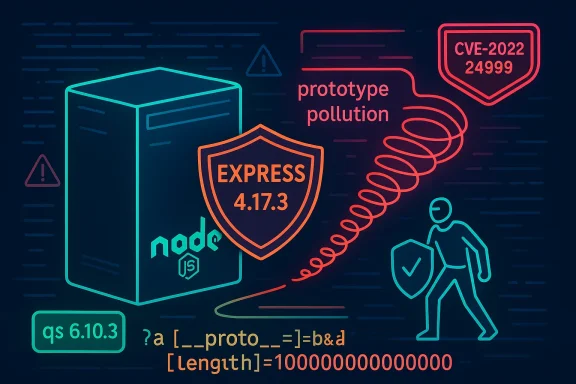
The qs library’s quietly dangerous prototype‑pollution bug — tracked as CVE‑2022‑24999 — is a textbook example of how a tiny parser behavior can cascade into a network‑accessible denial‑of‑service for Node.js applications. The flaw allowed an attacker to use a specially crafted query string (for example, payloads that include keys like
The Node.js ecosystem depends on tiny, focused libraries to handle everyday tasks. qs (a querystring parser) is one of those ubiquitous pieces: many frameworks and middleware use it to turn URL query strings like
CVE‑2022‑24999 describes a failure to do that. By allowing
Community trackers, vendor advisories, and vulnerability databases converged quickly on the same technical picture: this is not a remote code‑execution vulnerability by default, but it is an easy availability attack against many Express‑style apps that trust parsed query data. The issue prompted backports across multiple 6.x branches of qs and an update to Express to avoid shipping an affected qs.
When you review a patch or a vendored copy, validate for these signs:
If you’re responsible for Node/Express services, treat this as a reminder: dependency hygiene and runtime invariants matter as much as the application code you write. Patch now, audit your lockfiles, and add tests that exercise parsing edge cases so they never surprise you in production.
Source: MSRC Security Update Guide - Microsoft Security Response Center
a[[B]proto[/B]=b and a[length]=100000000) to change an object’s prototype and force application code into pathological behavior that hangs the Node process. The vulnerability was fixed in qs 6.10.3 and the fix was backported to several maintenance branches; Express’s 4.17.3 release includes a patched qs dependency ([email protected]) and is therefore not vulnerable when that release is used.
 Background / Overview
Background / Overview
The Node.js ecosystem depends on tiny, focused libraries to handle everyday tasks. qs (a querystring parser) is one of those ubiquitous pieces: many frameworks and middleware use it to turn URL query strings like foo[bar]=baz into JavaScript objects. That convenience, however, comes with subtle surface area: query parameters can express nested structures, and parser semantics must carefully avoid interacting with JavaScript’s prototype chain in unexpected ways.CVE‑2022‑24999 describes a failure to do that. By allowing
[B]proto[/B]‑style keys to influence the parsed object’s prototype, an attacker could make properties such as length appear on prototypes and thereby influence behaviors that assume those properties are safe to read as integers. When those properties are used in loops, buffer or array allocations, or other unbounded numeric operations, attackers can cause resource exhaustion or indefinite work that manifests as a process hang. The authoritative CVE record summarizes the issue and lists the patched versions and backports.Community trackers, vendor advisories, and vulnerability databases converged quickly on the same technical picture: this is not a remote code‑execution vulnerability by default, but it is an easy availability attack against many Express‑style apps that trust parsed query data. The issue prompted backports across multiple 6.x branches of qs and an update to Express to avoid shipping an affected qs.
What went wrong: technical anatomy
Prototype pollution + array semantics = trouble
At the heart of the problem are two facts about JavaScript:- Every object inherits from a prototype (usually
Object.prototypeunlessObject.create(null)orplainObjectsoptions are used). - Arrays and array‑like objects use a numeric
lengthproperty to bound iteration and allocation.
Object.prototype.length (or a prototype reachable by application code) to be set to a very large integer, code that iterates up to obj.length, or creates an array of obj.length, can spend an enormous amount of time or memory performing that work. Because qs’s parsing logic previously allowed [B]proto[/B] to be set via nested bracket notation in query keys, it was possible for an attacker to create an array‑like proto value and assign a giant length that then influenced downstream code. That leads to a hang or resource exhaustion without needing to execute arbitrary code in the process. This is the exploitation pattern demonstrated by multiple advisories and community write‑ups.Example payload and how it works
A compact, commonly cited example is:?a[[B]proto[/B]=b&a[[B]proto[/B]&a[length]=100000000
length value that looks like a normal array length. If application logic does something innocuous such as:- read
req.query.a.lengthto size a loop or buffer, or - call
Array.prototypemethods or iterate up to thelengthvalue,
req.query values or rely on length in request handling.Affected software, patched versions, and verification
- Affected component: qs before 6.10.3. The issue is tracked as CVE‑2022‑24999.
- Backports: the fix was backported to a range of 6.x maintenance versions: 6.9.7, 6.8.3, 6.7.3, 6.6.1, 6.5.3, 6.4.1, 6.3.3, and 6.2.4. That means many projects can update to the smallest compatible maintenance release rather than jumping to the latest major/minor if compatibility is a concern.
- Express: the Express 4.x line shipped a patched dependency in Express 4.17.3, which declared
deps: [email][email protected][/email]; using that Express release removes exposure for applications that rely on the framework’s bundled parsing path. Verify your app’s effective dependency graph (lock files, node_modules, andnpm ls qs) because transitive dependencies can still pull in vulnerable versions.
- Use package management tooling to identify every
qsinstance in your dependency graph (npm ls qs/yarn why qs). - Inspect lockfiles (package‑lock.json, yarn.lock) to confirm the actual installed version that your runtime will load.
- If your application bundles or vendors dependencies, check the bundled copy, because bundling can fix a vulnerable transitive dependency in a way that package metadata doesn’t reveal.
Exploitability and real‑world impact
How easy is it to weaponize?
Very easy in many real‑world deployments. The attack requires no authentication, no special credentials, and is triggered by placing crafted payloads into query strings — something that is trivially achievable from any web client, remote scanner, or automated bot. Because many Express apps expose GET endpoints (search, API, assets) to unauthenticated clients, the blast radius is meaningful: public, unauthenticated endpoints that parse query strings are viable targets. Multiple advisory sources and vulnerability trackers assigned a high impact rating for availability (CVSS base scores commonly around 7.5) to reflect the ease of causing a hang.Is remote code execution (RCE) possible?
Not directly in the default, common exploitation scenarios described by most advisories. The vulnerability’s primary impact is availability — a denial‑of‑service. That said, prototype pollution is a class of bug that can sometimes be leveraged into logic‑confusion paths or more powerful exploits in certain codebases. In other words: DoS is the high‑confidence outcome; RCE is context‑dependent and lower confidence, but it should not be dismissed where application logic or other unsafe operations interact with polluted prototypes. Advisories therefore reasonably emphasize immediate patching for availability reasons, while noting that more advanced exploitation paths may exist for bespoke applications.How maintainers fixed it (and what to look for in the fix)
The upstream fix for qs changes parsing rules to either disallow setting dangerous prototype keys or to parse into plain objects that do not inherit unwanted properties, i.e., objects created withObject.create(null) or equivalent safe patterns. The fix includes unit tests and explicit checks to prevent [B]proto[/B] from being treated as a normal nested assignment target. The patch work was performed in the qs repository and referenced by several advisories and the backport commits. Upstream maintainers also published point releases to allow downstream projects to adopt the fix without large semantic jumps.When you review a patch or a vendored copy, validate for these signs:
- The parser explicitly rejects
[B]proto[/B]or other prototype‑mutating keys by name or via a whitelist. - The parser may return objects created with
Object.create(null)when theplainObjectsoption is set, preventing accidental prototype inheritance. - Unit tests include PoC query strings that previously triggered the hang (for regression prevention).
- Release notes or changelogs enumerate the CVE and the exact fixed versions to make auditing simpler.
Detection and incident response guidance
If you maintain Node/Express apps, assume you could be targeted. Practical detection and response steps:- Search access logs for query strings that include suspicious bracketed keys like
[B]proto[/B],constructor, or unusually large numericlengthvalues used as parameters. A small scanner or grep over web server logs can quickly surface probing attempts. - Monitor for sudden increases in request latency or worker thread CPU usage tied to specific endpoints; a single request that causes a hang will typically spike CPU and block responses.
- Add WAF rules to inspect query parameters and block or rate‑limit requests that contain bracketed keys setting
[B]proto[/B]or extremely large numeric parameters inlength‑like fields. - For forensic analysis, capture a process dump of the Node process that’s hung (if possible) or collect the last access log lines and the exact query string that triggered the condition.
- Hardened deployment patterns (cgroups/container memory limits, per‑process CPU quotas, process supervisors that restart after N seconds) reduce blast radius by preventing a single worker from taking down the whole host. However, these are mitigations only; they don’t replace the need to patch.
Remediation checklist: practical steps to fix and validate
- Inventory: run
npm ls qsandyarn why qsto find every installed instance. If your app bundles dependencies, inspect the bundled tree too. - Patch: update to qs 6.10.3 or to any of the backported safe maintenance releases (for example 6.9.7), or upgrade Express to 4.17.3 or newer if you rely on the framework’s provided chain.
- Rebuild and test: run your unit and integration tests. Pay special attention to any code that reads query parameters and uses values as numeric bounds.
- Verify lockfiles: commit a fresh lockfile after the update, and ensure your CI builds and deployment artifacts contain the updated version.
- Deploy in stages: roll the change to a subset of hosts, monitor logs and telemetry for regressions, then complete the rollout.
- Compensating controls (temporary): apply WAF rules to block
[B]proto[/B]‑style bracketed parameters and rate limit unauthenticated endpoints while you patch. These controls reduce exposure but are not substitutes for patching.
Supply‑chain and governance lessons
This vulnerability is instructive on several supply‑chain fronts:- Small libraries matter. Even a focused parser used for one low‑level job can compromise availability of a large fleet of services.
- Backports are pragmatic. Upstream maintainers backported the fix across multiple maintenance branches to help downstream consumers with mibackports can obscure vulnerability presence if consumers only look at top‑level dependency versions. Lockfile inspection is required.
- Monitoring and SBOMs help. A software bill of materials (SBOM) and automated dependency scanning (npm audit, Snyk, OS vendor advisories, CI policy checks) catch transitive exposures faster than manual checks. Integrate vulnerability scanning into PR pipelines and release checks.
- Defense‑in‑depth reduces impact. Sandboxing, small process memory limits, aggressive health‑check and restart policies, and ingress filtering (CDN/WAF) make exploitation noisier and less durable while patches are deployed.
Critical analysis — strengths and lingering risks
Notable strengths
- The fix was applied quickly and backported to many maintenance branches, recognizing that real‑world applications often depend on exact minor versions and cannot always jump major versions immediately. That made remediation practical for many teams.
- Express’s team published a point release (4.17.3) that included a patched qs dependency to simplify remediation for framework consumers. That release path gave many users a low‑friction upgrade option.
- Multiple independent databases and vendors (NVD, Ubuntu, GitLab Advisory, vulnerability trackers) reached consistent conclusions about impact and patched ranges, enabling defenders to cross‑check and validate remediation.
Residual and systemic risks
- Transitive dependencies: even if a top‑level project upgrades, transitive packages or older bundled copies may still pull in vulnerable qs. Organizations that do not verify the exact runtime dependency tree remain exposed.
- Detection blind spots: because the exploit payload looks like ordinary bracketed query parameters, log‑only detection can miss attempts when logs are noisy or rotated. WAFs and behavioural alerts are required for reliable detection.
- Prototype pollution is a class of vulnerabilities: fixing one library does not prevent similar patterns in other parsers (JSON libraries, body parsers, or custom query parsing code). A single CVE does not eliminate the architectural hazard of prototype mutation via untrusted input.
Timeline and attribution
Public reporting aggregated by vulnerability trackers indicates disclosure occurred in November 2022, with CVE assignment and multiple advisories following. Several security platforms credit the discovery and analysis to researchers who reported the behavior to maintainers and public trackers. Independent write‑ups and advisories documented the PoC payload and the patch details. The discovery and reporting chain — including researcher disclosure, upstream PRs, vendor advisories, and community tracking — illustrates an effective, multi‑party remediation flow when maintainers, vendors, and the community coordinate.Practical checklist for WindowsForum readers (quick reference)
- Find every instance of qs in your projects: run
npm ls qsoryarn why qs. - If you use Express, check your Express version; upgrade to 4.17.3 or later if you are on an older 4.x release. Confirm
deps: [email][email protected][/email]or later is in the runtime tree. - Patch qs directly if it appears in your dependency tree: upgrade to qs 6.10.3 or a backported safe release (for example 6.9.7) and rebuild.
- Apply short‑term WAF rules to block
[B]proto[/B]orconstructorbracketed parameters, and add rate limits for public endpoints. - Add tests to your repo that include the known PoC query strings; preventive unit tests guard against regressions.
- Use CI to fail builds if any dependency has a known unpatched CVE (integrate
npm audit/Snyk or your vendor’s scanning tools).
Conclusion
CVE‑2022‑24999 is not flashy — it doesn’t require a multi‑stage exploit chain or exotic memory corruption to be impactful — but it is effective. A cleverly placed query string becomes a blunt instrument for availability disruption because the parser trusted input too much and JavaScript’s prototype semantics were not defended against. The lesson is straightforward: tiny parsing behaviors can become large‑scale operational failures across a distributed web. Patch promptly, verify the actual dependency graph that runs in production, and add defensive controls that assume hostile input. That three‑part posture — patch, verify, defend — is the shortest path to preventing a future single‑parameter outage from becoming an incident.If you’re responsible for Node/Express services, treat this as a reminder: dependency hygiene and runtime invariants matter as much as the application code you write. Patch now, audit your lockfiles, and add tests that exercise parsing edge cases so they never surprise you in production.
Source: MSRC Security Update Guide - Microsoft Security Response Center