat claims on scope with caution.
- Complexity and cost: The attack is not cheap. You need oscilloscope-grade measurement equipment, a reliable glitcher rig, fine soldering or interposer hardware, and the time to map signals and tune glitch timing. That reality limits the audience to researchers and invested collectors rather than casual users.
- No immediate mass-market effect: Because the attack requires physical access and bespoke equipment, it does not produce a simple “jailbreak file” you can drop onto a console. Organizations with an interest in quickly blockading a mass-exploit distribution (e.g., Microsoft) retain tools to limit the consequence: they can keep online services gated to signed consoles, detect altered consoles on Xbox Live, and maintain legal and enforcement mechanisms. Still, for offline preservation work and local research, Microsoft’s remote defenses are less relevant.
- Ethical and legal risk: Demonstrating research at a conference is within normal security-research norms, but distributing full exploit details can have legal consequences in some jurisdictions and may prompt takedowns or DMCA-style responses. Researchers often balance disclosure against misuse risk; how Gaasedelen and colleagues handle that balance will shape how the community uses the work.
What this unlocks for homebrew, emulation, and preservation
- Game dumping and firmware extraction: Boot ROM access enables safe dumping of protected firmware blobs and possibly decryption keys or boot-stage code needed to fully document system behavior. For archivists trying to ensure that Xbox One-era games survive beyond corporate hosting, that’s a very tangible benefit.
- Low-level emulation accuracy: Accurate emulators depend on detailed knowledge of hardware quirks, timing, and privileged code behavior. Having the ability to observe and instrument the platform yields emulation artifacts that are far more faithful than black-box reverse engineering. This work could help projects attempting to emulate Xbox One-level behavior at a cycle-accurate level.
- Homebrew that actually runs natively: Developer Mode and sanctioned app platforms already allow enthusiasts to create UWP apps and simple emulators on Xbox One and Series consoles. What a boot ROM compromise offers that Developer Mode does not is the ability to run arbitrary native privileged code—not just sandboxed user apps. That expands the range of possible experiments, from porting alternative OSes to enabling deeper hardware-level mods. However, this comes with a much higher risk of bricking or hardware damage for inexperienced tinkerers.
Security implications for Microsoft and console ecosystems
- Not the end of security: Microsoft’s broader security posture—attestation, signed updates, and telemetry—still provides layers of defense for modern consoles and services. A local hardware compromise does not automatically grant cloud-level trust or entitlement. For Microsoft, the real risk is in erosion of platform guarantees and the potential for the exploit to enable cheats, piracy, or breach of online services if paired with other vulnerabilities.
- Patchability limits: Silicon-level faults (or boot ROM logic burned into chips) are only mitigated for already-manufactured units by vendor-side compensations (firmware mitigations where possible) or by updating cloud-side attestation. For units with unfixable hardware issues, the practical outcome is often compartmentalized: fewer consoles are exploitable, and the economics of producing a robust mass-exploit remain poor.
- Legal and enforcement responses: Historically, platform vendors have used legal tools, service bans, and firmware updates to respond to jailbreaks. With a hardware-only attack, Microsoft’s takedown options are narrower, but enforcement via Live bans and removal of online functionality remains effective. The company also has the option of quietly altering service requirements or telemetry to make altered consoles unable to access the networked ecosystem. Expect measured responses rather than dramatic public pronouncements—particularly when the research is framed as preservation-focused.
Responsible disclosure and community expectations
Good-faith hardware research walks a narrow ethical line. Demonstrating a proof-of-concept at a conference educates platform owners and the security community, but public distribution of low-level exploit code can enable misuse. Responsible disclosure typically consists of:- Coordinating with the vendor where possible prior to broad publication.
- Publishing technical details that advance defensive research without providing trivial replication steps for bad actors.
- Ensuring preservation and archival goals are foregrounded (for instance, securely transferring dumped firmware to recognized archives or museums).
What collectors and enthusiasts should know right now
- If your unit is a launch-era revision, it might be of interest to researchers and collectors—both because those early boards may be attackable and because fixed later revisions will be rarer relative to the installed base. However, opening and instrumenting a unit for glitching can be destructive; don’t assume you’ll get your console back in the same state.
- Don’t expect a one-click jailbreak: The technique demonstrated is a laboratory-grade hardware fault-injection exploit. For everyday users wanting to run emulators, the official Developer Mode remains a safer path and will remain the practical option for the foreseeable future.
- Legal grey areas: Depending on where you live, attempting to replicate the attack or distributing exploit tools could violate local computer misuse or copyright laws. Proceed only with clear legal advice and community awareness of the consequences.
A balanced view: strengths, risks, and the road ahead
Strengths and positives
- Technical milestone: Breaking a boot ROM long considered impenetrable is a notable achievement for the security and reverse-engineering communities; it advances collective knowledge about hardened embedded systems.
- Preservation value: Access at this level can unlock the console’s internals for archival dumps, which helps preserve gaming history and enables more accurate emulation work.
- Research spin-offs: Techniques refined here can inform defensive research—improving fault-detection, power-domain monitoring, and future platform hardening.
Risks and downsides
- Potential misuse: Any capability that enables unsigned code at the root of the platform could be repurposed for piracy, cheats, or other harmful behavior.
- Hardware damage and scarcity: The technique can destroy hardware if mishandled, and exploitable units may be scarce. That raises the risk that the archive/knowledge benefits will be limited in practice.
- Community fragmentation: The conversation will split between preservationists, modders, and those worried about IP protection. That debate will shape disclosure choices and community norms going forward.
Conclusion
The RE//verse 2026 demonstration that the original Xbox One boot ROM is vulnerable to a carefully crafted voltage-glitching attack closes a long chapter in console reverse engineering: the platform that many considered “unhackable” has been probed at its most trusted layer. That result is a win for deep technical research and for those committed to preserving gaming history, but it comes with predictable caveats—limited scope, substantial practical barriers, legal and ethical considerations, and real risks if the work is misused.For players and collectors, the immediate effect is modest: expect community discussion, careful analysis from preservation groups, and a slow trickle of technical write-ups rather than a sudden flood of consumer-facing jailbreak tools. For Microsoft and other console vendors, this is another reminder that hardware-level security is a moving target: a design that looks impenetrable on paper can still be vulnerable to time, talent, and a laboratory’s worth of patience. The conversation that follows—about disclosure, stewardship of dumped data, and how to balance preservation with intellectual property protection—will be the real legacy of this breakthrough.
Source: Windows Central The original Xbox One was reportedly jailbroken — 13 years later