Hello, I'm getting BSOD mostly while playing online games. I have checked memory w/memtest passed. Drivers for video card are up to date. The error messages are all ways different. my machine is just 1yr old and after removing Norton a few months back BSOD went away with it. Unfortunately there back. Thanks for any help in advance.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Windows 7 Random BSOD
- Thread starter Loozzer
- Start date
cybercore
New Member
- Joined
- Jul 7, 2009
BugCheck 19, {20, fffffa80062cc4c0, fffffa80062cc740, d28b100}
BAD_POOL_HEADER (19)
Unable to load image atikmpag.sys, Win32 error 0n2
*** WARNING: Unable to verify timestamp for atikmpag.sys
*** ERROR: Module load completed but symbols could not be loaded for atikmpag.sys
Probably caused by : atikmpag.sys ( atikmpag+5eaf )
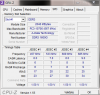
1. Attach CPU-Z memory tab + RamMon txt, as in the sticky thread of this forum section.
2. Update or disable ADMtek AN983/AN985 based ethernet adapter
AN983X64.sys Thu May 19 04:14:27 2005
3. Update Ideazon ZBoard/Ideazon Fang MM USB HID
Alpham164.sys Mon Jul 23 03:57:03 2007
Alpham264.sys Tue Mar 20 05:51:03 2007
4. Update Atheros AR8121/AR8113/AR8114 PCI-E Ethernet Controller
L1E62x64.sys Sun Aug 23 01:08:09 2009
Link Removed - Invalid URL
Crash Dumps:
Code:
Microsoft (R) Windows Debugger Version 6.12.0002.633 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [F:\a\Minidump\D M P\DMP\030511-25724-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: SRV*c:\websymbols*http://msdl.microsoft.com/download/symbols
Executable search path is:
Windows 7 Kernel Version 7601 (Service Pack 1) MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS
Built by: 7601.17514.amd64fre.win7sp1_rtm.101119-1850
Machine Name:
Kernel base = 0xfffff800`02c4f000 PsLoadedModuleList = 0xfffff800`02e94e90
Debug session time: Sat Mar 5 01:21:18.632 2011 (UTC - 5:00)
System Uptime: 0 days 0:24:43.146
Loading Kernel Symbols
...............................................................
................................................................
.....................................
Loading User Symbols
Loading unloaded module list
.....
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck C4, {91, 2, fffffa800885e4d0, 0}
Probably caused by : ntkrnlmp.exe ( nt! ?? ::FNODOBFM::`string'+4874 )
Followup: MachineOwner
---------
0: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
DRIVER_VERIFIER_DETECTED_VIOLATION (c4)
A device driver attempting to corrupt the system has been caught. This is
because the driver was specified in the registry as being suspect (by the
administrator) and the kernel has enabled substantial checking of this driver.
If the driver attempts to corrupt the system, bugchecks 0xC4, 0xC1 and 0xA will
be among the most commonly seen crashes.
Arguments:
Arg1: 0000000000000091, A driver switched stacks using a method that is not supported by
the operating system. The only supported way to extend a kernel
mode stack is by using KeExpandKernelStackAndCallout.
Arg2: 0000000000000002
Arg3: fffffa800885e4d0
Arg4: 0000000000000000
Debugging Details:
------------------
BUGCHECK_STR: 0xc4_91
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
PROCESS_NAME: svchost.exe
CURRENT_IRQL: 2
EXCEPTION_RECORD: fffff88003c1bd88 -- (.exr 0xfffff88003c1bd88)
ExceptionAddress: fffff80002cd22e2 (nt!SwapContext_PatchXRstor)
ExceptionCode: c0000005 (Access violation)
ExceptionFlags: 00000000
NumberParameters: 2
Parameter[0]: 0000000000000000
Parameter[1]: ffffffffffffffff
Attempt to read from address ffffffffffffffff
TRAP_FRAME: fffff88003c1be30 -- (.trap 0xfffff88003c1be30)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000000000000001 rbx=0000000000000000 rcx=fffff88003c1ce08
rdx=0000000000000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80002cd22e2 rsp=fffff88003c1bfc0 rbp=fffff88003c1cdb8
r8=fffffa80088560e8 r9=0000000000000000 r10=fffffffffffffffe
r11=0000000000000000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na pe nc
nt!SwapContext_PatchXRstor:
fffff800`02cd22e2 0fae09 fxrstor [rcx] ds:1f80:fffff880`03c1ce08=00
Resetting default scope
LAST_CONTROL_TRANSFER: from fffff80002d2653a to fffff80002ccf640
STACK_TEXT:
fffff880`03c1ae88 fffff800`02d2653a : 00000000`000000c4 00000000`00000091 00000000`00000002 fffffa80`0885e4d0 : nt!KeBugCheckEx
fffff880`03c1ae90 fffff800`02cf9963 : 00000000`00000000 00000000`00000000 00000000`00000003 00000000`00000000 : nt! ?? ::FNODOBFM::`string'+0x4874
fffff880`03c1aed0 fffff800`02d0adc1 : fffff880`03c1bd88 fffff880`03c1bae0 fffff880`03c1be30 fffff800`02e4fcc0 : nt!RtlDispatchException+0x33
fffff880`03c1b5b0 fffff800`02ccecc2 : fffff880`03c1bd88 fffff800`02e41e80 fffff880`03c1be30 fffffa80`0885e4d0 : nt!KiDispatchException+0x135
fffff880`03c1bc50 fffff800`02ccd5ca : 00000000`00000001 00000000`00000000 00000000`00000000 fffff880`03c1bea0 : nt!KiExceptionDispatch+0xc2
fffff880`03c1be30 fffff800`02cd22e2 : 00000000`00000000 fffff800`00000000 00000000`00000000 00000000`00000000 : nt!KiGeneralProtectionFault+0x10a
fffff880`03c1bfc0 fffff800`02cd1eda : fffff880`02f64180 fffff800`02cdb9b8 fffffa80`09212801 fffff880`03c1c9d8 : nt!SwapContext_PatchXRstor
fffff880`03c1c000 fffff800`02cd4992 : fffffa80`0885e4d0 fffffa80`0885e4d0 fffff880`00000000 fffff800`00000008 : nt!KiSwapContext+0x7a
fffff880`03c1c140 fffff800`02cd3eaa : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiCommitThreadWait+0x1d2
fffff880`03c1c1d0 fffff800`02fc5ccf : fffff880`0000002a fffff880`03c1c520 00000000`00000001 00000000`00000006 : nt!KeWaitForMultipleObjects+0x272
fffff880`03c1c490 fffff800`02fc603e : fffffa80`0822d301 fffff800`02cd22a4 fffff8a0`00000001 fffff800`00000001 : nt!ObpWaitForMultipleObjects+0x294
fffff880`03c1c960 fffff800`02cce8d3 : fffffa80`0885e4d0 00000000`00c9f708 fffff880`03c1cbc8 fffff880`03c1cc00 : nt!NtWaitForMultipleObjects+0xe5
fffff880`03c1cbb0 00000000`76fb18ca : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x13
00000000`00c9f6e8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x76fb18ca
STACK_COMMAND: kb
FOLLOWUP_IP:
nt! ?? ::FNODOBFM::`string'+4874
fffff800`02d2653a cc int 3
SYMBOL_STACK_INDEX: 1
SYMBOL_NAME: nt! ?? ::FNODOBFM::`string'+4874
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
DEBUG_FLR_IMAGE_TIMESTAMP: 4ce7951a
FAILURE_BUCKET_ID: X64_0xc4_91_nt!_??_::FNODOBFM::_string_+4874
BUCKET_ID: X64_0xc4_91_nt!_??_::FNODOBFM::_string_+4874
Followup: MachineOwner
---------
Microsoft (R) Windows Debugger Version 6.12.0002.633 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [F:\a\Minidump\D M P\DMP\030511-27175-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: SRV*c:\websymbols*http://msdl.microsoft.com/download/symbols
Executable search path is:
Windows 7 Kernel Version 7601 (Service Pack 1) MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS
Built by: 7601.17514.amd64fre.win7sp1_rtm.101119-1850
Machine Name:
Kernel base = 0xfffff800`02c0f000 PsLoadedModuleList = 0xfffff800`02e54e90
Debug session time: Sat Mar 5 00:55:50.700 2011 (UTC - 5:00)
System Uptime: 0 days 0:58:17.214
Loading Kernel Symbols
...............................................................
................................................................
.....................................
Loading User Symbols
Loading unloaded module list
......
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 19, {20, fffffa80062cc4c0, fffffa80062cc740, d28b100}
Unable to load image atikmpag.sys, Win32 error 0n2
*** WARNING: Unable to verify timestamp for atikmpag.sys
*** ERROR: Module load completed but symbols could not be loaded for atikmpag.sys
Probably caused by : atikmpag.sys ( atikmpag+5eaf )
Followup: MachineOwner
---------
2: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
BAD_POOL_HEADER (19)
The pool is already corrupt at the time of the current request.
This may or may not be due to the caller.
The internal pool links must be walked to figure out a possible cause of
the problem, and then special pool applied to the suspect tags or the driver
verifier to a suspect driver.
Arguments:
Arg1: 0000000000000020, a pool block header size is corrupt.
Arg2: fffffa80062cc4c0, The pool entry we were looking for within the page.
Arg3: fffffa80062cc740, The next pool entry.
Arg4: 000000000d28b100, (reserved)
Debugging Details:
------------------
BUGCHECK_STR: 0x19_20
POOL_ADDRESS: GetPointerFromAddress: unable to read from fffff80002ec00e8
fffffa80062cc4c0
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
PROCESS_NAME: BlackOpsMP.exe
CURRENT_IRQL: 0
LAST_CONTROL_TRANSFER: from fffff80002db9cae to fffff80002c8f640
STACK_TEXT:
fffff880`09033408 fffff800`02db9cae : 00000000`00000019 00000000`00000020 fffffa80`062cc4c0 fffffa80`062cc740 : nt!KeBugCheckEx
fffff880`09033410 fffff880`03e05eaf : fffff8a0`0903f330 fffff880`0400a0d1 00000000`7ffff8a0 fffffa80`080b4000 : nt!ExDeferredFreePool+0x12da
fffff880`090334c0 fffff8a0`0903f330 : fffff880`0400a0d1 00000000`7ffff8a0 fffffa80`080b4000 fffff8a0`00000001 : atikmpag+0x5eaf
fffff880`090334c8 fffff880`0400a0d1 : 00000000`7ffff8a0 fffffa80`080b4000 fffff8a0`00000001 fffff8a0`0903f330 : 0xfffff8a0`0903f330
fffff880`090334d0 fffff880`0403d204 : fffffa80`080b4000 00000000`00000000 fffff880`09033570 00000000`00000000 : dxgkrnl!DXGADAPTER::AcquireDdiSync+0xc9
fffff880`09033510 fffff880`040412c1 : fffff8a0`0903f330 00000000`00000000 00000000`00000000 fffff8a0`0136f000 : dxgkrnl!DXGADAPTER::DdiDestroyAllocation+0x50
fffff880`09033540 fffff880`04053784 : 00000000`00000001 00000000`00000000 00000000`00000000 fffff8a0`00000799 : dxgkrnl!DXGDEVICE::DestroyAllocations+0x83d
fffff880`09033630 fffff880`04038815 : 00000000`fffffeda fffff8a0`092de3c0 fffff8a0`0136f000 fffffa80`080b4000 : dxgkrnl!DXGDEVICE::~DXGDEVICE+0x19c
fffff880`090336a0 fffff880`04076e4a : 00000000`00000001 fffffa80`080b4000 fffff8a0`092de3c0 fffff8a0`092de440 : dxgkrnl!DXGADAPTER::DestroyDevice+0x1c9
fffff880`090336d0 fffff880`040767e0 : fffff900`c374d300 00000000`00000000 00000000`00000001 fffff900`c374d300 : dxgkrnl!DXGPROCESS::Destroy+0xba
fffff880`09033780 fffff960`00144e7c : 00000000`00000870 fffff900`c374d300 00000000`00000000 fffff900`c374d300 : dxgkrnl!DxgkProcessCallout+0x268
fffff880`09033810 fffff960`0014457f : 00000000`00000000 fffff880`09033c20 fffffa80`06373660 00000000`00000000 : win32k!GdiProcessCallout+0x244
fffff880`09033890 fffff800`02f65001 : 00000000`00000000 00000000`00000000 00000000`00000000 fffffa80`06373600 : win32k!W32pProcessCallout+0x6b
fffff880`090338c0 fffff800`02f4a37d : 00000000`cfffffff fffff960`00154201 00000000`78457300 fffffa80`093027f0 : nt!PspExitThread+0x4d1
fffff880`090339c0 fffff800`02c82dfa : fffff900`c06c3010 fffff960`00149fa0 fffff900`c06c3010 00000000`00000000 : nt!PsExitSpecialApc+0x1d
fffff880`090339f0 fffff800`02c83140 : 00000000`00000246 fffff880`09033a70 fffff800`02f4a2f0 00000000`00000001 : nt!KiDeliverApc+0x2ca
fffff880`09033a70 fffff800`02c8e977 : fffff880`09033ca0 fffff800`02c9935a 00000000`0000002a 00000000`73ba2450 : nt!KiInitiateUserApc+0x70
fffff880`09033bb0 00000000`73ba2e09 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceExit+0x9c
00000000`349af0f8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x73ba2e09
STACK_COMMAND: kb
FOLLOWUP_IP:
atikmpag+5eaf
fffff880`03e05eaf ?? ???
SYMBOL_STACK_INDEX: 2
SYMBOL_NAME: atikmpag+5eaf
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: atikmpag
IMAGE_NAME: atikmpag.sys
DEBUG_FLR_IMAGE_TIMESTAMP: 4d409c8d
FAILURE_BUCKET_ID: X64_0x19_20_atikmpag+5eaf
BUCKET_ID: X64_0x19_20_atikmpag+5eaf
Followup: MachineOwner
---------Drivers:
Code:
start end module name
fffff880`04036000 fffff880`04074000 1394ohci 1394ohci.sys Sat Nov 20 05:44:56 2010 (4CE7A6A8)
fffff880`00e0a000 fffff880`00e61000 ACPI ACPI.sys Sat Nov 20 04:19:16 2010 (4CE79294)
fffff880`02c7a000 fffff880`02d03000 afd afd.sys Sat Nov 20 04:23:27 2010 (4CE7938F)
fffff880`04824000 fffff880`0483a000 AgileVpn AgileVpn.sys Mon Jul 13 20:10:24 2009 (4A5BCCF0)
fffff880`05fdb000 fffff880`05fe7f00 Alpham164 Alpham164.sys Mon Jul 23 03:57:03 2007 (46A45F4F)
fffff880`05fe8000 fffff880`05fed500 Alpham264 Alpham264.sys Tue Mar 20 05:51:03 2007 (45FFAE87)
fffff880`03e7d000 fffff880`03e91000 amdiox64 amdiox64.sys Thu Feb 18 10:17:53 2010 (4B7D5A21)
fffff880`03f70000 fffff880`03f85000 amdppm amdppm.sys Mon Jul 13 19:19:25 2009 (4A5BC0FD)
fffff880`00fee000 fffff880`00ff9000 amdxata amdxata.sys Fri Mar 19 12:18:18 2010 (4BA3A3CA)
fffff880`041ee000 fffff880`041ff000 AN983X64 AN983X64.sys Thu May 19 04:14:27 2005 (428C4AE3)
fffff880`04090000 fffff880`04098000 ASACPI ASACPI.sys Wed Jul 15 23:31:29 2009 (4A5E9F11)
fffff880`03f44000 fffff880`03f4a000 AsIO AsIO.sys Thu Apr 22 07:18:03 2010 (4BD0306B)
fffff880`08e00000 fffff880`08e0b000 asyncmac asyncmac.sys Mon Jul 13 20:10:13 2009 (4A5BCCE5)
fffff880`00fbb000 fffff880`00fc4000 atapi atapi.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`00fc4000 fffff880`00fee000 ataport ataport.SYS Sat Nov 20 04:19:15 2010 (4CE79293)
fffff880`05e5f000 fffff880`05e7f000 AtihdW76 AtihdW76.sys Wed Nov 17 07:02:04 2010 (4CE3C43C)
fffff880`048a8000 fffff880`051a4000 atikmdag atikmdag.sys Wed Jan 26 17:48:28 2011 (4D40A4BC)
fffff880`03f85000 fffff880`03fd3000 atikmpag atikmpag.sys Wed Jan 26 17:13:33 2011 (4D409C8D)
fffff880`0166f000 fffff880`01676000 Beep Beep.SYS Mon Jul 13 20:00:13 2009 (4A5BCA8D)
fffff880`03f33000 fffff880`03f44000 blbdrive blbdrive.sys Mon Jul 13 19:35:59 2009 (4A5BC4DF)
fffff880`06f2d000 fffff880`06f4b000 bowser bowser.sys Mon Jul 13 19:23:50 2009 (4A5BC206)
fffff960`006a0000 fffff960`006c7000 cdd cdd.dll Sat Nov 20 07:55:34 2010 (4CE7C546)
fffff880`0148b000 fffff880`014b5000 cdrom cdrom.sys Sat Nov 20 04:19:20 2010 (4CE79298)
fffff880`00c99000 fffff880`00d59000 CI CI.dll Sat Nov 20 08:12:36 2010 (4CE7C944)
fffff880`01600000 fffff880`01630000 CLASSPNP CLASSPNP.SYS Sat Nov 20 04:19:23 2010 (4CE7929B)
fffff880`00c3b000 fffff880`00c99000 CLFS CLFS.SYS Mon Jul 13 19:19:57 2009 (4A5BC11D)
fffff880`0111a000 fffff880`0118c000 cng cng.sys Sat Nov 20 05:08:45 2010 (4CE79E2D)
fffff880`04809000 fffff880`04819000 CompositeBus CompositeBus.sys Sat Nov 20 05:33:17 2010 (4CE7A3ED)
fffff880`06e24000 fffff880`06e2d000 cpuz133_x64 cpuz133_x64.sys Tue May 11 05:58:57 2010 (4BE92A61)
fffff880`06e2d000 fffff880`06e36000 cpuz134_x64 cpuz134_x64.sys Fri Jul 09 07:16:58 2010 (4C37052A)
fffff880`05f4c000 fffff880`05f5a000 crashdmp crashdmp.sys Mon Jul 13 20:01:01 2009 (4A5BCABD)
fffff880`03e92000 fffff880`03f15000 csc csc.sys Sat Nov 20 04:27:12 2010 (4CE79470)
fffff880`05f82000 fffff880`05f84f00 dadder dadder.sys Mon Apr 19 05:04:42 2010 (4BCC1CAA)
fffff880`03f15000 fffff880`03f33000 dfsc dfsc.sys Sat Nov 20 04:26:31 2010 (4CE79447)
fffff880`02c68000 fffff880`02c77000 discache discache.sys Mon Jul 13 19:37:18 2009 (4A5BC52E)
fffff880`019c6000 fffff880`019dc000 disk disk.sys Mon Jul 13 19:19:57 2009 (4A5BC11D)
fffff880`05ebc000 fffff880`05ede000 drmk drmk.sys Mon Jul 13 21:01:25 2009 (4A5BD8E5)
fffff880`05f66000 fffff880`05f6f000 dump_atapi dump_atapi.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`05f5a000 fffff880`05f66000 dump_ataport dump_ataport.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`05f6f000 fffff880`05f82000 dump_dumpfve dump_dumpfve.sys Mon Jul 13 19:21:51 2009 (4A5BC18F)
fffff880`05f40000 fffff880`05f4c000 Dxapi Dxapi.sys Mon Jul 13 19:38:28 2009 (4A5BC574)
fffff880`040b4000 fffff880`041a8000 dxgkrnl dxgkrnl.sys Sat Nov 20 04:50:50 2010 (4CE799FA)
fffff880`041a8000 fffff880`041ee000 dxgmms1 dxgmms1.sys Sat Nov 20 04:49:53 2010 (4CE799C1)
fffff880`060af000 fffff880`06186000 eamonm eamonm.sys Wed Jul 14 04:13:43 2010 (4C3D71B7)
fffff880`015c3000 fffff880`015e8000 ehdrv ehdrv.sys Wed Jul 14 04:14:21 2010 (4C3D71DD)
fffff880`061a7000 fffff880`061d4000 epfw epfw.sys Wed Jul 14 04:10:34 2010 (4C3D70FA)
fffff880`04819000 fffff880`04824000 Epfwndis Epfwndis.sys Wed Jul 14 04:10:31 2010 (4C3D70F7)
fffff880`06e36000 fffff880`06e47000 epfwwfp epfwwfp.sys Wed Jul 14 04:10:34 2010 (4C3D70FA)
fffff880`06018000 fffff880`0604e000 fastfat fastfat.SYS Mon Jul 13 19:23:28 2009 (4A5BC1F0)
fffff880`040a4000 fffff880`040b1000 fdc fdc.sys Mon Jul 13 20:00:54 2009 (4A5BCAB6)
fffff880`010a8000 fffff880`010bc000 fileinfo fileinfo.sys Mon Jul 13 19:34:25 2009 (4A5BC481)
fffff880`02dd2000 fffff880`02ddd000 flpydisk flpydisk.sys Mon Jul 13 20:00:54 2009 (4A5BCAB6)
fffff880`0105c000 fffff880`010a8000 fltmgr fltmgr.sys Sat Nov 20 04:19:24 2010 (4CE7929C)
fffff880`013f4000 fffff880`013fe000 Fs_Rec Fs_Rec.sys Mon Jul 13 19:19:45 2009 (4A5BC111)
fffff880`01983000 fffff880`019bd000 fvevol fvevol.sys Sat Nov 20 04:24:06 2010 (4CE793B6)
fffff880`01889000 fffff880`018d3000 fwpkclnt fwpkclnt.sys Sat Nov 20 04:21:37 2010 (4CE79321)
fffff800`02c06000 fffff800`02c4f000 hal hal.dll Sat Nov 20 08:00:25 2010 (4CE7C669)
fffff880`04000000 fffff880`04024000 HDAudBus HDAudBus.sys Sat Nov 20 05:43:42 2010 (4CE7A65E)
fffff880`05ee4000 fffff880`05f40000 HdAudio HdAudio.sys Sat Nov 20 05:44:23 2010 (4CE7A687)
fffff880`03e3b000 fffff880`03e54000 HIDCLASS HIDCLASS.SYS Sat Nov 20 05:43:49 2010 (4CE7A665)
fffff880`04899000 fffff880`048a1080 HIDPARSE HIDPARSE.SYS Mon Jul 13 20:06:17 2009 (4A5BCBF9)
fffff880`05f85000 fffff880`05f93000 hidusb hidusb.sys Sat Nov 20 05:43:49 2010 (4CE7A665)
fffff880`06e64000 fffff880`06f2d000 HTTP HTTP.sys Sat Nov 20 04:24:30 2010 (4CE793CE)
fffff880`019bd000 fffff880`019c6000 hwpolicy hwpolicy.sys Sat Nov 20 04:18:54 2010 (4CE7927E)
fffff880`03e5f000 fffff880`03e6e000 kbdclass kbdclass.sys Mon Jul 13 19:19:50 2009 (4A5BC116)
fffff880`05e51000 fffff880`05e5f000 kbdhid kbdhid.sys Sat Nov 20 05:33:25 2010 (4CE7A3F5)
fffff800`00bcf000 fffff800`00bd9000 kdcom kdcom.dll Mon Jul 13 21:31:07 2009 (4A5BDFDB)
fffff880`011bb000 fffff880`011fe000 ks ks.sys Sat Nov 20 05:33:23 2010 (4CE7A3F3)
fffff880`013c8000 fffff880`013e3000 ksecdd ksecdd.sys Sat Nov 20 04:21:15 2010 (4CE7930B)
fffff880`01460000 fffff880`0148b000 ksecpkg ksecpkg.sys Sat Nov 20 05:10:34 2010 (4CE79E9A)
fffff880`05ede000 fffff880`05ee3200 ksthunk ksthunk.sys Mon Jul 13 20:00:19 2009 (4A5BCA93)
fffff880`04024000 fffff880`04036000 L1E62x64 L1E62x64.sys Sun Aug 23 01:08:09 2009 (4A90CEB9)
fffff880`061d4000 fffff880`061e9000 lltdio lltdio.sys Mon Jul 13 20:08:50 2009 (4A5BCC92)
fffff880`05e00000 fffff880`05e23000 luafv luafv.sys Mon Jul 13 19:26:13 2009 (4A5BC295)
fffff880`00c1a000 fffff880`00c27000 mcupdate mcupdate.dll Mon Jul 13 21:29:09 2009 (4A5BDF65)
fffff880`05fb0000 fffff880`05fbe000 monitor monitor.sys Mon Jul 13 19:38:52 2009 (4A5BC58C)
fffff880`03e6e000 fffff880`03e7d000 mouclass mouclass.sys Mon Jul 13 19:19:50 2009 (4A5BC116)
fffff880`02df2000 fffff880`02dff000 mouhid mouhid.sys Mon Jul 13 20:00:20 2009 (4A5BCA94)
fffff880`00f51000 fffff880`00f6b000 mountmgr mountmgr.sys Sat Nov 20 04:19:21 2010 (4CE79299)
fffff880`06f4b000 fffff880`06f63000 mpsdrv mpsdrv.sys Mon Jul 13 20:08:25 2009 (4A5BCC79)
fffff880`06f63000 fffff880`06f90000 mrxsmb mrxsmb.sys Sat Nov 20 04:27:41 2010 (4CE7948D)
fffff880`06f90000 fffff880`06fdd000 mrxsmb10 mrxsmb10.sys Sat Nov 20 04:26:53 2010 (4CE7945D)
fffff880`06e00000 fffff880`06e24000 mrxsmb20 mrxsmb20.sys Sat Nov 20 04:26:47 2010 (4CE79457)
fffff880`015f1000 fffff880`015fc000 Msfs Msfs.SYS Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`00e6a000 fffff880`00e74000 msisadrv msisadrv.sys Mon Jul 13 19:19:26 2009 (4A5BC0FE)
fffff880`010bc000 fffff880`0111a000 msrpc msrpc.sys Sat Nov 20 04:21:56 2010 (4CE79334)
fffff880`02c5d000 fffff880`02c68000 mssmbios mssmbios.sys Mon Jul 13 19:31:10 2009 (4A5BC3BE)
fffff880`01971000 fffff880`01983000 mup mup.sys Mon Jul 13 19:23:45 2009 (4A5BC201)
fffff880`014d0000 fffff880`015c3000 ndis ndis.sys Sat Nov 20 04:23:30 2010 (4CE79392)
fffff880`0485e000 fffff880`0486a000 ndistapi ndistapi.sys Mon Jul 13 20:10:00 2009 (4A5BCCD8)
fffff880`08e5e000 fffff880`08e71000 ndisuio ndisuio.sys Sat Nov 20 05:50:08 2010 (4CE7A7E0)
fffff880`0486a000 fffff880`04899000 ndiswan ndiswan.sys Sat Nov 20 05:52:32 2010 (4CE7A870)
fffff880`02ddd000 fffff880`02df2000 NDProxy NDProxy.SYS Sat Nov 20 05:52:20 2010 (4CE7A864)
fffff880`02d77000 fffff880`02d86000 netbios netbios.sys Mon Jul 13 20:09:26 2009 (4A5BCCB6)
fffff880`02d03000 fffff880`02d48000 netbt netbt.sys Sat Nov 20 04:23:18 2010 (4CE79386)
fffff880`01400000 fffff880`01460000 NETIO NETIO.SYS Sat Nov 20 04:23:13 2010 (4CE79381)
fffff880`014b5000 fffff880`014c6000 Npfs Npfs.SYS Mon Jul 13 19:19:48 2009 (4A5BC114)
fffff880`02c51000 fffff880`02c5d000 nsiproxy nsiproxy.sys Mon Jul 13 19:21:02 2009 (4A5BC15E)
fffff800`02c4f000 fffff800`03239000 nt ntkrnlmp.exe Sat Nov 20 04:30:02 2010 (4CE7951A)
fffff880`01225000 fffff880`013c8000 Ntfs Ntfs.sys Sat Nov 20 04:20:57 2010 (4CE792F9)
fffff880`01666000 fffff880`0166f000 Null Null.SYS Mon Jul 13 19:19:37 2009 (4A5BC109)
fffff880`08e0b000 fffff880`08e5e000 nwifi nwifi.sys Mon Jul 13 20:07:23 2009 (4A5BCC3B)
fffff880`02d51000 fffff880`02d77000 pacer pacer.sys Sat Nov 20 05:52:18 2010 (4CE7A862)
fffff880`00eb4000 fffff880`00ec9000 partmgr partmgr.sys Sat Nov 20 04:20:00 2010 (4CE792C0)
fffff880`00e74000 fffff880`00ea7000 pci pci.sys Sat Nov 20 04:19:11 2010 (4CE7928F)
fffff880`00f3a000 fffff880`00f41000 pciide pciide.sys Mon Jul 13 19:19:49 2009 (4A5BC115)
fffff880`00f41000 fffff880`00f51000 PCIIDEX PCIIDEX.SYS Mon Jul 13 19:19:48 2009 (4A5BC114)
fffff880`013e3000 fffff880`013f4000 pcw pcw.sys Mon Jul 13 19:19:27 2009 (4A5BC0FF)
fffff880`08a46000 fffff880`08aec000 peauth peauth.sys Mon Jul 13 21:01:19 2009 (4A5BD8DF)
fffff880`05e7f000 fffff880`05ebc000 portcls portcls.sys Mon Jul 13 20:06:27 2009 (4A5BCC03)
fffff880`00c27000 fffff880`00c3b000 PSHED PSHED.dll Mon Jul 13 21:32:23 2009 (4A5BE027)
fffff880`0483a000 fffff880`0485e000 rasl2tp rasl2tp.sys Sat Nov 20 05:52:34 2010 (4CE7A872)
fffff880`03fd3000 fffff880`03fee000 raspppoe raspppoe.sys Mon Jul 13 20:10:17 2009 (4A5BCCE9)
fffff880`03e00000 fffff880`03e21000 raspptp raspptp.sys Sat Nov 20 05:52:31 2010 (4CE7A86F)
fffff880`03e21000 fffff880`03e3b000 rassstp rassstp.sys Mon Jul 13 20:10:25 2009 (4A5BCCF1)
fffff880`02c00000 fffff880`02c51000 rdbss rdbss.sys Sat Nov 20 04:27:51 2010 (4CE79497)
fffff880`03e54000 fffff880`03e5f000 rdpbus rdpbus.sys Mon Jul 13 20:17:46 2009 (4A5BCEAA)
fffff880`019ec000 fffff880`019f5000 RDPCDD RDPCDD.sys Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`019f5000 fffff880`019fe000 rdpencdd rdpencdd.sys Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`015e8000 fffff880`015f1000 rdprefmp rdprefmp.sys Mon Jul 13 20:16:35 2009 (4A5BCE63)
fffff880`01937000 fffff880`01971000 rdyboost rdyboost.sys Sat Nov 20 04:43:10 2010 (4CE7982E)
fffff880`06000000 fffff880`06018000 rspndr rspndr.sys Mon Jul 13 20:08:50 2009 (4A5BCC92)
fffff880`08aec000 fffff880`08af7000 secdrv secdrv.SYS Wed Sep 13 09:18:38 2006 (4508052E)
fffff880`04098000 fffff880`040a4000 serenum serenum.sys Mon Jul 13 20:00:33 2009 (4A5BCAA1)
fffff880`02d86000 fffff880`02da3000 serial serial.sys Mon Jul 13 20:00:40 2009 (4A5BCAA8)
fffff880`0192f000 fffff880`01937000 spldr spldr.sys Mon May 11 12:56:27 2009 (4A0858BB)
fffff880`08ef5000 fffff880`08f8e000 srv srv.sys Sat Nov 20 04:28:05 2010 (4CE794A5)
fffff880`08b3a000 fffff880`08ba5000 srv2 srv2.sys Sat Nov 20 04:27:43 2010 (4CE7948F)
fffff880`08af7000 fffff880`08b28000 srvnet srvnet.sys Sat Nov 20 04:27:20 2010 (4CE79478)
fffff880`048a2000 fffff880`048a3480 swenum swenum.sys Mon Jul 13 20:00:18 2009 (4A5BCA92)
fffff880`01685000 fffff880`01889000 tcpip tcpip.sys Sat Nov 20 04:25:52 2010 (4CE79420)
fffff880`08b28000 fffff880`08b3a000 tcpipreg tcpipreg.sys Sat Nov 20 05:51:48 2010 (4CE7A844)
fffff880`011ae000 fffff880`011bb000 TDI TDI.SYS Sat Nov 20 04:22:06 2010 (4CE7933E)
fffff880`0118c000 fffff880`011ae000 tdx tdx.sys Sat Nov 20 04:21:54 2010 (4CE79332)
fffff880`02dbe000 fffff880`02dd2000 termdd termdd.sys Sat Nov 20 06:03:40 2010 (4CE7AB0C)
fffff960`005c0000 fffff960`005ca000 TSDDD TSDDD.dll Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`03f4a000 fffff880`03f70000 tunnel tunnel.sys Sat Nov 20 05:51:50 2010 (4CE7A846)
fffff880`03fee000 fffff880`04000000 umbus umbus.sys Sat Nov 20 05:44:37 2010 (4CE7A695)
fffff880`05fbe000 fffff880`05fdb000 usbccgp usbccgp.sys Sat Nov 20 05:44:03 2010 (4CE7A673)
fffff880`05f93000 fffff880`05f94f00 USBD USBD.SYS Mon Jul 13 20:06:23 2009 (4A5BCBFF)
fffff880`0407f000 fffff880`04090000 usbehci usbehci.sys Mon Jul 13 20:06:30 2009 (4A5BCC06)
fffff880`01000000 fffff880`0105a000 usbhub usbhub.sys Sat Nov 20 05:44:30 2010 (4CE7A68E)
fffff880`04074000 fffff880`0407f000 usbohci usbohci.sys Mon Jul 13 20:06:30 2009 (4A5BCC06)
fffff880`051a4000 fffff880`051fa000 USBPORT USBPORT.SYS Mon Jul 13 20:06:31 2009 (4A5BCC07)
fffff880`05f95000 fffff880`05fb0000 USBSTOR USBSTOR.SYS Sat Nov 20 05:44:05 2010 (4CE7A675)
fffff880`00ea7000 fffff880`00eb4000 vdrvroot vdrvroot.sys Mon Jul 13 20:01:31 2009 (4A5BCADB)
fffff880`01676000 fffff880`01684000 vga vga.sys Mon Jul 13 19:38:47 2009 (4A5BC587)
fffff880`040b1000 fffff880`040b2d80 vHidDev vHidDev.sys Mon Dec 21 08:49:58 2009 (4B2F7D06)
fffff880`01200000 fffff880`01225000 VIDEOPRT VIDEOPRT.SYS Mon Jul 13 19:38:51 2009 (4A5BC58B)
fffff880`00f6b000 fffff880`00fa7000 vmbus vmbus.sys Sat Nov 20 04:57:29 2010 (4CE79B89)
fffff880`018d3000 fffff880`018e3000 vmstorfl vmstorfl.sys Sat Nov 20 04:57:30 2010 (4CE79B8A)
fffff880`00ec9000 fffff880`00ede000 volmgr volmgr.sys Sat Nov 20 04:19:28 2010 (4CE792A0)
fffff880`00ede000 fffff880`00f3a000 volmgrx volmgrx.sys Sat Nov 20 04:20:43 2010 (4CE792EB)
fffff880`018e3000 fffff880`0192f000 volsnap volsnap.sys Sat Nov 20 04:20:08 2010 (4CE792C8)
fffff880`02da3000 fffff880`02dbe000 wanarp wanarp.sys Sat Nov 20 05:52:36 2010 (4CE7A874)
fffff880`019dc000 fffff880`019ec000 watchdog watchdog.sys Mon Jul 13 19:37:35 2009 (4A5BC53F)
fffff880`00d59000 fffff880`00dfd000 Wdf01000 Wdf01000.sys Mon Jul 13 19:22:07 2009 (4A5BC19F)
fffff880`00c00000 fffff880`00c0f000 WDFLDR WDFLDR.SYS Mon Jul 13 19:19:54 2009 (4A5BC11A)
fffff880`02d48000 fffff880`02d51000 wfplwf wfplwf.sys Mon Jul 13 20:09:26 2009 (4A5BCCB6)
fffff960`00020000 fffff960`00331000 win32k win32k.sys Wed Jan 05 01:55:38 2011 (4D2415EA)
fffff880`00fa7000 fffff880`00fbb000 winhv winhv.sys Sat Nov 20 04:20:02 2010 (4CE792C2)
fffff880`04800000 fffff880`04809000 wmiacpi wmiacpi.sys Mon Jul 13 19:31:02 2009 (4A5BC3B6)
fffff880`00e61000 fffff880`00e6a000 WMILIB WMILIB.SYS Mon Jul 13 19:19:51 2009 (4A5BC117)
fffff880`06186000 fffff880`061a7000 WudfPf WudfPf.sys Sat Nov 20 05:42:44 2010 (4CE7A624)
fffff880`08e71000 fffff880`08ea2000 WUDFRd WUDFRd.sys Sat Nov 20 05:43:32 2010 (4CE7A654)
Unloaded modules:
fffff880`08f8e000 fffff880`08fff000 spsys.sys
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00071000
fffff880`01630000 fffff880`0163e000 crashdmp.sys
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 0000E000
fffff880`0163e000 fffff880`0164a000 dump_ataport
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 0000C000
fffff880`0164a000 fffff880`01653000 dump_atapi.s
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00009000
fffff880`01653000 fffff880`01666000 dump_dumpfve
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00013000cybercore
New Member
- Joined
- Jul 7, 2009
1. Disable Driver Verifier!
2. Old drivers,
AN983X64.sys Thu May 19 04:14:27 2005
Alpham164.sys Mon Jul 23 03:57:03 2007
Crash Dumps:
Drivers:
2. Old drivers,
AN983X64.sys Thu May 19 04:14:27 2005
Alpham164.sys Mon Jul 23 03:57:03 2007
2. Update or disable ADMtek AN983/AN985 based ethernet adapter
AN983X64.sys Thu May 19 04:14:27 2005
3. Update Ideazon ZBoard/Ideazon Fang MM USB HID
Alpham164.sys Mon Jul 23 03:57:03 2007
Alpham264.sys Tue Mar 20 05:51:03 2007
Crash Dumps:
Code:
Microsoft (R) Windows Debugger Version 6.12.0002.633 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [F:\a\Minidump\D M P\DMP\030511-27175-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: SRV*c:\websymbols*http://msdl.microsoft.com/download/symbols
Executable search path is:
Windows 7 Kernel Version 7601 (Service Pack 1) MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS
Built by: 7601.17514.amd64fre.win7sp1_rtm.101119-1850
Machine Name:
Kernel base = 0xfffff800`02c0f000 PsLoadedModuleList = 0xfffff800`02e54e90
Debug session time: Sat Mar 5 00:55:50.700 2011 (UTC - 5:00)
System Uptime: 0 days 0:58:17.214
Loading Kernel Symbols
...............................................................
................................................................
.....................................
Loading User Symbols
Loading unloaded module list
......
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 19, {20, fffffa80062cc4c0, fffffa80062cc740, d28b100}
Unable to load image atikmpag.sys, Win32 error 0n2
*** WARNING: Unable to verify timestamp for atikmpag.sys
*** ERROR: Module load completed but symbols could not be loaded for atikmpag.sys
Probably caused by : atikmpag.sys ( atikmpag+5eaf )
Followup: MachineOwner
---------
2: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
BAD_POOL_HEADER (19)
The pool is already corrupt at the time of the current request.
This may or may not be due to the caller.
The internal pool links must be walked to figure out a possible cause of
the problem, and then special pool applied to the suspect tags or the driver
verifier to a suspect driver.
Arguments:
Arg1: 0000000000000020, a pool block header size is corrupt.
Arg2: fffffa80062cc4c0, The pool entry we were looking for within the page.
Arg3: fffffa80062cc740, The next pool entry.
Arg4: 000000000d28b100, (reserved)
Debugging Details:
------------------
BUGCHECK_STR: 0x19_20
POOL_ADDRESS: GetPointerFromAddress: unable to read from fffff80002ec00e8
fffffa80062cc4c0
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
PROCESS_NAME: BlackOpsMP.exe
CURRENT_IRQL: 0
LAST_CONTROL_TRANSFER: from fffff80002db9cae to fffff80002c8f640
STACK_TEXT:
fffff880`09033408 fffff800`02db9cae : 00000000`00000019 00000000`00000020 fffffa80`062cc4c0 fffffa80`062cc740 : nt!KeBugCheckEx
fffff880`09033410 fffff880`03e05eaf : fffff8a0`0903f330 fffff880`0400a0d1 00000000`7ffff8a0 fffffa80`080b4000 : nt!ExDeferredFreePool+0x12da
fffff880`090334c0 fffff8a0`0903f330 : fffff880`0400a0d1 00000000`7ffff8a0 fffffa80`080b4000 fffff8a0`00000001 : atikmpag+0x5eaf
fffff880`090334c8 fffff880`0400a0d1 : 00000000`7ffff8a0 fffffa80`080b4000 fffff8a0`00000001 fffff8a0`0903f330 : 0xfffff8a0`0903f330
fffff880`090334d0 fffff880`0403d204 : fffffa80`080b4000 00000000`00000000 fffff880`09033570 00000000`00000000 : dxgkrnl!DXGADAPTER::AcquireDdiSync+0xc9
fffff880`09033510 fffff880`040412c1 : fffff8a0`0903f330 00000000`00000000 00000000`00000000 fffff8a0`0136f000 : dxgkrnl!DXGADAPTER::DdiDestroyAllocation+0x50
fffff880`09033540 fffff880`04053784 : 00000000`00000001 00000000`00000000 00000000`00000000 fffff8a0`00000799 : dxgkrnl!DXGDEVICE::DestroyAllocations+0x83d
fffff880`09033630 fffff880`04038815 : 00000000`fffffeda fffff8a0`092de3c0 fffff8a0`0136f000 fffffa80`080b4000 : dxgkrnl!DXGDEVICE::~DXGDEVICE+0x19c
fffff880`090336a0 fffff880`04076e4a : 00000000`00000001 fffffa80`080b4000 fffff8a0`092de3c0 fffff8a0`092de440 : dxgkrnl!DXGADAPTER::DestroyDevice+0x1c9
fffff880`090336d0 fffff880`040767e0 : fffff900`c374d300 00000000`00000000 00000000`00000001 fffff900`c374d300 : dxgkrnl!DXGPROCESS::Destroy+0xba
fffff880`09033780 fffff960`00144e7c : 00000000`00000870 fffff900`c374d300 00000000`00000000 fffff900`c374d300 : dxgkrnl!DxgkProcessCallout+0x268
fffff880`09033810 fffff960`0014457f : 00000000`00000000 fffff880`09033c20 fffffa80`06373660 00000000`00000000 : win32k!GdiProcessCallout+0x244
fffff880`09033890 fffff800`02f65001 : 00000000`00000000 00000000`00000000 00000000`00000000 fffffa80`06373600 : win32k!W32pProcessCallout+0x6b
fffff880`090338c0 fffff800`02f4a37d : 00000000`cfffffff fffff960`00154201 00000000`78457300 fffffa80`093027f0 : nt!PspExitThread+0x4d1
fffff880`090339c0 fffff800`02c82dfa : fffff900`c06c3010 fffff960`00149fa0 fffff900`c06c3010 00000000`00000000 : nt!PsExitSpecialApc+0x1d
fffff880`090339f0 fffff800`02c83140 : 00000000`00000246 fffff880`09033a70 fffff800`02f4a2f0 00000000`00000001 : nt!KiDeliverApc+0x2ca
fffff880`09033a70 fffff800`02c8e977 : fffff880`09033ca0 fffff800`02c9935a 00000000`0000002a 00000000`73ba2450 : nt!KiInitiateUserApc+0x70
fffff880`09033bb0 00000000`73ba2e09 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceExit+0x9c
00000000`349af0f8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x73ba2e09
STACK_COMMAND: kb
FOLLOWUP_IP:
atikmpag+5eaf
fffff880`03e05eaf ?? ???
SYMBOL_STACK_INDEX: 2
SYMBOL_NAME: atikmpag+5eaf
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: atikmpag
IMAGE_NAME: atikmpag.sys
DEBUG_FLR_IMAGE_TIMESTAMP: 4d409c8d
FAILURE_BUCKET_ID: X64_0x19_20_atikmpag+5eaf
BUCKET_ID: X64_0x19_20_atikmpag+5eaf
Followup: MachineOwner
---------
Microsoft (R) Windows Debugger Version 6.12.0002.633 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [F:\a\Minidump\D M P\DMP\030511-25724-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: SRV*c:\websymbols*http://msdl.microsoft.com/download/symbols
Executable search path is:
Windows 7 Kernel Version 7601 (Service Pack 1) MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS
Built by: 7601.17514.amd64fre.win7sp1_rtm.101119-1850
Machine Name:
Kernel base = 0xfffff800`02c4f000 PsLoadedModuleList = 0xfffff800`02e94e90
Debug session time: Sat Mar 5 01:21:18.632 2011 (UTC - 5:00)
System Uptime: 0 days 0:24:43.146
Loading Kernel Symbols
...............................................................
................................................................
.....................................
Loading User Symbols
Loading unloaded module list
.....
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck C4, {91, 2, fffffa800885e4d0, 0}
Probably caused by : ntkrnlmp.exe ( nt! ?? ::FNODOBFM::`string'+4874 )
Followup: MachineOwner
---------
0: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
DRIVER_VERIFIER_DETECTED_VIOLATION (c4)
A device driver attempting to corrupt the system has been caught. This is
because the driver was specified in the registry as being suspect (by the
administrator) and the kernel has enabled substantial checking of this driver.
If the driver attempts to corrupt the system, bugchecks 0xC4, 0xC1 and 0xA will
be among the most commonly seen crashes.
Arguments:
Arg1: 0000000000000091, A driver switched stacks using a method that is not supported by
the operating system. The only supported way to extend a kernel
mode stack is by using KeExpandKernelStackAndCallout.
Arg2: 0000000000000002
Arg3: fffffa800885e4d0
Arg4: 0000000000000000
Debugging Details:
------------------
BUGCHECK_STR: 0xc4_91
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
PROCESS_NAME: svchost.exe
CURRENT_IRQL: 2
EXCEPTION_RECORD: fffff88003c1bd88 -- (.exr 0xfffff88003c1bd88)
ExceptionAddress: fffff80002cd22e2 (nt!SwapContext_PatchXRstor)
ExceptionCode: c0000005 (Access violation)
ExceptionFlags: 00000000
NumberParameters: 2
Parameter[0]: 0000000000000000
Parameter[1]: ffffffffffffffff
Attempt to read from address ffffffffffffffff
TRAP_FRAME: fffff88003c1be30 -- (.trap 0xfffff88003c1be30)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000000000000001 rbx=0000000000000000 rcx=fffff88003c1ce08
rdx=0000000000000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80002cd22e2 rsp=fffff88003c1bfc0 rbp=fffff88003c1cdb8
r8=fffffa80088560e8 r9=0000000000000000 r10=fffffffffffffffe
r11=0000000000000000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na pe nc
nt!SwapContext_PatchXRstor:
fffff800`02cd22e2 0fae09 fxrstor [rcx] ds:1f80:fffff880`03c1ce08=00
Resetting default scope
LAST_CONTROL_TRANSFER: from fffff80002d2653a to fffff80002ccf640
STACK_TEXT:
fffff880`03c1ae88 fffff800`02d2653a : 00000000`000000c4 00000000`00000091 00000000`00000002 fffffa80`0885e4d0 : nt!KeBugCheckEx
fffff880`03c1ae90 fffff800`02cf9963 : 00000000`00000000 00000000`00000000 00000000`00000003 00000000`00000000 : nt! ?? ::FNODOBFM::`string'+0x4874
fffff880`03c1aed0 fffff800`02d0adc1 : fffff880`03c1bd88 fffff880`03c1bae0 fffff880`03c1be30 fffff800`02e4fcc0 : nt!RtlDispatchException+0x33
fffff880`03c1b5b0 fffff800`02ccecc2 : fffff880`03c1bd88 fffff800`02e41e80 fffff880`03c1be30 fffffa80`0885e4d0 : nt!KiDispatchException+0x135
fffff880`03c1bc50 fffff800`02ccd5ca : 00000000`00000001 00000000`00000000 00000000`00000000 fffff880`03c1bea0 : nt!KiExceptionDispatch+0xc2
fffff880`03c1be30 fffff800`02cd22e2 : 00000000`00000000 fffff800`00000000 00000000`00000000 00000000`00000000 : nt!KiGeneralProtectionFault+0x10a
fffff880`03c1bfc0 fffff800`02cd1eda : fffff880`02f64180 fffff800`02cdb9b8 fffffa80`09212801 fffff880`03c1c9d8 : nt!SwapContext_PatchXRstor
fffff880`03c1c000 fffff800`02cd4992 : fffffa80`0885e4d0 fffffa80`0885e4d0 fffff880`00000000 fffff800`00000008 : nt!KiSwapContext+0x7a
fffff880`03c1c140 fffff800`02cd3eaa : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiCommitThreadWait+0x1d2
fffff880`03c1c1d0 fffff800`02fc5ccf : fffff880`0000002a fffff880`03c1c520 00000000`00000001 00000000`00000006 : nt!KeWaitForMultipleObjects+0x272
fffff880`03c1c490 fffff800`02fc603e : fffffa80`0822d301 fffff800`02cd22a4 fffff8a0`00000001 fffff800`00000001 : nt!ObpWaitForMultipleObjects+0x294
fffff880`03c1c960 fffff800`02cce8d3 : fffffa80`0885e4d0 00000000`00c9f708 fffff880`03c1cbc8 fffff880`03c1cc00 : nt!NtWaitForMultipleObjects+0xe5
fffff880`03c1cbb0 00000000`76fb18ca : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x13
00000000`00c9f6e8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x76fb18ca
STACK_COMMAND: kb
FOLLOWUP_IP:
nt! ?? ::FNODOBFM::`string'+4874
fffff800`02d2653a cc int 3
SYMBOL_STACK_INDEX: 1
SYMBOL_NAME: nt! ?? ::FNODOBFM::`string'+4874
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
DEBUG_FLR_IMAGE_TIMESTAMP: 4ce7951a
FAILURE_BUCKET_ID: X64_0xc4_91_nt!_??_::FNODOBFM::_string_+4874
BUCKET_ID: X64_0xc4_91_nt!_??_::FNODOBFM::_string_+4874
Followup: MachineOwner
---------Drivers:
Code:
start end module name
fffff880`04036000 fffff880`04074000 1394ohci 1394ohci.sys Sat Nov 20 05:44:56 2010 (4CE7A6A8)
fffff880`00e0a000 fffff880`00e61000 ACPI ACPI.sys Sat Nov 20 04:19:16 2010 (4CE79294)
fffff880`02c7a000 fffff880`02d03000 afd afd.sys Sat Nov 20 04:23:27 2010 (4CE7938F)
fffff880`04824000 fffff880`0483a000 AgileVpn AgileVpn.sys Mon Jul 13 20:10:24 2009 (4A5BCCF0)
fffff880`05fdb000 fffff880`05fe7f00 Alpham164 Alpham164.sys Mon Jul 23 03:57:03 2007 (46A45F4F)
fffff880`05fe8000 fffff880`05fed500 Alpham264 Alpham264.sys Tue Mar 20 05:51:03 2007 (45FFAE87)
fffff880`03e7d000 fffff880`03e91000 amdiox64 amdiox64.sys Thu Feb 18 10:17:53 2010 (4B7D5A21)
fffff880`03f70000 fffff880`03f85000 amdppm amdppm.sys Mon Jul 13 19:19:25 2009 (4A5BC0FD)
fffff880`00fee000 fffff880`00ff9000 amdxata amdxata.sys Fri Mar 19 12:18:18 2010 (4BA3A3CA)
fffff880`041ee000 fffff880`041ff000 AN983X64 AN983X64.sys Thu May 19 04:14:27 2005 (428C4AE3)
fffff880`04090000 fffff880`04098000 ASACPI ASACPI.sys Wed Jul 15 23:31:29 2009 (4A5E9F11)
fffff880`03f44000 fffff880`03f4a000 AsIO AsIO.sys Thu Apr 22 07:18:03 2010 (4BD0306B)
fffff880`08e00000 fffff880`08e0b000 asyncmac asyncmac.sys Mon Jul 13 20:10:13 2009 (4A5BCCE5)
fffff880`00fbb000 fffff880`00fc4000 atapi atapi.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`00fc4000 fffff880`00fee000 ataport ataport.SYS Sat Nov 20 04:19:15 2010 (4CE79293)
fffff880`05e5f000 fffff880`05e7f000 AtihdW76 AtihdW76.sys Wed Nov 17 07:02:04 2010 (4CE3C43C)
fffff880`048a8000 fffff880`051a4000 atikmdag atikmdag.sys Wed Jan 26 17:48:28 2011 (4D40A4BC)
fffff880`03f85000 fffff880`03fd3000 atikmpag atikmpag.sys Wed Jan 26 17:13:33 2011 (4D409C8D)
fffff880`0166f000 fffff880`01676000 Beep Beep.SYS Mon Jul 13 20:00:13 2009 (4A5BCA8D)
fffff880`03f33000 fffff880`03f44000 blbdrive blbdrive.sys Mon Jul 13 19:35:59 2009 (4A5BC4DF)
fffff880`06f2d000 fffff880`06f4b000 bowser bowser.sys Mon Jul 13 19:23:50 2009 (4A5BC206)
fffff960`006a0000 fffff960`006c7000 cdd cdd.dll Sat Nov 20 07:55:34 2010 (4CE7C546)
fffff880`0148b000 fffff880`014b5000 cdrom cdrom.sys Sat Nov 20 04:19:20 2010 (4CE79298)
fffff880`00c99000 fffff880`00d59000 CI CI.dll Sat Nov 20 08:12:36 2010 (4CE7C944)
fffff880`01600000 fffff880`01630000 CLASSPNP CLASSPNP.SYS Sat Nov 20 04:19:23 2010 (4CE7929B)
fffff880`00c3b000 fffff880`00c99000 CLFS CLFS.SYS Mon Jul 13 19:19:57 2009 (4A5BC11D)
fffff880`0111a000 fffff880`0118c000 cng cng.sys Sat Nov 20 05:08:45 2010 (4CE79E2D)
fffff880`04809000 fffff880`04819000 CompositeBus CompositeBus.sys Sat Nov 20 05:33:17 2010 (4CE7A3ED)
fffff880`06e24000 fffff880`06e2d000 cpuz133_x64 cpuz133_x64.sys Tue May 11 05:58:57 2010 (4BE92A61)
fffff880`06e2d000 fffff880`06e36000 cpuz134_x64 cpuz134_x64.sys Fri Jul 09 07:16:58 2010 (4C37052A)
fffff880`05f4c000 fffff880`05f5a000 crashdmp crashdmp.sys Mon Jul 13 20:01:01 2009 (4A5BCABD)
fffff880`03e92000 fffff880`03f15000 csc csc.sys Sat Nov 20 04:27:12 2010 (4CE79470)
fffff880`05f82000 fffff880`05f84f00 dadder dadder.sys Mon Apr 19 05:04:42 2010 (4BCC1CAA)
fffff880`03f15000 fffff880`03f33000 dfsc dfsc.sys Sat Nov 20 04:26:31 2010 (4CE79447)
fffff880`02c68000 fffff880`02c77000 discache discache.sys Mon Jul 13 19:37:18 2009 (4A5BC52E)
fffff880`019c6000 fffff880`019dc000 disk disk.sys Mon Jul 13 19:19:57 2009 (4A5BC11D)
fffff880`05ebc000 fffff880`05ede000 drmk drmk.sys Mon Jul 13 21:01:25 2009 (4A5BD8E5)
fffff880`05f66000 fffff880`05f6f000 dump_atapi dump_atapi.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`05f5a000 fffff880`05f66000 dump_ataport dump_ataport.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`05f6f000 fffff880`05f82000 dump_dumpfve dump_dumpfve.sys Mon Jul 13 19:21:51 2009 (4A5BC18F)
fffff880`05f40000 fffff880`05f4c000 Dxapi Dxapi.sys Mon Jul 13 19:38:28 2009 (4A5BC574)
fffff880`040b4000 fffff880`041a8000 dxgkrnl dxgkrnl.sys Sat Nov 20 04:50:50 2010 (4CE799FA)
fffff880`041a8000 fffff880`041ee000 dxgmms1 dxgmms1.sys Sat Nov 20 04:49:53 2010 (4CE799C1)
fffff880`060af000 fffff880`06186000 eamonm eamonm.sys Wed Jul 14 04:13:43 2010 (4C3D71B7)
fffff880`015c3000 fffff880`015e8000 ehdrv ehdrv.sys Wed Jul 14 04:14:21 2010 (4C3D71DD)
fffff880`061a7000 fffff880`061d4000 epfw epfw.sys Wed Jul 14 04:10:34 2010 (4C3D70FA)
fffff880`04819000 fffff880`04824000 Epfwndis Epfwndis.sys Wed Jul 14 04:10:31 2010 (4C3D70F7)
fffff880`06e36000 fffff880`06e47000 epfwwfp epfwwfp.sys Wed Jul 14 04:10:34 2010 (4C3D70FA)
fffff880`06018000 fffff880`0604e000 fastfat fastfat.SYS Mon Jul 13 19:23:28 2009 (4A5BC1F0)
fffff880`040a4000 fffff880`040b1000 fdc fdc.sys Mon Jul 13 20:00:54 2009 (4A5BCAB6)
fffff880`010a8000 fffff880`010bc000 fileinfo fileinfo.sys Mon Jul 13 19:34:25 2009 (4A5BC481)
fffff880`02dd2000 fffff880`02ddd000 flpydisk flpydisk.sys Mon Jul 13 20:00:54 2009 (4A5BCAB6)
fffff880`0105c000 fffff880`010a8000 fltmgr fltmgr.sys Sat Nov 20 04:19:24 2010 (4CE7929C)
fffff880`013f4000 fffff880`013fe000 Fs_Rec Fs_Rec.sys Mon Jul 13 19:19:45 2009 (4A5BC111)
fffff880`01983000 fffff880`019bd000 fvevol fvevol.sys Sat Nov 20 04:24:06 2010 (4CE793B6)
fffff880`01889000 fffff880`018d3000 fwpkclnt fwpkclnt.sys Sat Nov 20 04:21:37 2010 (4CE79321)
fffff800`02c06000 fffff800`02c4f000 hal hal.dll Sat Nov 20 08:00:25 2010 (4CE7C669)
fffff880`04000000 fffff880`04024000 HDAudBus HDAudBus.sys Sat Nov 20 05:43:42 2010 (4CE7A65E)
fffff880`05ee4000 fffff880`05f40000 HdAudio HdAudio.sys Sat Nov 20 05:44:23 2010 (4CE7A687)
fffff880`03e3b000 fffff880`03e54000 HIDCLASS HIDCLASS.SYS Sat Nov 20 05:43:49 2010 (4CE7A665)
fffff880`04899000 fffff880`048a1080 HIDPARSE HIDPARSE.SYS Mon Jul 13 20:06:17 2009 (4A5BCBF9)
fffff880`05f85000 fffff880`05f93000 hidusb hidusb.sys Sat Nov 20 05:43:49 2010 (4CE7A665)
fffff880`06e64000 fffff880`06f2d000 HTTP HTTP.sys Sat Nov 20 04:24:30 2010 (4CE793CE)
fffff880`019bd000 fffff880`019c6000 hwpolicy hwpolicy.sys Sat Nov 20 04:18:54 2010 (4CE7927E)
fffff880`03e5f000 fffff880`03e6e000 kbdclass kbdclass.sys Mon Jul 13 19:19:50 2009 (4A5BC116)
fffff880`05e51000 fffff880`05e5f000 kbdhid kbdhid.sys Sat Nov 20 05:33:25 2010 (4CE7A3F5)
fffff800`00bcf000 fffff800`00bd9000 kdcom kdcom.dll Mon Jul 13 21:31:07 2009 (4A5BDFDB)
fffff880`011bb000 fffff880`011fe000 ks ks.sys Sat Nov 20 05:33:23 2010 (4CE7A3F3)
fffff880`013c8000 fffff880`013e3000 ksecdd ksecdd.sys Sat Nov 20 04:21:15 2010 (4CE7930B)
fffff880`01460000 fffff880`0148b000 ksecpkg ksecpkg.sys Sat Nov 20 05:10:34 2010 (4CE79E9A)
fffff880`05ede000 fffff880`05ee3200 ksthunk ksthunk.sys Mon Jul 13 20:00:19 2009 (4A5BCA93)
fffff880`04024000 fffff880`04036000 L1E62x64 L1E62x64.sys Sun Aug 23 01:08:09 2009 (4A90CEB9)
fffff880`061d4000 fffff880`061e9000 lltdio lltdio.sys Mon Jul 13 20:08:50 2009 (4A5BCC92)
fffff880`05e00000 fffff880`05e23000 luafv luafv.sys Mon Jul 13 19:26:13 2009 (4A5BC295)
fffff880`00c1a000 fffff880`00c27000 mcupdate mcupdate.dll Mon Jul 13 21:29:09 2009 (4A5BDF65)
fffff880`05fb0000 fffff880`05fbe000 monitor monitor.sys Mon Jul 13 19:38:52 2009 (4A5BC58C)
fffff880`03e6e000 fffff880`03e7d000 mouclass mouclass.sys Mon Jul 13 19:19:50 2009 (4A5BC116)
fffff880`02df2000 fffff880`02dff000 mouhid mouhid.sys Mon Jul 13 20:00:20 2009 (4A5BCA94)
fffff880`00f51000 fffff880`00f6b000 mountmgr mountmgr.sys Sat Nov 20 04:19:21 2010 (4CE79299)
fffff880`06f4b000 fffff880`06f63000 mpsdrv mpsdrv.sys Mon Jul 13 20:08:25 2009 (4A5BCC79)
fffff880`06f63000 fffff880`06f90000 mrxsmb mrxsmb.sys Sat Nov 20 04:27:41 2010 (4CE7948D)
fffff880`06f90000 fffff880`06fdd000 mrxsmb10 mrxsmb10.sys Sat Nov 20 04:26:53 2010 (4CE7945D)
fffff880`06e00000 fffff880`06e24000 mrxsmb20 mrxsmb20.sys Sat Nov 20 04:26:47 2010 (4CE79457)
fffff880`015f1000 fffff880`015fc000 Msfs Msfs.SYS Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`00e6a000 fffff880`00e74000 msisadrv msisadrv.sys Mon Jul 13 19:19:26 2009 (4A5BC0FE)
fffff880`010bc000 fffff880`0111a000 msrpc msrpc.sys Sat Nov 20 04:21:56 2010 (4CE79334)
fffff880`02c5d000 fffff880`02c68000 mssmbios mssmbios.sys Mon Jul 13 19:31:10 2009 (4A5BC3BE)
fffff880`01971000 fffff880`01983000 mup mup.sys Mon Jul 13 19:23:45 2009 (4A5BC201)
fffff880`014d0000 fffff880`015c3000 ndis ndis.sys Sat Nov 20 04:23:30 2010 (4CE79392)
fffff880`0485e000 fffff880`0486a000 ndistapi ndistapi.sys Mon Jul 13 20:10:00 2009 (4A5BCCD8)
fffff880`08e5e000 fffff880`08e71000 ndisuio ndisuio.sys Sat Nov 20 05:50:08 2010 (4CE7A7E0)
fffff880`0486a000 fffff880`04899000 ndiswan ndiswan.sys Sat Nov 20 05:52:32 2010 (4CE7A870)
fffff880`02ddd000 fffff880`02df2000 NDProxy NDProxy.SYS Sat Nov 20 05:52:20 2010 (4CE7A864)
fffff880`02d77000 fffff880`02d86000 netbios netbios.sys Mon Jul 13 20:09:26 2009 (4A5BCCB6)
fffff880`02d03000 fffff880`02d48000 netbt netbt.sys Sat Nov 20 04:23:18 2010 (4CE79386)
fffff880`01400000 fffff880`01460000 NETIO NETIO.SYS Sat Nov 20 04:23:13 2010 (4CE79381)
fffff880`014b5000 fffff880`014c6000 Npfs Npfs.SYS Mon Jul 13 19:19:48 2009 (4A5BC114)
fffff880`02c51000 fffff880`02c5d000 nsiproxy nsiproxy.sys Mon Jul 13 19:21:02 2009 (4A5BC15E)
fffff800`02c4f000 fffff800`03239000 nt ntkrnlmp.exe Sat Nov 20 04:30:02 2010 (4CE7951A)
fffff880`01225000 fffff880`013c8000 Ntfs Ntfs.sys Sat Nov 20 04:20:57 2010 (4CE792F9)
fffff880`01666000 fffff880`0166f000 Null Null.SYS Mon Jul 13 19:19:37 2009 (4A5BC109)
fffff880`08e0b000 fffff880`08e5e000 nwifi nwifi.sys Mon Jul 13 20:07:23 2009 (4A5BCC3B)
fffff880`02d51000 fffff880`02d77000 pacer pacer.sys Sat Nov 20 05:52:18 2010 (4CE7A862)
fffff880`00eb4000 fffff880`00ec9000 partmgr partmgr.sys Sat Nov 20 04:20:00 2010 (4CE792C0)
fffff880`00e74000 fffff880`00ea7000 pci pci.sys Sat Nov 20 04:19:11 2010 (4CE7928F)
fffff880`00f3a000 fffff880`00f41000 pciide pciide.sys Mon Jul 13 19:19:49 2009 (4A5BC115)
fffff880`00f41000 fffff880`00f51000 PCIIDEX PCIIDEX.SYS Mon Jul 13 19:19:48 2009 (4A5BC114)
fffff880`013e3000 fffff880`013f4000 pcw pcw.sys Mon Jul 13 19:19:27 2009 (4A5BC0FF)
fffff880`08a46000 fffff880`08aec000 peauth peauth.sys Mon Jul 13 21:01:19 2009 (4A5BD8DF)
fffff880`05e7f000 fffff880`05ebc000 portcls portcls.sys Mon Jul 13 20:06:27 2009 (4A5BCC03)
fffff880`00c27000 fffff880`00c3b000 PSHED PSHED.dll Mon Jul 13 21:32:23 2009 (4A5BE027)
fffff880`0483a000 fffff880`0485e000 rasl2tp rasl2tp.sys Sat Nov 20 05:52:34 2010 (4CE7A872)
fffff880`03fd3000 fffff880`03fee000 raspppoe raspppoe.sys Mon Jul 13 20:10:17 2009 (4A5BCCE9)
fffff880`03e00000 fffff880`03e21000 raspptp raspptp.sys Sat Nov 20 05:52:31 2010 (4CE7A86F)
fffff880`03e21000 fffff880`03e3b000 rassstp rassstp.sys Mon Jul 13 20:10:25 2009 (4A5BCCF1)
fffff880`02c00000 fffff880`02c51000 rdbss rdbss.sys Sat Nov 20 04:27:51 2010 (4CE79497)
fffff880`03e54000 fffff880`03e5f000 rdpbus rdpbus.sys Mon Jul 13 20:17:46 2009 (4A5BCEAA)
fffff880`019ec000 fffff880`019f5000 RDPCDD RDPCDD.sys Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`019f5000 fffff880`019fe000 rdpencdd rdpencdd.sys Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`015e8000 fffff880`015f1000 rdprefmp rdprefmp.sys Mon Jul 13 20:16:35 2009 (4A5BCE63)
fffff880`01937000 fffff880`01971000 rdyboost rdyboost.sys Sat Nov 20 04:43:10 2010 (4CE7982E)
fffff880`06000000 fffff880`06018000 rspndr rspndr.sys Mon Jul 13 20:08:50 2009 (4A5BCC92)
fffff880`08aec000 fffff880`08af7000 secdrv secdrv.SYS Wed Sep 13 09:18:38 2006 (4508052E)
fffff880`04098000 fffff880`040a4000 serenum serenum.sys Mon Jul 13 20:00:33 2009 (4A5BCAA1)
fffff880`02d86000 fffff880`02da3000 serial serial.sys Mon Jul 13 20:00:40 2009 (4A5BCAA8)
fffff880`0192f000 fffff880`01937000 spldr spldr.sys Mon May 11 12:56:27 2009 (4A0858BB)
fffff880`08ef5000 fffff880`08f8e000 srv srv.sys Sat Nov 20 04:28:05 2010 (4CE794A5)
fffff880`08b3a000 fffff880`08ba5000 srv2 srv2.sys Sat Nov 20 04:27:43 2010 (4CE7948F)
fffff880`08af7000 fffff880`08b28000 srvnet srvnet.sys Sat Nov 20 04:27:20 2010 (4CE79478)
fffff880`048a2000 fffff880`048a3480 swenum swenum.sys Mon Jul 13 20:00:18 2009 (4A5BCA92)
fffff880`01685000 fffff880`01889000 tcpip tcpip.sys Sat Nov 20 04:25:52 2010 (4CE79420)
fffff880`08b28000 fffff880`08b3a000 tcpipreg tcpipreg.sys Sat Nov 20 05:51:48 2010 (4CE7A844)
fffff880`011ae000 fffff880`011bb000 TDI TDI.SYS Sat Nov 20 04:22:06 2010 (4CE7933E)
fffff880`0118c000 fffff880`011ae000 tdx tdx.sys Sat Nov 20 04:21:54 2010 (4CE79332)
fffff880`02dbe000 fffff880`02dd2000 termdd termdd.sys Sat Nov 20 06:03:40 2010 (4CE7AB0C)
fffff960`005c0000 fffff960`005ca000 TSDDD TSDDD.dll Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`03f4a000 fffff880`03f70000 tunnel tunnel.sys Sat Nov 20 05:51:50 2010 (4CE7A846)
fffff880`03fee000 fffff880`04000000 umbus umbus.sys Sat Nov 20 05:44:37 2010 (4CE7A695)
fffff880`05fbe000 fffff880`05fdb000 usbccgp usbccgp.sys Sat Nov 20 05:44:03 2010 (4CE7A673)
fffff880`05f93000 fffff880`05f94f00 USBD USBD.SYS Mon Jul 13 20:06:23 2009 (4A5BCBFF)
fffff880`0407f000 fffff880`04090000 usbehci usbehci.sys Mon Jul 13 20:06:30 2009 (4A5BCC06)
fffff880`01000000 fffff880`0105a000 usbhub usbhub.sys Sat Nov 20 05:44:30 2010 (4CE7A68E)
fffff880`04074000 fffff880`0407f000 usbohci usbohci.sys Mon Jul 13 20:06:30 2009 (4A5BCC06)
fffff880`051a4000 fffff880`051fa000 USBPORT USBPORT.SYS Mon Jul 13 20:06:31 2009 (4A5BCC07)
fffff880`05f95000 fffff880`05fb0000 USBSTOR USBSTOR.SYS Sat Nov 20 05:44:05 2010 (4CE7A675)
fffff880`00ea7000 fffff880`00eb4000 vdrvroot vdrvroot.sys Mon Jul 13 20:01:31 2009 (4A5BCADB)
fffff880`01676000 fffff880`01684000 vga vga.sys Mon Jul 13 19:38:47 2009 (4A5BC587)
fffff880`040b1000 fffff880`040b2d80 vHidDev vHidDev.sys Mon Dec 21 08:49:58 2009 (4B2F7D06)
fffff880`01200000 fffff880`01225000 VIDEOPRT VIDEOPRT.SYS Mon Jul 13 19:38:51 2009 (4A5BC58B)
fffff880`00f6b000 fffff880`00fa7000 vmbus vmbus.sys Sat Nov 20 04:57:29 2010 (4CE79B89)
fffff880`018d3000 fffff880`018e3000 vmstorfl vmstorfl.sys Sat Nov 20 04:57:30 2010 (4CE79B8A)
fffff880`00ec9000 fffff880`00ede000 volmgr volmgr.sys Sat Nov 20 04:19:28 2010 (4CE792A0)
fffff880`00ede000 fffff880`00f3a000 volmgrx volmgrx.sys Sat Nov 20 04:20:43 2010 (4CE792EB)
fffff880`018e3000 fffff880`0192f000 volsnap volsnap.sys Sat Nov 20 04:20:08 2010 (4CE792C8)
fffff880`02da3000 fffff880`02dbe000 wanarp wanarp.sys Sat Nov 20 05:52:36 2010 (4CE7A874)
fffff880`019dc000 fffff880`019ec000 watchdog watchdog.sys Mon Jul 13 19:37:35 2009 (4A5BC53F)
fffff880`00d59000 fffff880`00dfd000 Wdf01000 Wdf01000.sys Mon Jul 13 19:22:07 2009 (4A5BC19F)
fffff880`00c00000 fffff880`00c0f000 WDFLDR WDFLDR.SYS Mon Jul 13 19:19:54 2009 (4A5BC11A)
fffff880`02d48000 fffff880`02d51000 wfplwf wfplwf.sys Mon Jul 13 20:09:26 2009 (4A5BCCB6)
fffff960`00020000 fffff960`00331000 win32k win32k.sys Wed Jan 05 01:55:38 2011 (4D2415EA)
fffff880`00fa7000 fffff880`00fbb000 winhv winhv.sys Sat Nov 20 04:20:02 2010 (4CE792C2)
fffff880`04800000 fffff880`04809000 wmiacpi wmiacpi.sys Mon Jul 13 19:31:02 2009 (4A5BC3B6)
fffff880`00e61000 fffff880`00e6a000 WMILIB WMILIB.SYS Mon Jul 13 19:19:51 2009 (4A5BC117)
fffff880`06186000 fffff880`061a7000 WudfPf WudfPf.sys Sat Nov 20 05:42:44 2010 (4CE7A624)
fffff880`08e71000 fffff880`08ea2000 WUDFRd WUDFRd.sys Sat Nov 20 05:43:32 2010 (4CE7A654)
Unloaded modules:
fffff880`08f8e000 fffff880`08fff000 spsys.sys
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00071000
fffff880`01630000 fffff880`0163e000 crashdmp.sys
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 0000E000
fffff880`0163e000 fffff880`0164a000 dump_ataport
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 0000C000
fffff880`0164a000 fffff880`01653000 dump_atapi.s
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00009000
fffff880`01653000 fffff880`01666000 dump_dumpfve
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00013000cybercore
New Member
- Joined
- Jul 7, 2009
Welcome to windows7forums,
1. Update Ideazon ZBoard Keyboard
Alpham164.sys Mon Jul 23 03:57:03 2007
Alpham264.sys Tue Mar 20 05:51:03 2007
2. If crashes persist, attach your CPU-Z memory tab + Rammon txt report:
http://windows7forums.com/blue-scre...mportant-every-thread-starter-please-see.html
Crash Dumps:
Drivers:
030511-27783-01.dmp
BugCheck 113, {4, fffffa8008d4a0d0, 0, 0}
VIDEO_DXGKRNL_FATAL_ERROR (113)
PROCESS_NAME: System
Stack: nt nt dxgmms1 dxgmms1 dxgmms1 dxgmms1 dxgmms1 dxgmms1 dxgmms1 dxgmms1 watchdog nt
The dxgkrnl has detected that a violation has occurred. This resulted
in a condition that dxgkrnl can no longer progress.
Probably caused by : dxgmms1.sys ( dxgmms1!DXGFASTMUTEX::Release+50 )
1. Update Ideazon ZBoard Keyboard
Alpham164.sys Mon Jul 23 03:57:03 2007
Alpham264.sys Tue Mar 20 05:51:03 2007
2. If crashes persist, attach your CPU-Z memory tab + Rammon txt report:
http://windows7forums.com/blue-scre...mportant-every-thread-starter-please-see.html
Crash Dumps:
Code:
Microsoft (R) Windows Debugger Version 6.12.0002.633 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [F:\a\Minidump\D M P\DMP\030511-27783-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: SRV*c:\websymbols*http://msdl.microsoft.com/download/symbols
Executable search path is:
Windows 7 Kernel Version 7601 (Service Pack 1) MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS
Built by: 7601.17514.amd64fre.win7sp1_rtm.101119-1850
Machine Name:
Kernel base = 0xfffff800`02c61000 PsLoadedModuleList = 0xfffff800`02ea6e90
Debug session time: Sat Mar 5 15:18:21.889 2011 (UTC - 5:00)
System Uptime: 0 days 0:04:04.403
Loading Kernel Symbols
...............................................................
................................................................
....................................
Loading User Symbols
Loading unloaded module list
....
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 113, {4, fffffa8008d4a0d0, 0, 0}
Probably caused by : dxgmms1.sys ( dxgmms1!DXGFASTMUTEX::Release+50 )
Followup: MachineOwner
---------
2: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
VIDEO_DXGKRNL_FATAL_ERROR (113)
The dxgkrnl has detected that a violation has occurred. This resulted
in a condition that dxgkrnl can no longer progress. By crashing, dxgkrnl
is attempting to get enough information into the minidump such that somebody
can pinpoint the crash cause. Any other values after parameter 1 must be
individually examined according to the subtype.
Arguments:
Arg1: 0000000000000004, The subtype of the bugcheck:
Arg2: fffffa8008d4a0d0
Arg3: 0000000000000000
Arg4: 0000000000000000
Debugging Details:
------------------
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
BUGCHECK_STR: 0x113
PROCESS_NAME: System
CURRENT_IRQL: 0
LAST_CONTROL_TRANSFER: from fffff880015d922f to fffff80002ce1640
STACK_TEXT:
fffff880`0593ba58 fffff880`015d922f : 00000000`00000113 00000000`00000004 fffffa80`08d4a0d0 00000000`00000000 : nt!KeBugCheckEx
fffff880`0593ba60 fffff880`04005e50 : fffff880`00000001 fffffa80`08d4a0d0 00000000`00000000 fffff8a0`079f8c48 : watchdog!WdLogEvent5+0x11b
fffff880`0593bab0 fffff880`0402daad : fffff8a0`00000090 00000000`00000000 00000000`00000000 fffff8a0`079f8c48 : dxgmms1!DXGFASTMUTEX::Release+0x50
fffff880`0593bae0 fffff880`0402025d : fffff8a0`079f8b40 fffffa80`08359000 fffffa80`08793410 fffffa80`08359000 : dxgmms1!VIDMM_APERTURE_SEGMENT::EvictResource+0x31d
fffff880`0593bb30 fffff880`0401b358 : fffffa80`08a6a2c0 00000000`00000000 00000000`00000000 fffff880`0593bca0 : dxgmms1!VIDMM_GLOBAL::ProcessDeferredCommand+0x96d
fffff880`0593bc50 fffff880`0403916d : fffffa80`00000000 fffffa80`0833c010 00000000`0000000f fffff880`0403af09 : dxgmms1!VidMmiProcessTerminationCommand+0x4c
fffff880`0593bca0 fffff880`040383f8 : fffff800`00b96080 fffffa80`0924b530 00000000`00000000 fffffa80`0833c010 : dxgmms1!VidSchiSubmitDeviceCommand+0x39
fffff880`0593bcd0 fffff880`04037e96 : 00000000`00000000 fffffa80`0924b530 00000000`00000080 fffffa80`0833c010 : dxgmms1!VidSchiSubmitQueueCommand+0xb0
fffff880`0593bd00 fffff800`02f7ecce : 00000000`105f2b10 fffffa80`08358620 fffffa80`0611b040 fffffa80`08358620 : dxgmms1!VidSchiWorkerThread+0xd6
fffff880`0593bd40 fffff800`02cd2fe6 : fffff800`02e53e80 fffffa80`08358620 fffff800`02e61cc0 fffff880`01228384 : nt!PspSystemThreadStartup+0x5a
fffff880`0593bd80 00000000`00000000 : fffff880`0593c000 fffff880`05936000 fffff880`0593b470 00000000`00000000 : nt!KxStartSystemThread+0x16
STACK_COMMAND: kb
FOLLOWUP_IP:
dxgmms1!DXGFASTMUTEX::Release+50
fffff880`04005e50 c74424306fffffff mov dword ptr [rsp+30h],0FFFFFF6Fh
SYMBOL_STACK_INDEX: 2
SYMBOL_NAME: dxgmms1!DXGFASTMUTEX::Release+50
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: dxgmms1
IMAGE_NAME: dxgmms1.sys
DEBUG_FLR_IMAGE_TIMESTAMP: 4ce799c1
FAILURE_BUCKET_ID: X64_0x113_dxgmms1!DXGFASTMUTEX::Release+50
BUCKET_ID: X64_0x113_dxgmms1!DXGFASTMUTEX::Release+50
Followup: MachineOwner
---------Drivers:
Code:
start end module name
fffff880`0407c000 fffff880`040ba000 1394ohci 1394ohci.sys Sat Nov 20 05:44:56 2010 (4CE7A6A8)
fffff880`00e06000 fffff880`00e5d000 ACPI ACPI.sys Sat Nov 20 04:19:16 2010 (4CE79294)
fffff880`02cdd000 fffff880`02d66000 afd afd.sys Sat Nov 20 04:23:27 2010 (4CE7938F)
fffff880`05180000 fffff880`05196000 AgileVpn AgileVpn.sys Mon Jul 13 20:10:24 2009 (4A5BCCF0)
fffff880`0520e000 fffff880`0521af00 Alpham164 Alpham164.sys Mon Jul 23 03:57:03 2007 (46A45F4F)
fffff880`0480b000 fffff880`04810500 Alpham264 Alpham264.sys Tue Mar 20 05:51:03 2007 (45FFAE87)
fffff880`03fea000 fffff880`03ffe000 amdiox64 amdiox64.sys Thu Feb 18 10:17:53 2010 (4B7D5A21)
fffff880`03efa000 fffff880`03f0f000 amdppm amdppm.sys Mon Jul 13 19:19:25 2009 (4A5BC0FD)
fffff880`00fea000 fffff880`00ff5000 amdxata amdxata.sys Fri Mar 19 12:18:18 2010 (4BA3A3CA)
fffff880`041cf000 fffff880`041d7000 ASACPI ASACPI.sys Wed Jul 15 23:31:29 2009 (4A5E9F11)
fffff880`03ece000 fffff880`03ed4000 AsIO AsIO.sys Thu Apr 22 07:18:03 2010 (4BD0306B)
fffff880`08871000 fffff880`0887c000 asyncmac asyncmac.sys Mon Jul 13 20:10:13 2009 (4A5BCCE5)
fffff880`00fb7000 fffff880`00fc0000 atapi atapi.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`00fc0000 fffff880`00fea000 ataport ataport.SYS Sat Nov 20 04:19:15 2010 (4CE79293)
fffff880`052b0000 fffff880`052d0000 AtihdW76 AtihdW76.sys Wed Nov 17 07:02:04 2010 (4CE3C43C)
fffff880`04813000 fffff880`0510f000 atikmdag atikmdag.sys Wed Jan 26 17:48:28 2011 (4D40A4BC)
fffff880`03f0f000 fffff880`03f5d000 atikmpag atikmpag.sys Wed Jan 26 17:13:33 2011 (4D409C8D)
fffff880`019f6000 fffff880`019fd000 Beep Beep.SYS Mon Jul 13 20:00:13 2009 (4A5BCA8D)
fffff880`03ebd000 fffff880`03ece000 blbdrive blbdrive.sys Mon Jul 13 19:35:59 2009 (4A5BC4DF)
fffff880`03b16000 fffff880`03b34000 bowser bowser.sys Mon Jul 13 19:23:50 2009 (4A5BC206)
fffff960`007b0000 fffff960`007d7000 cdd cdd.dll Sat Nov 20 07:55:34 2010 (4CE7C546)
fffff880`01600000 fffff880`0162a000 cdrom cdrom.sys Sat Nov 20 04:19:20 2010 (4CE79298)
fffff880`00c9a000 fffff880`00d5a000 CI CI.dll Sat Nov 20 08:12:36 2010 (4CE7C944)
fffff880`01987000 fffff880`019b7000 CLASSPNP CLASSPNP.SYS Sat Nov 20 04:19:23 2010 (4CE7929B)
fffff880`00c3c000 fffff880`00c9a000 CLFS CLFS.SYS Mon Jul 13 19:19:57 2009 (4A5BC11D)
fffff880`01122000 fffff880`01194000 cng cng.sys Sat Nov 20 05:08:45 2010 (4CE79E2D)
fffff880`05165000 fffff880`05175000 CompositeBus CompositeBus.sys Sat Nov 20 05:33:17 2010 (4CE7A3ED)
fffff880`03bea000 fffff880`03bf3000 cpuz133_x64 cpuz133_x64.sys Tue May 11 05:58:57 2010 (4BE92A61)
fffff880`03bf3000 fffff880`03bfc000 cpuz134_x64 cpuz134_x64.sys Fri Jul 09 07:16:58 2010 (4C37052A)
fffff880`0539d000 fffff880`053ab000 crashdmp crashdmp.sys Mon Jul 13 20:01:01 2009 (4A5BCABD)
fffff880`03e1c000 fffff880`03e9f000 csc csc.sys Sat Nov 20 04:27:12 2010 (4CE79470)
fffff880`03e9f000 fffff880`03ebd000 dfsc dfsc.sys Sat Nov 20 04:26:31 2010 (4CE79447)
fffff880`02cb4000 fffff880`02cc3000 discache discache.sys Mon Jul 13 19:37:18 2009 (4A5BC52E)
fffff880`01971000 fffff880`01987000 disk disk.sys Mon Jul 13 19:19:57 2009 (4A5BC11D)
fffff880`0530d000 fffff880`0532f000 drmk drmk.sys Mon Jul 13 21:01:25 2009 (4A5BD8E5)
fffff880`053b7000 fffff880`053c0000 dump_atapi dump_atapi.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`053ab000 fffff880`053b7000 dump_ataport dump_ataport.sys Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`053c0000 fffff880`053d3000 dump_dumpfve dump_dumpfve.sys Mon Jul 13 19:21:51 2009 (4A5BC18F)
fffff880`05391000 fffff880`0539d000 Dxapi Dxapi.sys Mon Jul 13 19:38:28 2009 (4A5BC574)
fffff880`040ca000 fffff880`041be000 dxgkrnl dxgkrnl.sys Sat Nov 20 04:50:50 2010 (4CE799FA)
fffff880`04000000 fffff880`04046000 dxgmms1 dxgmms1.sys Sat Nov 20 04:49:53 2010 (4CE799C1)
fffff880`02a59000 fffff880`02b30000 eamonm eamonm.sys Wed Jul 14 04:13:43 2010 (4C3D71B7)
fffff880`01580000 fffff880`015a5000 ehdrv ehdrv.sys Wed Jul 14 04:14:21 2010 (4C3D71DD)
fffff880`02b51000 fffff880`02b7e000 epfw epfw.sys Wed Jul 14 04:10:34 2010 (4C3D70FA)
fffff880`05175000 fffff880`05180000 Epfwndis Epfwndis.sys Wed Jul 14 04:10:31 2010 (4C3D70F7)
fffff880`03a00000 fffff880`03a11000 epfwwfp epfwwfp.sys Wed Jul 14 04:10:34 2010 (4C3D70FA)
fffff880`03a11000 fffff880`03a47000 fastfat fastfat.SYS Mon Jul 13 19:23:28 2009 (4A5BC1F0)
fffff880`041e3000 fffff880`041f0000 fdc fdc.sys Mon Jul 13 20:00:54 2009 (4A5BCAB6)
fffff880`010b0000 fffff880`010c4000 fileinfo fileinfo.sys Mon Jul 13 19:34:25 2009 (4A5BC481)
fffff880`05275000 fffff880`05280000 flpydisk flpydisk.sys Mon Jul 13 20:00:54 2009 (4A5BCAB6)
fffff880`01064000 fffff880`010b0000 fltmgr fltmgr.sys Sat Nov 20 04:19:24 2010 (4CE7929C)
fffff880`013e4000 fffff880`013ee000 Fs_Rec Fs_Rec.sys Mon Jul 13 19:19:45 2009 (4A5BC111)
fffff880`0192e000 fffff880`01968000 fvevol fvevol.sys Sat Nov 20 04:24:06 2010 (4CE793B6)
fffff880`01834000 fffff880`0187e000 fwpkclnt fwpkclnt.sys Sat Nov 20 04:21:37 2010 (4CE79321)
fffff800`02c18000 fffff800`02c61000 hal hal.dll Sat Nov 20 08:00:25 2010 (4CE7C669)
fffff880`04046000 fffff880`0406a000 HDAudBus HDAudBus.sys Sat Nov 20 05:43:42 2010 (4CE7A65E)
fffff880`05335000 fffff880`05391000 HdAudio HdAudio.sys Sat Nov 20 05:44:23 2010 (4CE7A687)
fffff880`03fb3000 fffff880`03fcc000 HIDCLASS HIDCLASS.SYS Sat Nov 20 05:43:49 2010 (4CE7A665)
fffff880`051f5000 fffff880`051fd080 HIDPARSE HIDPARSE.SYS Mon Jul 13 20:06:17 2009 (4A5BCBF9)
fffff880`053d3000 fffff880`053e1000 hidusb hidusb.sys Sat Nov 20 05:43:49 2010 (4CE7A665)
fffff880`03a4d000 fffff880`03b16000 HTTP HTTP.sys Sat Nov 20 04:24:30 2010 (4CE793CE)
fffff880`01968000 fffff880`01971000 hwpolicy hwpolicy.sys Sat Nov 20 04:18:54 2010 (4CE7927E)
fffff880`03fcc000 fffff880`03fdb000 kbdclass kbdclass.sys Mon Jul 13 19:19:50 2009 (4A5BC116)
fffff880`052a2000 fffff880`052b0000 kbdhid kbdhid.sys Sat Nov 20 05:33:25 2010 (4CE7A3F5)
fffff800`00bb4000 fffff800`00bbe000 kdcom kdcom.dll Mon Jul 13 21:31:07 2009 (4A5BDFDB)
fffff880`01000000 fffff880`01043000 ks ks.sys Sat Nov 20 05:33:23 2010 (4CE7A3F3)
fffff880`013b8000 fffff880`013d3000 ksecdd ksecdd.sys Sat Nov 20 04:21:15 2010 (4CE7930B)
fffff880`01555000 fffff880`01580000 ksecpkg ksecpkg.sys Sat Nov 20 05:10:34 2010 (4CE79E9A)
fffff880`0532f000 fffff880`05334200 ksthunk ksthunk.sys Mon Jul 13 20:00:19 2009 (4A5BCA93)
fffff880`0406a000 fffff880`0407c000 L1E62x64 L1E62x64.sys Sun Mar 28 22:08:44 2010 (4BB00BAC)
fffff880`02b7e000 fffff880`02b93000 lltdio lltdio.sys Mon Jul 13 20:08:50 2009 (4A5BCC92)
fffff880`011d4000 fffff880`011f7000 luafv luafv.sys Mon Jul 13 19:26:13 2009 (4A5BC295)
fffff880`00c1b000 fffff880`00c28000 mcupdate mcupdate.dll Mon Jul 13 21:29:09 2009 (4A5BDF65)
fffff880`05200000 fffff880`0520e000 monitor monitor.sys Mon Jul 13 19:38:52 2009 (4A5BC58C)
fffff880`03fdb000 fffff880`03fea000 mouclass mouclass.sys Mon Jul 13 19:19:50 2009 (4A5BC116)
fffff880`05295000 fffff880`052a2000 mouhid mouhid.sys Mon Jul 13 20:00:20 2009 (4A5BCA94)
fffff880`00f4d000 fffff880`00f67000 mountmgr mountmgr.sys Sat Nov 20 04:19:21 2010 (4CE79299)
fffff880`03b34000 fffff880`03b4c000 mpsdrv mpsdrv.sys Mon Jul 13 20:08:25 2009 (4A5BCC79)
fffff880`03b4c000 fffff880`03b79000 mrxsmb mrxsmb.sys Sat Nov 20 04:27:41 2010 (4CE7948D)
fffff880`03b79000 fffff880`03bc6000 mrxsmb10 mrxsmb10.sys Sat Nov 20 04:26:53 2010 (4CE7945D)
fffff880`03bc6000 fffff880`03bea000 mrxsmb20 mrxsmb20.sys Sat Nov 20 04:26:47 2010 (4CE79457)
fffff880`01200000 fffff880`0120b000 Msfs Msfs.SYS Mon Jul 13 19:19:47 2009 (4A5BC113)
fffff880`00e66000 fffff880`00e70000 msisadrv msisadrv.sys Mon Jul 13 19:19:26 2009 (4A5BC0FE)
fffff880`010c4000 fffff880`01122000 msrpc msrpc.sys Sat Nov 20 04:21:56 2010 (4CE79334)
fffff880`02ca9000 fffff880`02cb4000 mssmbios mssmbios.sys Mon Jul 13 19:31:10 2009 (4A5BC3BE)
fffff880`0191c000 fffff880`0192e000 mup mup.sys Mon Jul 13 19:23:45 2009 (4A5BC201)
fffff880`01402000 fffff880`014f5000 ndis ndis.sys Sat Nov 20 04:23:30 2010 (4CE79392)
fffff880`051ba000 fffff880`051c6000 ndistapi ndistapi.sys Mon Jul 13 20:10:00 2009 (4A5BCCD8)
fffff880`089dd000 fffff880`089f0000 ndisuio ndisuio.sys Sat Nov 20 05:50:08 2010 (4CE7A7E0)
fffff880`051c6000 fffff880`051f5000 ndiswan ndiswan.sys Sat Nov 20 05:52:32 2010 (4CE7A870)
fffff880`05280000 fffff880`05295000 NDProxy NDProxy.SYS Sat Nov 20 05:52:20 2010 (4CE7A864)
fffff880`02dda000 fffff880`02de9000 netbios netbios.sys Mon Jul 13 20:09:26 2009 (4A5BCCB6)
fffff880`02d66000 fffff880`02dab000 netbt netbt.sys Sat Nov 20 04:23:18 2010 (4CE79386)
fffff880`014f5000 fffff880`01555000 NETIO NETIO.SYS Sat Nov 20 04:23:13 2010 (4CE79381)
fffff880`01194000 fffff880`011a5000 Npfs Npfs.SYS Mon Jul 13 19:19:48 2009 (4A5BC114)
fffff880`02c9d000 fffff880`02ca9000 nsiproxy nsiproxy.sys Mon Jul 13 19:21:02 2009 (4A5BC15E)
fffff800`02c61000 fffff800`0324b000 nt ntkrnlmp.exe Sat Nov 20 04:30:02 2010 (4CE7951A)
fffff880`01215000 fffff880`013b8000 Ntfs Ntfs.sys Sat Nov 20 04:20:57 2010 (4CE792F9)
fffff880`019ed000 fffff880`019f6000 Null Null.SYS Mon Jul 13 19:19:37 2009 (4A5BC109)
fffff880`0898a000 fffff880`089dd000 nwifi nwifi.sys Mon Jul 13 20:07:23 2009 (4A5BCC3B)
fffff880`02db4000 fffff880`02dda000 pacer pacer.sys Sat Nov 20 05:52:18 2010 (4CE7A862)
fffff880`00eb0000 fffff880`00ec5000 partmgr partmgr.sys Sat Nov 20 04:20:00 2010 (4CE792C0)
fffff880`00e70000 fffff880`00ea3000 pci pci.sys Sat Nov 20 04:19:11 2010 (4CE7928F)
fffff880`00f36000 fffff880`00f3d000 pciide pciide.sys Mon Jul 13 19:19:49 2009 (4A5BC115)
fffff880`00f3d000 fffff880`00f4d000 PCIIDEX PCIIDEX.SYS Mon Jul 13 19:19:48 2009 (4A5BC114)
fffff880`013d3000 fffff880`013e4000 pcw pcw.sys Mon Jul 13 19:19:27 2009 (4A5BC0FF)
fffff880`07cec000 fffff880`07d92000 peauth peauth.sys Mon Jul 13 21:01:19 2009 (4A5BD8DF)
fffff880`052d0000 fffff880`0530d000 portcls portcls.sys Mon Jul 13 20:06:27 2009 (4A5BCC03)
fffff880`00c28000 fffff880`00c3c000 PSHED PSHED.dll Mon Jul 13 21:32:23 2009 (4A5BE027)
fffff880`05196000 fffff880`051ba000 rasl2tp rasl2tp.sys Sat Nov 20 05:52:34 2010 (4CE7A872)
fffff880`03f5d000 fffff880`03f78000 raspppoe raspppoe.sys Mon Jul 13 20:10:17 2009 (4A5BCCE9)
fffff880`03f78000 fffff880`03f99000 raspptp raspptp.sys Sat Nov 20 05:52:31 2010 (4CE7A86F)
fffff880`03f99000 fffff880`03fb3000 rassstp rassstp.sys Mon Jul 13 20:10:25 2009 (4A5BCCF1)
fffff880`02c4c000 fffff880`02c9d000 rdbss rdbss.sys Sat Nov 20 04:27:51 2010 (4CE79497)
fffff880`04800000 fffff880`0480b000 rdpbus rdpbus.sys Mon Jul 13 20:17:46 2009 (4A5BCEAA)
fffff880`015e8000 fffff880`015f1000 RDPCDD RDPCDD.sys Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`015f1000 fffff880`015fa000 rdpencdd rdpencdd.sys Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`013ee000 fffff880`013f7000 rdprefmp rdprefmp.sys Mon Jul 13 20:16:35 2009 (4A5BCE63)
fffff880`018e2000 fffff880`0191c000 rdyboost rdyboost.sys Sat Nov 20 04:43:10 2010 (4CE7982E)
fffff880`02b93000 fffff880`02bab000 rspndr rspndr.sys Mon Jul 13 20:08:50 2009 (4A5BCC92)
fffff880`07d92000 fffff880`07d9d000 secdrv secdrv.SYS Wed Sep 13 09:18:38 2006 (4508052E)
fffff880`041d7000 fffff880`041e3000 serenum serenum.sys Mon Jul 13 20:00:33 2009 (4A5BCAA1)
fffff880`02c00000 fffff880`02c1d000 serial serial.sys Mon Jul 13 20:00:40 2009 (4A5BCAA8)
fffff880`018da000 fffff880`018e2000 spldr spldr.sys Mon May 11 12:56:27 2009 (4A0858BB)
fffff880`08800000 fffff880`08871000 spsys spsys.sys Mon May 11 13:20:58 2009 (4A085E7A)
fffff880`088f1000 fffff880`0898a000 srv srv.sys Sat Nov 20 04:28:05 2010 (4CE794A5)
fffff880`07c00000 fffff880`07c6b000 srv2 srv2.sys Sat Nov 20 04:27:43 2010 (4CE7948F)
fffff880`07d9d000 fffff880`07dce000 srvnet srvnet.sys Sat Nov 20 04:27:20 2010 (4CE79478)
fffff880`041fb000 fffff880`041fc480 swenum swenum.sys Mon Jul 13 20:00:18 2009 (4A5BCA92)
fffff880`01630000 fffff880`01834000 tcpip tcpip.sys Sat Nov 20 04:25:52 2010 (4CE79420)
fffff880`07dce000 fffff880`07de0000 tcpipreg tcpipreg.sys Sat Nov 20 05:51:48 2010 (4CE7A844)
fffff880`011c7000 fffff880`011d4000 TDI TDI.SYS Sat Nov 20 04:22:06 2010 (4CE7933E)
fffff880`011a5000 fffff880`011c7000 tdx tdx.sys Sat Nov 20 04:21:54 2010 (4CE79332)
fffff880`02c38000 fffff880`02c4c000 termdd termdd.sys Sat Nov 20 06:03:40 2010 (4CE7AB0C)
fffff960`00520000 fffff960`0052a000 TSDDD TSDDD.dll Mon Jul 13 20:16:34 2009 (4A5BCE62)
fffff880`03ed4000 fffff880`03efa000 tunnel tunnel.sys Sat Nov 20 05:51:50 2010 (4CE7A846)
fffff880`03e00000 fffff880`03e12000 umbus umbus.sys Sat Nov 20 05:44:37 2010 (4CE7A695)
fffff880`019b7000 fffff880`019d4000 usbccgp usbccgp.sys Sat Nov 20 05:44:03 2010 (4CE7A673)
fffff880`053e1000 fffff880`053e2f00 USBD USBD.SYS Mon Jul 13 20:06:23 2009 (4A5BCBFF)
fffff880`041be000 fffff880`041cf000 usbehci usbehci.sys Mon Jul 13 20:06:30 2009 (4A5BCC06)
fffff880`0521b000 fffff880`05275000 usbhub usbhub.sys Sat Nov 20 05:44:30 2010 (4CE7A68E)
fffff880`040ba000 fffff880`040c5000 usbohci usbohci.sys Mon Jul 13 20:06:30 2009 (4A5BCC06)
fffff880`0510f000 fffff880`05165000 USBPORT USBPORT.SYS Mon Jul 13 20:06:31 2009 (4A5BCC07)
fffff880`053e3000 fffff880`053fe000 USBSTOR USBSTOR.SYS Sat Nov 20 05:44:05 2010 (4CE7A675)
fffff880`00ea3000 fffff880`00eb0000 vdrvroot vdrvroot.sys Mon Jul 13 20:01:31 2009 (4A5BCADB)
fffff880`015a5000 fffff880`015b3000 vga vga.sys Mon Jul 13 19:38:47 2009 (4A5BC587)
fffff880`041f9000 fffff880`041fad80 vHidDev vHidDev.sys Mon Dec 21 08:49:58 2009 (4B2F7D06)
fffff880`015b3000 fffff880`015d8000 VIDEOPRT VIDEOPRT.SYS Mon Jul 13 19:38:51 2009 (4A5BC58B)
fffff880`00f67000 fffff880`00fa3000 vmbus vmbus.sys Sat Nov 20 04:57:29 2010 (4CE79B89)
fffff880`0187e000 fffff880`0188e000 vmstorfl vmstorfl.sys Sat Nov 20 04:57:30 2010 (4CE79B8A)
fffff880`00ec5000 fffff880`00eda000 volmgr volmgr.sys Sat Nov 20 04:19:28 2010 (4CE792A0)
fffff880`00eda000 fffff880`00f36000 volmgrx volmgrx.sys Sat Nov 20 04:20:43 2010 (4CE792EB)
fffff880`0188e000 fffff880`018da000 volsnap volsnap.sys Sat Nov 20 04:20:08 2010 (4CE792C8)
fffff880`02c1d000 fffff880`02c38000 wanarp wanarp.sys Sat Nov 20 05:52:36 2010 (4CE7A874)
fffff880`015d8000 fffff880`015e8000 watchdog watchdog.sys Mon Jul 13 19:37:35 2009 (4A5BC53F)
fffff880`00d5a000 fffff880`00dfe000 Wdf01000 Wdf01000.sys Mon Jul 13 19:22:07 2009 (4A5BC19F)
fffff880`00c00000 fffff880`00c0f000 WDFLDR WDFLDR.SYS Mon Jul 13 19:19:54 2009 (4A5BC11A)
fffff880`02dab000 fffff880`02db4000 wfplwf wfplwf.sys Mon Jul 13 20:09:26 2009 (4A5BCCB6)
fffff960`00040000 fffff960`00351000 win32k win32k.sys Wed Jan 05 01:55:38 2011 (4D2415EA)
fffff880`00fa3000 fffff880`00fb7000 winhv winhv.sys Sat Nov 20 04:20:02 2010 (4CE792C2)
fffff880`041f0000 fffff880`041f9000 wmiacpi wmiacpi.sys Mon Jul 13 19:31:02 2009 (4A5BC3B6)
fffff880`00e5d000 fffff880`00e66000 WMILIB WMILIB.SYS Mon Jul 13 19:19:51 2009 (4A5BC117)
fffff880`02b30000 fffff880`02b51000 WudfPf WudfPf.sys Sat Nov 20 05:42:44 2010 (4CE7A624)
fffff880`0887c000 fffff880`088ad000 WUDFRd WUDFRd.sys Sat Nov 20 05:43:32 2010 (4CE7A654)
Unloaded modules:
fffff880`019b7000 fffff880`019c5000 crashdmp.sys
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 0000E000
fffff880`019c5000 fffff880`019d1000 dump_ataport
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 0000C000
fffff880`019d1000 fffff880`019da000 dump_atapi.s
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00009000
fffff880`019da000 fffff880`019ed000 dump_dumpfve
Timestamp: unavailable (00000000)
Checksum: 00000000
ImageSize: 00013000cybercore
New Member
- Joined
- Jul 7, 2009
Update machine is stable w/ only 2 sticks of ram in bslots only add a 3rd stick and bsod. ADATA GSeries DDR3 1600G CL99924 1.55v~1.75
That's why we always ask for this:
- CPU-Z m e m o r y tab snip
- Rammon h t m l report
http://windows7forums.com/blue-scre...mportant-every-thread-starter-please-see.html
To be sure memory is set right and that the sticks are matched.
Gaming Series, Gaming Series, XPG, Welcome to ADATA ?Love?Life?Dreams DDR3-1600G CL99924 2GB
Attachments
Similar threads
- Replies
- 6
- Views
- 1K
- Replies
- 3
- Views
- 2K
- Replies
- 2
- Views
- 3K