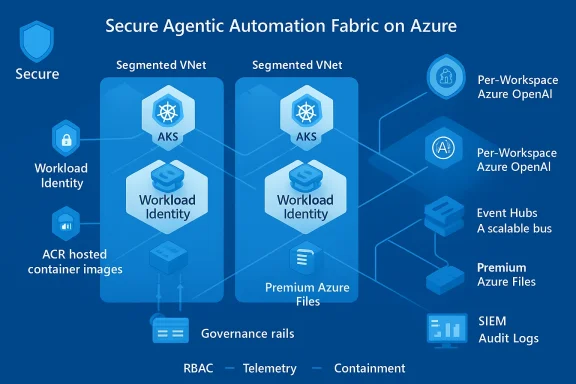
Overcut’s approach to agentic automation is a study in restraint: deliver autonomous, multi‑step workflows that actually fit inside enterprise operational boundaries rather than promising unbounded autonomy. The company builds its execution plane on Azure primitives—AKS for orchestration, Azure AD identities for workload access, ACR for verified runtimes, Event Hubs for the workflow bus, Premium Azure Files for shared storage, and a per‑workspace Azure OpenAI deployment for model reasoning—so each agent runs inside an observable, identity‑driven, network‑segmented environment that enterprises already understand and can govern.
Enterprises face a familiar paradox: they need the speed and creativity that agentic automation delivers, yet they cannot accept the operational and compliance risks that often come with early AI systems. Overcut positions itself not as a developer productivity toy but as a controlled automation fabric for the software development lifecycle (SDLC)—ticket triage, root cause analysis, test generation, remediation, release preparation, migrations, and documentation—where each agent is a short‑lived worker that must be auditable, isolated, and identity‑bound. This design decision follows an industry pattern where enterprise adoption is driven less by model quality and more by governance, integration, and lifecycle controls. Microsoft’s emerging agent ecosystem and enterprise primitives—tenant‑scoped grounding, agent identities, private network options, and observability—are central operational. Several vendor and platform analyses reinforce that enterprises need a management plane for agents—cataloging, RBAC, telemetry and remediation—before agent fleets can move from pilots to production.
At the same time, enterprises and founders must not mistake platform foundations for finished governance. Model behavior, cost management, supply‑chain security, and identity bookkeeping remain active operational responsibilities. In sum, the path to enterprise‑ready agentic automation is less about the size of the model and more about the quality of the controls—and Overcut’s architecture shows one practical way to build that control plane on Azure.
Source: Microsoft Design enterprise‑ready agentic workflows on Azure with Overcut
 Background / Overview
Background / Overview
Enterprises face a familiar paradox: they need the speed and creativity that agentic automation delivers, yet they cannot accept the operational and compliance risks that often come with early AI systems. Overcut positions itself not as a developer productivity toy but as a controlled automation fabric for the software development lifecycle (SDLC)—ticket triage, root cause analysis, test generation, remediation, release preparation, migrations, and documentation—where each agent is a short‑lived worker that must be auditable, isolated, and identity‑bound. This design decision follows an industry pattern where enterprise adoption is driven less by model quality and more by governance, integration, and lifecycle controls. Microsoft’s emerging agent ecosystem and enterprise primitives—tenant‑scoped grounding, agent identities, private network options, and observability—are central operational. Several vendor and platform analyses reinforce that enterprises need a management plane for agents—cataloging, RBAC, telemetry and remediation—before agent fleets can move from pilots to production.Why Azure as the foundation
Overcut’s choice to build natively on Azure is pragmatic and tactical. Azure supplies a broad set of managed services that remove infrastructure plumbing from the product roadmap while providing enterprise‑grade controls:- Identity and least‑privilege through Microsoft Entra / Azure AD and workload identity patterns.
- Isolated networking via Azure Virtual Network (VNet), private endpoints, and managed NAT for predictable egress IPs.
- Managed compute and storage (AKS, Azure Files Premium, ACR, Azure Database for PostgreSQL Flexible Server) for production reliability and regional data residency.
- Managed AI with per‑workspace Azure OpenAI deployments to confine AI processing to a tenant and region.
Architecture: Controlled autonomy by design
Overcut’s architecture centers on a single operating principle: agents must be powerful, but never uncontrolled. Below is a concise breakdown of the core infrastructure choices and how they map to enterprise requirements.Azure Kubernetes Service (AKS) — orchestration backbone
Overcut runs its execution engine and microservices on Azure Kubernetes Service (AKS) to orchestrate and scale agent workloads. AKS provides elasticity for spikes (incident response, mass migrations) and lets Overcut run thousands of isolated agents in parallel. Importantly, Overcut uses workload identity patterns rather than long‑lived static secrets—AKS integrates with Microsoft Entra Workload ID so pods can securely obtain Azure tokens without credential files. This reduces secret sprawl and simplifies rotation. Key operational benefits:- Dynamic scaling to match workflow demand.
- Identity‑based access for platform components (no embedded secrets).
- Reduced operational overhead compared to VM fleets.
Network isolation — VNets and NAT Gateway
Every Overcut component lives in segmented subnets with Network Security Groups enforcing east‑west rules. Outbound traffic is normalized through an Azure NAT Gateway so customer allow‑lists and external integrations see consistent IP addresses. This network‑first posture matches expectations for regulated environments where egress control and private interconnects are mandatory. Azure’s NAT Gateway and managed NAT options support AKS clusters directly, which simplifies creating deterministic outbound paths for ephemeral agents.Container images — Azure Container Registry (ACR)
Agent runtimes are delivered as container images stored and signed in Azure Container Registry. Overcut relies on federated pull identities so AKS can retrieve images securely without embedded credentials, preserving image provenance and reducing tamper risk. Managed identity‑based ACR pulls are a common enterprise best practice that avoids static secrets and enables RBAC on registries.Durable state — Azure Database for PostgreSQL Flexible Server
Workflow metadata, agent state, and execution history need durability and regional residency guarantees. Overcut uses Azure Database for PostgreSQL Flexible Server, which provides managed patching, automated backups, zone‑redundant high availability (where available), and private endpoint support for VNet‑only access. This keeps audit trails inside the tenant’s network while giving operational resilience for production workloads. Operational note: Flexible Server supports high‑availability modes and private endpoints, but specifics such as AZ support and maintenance windows must be validated per region and SKU during procurement and architecture reviews.High‑performance shared storage — Azure Files Premium (CSI)
Agentic workflows often mount large code repositories and temporary state across containers. Overcut uses Azure Files Premium accessed through the CSI driver to provide low‑latency, persistent shared volumes across pods. The AKS‑native CSI support and Premium storage classes reduce I/O bottlenecks in parallel executions and enable efficient cache reuse between ephemeral agents.Event-driven orchestration — Azure Event Hubs (Kafka‑compatible)
For a scalable internal workflow bus, Overcut leverages Azure Event Hubs with its Kafka‑compatible interface. This permits reuse of existing Kafka producers/consumers and gives elastic throughput for event‑driven agent orchestration. Event Hubs’ managed service model reduces operational overhead compared to self‑hosted Kafka while preserving familiar developer APIs.Private, compliant AI — Azure OpenAI per workspace
Crucially, Overcut assigns each customer workspace a dedicated Azure OpenAI deployment scoped to a region. That approach keeps prompts, embeddings, and inference within a defined geographic boundary, simplifies regulatory compliance, and reduces cross‑tenant data leakage risk. Microsoft’s enterprise guidance emphasizes that Azure OpenAI resources remain under tenant control and are not used to train foundation models without explicit agreement—an important contractual and operational boundary for regulated customers.Front‑end and CI/CD — Azure Static Web Apps and GitHub Actions
The user interface and tenant portal are hosted via Azure Static Web Apps, with CI/CD pipelines delivered through GitHub Actions for staged, zero‑downtime releases. Static Web Apps automates global distribution, SSL management, and staging environments for pull requests—helping Overcut ship UI changes quickly while preserving a predictable release model.What Overcut automates (real enterprise workflows)
Overcut focuses on enterprise SDLC processes rather than single‑user prompts. Key workflow templates it supports include:- Ticket triage, prioritization, and assignment across Jira/Azure DevOps.
- Root cause analysis and automated runbook suggestions during incidents.
- Test generation and automated test orchestration integrated with CI systems.
- Remediation and patch candidate generation with human approval gates.
- Migrations and large‑scale refactor orchestration with dependency analysis.
- Release preparation work: changelogs, release notes, and preflight checks.
Security, governance, and observability — the operational controls
The difference between an interesting demo and production adoption is governance. Overcut centers these controls:- Identity‑first security: agents and services run with Entra identities and workload identity tokens, which allows access reviews, conditional access, and lifecycle management similar to human or service identities.
- Network isolation: VNets, private endpoints, and managed NAT give predictable egress and ensure traffic flows follow enterprise policy.
- Tamper‑resistant images: images are stored and governed in ACR with role assignments instead of secret pull keys.
- Auditable state: persistent state and logs live in managed services with backup and HA guarantees (PostgreSQL Flexible Server, Event Hubs).
- Model confinement: per‑workspace OpenAI deployments keep data residency tight and inference within the chosen region.
- Observability: traces, spans, and tool calls are surfaced to enterprise monitoring so decisions and tool invocations can be reconstructed for audits. This mirrors Microsoft’s agent telemetry themes and industry guidance for agent traceability.
Strengths: why this approach resonates with enterprises
- Operational parity with existing systems
By using the same identity, networking, and observability primitives that enterprises already operate, Overcut reduces the conceptual and compliance gap between traditional services and agentic automation. Enterprises can treat agent runs like any other service activity. - Deterministic governance
Agents are short‑lived, identity‑bound, and run in segmented networks—this makes it feasible to enforce least‑privilege, revoke access, or quarantine an agent without disrupting unrelated workloads. - Scalable orchestration
AKS + Event Hubs enables parallel execution at scale while preserving telemetry and audit records, which is crucial for mass rollout across multiple teams and projects. - Regional compliance and latency
Per‑workspace Azure OpenAI deployments deliver predictable inference latency and help satisfy data‑residency constraints that regulated customers require. - Faster GTM and reduced infra work
Building on managed services accelerates product development and reduces the team’s burden to maintain edge infrastructure—important for startups scaling into enterprise sales.
Risks, limitations, and pragmatic trade‑offs
No architecture is without trade‑offs. The key risks organizations and founders should weigh:- Model risk and hallucinations
Agents that synthesize remediation steps, write code, or alter configurations can produce incorrect or risky outputs. Overcut’s architecture mitigates this with guardrails and human‑in‑the‑loop validations, but the underlying model behavior remains a risk that must be managed with verification steps and safety checks. - Cost and runaway compute
Agentic systems can spawn many parallel model calls and container workloads. Without strict quotas, environment‑level budgets, or rate limits, customers risk unexpected bills. Implement usage caps, shadow deployments, and cost‑alerting during pilots. - Supply‑chain and image security
Although ACR with federated pull reduces credential risk, image provenance and supply‑chain integrity still require signing, vulnerability scanning, and runtime attestation to prevent compromised agents from executing. Use image signing, vulnerability scanning, and runtime policies. - **Operational complexity o
Workload identity and identity binding features introduce new operational artefacts (federated credentials, service account mappings). Large platform deployments must account for quotas and automation required to provision identity bindings at scale. Validate limits and automation paths during design. - Data residency and regulatory nuance
Per‑workspace OpenAI deployments are a big step toward compliance, but customers must verify processing vs. storage locality, logging policies, and contractual commitments (DPA/ADD) when subject matter is regulated. Microsoft’s commitments are explicit, but organizational legal and security teams must validate contracts and configurations. - Edge cases and human escalation
Agents are good at routine, repeatable work; they struggle with ambiguous, context‑heavy edge cases. Overcut’s platform includes human gates, but designing those handoffs and fail‑safe playbooks is nontrivial and must be part of project scoping. - Vendor lock‑in and integration risk
Building tightly on Azure simplifies operations for Azure‑first customers but raises migration frictiohybrid estates, teams should evaluate abstraction patterns (APIs, MCP servers) and a clear export path for workflows and data.
Practical checklist for enterprise adopters
- Secure the agent identity model
- Use workload identity, policy‑driven RBAC, and automated provisioning/rotation. Validate federated identity quotas and cluster requirements.
- Build deterministic network egress and allow‑lists
- Assign NAT gateways and document egress IPs for external integrations. Test connectivity with production endpoints early.
- Constrain model consumption and cost
- Implement rate limits, quota alerts, and plan for tiered model routing (cheap models for routine tasks, high‑quality models for critical operations). Consider shadow routing trials.
- Harden container supply chain
- Sign and scan images in ACR; enforce pull policies via managed identities.
- Validate data residency end‑to‑end
- Confirm where prompts, embeddings, and logs are processed and retained for Azure OpenAI and any retrieval stores. Review contractual data protections.
- Define human‑in‑the‑loop policies and SLAs
- Specify when manual validation is required, how to escalate, and retention policies for audit trails.
- Monitor and rehearse incident playbooks
- Ensure observability surfaces (traces, Event Hubs topics, DB logs) are integrated with SIEM and incident runbooks for rapid triage.
Developer and product lessons for founders building agentic SDLC platforms
- Enterprise adoption is governed by trust, not novelty. Teams will prioritize identity, audibility, and predictable costs over flashier model demos. Overcut’s emphasis on controlled autonomy is a pragmatic blueprint for founder teams aiming for enterprise customers.
- Build with platform primitives in mind. Foundational services (AKS, ACR, managed databases, VNet primitives, per‑tenant AI deployments) accelerate procurement and reduce surprises during security reviews. Document exactly how you use each primitive so procurement and cloud teams can audit decisions quickly.
- Offer integration patterns, not just connectors. Enterprises value well‑defined patterns—prebuilt workflow templates, a policy catalog, and deterministic handoff behaviors—over bespoke integrations that become operational nightmares.
- Design for observability from day one. Trace model calls, tool invocations, data retrievals, and agent state transitions. Make these trails queryable in the tenant’s monitoring tooling.
- Prepare for compliance and procurement friction. Legal and security teams will request data maps, retention policies, and DPA addenda for model and telemetry storage. Early alignment prevents long procurement cycles.
Conclusion
Overcut’s Azure‑native fabric is a pragmatic answer to a hard enterprise problem: how to bring goal‑driven, agentic automation into SDLC workflows without sacrificing control. The platform’s design—identity‑bound agents, network isolation, verified runtimes, managed model deployments, and durable telemetry—targets the precise objections that prevent pilots from scaling into production. By leaning on managed Azure services, Overcut shortens operational lead time and gives buyers the guardrails they require.At the same time, enterprises and founders must not mistake platform foundations for finished governance. Model behavior, cost management, supply‑chain security, and identity bookkeeping remain active operational responsibilities. In sum, the path to enterprise‑ready agentic automation is less about the size of the model and more about the quality of the controls—and Overcut’s architecture shows one practical way to build that control plane on Azure.
Source: Microsoft Design enterprise‑ready agentic workflows on Azure with Overcut
