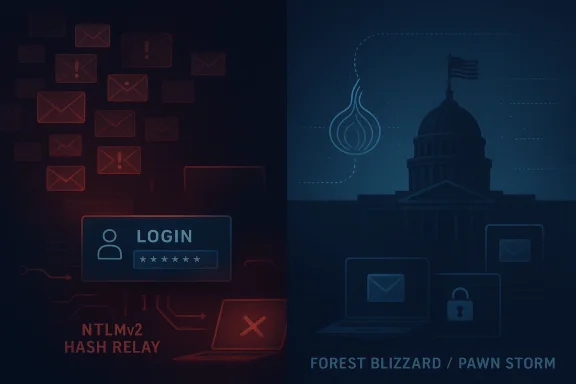
Pawn Storm’s latest campaign is a reminder that the most dangerous intrusions are often the ones that look repetitive on the surface. Trend Micro’s analysis describes a threat actor better known as APT28 or Forest Blizzard using a mix of loud brute-force activity, long-running phishing, and stealthy post-compromise tradecraft against high-value government and defense targets. The key takeaway is not that the group is clumsy, but that its volume and persistence may be part of the design: noisy operations help camouflage quieter, more consequential access operations. Microsoft’s own reporting on Forest Blizzard reinforces that this actor continues to use password spraying, spear phishing, and NTLM abuse in a way that remains highly relevant to defenders. (microsoft.com)
Pawn Storm is one of those threat names that has accumulated layers over time. Security vendors have tracked the cluster under labels including APT28, Fancy Bear, STRONTIUM, and now Forest Blizzard, reflecting both the challenge of attribution and the evolution of naming conventions across vendors. Microsoft’s current actor profile explicitly connects Forest Blizzard with APT28 and Fancy Bear, while listing Russia as the country of origin and identifying a broad set of sectors and countries that have been repeatedly targeted. (microsoft.com)
Historically, the group became known for campaigns against governments, diplomats, military organizations, and think tanks. Trend Micro’s older research shows that this was never a narrow operation; even a decade ago, Pawn Storm was already directing phishing infrastructure at ministries of defense, foreign affairs offices, and military organizations across multiple countries. That long arc matters because it shows the actor’s strategic continuity: the targets change, the lure themes adapt, but the mission remains aligned to intelligence collection and access.
What changes in the 2024 Trend Micro write-up is the framing. The company argues that the repetitive attacks are not just background noise; they are an operational feature that helps cover the real intrusion path. The report ties the campaign to Net-NTLMv2 hash relay attempts and says the activity spanned regions including Europe, North America, South America, Asia, Africa, and the Middle East. That breadth makes the campaign look less like a narrow spear-phishing operation and more like a large-scale access-finding machine. (trendmicro.com)
Microsoft’s reporting gives the story more technical weight. In its investigation of CVE-2023-23397, Microsoft said Forest Blizzard was actively exploiting the Outlook vulnerability to obtain unauthorized access to Exchange email accounts and that evidence of potential exploitation could be traced as far back as April 2022. Microsoft also explained that the exploit can trigger a Net-NTLMv2 hash leak with very few forensic artifacts, which is exactly the kind of low-noise, high-value access path that makes repeated brute-force campaigns so effective. (microsoft.com)
The result is a more nuanced picture than “old-school phishing.” Pawn Storm appears to combine simple credential collection, relay attacks, and stealthier follow-on activity in the same broader campaign architecture. That blend is what makes the actor enduring: not sophistication in every step, but enough sophistication at the right step. (microsoft.com)
The “reputation” point is not academic. Once a group is known for a certain style of compromise, defenders can easily underestimate it as noisy or stale. That can create a dangerous blind spot, because the most effective phases of the intrusion may occur after the initial spam wave or brute-force burst has already been dismissed as routine. That is why Trend Micro’s emphasis on stealth after the foothold is significant. (trendmicro.com)
That matters because relaying a captured hash is different from stealing a password in the traditional sense. The attacker may never need the user’s cleartext credentials, and the user may never need to click anything if Outlook is open when the malicious reminder is triggered. In other words, this is an attack path designed to exploit trust in normal authentication flows rather than user mistake alone. (microsoft.com)
Microsoft’s CVE guidance says the vulnerability leaves few traditional endpoint artifacts, which increases the value of logging and server-side telemetry. That means defenders must think in terms of identity traces, mailbox behavior, Exchange logs, and unusual authentication activity, not just malware alerts. The security lesson is that a weakly monitored identity layer can make a low-complexity exploit feel far more advanced than it really is. (microsoft.com)
Brute force sounds unsophisticated because it is easy to explain. But in modern campaigns, it is often paired with infrastructure rotation, proxying, and distributed operations that make it harder to block at the network edge. The fact that the actor can keep this behavior going for months suggests not naiveté, but operational discipline and patience. (microsoft.com)
The broader implication is that defenders cannot treat “password attacks” as low priority just because they are common. A well-timed spray against high-value mailboxes, admins, or exposed services can have outsized strategic impact, especially when paired with subsequent relay or mailbox manipulation. Repetition becomes a way to find the weakest seam in a large and complex organization. (microsoft.com)
Microsoft’s report on Forest Blizzard also shows that the group adapts its lure set over time, including exploitation of newer vulnerabilities and reuse of spear-phishing in support of state objectives. The pattern is consistent with a professionalized intelligence operation that treats each campaign as both access attempt and reconnaissance event. (microsoft.com)
This is especially important in government and defense circles, where a single compromised account can reveal correspondence patterns or lead to secondary targeting. A mailbox is not just a mailbox when it can become a delivery platform for later-stage compromise. That is why mailbox access is often the real prize, not merely a metric of compromise. (microsoft.com)
This matters because mailbox compromise changes the attacker’s economics. Once inside, the group can use trusted accounts and internal context to bypass suspicion that would normally be triggered by external phishing. From a defender’s perspective, the attack has shifted from perimeter abuse to identity abuse. (microsoft.com)
Trend Micro’s framing is especially useful here because it reminds readers that brute-force and phishing are only the opening act. If defenders only measure the initial intrusion, they will miss the more damaging layer that follows. The technical and operational challenge is to detect when normal collaboration tools have been turned into attacker infrastructure. (microsoft.com)
Microsoft’s Forest Blizzard profile similarly lists government, diplomatic and defense entities, think tanks, NGOs, higher education, IT services, and defense contractors as targets. The overlap between vendor reporting is strong enough to support a clear conclusion: this is an intelligence-driven actor with interests far beyond any single vertical. (microsoft.com)
Geography also matters. Trend Micro says it observed targeting across Europe, North America, South America, Asia, Africa, and the Middle East. That global footprint indicates that the campaign is not simply opportunistic spam; it is likely guided by strategic collection priorities and infrastructure availability.
Microsoft’s reporting adds another layer by showing that the actor keeps combining public exploits, custom tooling, and credential abuse. Its 2024 analysis of GooseEgg demonstrates that Forest Blizzard continues to invest in custom post-compromise capabilities for credential extraction. That indicates a mature actor that can mix commodity techniques with bespoke tools depending on the objective.
It also means the security community should be careful about dismissing familiar groups as “solved.” In reality, the most resilient threat actors are those that preserve what works, discard what fails, and layer in just enough innovation to keep pace with defenses. That is a pragmatic form of sophistication. (microsoft.com)
This means the defensive model cannot be siloed. Email security teams need to coordinate with identity teams, cloud security teams, and SOC analysts who can correlate unusual mailbox activity with authentication events. A classic single-control approach will miss the multi-stage nature of the intrusion. (microsoft.com)
Security teams should also be skeptical of “normal” account behavior that suddenly changes in subtle ways. A trusted mailbox sending unusual messages, an account that authenticates from a new region, or a permission change in an inbox can all be signs of a deeper compromise. That kind of detection requires context, not just alerts. (microsoft.com)
There is also a wider strategic lesson here. APTs do not need to be glamorous to be effective, and the most dangerous campaigns are often the ones that look familiar enough to ignore. If defenders internalize anything from this reporting, it should be that repetition is not reassurance; in the hands of a patient state-linked operator, repetition can be camouflage. (trendmicro.com)
Source: www.trendmicro.com Pawn Storm Uses Brute Force and Stealth Against High-Value Targets
 Background
Background
Pawn Storm is one of those threat names that has accumulated layers over time. Security vendors have tracked the cluster under labels including APT28, Fancy Bear, STRONTIUM, and now Forest Blizzard, reflecting both the challenge of attribution and the evolution of naming conventions across vendors. Microsoft’s current actor profile explicitly connects Forest Blizzard with APT28 and Fancy Bear, while listing Russia as the country of origin and identifying a broad set of sectors and countries that have been repeatedly targeted. (microsoft.com)Historically, the group became known for campaigns against governments, diplomats, military organizations, and think tanks. Trend Micro’s older research shows that this was never a narrow operation; even a decade ago, Pawn Storm was already directing phishing infrastructure at ministries of defense, foreign affairs offices, and military organizations across multiple countries. That long arc matters because it shows the actor’s strategic continuity: the targets change, the lure themes adapt, but the mission remains aligned to intelligence collection and access.
What changes in the 2024 Trend Micro write-up is the framing. The company argues that the repetitive attacks are not just background noise; they are an operational feature that helps cover the real intrusion path. The report ties the campaign to Net-NTLMv2 hash relay attempts and says the activity spanned regions including Europe, North America, South America, Asia, Africa, and the Middle East. That breadth makes the campaign look less like a narrow spear-phishing operation and more like a large-scale access-finding machine. (trendmicro.com)
Microsoft’s reporting gives the story more technical weight. In its investigation of CVE-2023-23397, Microsoft said Forest Blizzard was actively exploiting the Outlook vulnerability to obtain unauthorized access to Exchange email accounts and that evidence of potential exploitation could be traced as far back as April 2022. Microsoft also explained that the exploit can trigger a Net-NTLMv2 hash leak with very few forensic artifacts, which is exactly the kind of low-noise, high-value access path that makes repeated brute-force campaigns so effective. (microsoft.com)
The result is a more nuanced picture than “old-school phishing.” Pawn Storm appears to combine simple credential collection, relay attacks, and stealthier follow-on activity in the same broader campaign architecture. That blend is what makes the actor enduring: not sophistication in every step, but enough sophistication at the right step. (microsoft.com)
Why the Group’s Reputation Still Matters
A lot of threat reporting falls into the trap of equating novelty with danger. Pawn Storm is a useful counterexample because its methods can look dated while its outcomes remain severe. Microsoft says Forest Blizzard uses spear phishing, web-facing application exploitation, and an automated password spray/brute-force tool operating through Tor. That is not flashy tradecraft, but it is a reliable one-two punch: find credentials, then use them to persist or move laterally. (microsoft.com)Brand equity in cybercrime
Groups like Pawn Storm also benefit from operational brand recognition inside the security community. Defenders may recognize patterns, but so do attackers; a well-established actor can reuse infrastructure, train operators, and refine lures across many targets. The continuity of this actor’s playbook suggests a mature pipeline for tasking, collection, and retention. (microsoft.com)The “reputation” point is not academic. Once a group is known for a certain style of compromise, defenders can easily underestimate it as noisy or stale. That can create a dangerous blind spot, because the most effective phases of the intrusion may occur after the initial spam wave or brute-force burst has already been dismissed as routine. That is why Trend Micro’s emphasis on stealth after the foothold is significant. (trendmicro.com)
- Repetition can be a masking strategy, not a sign of weakness.
- Old phishing infrastructure can still be highly effective against unprepared organizations.
- Credential theft remains valuable because it bypasses some perimeter defenses.
- The actor’s long history makes correlation across incidents easier for defenders.
- Persistent targeting increases the odds of eventual compromise.
The NTLMv2 Relay Angle
The technical center of gravity in this report is the use of Net-NTLMv2 hash relay attempts. Microsoft explains that CVE-2023-23397 can trigger a hash leak when a specially crafted Outlook message causes a connection to a threat-actor-controlled SMB server. Once the hash is captured, it can be relayed for authentication against systems that support NTLMv2 or used offline for password cracking. (microsoft.com)That matters because relaying a captured hash is different from stealing a password in the traditional sense. The attacker may never need the user’s cleartext credentials, and the user may never need to click anything if Outlook is open when the malicious reminder is triggered. In other words, this is an attack path designed to exploit trust in normal authentication flows rather than user mistake alone. (microsoft.com)
Why relay attacks are attractive
Relay attacks are attractive because they scale. A threat actor can automate the collection of hashes, test them against infrastructure, and use successful relays to jump into email or server environments. This turns what looks like a narrow phishing problem into a wider identity and authentication problem. (microsoft.com)Microsoft’s CVE guidance says the vulnerability leaves few traditional endpoint artifacts, which increases the value of logging and server-side telemetry. That means defenders must think in terms of identity traces, mailbox behavior, Exchange logs, and unusual authentication activity, not just malware alerts. The security lesson is that a weakly monitored identity layer can make a low-complexity exploit feel far more advanced than it really is. (microsoft.com)
- Hash relay is dangerous because it bypasses password disclosure requirements.
- Outlook and Exchange are especially sensitive to this kind of abuse.
- Minimal endpoint traces make detection harder than with commodity malware.
- A successful relay can become a stepping stone to persistence.
- Identity telemetry is as important as endpoint telemetry.
Brute Force at Scale
Trend Micro’s argument is that brute force is not a fallback for Pawn Storm; it is part of the business model. The report says the group launched NTLMv2 hash relay attacks from roughly April 2022 through November 2023, with peaks in target volume and variations in government departments targeted. Microsoft also notes that Forest Blizzard uses an automated password spray/brute-force tool over Tor, which underscores the actor’s preference for scalable credential access. (trendmicro.com)Brute force sounds unsophisticated because it is easy to explain. But in modern campaigns, it is often paired with infrastructure rotation, proxying, and distributed operations that make it harder to block at the network edge. The fact that the actor can keep this behavior going for months suggests not naiveté, but operational discipline and patience. (microsoft.com)
Why repeated login abuse still works
Repeated login abuse still works because many organizations struggle with legacy authentication, weak password hygiene, incomplete MFA coverage, and uneven monitoring across accounts. Attackers do not need every login attempt to succeed; they need enough to open a durable foothold. In that sense, brute force remains economically efficient. (microsoft.com)The broader implication is that defenders cannot treat “password attacks” as low priority just because they are common. A well-timed spray against high-value mailboxes, admins, or exposed services can have outsized strategic impact, especially when paired with subsequent relay or mailbox manipulation. Repetition becomes a way to find the weakest seam in a large and complex organization. (microsoft.com)
- Automated spraying can bypass simple lockout assumptions.
- Tor and rotating infrastructure complicate blocking decisions.
- High-value accounts are the real target, not random users.
- Brute force becomes more effective when combined with phishing.
- Success can come from persistence, not from speed.
Phishing as an Intelligence Collection Tool
The Trend Micro report emphasizes that Pawn Storm has been using phishing campaigns for more than a decade. That continuity is important because phishing in this context is not just a delivery mechanism; it is an intelligence-gathering tool that reveals which accounts are active, which users respond, and what infrastructure is reachable. Older phishing campaigns can still expose live relationships, mailbox structures, and internal naming conventions.Microsoft’s report on Forest Blizzard also shows that the group adapts its lure set over time, including exploitation of newer vulnerabilities and reuse of spear-phishing in support of state objectives. The pattern is consistent with a professionalized intelligence operation that treats each campaign as both access attempt and reconnaissance event. (microsoft.com)
The value of “unfashionable” lures
Old phishing templates often survive because defenders spend more time looking for novelty than for repetition. A lure that has been seen before can still work if it reaches a different user, arrives from a compromised sender, or is wrapped in a different operational context. Attackers do not need originality if they have access to timing, trust, and volume. (trendmicro.com)This is especially important in government and defense circles, where a single compromised account can reveal correspondence patterns or lead to secondary targeting. A mailbox is not just a mailbox when it can become a delivery platform for later-stage compromise. That is why mailbox access is often the real prize, not merely a metric of compromise. (microsoft.com)
- Phishing reveals organizational structure and trust relationships.
- Reused sender infrastructure can carry credibility from one campaign to another.
- Compromised mailboxes can become launchpads for internal attacks.
- Sector-specific lures increase the chance of engagement.
- Messaging fatigue makes even old lures effective again.
Stealth After Entry
One of the more important conclusions in Trend Micro’s piece is that the “loud” part of the campaign hides the “silent” part. The report says post-exploitation activities can include modifying folder permissions within a victim mailbox, which supports persistence, and using compromised email accounts for lateral movement by sending additional malicious emails from inside the organization. That is a classic example of stealth through legitimacy.This matters because mailbox compromise changes the attacker’s economics. Once inside, the group can use trusted accounts and internal context to bypass suspicion that would normally be triggered by external phishing. From a defender’s perspective, the attack has shifted from perimeter abuse to identity abuse. (microsoft.com)
Mailboxes as persistence anchors
A mailbox can become a persistence anchor if attackers adjust permissions, create forwarding logic, or use existing account trust to send targeted emails internally. That kind of persistence is harder to notice than malware running on an endpoint because it may look like normal business communication. The result is a threat that survives on routine. (microsoft.com)Trend Micro’s framing is especially useful here because it reminds readers that brute-force and phishing are only the opening act. If defenders only measure the initial intrusion, they will miss the more damaging layer that follows. The technical and operational challenge is to detect when normal collaboration tools have been turned into attacker infrastructure. (microsoft.com)
- Mailbox permission changes may be a sign of persistence.
- Internal phishing from trusted senders is harder to spot.
- Forwarding rules and delegated access deserve scrutiny.
- Legitimate collaboration tools can become attack channels.
- Post-compromise behavior is often more revealing than the initial lure.
Target Profile and Geographic Reach
Trend Micro says the targets included organizations in foreign affairs, energy, defense, transportation, labor, social welfare, finance, parenthood, and even local city councils, a central bank, court houses, and a military fire department. That range is broader than the usual government-and-defense stereotype and suggests the actor values access to administrative, logistical, and policy-relevant institutions, not just overtly military ones. (trendmicro.com)Microsoft’s Forest Blizzard profile similarly lists government, diplomatic and defense entities, think tanks, NGOs, higher education, IT services, and defense contractors as targets. The overlap between vendor reporting is strong enough to support a clear conclusion: this is an intelligence-driven actor with interests far beyond any single vertical. (microsoft.com)
Why the sector spread matters
The broader the sector spread, the more likely it is that the actor is seeking adjacent leverage. Transportation and energy organizations can reveal dependencies; social welfare and local councils can expose citizen-facing processes; finance and central banking can reveal policy insight. In espionage, access to a small administrative node can be as valuable as access to a national ministry. (microsoft.com)Geography also matters. Trend Micro says it observed targeting across Europe, North America, South America, Asia, Africa, and the Middle East. That global footprint indicates that the campaign is not simply opportunistic spam; it is likely guided by strategic collection priorities and infrastructure availability.
- The target list spans both strategic and civic institutions.
- Administrative offices can be as useful as military ones.
- Broad geographic targeting suggests coordinated tasking.
- Sector diversity makes simple blocklists less effective.
- Cross-region targeting complicates attribution and response.
Historical Continuity and Evolution
One of the most interesting parts of the reporting is how little the actor’s core logic seems to have changed. Trend Micro’s earlier work on Pawn Storm documented long-running campaigns against military and foreign affairs targets, while later reports show the same actor adopting more infrastructure-heavy, credential-focused operations. The shift is evolutionary, not revolutionary.Microsoft’s reporting adds another layer by showing that the actor keeps combining public exploits, custom tooling, and credential abuse. Its 2024 analysis of GooseEgg demonstrates that Forest Blizzard continues to invest in custom post-compromise capabilities for credential extraction. That indicates a mature actor that can mix commodity techniques with bespoke tools depending on the objective.
Continuity is the real threat
Continuity means defenders cannot assume that older detections are obsolete. Even when the exact campaign mechanics shift, the actor may still be using the same operational habits, the same sectors, and the same persistence goals. That creates a cumulative danger: each wave of compromise can inform the next. (microsoft.com)It also means the security community should be careful about dismissing familiar groups as “solved.” In reality, the most resilient threat actors are those that preserve what works, discard what fails, and layer in just enough innovation to keep pace with defenses. That is a pragmatic form of sophistication. (microsoft.com)
- Old tradecraft can remain effective for years.
- New tooling often complements, rather than replaces, older methods.
- Persistent actors learn from defensive improvements.
- Campaign continuity helps them exploit predictable gaps.
- Reuse across years can signal operational confidence.
Defensive Implications for Enterprises
For enterprises, the real challenge is that this campaign straddles email, identity, and endpoint security. Microsoft’s guidance on CVE-2023-23397 stresses the need to patch Outlook, inspect Exchange logs, and look for evidence of relay and post-compromise activity. Trend Micro’s analysis reinforces that organizations must also monitor for mailbox permission changes and internal abuse of trusted email accounts. (microsoft.com)This means the defensive model cannot be siloed. Email security teams need to coordinate with identity teams, cloud security teams, and SOC analysts who can correlate unusual mailbox activity with authentication events. A classic single-control approach will miss the multi-stage nature of the intrusion. (microsoft.com)
Practical control priorities
A sound response strategy should focus on reducing both exposure and dwell time. That means patch management, phishing resistance, mailbox auditing, and authentication hardening need to be treated as a single program rather than separate checkboxes. In an attack like this, the weakest control is the one that gives the attacker a second chance. (microsoft.com)Security teams should also be skeptical of “normal” account behavior that suddenly changes in subtle ways. A trusted mailbox sending unusual messages, an account that authenticates from a new region, or a permission change in an inbox can all be signs of a deeper compromise. That kind of detection requires context, not just alerts. (microsoft.com)
- Patch Outlook and Exchange-related exposures quickly.
- Review mailbox delegation and permission changes regularly.
- Correlate identity events with email and server logs.
- Treat Tor-based login attempts as high-risk signals.
- Hunt for internal phishing from compromised accounts.
- Strengthen MFA and reduce legacy authentication paths.
Strengths and Opportunities
The report highlights several reasons this campaign remains effective, but it also points to practical opportunities for defenders who are willing to adapt. The good news is that the same operational patterns that make Pawn Storm durable also create repeatable detection opportunities, especially when organizations treat email, identity, and endpoint telemetry as a unified picture.- Cross-layer detection can expose the chain from phishing to relay to persistence.
- Mailbox auditing can reveal abuse that endpoint tools miss.
- Patched Outlook and Exchange systems reduce one of the actor’s most dangerous entry points.
- Identity analytics can identify unusual authentication patterns faster.
- Correlation with server logs improves visibility into relay-based compromise.
- User training still matters, especially for high-value targets.
- Segmentation and least privilege can limit lateral movement after initial access.
Risks and Concerns
The most concerning aspect of the report is that the actor’s methods are both familiar and adaptable. That combination makes it easy for organizations to underestimate the risk until after a breach has already occurred. The overlap between phishing, relay, brute force, and mailbox abuse also means that no single control is sufficient.- Legacy authentication remains a weak point in many environments.
- Few forensic artifacts can make incidents hard to reconstruct.
- Trusted sender abuse can defeat conventional email suspicion.
- Broad target sets increase the chance of one successful foothold.
- Stealthy mailbox changes may go unnoticed for long periods.
- Tor and proxy infrastructure complicate network-based blocking.
- Repeated campaigns can exhaust analyst attention and create alert fatigue.
Looking Ahead
The next phase of this story will likely be less about whether Pawn Storm is noisy and more about whether defenders can stop treating noise as harmless. Microsoft’s continued tracking of Forest Blizzard, together with Trend Micro’s long-term view of the actor, suggests that this threat cluster will keep blending brute force, phishing, relay attacks, and post-compromise persistence. The more important question is whether organizations can develop enough visibility to distinguish background chatter from true intrusion. (microsoft.com)There is also a wider strategic lesson here. APTs do not need to be glamorous to be effective, and the most dangerous campaigns are often the ones that look familiar enough to ignore. If defenders internalize anything from this reporting, it should be that repetition is not reassurance; in the hands of a patient state-linked operator, repetition can be camouflage. (trendmicro.com)
- Watch for follow-on reporting on Forest Blizzard’s post-compromise tooling.
- Monitor whether NTLM relay abuse remains a favored access path.
- Track any new Microsoft or Trend Micro guidance on mailbox persistence.
- Prioritize detection engineering around identity and email abuse.
- Review whether your organization still allows avoidable legacy authentication.
Source: www.trendmicro.com Pawn Storm Uses Brute Force and Stealth Against High-Value Targets