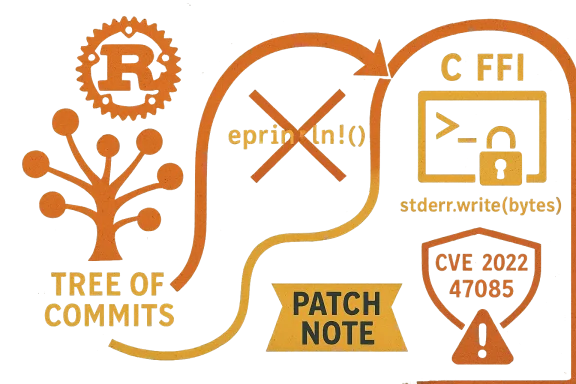
A panic-printing helper in OSTree’s Rust bindings quietly opened a path to denial-of-service: a small, unsafe panic-handling routine in rust-bindings/src/repo_checkout_at_options/repo_checkout_filter.rs could itself panic while trying to report a prior panic, producing a double-unwind or abort scenario that allows an attacker to crash or otherwise render OSTree-driven components unavailable. The defect is tracked as CVE-2022-47085, affects OSTree releases before the 2022.7 / 0.17.1 line, and was fixed by replacing eprintln!-based reporting with a conservative, direct stderr write in a committed patch. (github.com)
OSTree is a content-addressed object store and deployment system that underpins several “immutable” Linux distributions and components — notably rpm-ostree, Flatpak tooling, Silverblue, and many IoT or container-oriented images. OSTree’s architecture blends Git-like commits for filesystem trees with runtime deployment mechanics; parts of the codebase are implemented in Rust and bound into C interfaces used by packaging and deployment layers. That mixed-language boundary (Rust panics crossing FFI boundaries) is the precise place this vulnerability manifested.
The vulnerability was reported, triaged and fixed upstream in 2023; vendor advisories and distribution errata subsequently reflected the issue and recommended upgrades. Public tracking entries show the flaw was acknowledged by common vulnerability databases and security tooling, and vendors including Red Hat and other groups included the CVE in their advisories and scan plugins.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
OSTree is a content-addressed object store and deployment system that underpins several “immutable” Linux distributions and components — notably rpm-ostree, Flatpak tooling, Silverblue, and many IoT or container-oriented images. OSTree’s architecture blends Git-like commits for filesystem trees with runtime deployment mechanics; parts of the codebase are implemented in Rust and bound into C interfaces used by packaging and deployment layers. That mixed-language boundary (Rust panics crossing FFI boundaries) is the precise place this vulnerability manifested.The vulnerability was reported, triaged and fixed upstream in 2023; vendor advisories and distribution errata subsequently reflected the issue and recommended upgrades. Public tracking entries show the flaw was acknowledged by common vulnerability databases and security tooling, and vendors including Red Hat and other groups included the CVE in their advisories and scan plugins.
What happened: technical root cause
The panic path and double-unwind danger
Rust prohibits unwinding across FFI boundaries — letting a Rust panic propagate out through C code leads to undefined behavior and usually results in an abort. In OSTree’s Rust bindings, the function responsible for printing panic values, named print_panic, attempted to use Rust’s high-level eprintln! macro to emit diagnostic text when a callback panicked. If the act of writing that message itself caused an error (for example, if eprintln! panicked under low-memory or I/O failure conditions), OSTree could end up in a double-panic or other undefined scenario that ultimately aborts or destabilizes the process. The code change committed to fix the issue removed the use of eprintln! and instead acquires a locked handle to stderr and writes bytes directly, swallowing write failures to avoid triggering a second panic. (github.com)Why the failure matters operationally
The immediate operational consequence is a loss of availability: OSTree is often a core component of update and runtime deployment for systems that rely on rpm-ostree or Flatpak content distribution. If a remote or local input sequence can cause the codepath that runs Rust callbacks to panic, and the panic-reporting itself then panics, the end result can be a process abort or crash. For services that route package pulls, image deployments, or repository checkouts through OSTree, a crash can stop upgrades, prevent new images from being deployed, or disrupt system boot paths that depend on deployed commits — in short, it can deny new or continued access to critical resources. This availability-centric impact is reflected in vendor severity assessments.Affected versions and scope
- Upstream OSTree: all versions before the 2022.7 (also referenced as 0.17.1) release line are affected. The upstream fix is included in the 0.17.1 changeset.
- Distributions: because OSTree is embedded into other packaging and runtime stacks, the practical exposure surface depends on how a given distribution packages OSTree and which consumers rely on it. At the time of disclosure and after, several distribution advisories and scan plugins listed the CVE and produced hotfixes or errata entries. Tools that scan for vulnerable dependencies (Nessus/Tenable, Red Hat errata, Snyk/OSS security feeds) also cataloged the vulnerability.
- Key note on reachability: the vulnerability is not necessarily self-contained as a network service bug; exploitability depends on whether a panic can be triggered through inputs seen in the relevant OSTree consumers (for example, malformed repo content, malicious repository metadata served to clients, or crafted runtime inputs to rust callbacks). In practice, maintainers treated the defect as a serious availability issue and moved to fix or backport the change into stable branches.
How the upstream fix addresses the problem
The patch merged into the upstream repository makes three practical changes inside the print_panic helper:- Stop using the eprintln! macro for panic diagnostics because eprintln! uses higher-level formatting infrastructure that can itself panic under extreme conditions.
- Use std:
 :stderr(), lock the handle, and use write_all to write a static diagnostic message and the panic string directly as bytes.
:stderr(), lock the handle, and use write_all to write a static diagnostic message and the panic string directly as bytes. - Treat write failures as non-fatal and ignore them (write errors are mapped to a discarded result), explicitly avoiding any code path that could cause a second panic while handling an earlier one.
Exploitability and practical risk
Can the vulnerability be exploited remotely?
Exploitability depends on whether a reachable input will cause a Rust callback to panic inside the affected codepath and whether an attacker can trigger that behavior remotely. Some OSTree consumers expose network-facing surfaces (for example, clients pulling from remote repositories or servers offering updates), so remote exploitation cannot be categorically ruled out. Distribution advisories and scanning engines treated the issue as a denial-of-service risk and assigned it high availability impact in several advisories.What an attacker can achieve
- Repeated triggering of the panic path can cause application crashes, leading to sustained unavailability while the attacker continues exploitation.
- In certain deployment topologies, a crash could block updates or new deployments until an operator intervenes — this may be especially disruptive in immutable-OS workflows where OSTree-controlled deployments are central to system state changes.
- There is no public record of privilege escalation or code execution tied to this CVE; the primary, documented consequence is denial-of-service. (If you require definitive exploit code or POC status, note that proof-of-concept artifacts were not broadly published in trusted advisories at the time of the upstream fix. Treat any third-party claims cautiously.)
Scoring and severity
Different databases applied slightly different severities. NVD’s public description recorded the issue and referenced the upstream change, while vendor and scanning sources (Red Hat / Snyk) assigned a CVSS-like high rating in their advisories and contexts, emphasizing a total loss of availability risk. Use the vendor advisories that apply to your distribution as the authoritative severity for your environment.Which distributions and stacks should you check?
Because OSTree is used as a library by several projects, you must verify each distribution and stack where OSTree is present:- Immutable Fedora variants (Silverblue, Kinoite): OSTree and rpm-ostree are core components. Users reported related breakages during June–July 2023 when packages incorporating the upstream changes were rolling out. Operators should verify package versions and ensure the fix has been included.
- Flatpak and related tooling: Flatpak uses OSTree for content addressing; Flatpak users and maintainers often reacted to OSTree library updates. If your environment uses Flatpak runtimes or repos, ensure the underlying OSTree libraries are patched. Community threads from mid-2023 discussed observable failures in flatpak interactions tied to OSTree updates.
- Embedded / IoT images and vendor builds: OSTree is common in device images where immutable updates are used. Check vendor errata and supply-chain notices for patches or backports to platform-specific OSTree packages. Distribution advisories and vendor errata feeds are the place to confirm backports.
- Containers and build systems: any CI pipelines or container images that include the OSTree library should be scanned; supply-chain scanning tools and SBOMs help identify affected images. The vulnerability is tracked in GitHub advisories and dependency databases used by modern toolchains.
Recommended immediate actions (for admins and maintainers)
- Inventory: locate all systems, packages, images, and containers that include OSTree or rpm-ostree. Use your package manager and SBOM tools to enumerate OSTree versions in use. This is the single most important first step.
- Patch: upgrade OSTree to the fixed release (0.17.1 / 2022.7 or later) or install distribution-specific security updates that backport the fix. Vendors and advisories list the fixed versions; ensure you apply the update that matches your platform’s packaging.
- Restart & verify: after applying patches, restart affected services and perform basic repository operations (pulls, checkouts, deployments) in a controlled environment to confirm the crash condition no longer reproduces.
- If you can’t patch immediately: mitigate exposure by restricting untrusted inputs to OSTree consumers. For network-facing deployment endpoints, consider limiting access via firewall rules, VPN, or other network segmentation until updates are available.
- Monitor: set up or check existing monitoring for process crashes, core dumps, and repeated restart loops for services that use OSTree. High rates of panics or repeated aborts are a clear sign of unresolved issues.
- Scan: run dependency scanners and container image scans (Nessus, Snyk, distro-specific scanners). Many scanners already include plugins or signatures for CVE-2022-47085.
Detection and hunting guidance
- Look for patterns of process aborts or restarts in logs related to rpm-ostree, ostree, flatpak, or any custom service that calls into OSTree’s C bindings.
- Search for kernel oops, crash logs, or coredumps timestamped around package pulls or repo checkouts; these may indicate an abrupt abort caused by double-panic behavior.
- Use runtime instrumentation (strace/ltrace) in staging environments to validate panic paths do not lead to aborts after patching.
- If you maintain a fleet, consider rolling patching windows prioritized by exposure: network-facing update servers and developer workstations should be higher priority than offline build hosts.
Why this kind of bug is important and what it teaches us
- Mixed-language boundaries are dangerous: Rust’s safety guarantees don’t extend across FFI boundaries. Panic semantics must be carefully managed where Rust and C interoperate, and diagnostics code must be written so it cannot fail while handling a prior failure.
- Small, low-level changes can have outsized operational impact: the fix was small (switching from eprintln! to a locked stderr write), but the potential disruption — crashing update services and blocking deployments — was large.
- The supply-chain effect: OSTree is not an end-user app but a foundational library; a flaw here ripples through Flatpak runtimes, immutable OS images, and vendor update stacks. That’s why security tooling and distribution errata tracked the CVE and why operators must treat library-level CVEs seriously across their stack. (github.com)
Risk analysis: strengths and remaining considerations
- Strengths of the upstream response:
- The project issued a targeted fix that follows defensive coding best-practices for FFI unwinding.
- The fix is minimal and straightforward to backport, easing distribution-level remediation and decreasing the window where systems remain vulnerable. (github.com)
- Remaining risks and caveats:
- Not all distributions backport fixes at the same cadence; some enterprise distributions may retain older OSTree package names or have different versioning semantics. Administrators must confirm patch availability in vendor channels rather than relying on upstream tags alone.
- The overall exploitability in a particular environment depends on how easily a Rust callback can be induced to panic via reachable inputs. Where that input path exists and is externally reachable, risk is higher.
- Public exploit code was not a mainstream artifact at the time of the fix; s reduces immediate wildfire risk but doesn’t eliminate targeted exploitation potential. Treat claims on unverified exploit traffic cautiously.
Practical checklist for operators
- Inventory OSTree usage across your organization (clients, servers, images).
- Confirm OSTree package versions — upgrade to 0.17.1 / 2022.7 or to vendor-supplied patched packages where available.
- Apply updates first to update infra (repo servers, rpm-ostree servers), then to clients.
- After updating, validate repository pulls and image checkouts in a test environment.
- Monitor for crash signatures and repeaters; set alerts on abnormal restart or core dump rates.
- If immediate patching is not possible, restrict access and follow network segmentation until fixes are applied.
Community signals and discussion
Public forums and distribution issue trackers recorded observable breakages around the time the issue was fixed and patched into rolling distributions, with users reporting Flatpak and rpm-ostree operation problems until patched packages propagated. These discussions reflect an important operational reality: even when upstream makes a small, correct fix, the remediation timeline is governed by distribution packaging, CI cadence, and mirror propagation. Administrators should keep these realities in mind during incident response and remediation.Conclusion
CVE-2022-47085 is a classic example of how subtle interactions at language boundaries (Rust panics crossing into C) can create high-availability consequences for otherwise well-architected systems. The upstream patch is precise and conservative — replacing a panic-prone diagnostic path with a minimal, non-panicking write to stderr — and should be applied wherever OSTree is used in production. Operators must treat OSTree as a foundational component: inventory its presence, prioritize fixes for update servers and image deployment tooling, and validate that distribution-specific backports are applied. Vigilant patching, combined with process monitoring and limited exposure of update endpoints, will close the window of risk and restore the robust availability expectations that OSTree-based deployments promise. (github.com)Source: MSRC Security Update Guide - Microsoft Security Response Center