SecQube’s official U.S. launch on February 23, 2026 marks a deliberate push by the Microsoft-aligned security vendor to convert rising demand for cloud-native, AI-assisted security operations into a partner-driven, marketplace-ready business in North America.
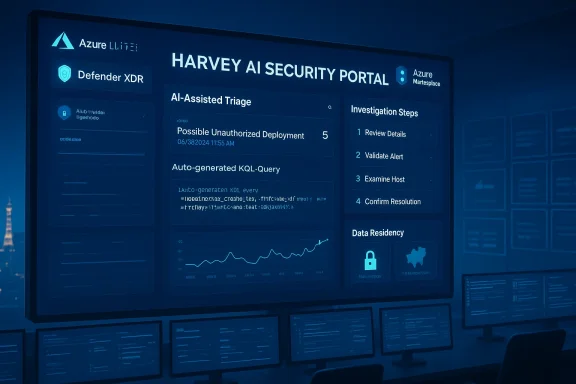
SecQube began life as a Microsoft Sentinel-centric platform vendor focused on automating routine Security Operations Center (SOC) work. The company’s core product suite centers on the Harvey® Security Portal, a cloud-native, serverless application designed to run inside a customer’s Azure tenancy and to accelerate alert triage, investigation, and remediation for Sentinel- and Defender-based telemetry. The vendor positions Harvey as an AI assistant that generates Kusto Query Language (KQL), automates L1/L2 workflows, and delivers multi-tenant “SOC-in-a-box” capabilities to managed security service providers (MSSPs) and enterprises alike.
The announcement on February 23, 2026 formalizes SecQube’s U.S. presence with a Las Vegas corporate address and claims of availability through the Microsoft Azure Marketplace, supported by a U.S.-based commercial team. That launch follows earlier deployments and product positioning in the UK, EU, UAE, Australia and a specific instance tailored for NHS operations in the United Kingdom.
But this tight coupling also creates dependencies:
Key technical assertions to validate in a proof-of-concept (POC):
Recommended verification steps during procurement:
Source: ChartMill https://www.chartmill.com/news/MSFT...nt-with-official-launch-in-the-united-states/
 Background
Background
SecQube began life as a Microsoft Sentinel-centric platform vendor focused on automating routine Security Operations Center (SOC) work. The company’s core product suite centers on the Harvey® Security Portal, a cloud-native, serverless application designed to run inside a customer’s Azure tenancy and to accelerate alert triage, investigation, and remediation for Sentinel- and Defender-based telemetry. The vendor positions Harvey as an AI assistant that generates Kusto Query Language (KQL), automates L1/L2 workflows, and delivers multi-tenant “SOC-in-a-box” capabilities to managed security service providers (MSSPs) and enterprises alike.The announcement on February 23, 2026 formalizes SecQube’s U.S. presence with a Las Vegas corporate address and claims of availability through the Microsoft Azure Marketplace, supported by a U.S.-based commercial team. That launch follows earlier deployments and product positioning in the UK, EU, UAE, Australia and a specific instance tailored for NHS operations in the United Kingdom.
What SecQube says it delivers
The Harvey Security Portal — product highlights
- AI-assistant "Harvey®": Branded as an in-tenant AI engine that performs automated triage, translates natural language into KQL, and surfaces investigation steps to analysts.
- Microsoft-native integration: Native Azure deployment architecture, Azure Lighthouse connectivity to Microsoft Sentinel, and stated alignment with Microsoft Defender XDR.
- Rapid, serverless deployment: Marketed as deployable in minutes with a self-service try-before-you-buy model and modular, multi-tenant capabilities.
- Partner and MSSP focus: White-labeling, multi-tenancy, and partner portal features aimed at scaling MSSPs and service providers.
- Compliance and data residency: Claims to keep security data in the customer’s Azure tenant and to be compatible with compliance controls such as HIPAA, GDPR and SOC 2.
- Operational economics: Promises to automate a significant share of routine SOC work (vendor materials claim up to 70–90%), reducing analyst headcount pressure and lowering mean time to triage.
Commercial and go-to-market notes
SecQube is marketing:- Availability via the Azure Marketplace (with listings for region-specific offerings such as a UK NHS-only instance and a U.S. instance),
- A partner/reseller program for geographic coverage and managed services,
- A pricing approach that mixes per-analyst and per-end-user subscription metrics and a flat-rate tier for smaller deployments.
Why the U.S. launch matters
The United States is the largest single market for security software by spend, and it remains the broadest adopter base for Microsoft Sentinel and Defender. SecQube’s U.S. entry is therefore strategically sensible for several reasons:- Marketplace reach: Azure Marketplace placement lowers friction for procurement teams already standardized on Azure and Microsoft licensing, streamlining evaluation and procurement.
- MSSP opportunity: Many North American MSSPs seek scalable multi-tenant tooling that reduces per-customer marginal costs; SecQube’s white-label positioning targets that need directly.
- Talent arbitrage pressure: The well-publicized cybersecurity staffing shortage in the U.S. makes automation claims commercially attractive to enterprises struggling to staff 24/7 SOCs.
- Public sector demand: Federal, state, and local agencies — plus regulated industries such as healthcare and finance — require tools with clear compliance posture and data residency guarantees.
Technical analysis: architecture, integrations, and the role of AI
Azure-native, in-tenant model
SecQube’s architecture emphasizes an in-tenant deployment model: the portal runs serverless in the customer’s Azure environment, with the vendor’s automation logic operating against data that remains inside the customer’s subscription. That approach has clear advantages:- It reduces the legal and compliance concerns that accompany sending raw security telemetry outside a tenant.
- It eases corporate procurement objections tied to data sovereignty and cross-border transfer.
- It can align with enterprise policies that require security logs and forensic artifacts to remain on-premises or in region-specific cloud instances.
Microsoft Sentinel and Defender XDR alignment
The vendor’s decision to build for Microsoft Sentinel and to advertise Defender XDR compatibility positions it as a focused complement to Microsoft’s security stack rather than as a replacement SIEM. For Sentinel customers this can be attractive: SecQube promises faster time-to-value by layering automation, AI-assisted investigation, and built-in playbooks on top of events and alerts Sentinel already ingests.But this tight coupling also creates dependencies:
- Customers that do not use Sentinel or that rely on a heterogeneous SIEM/XDR portfolio may see less direct value.
- Changes in Microsoft APIs, licensing, or native Sentinel capabilities could affect SecQube’s integration roadmap more than a platform-agnostic vendor.
The "Harvey" AI assistant — capabilities and questions
SecQube markets a branded assistant — Harvey® — that performs conversational triage, no-code KQL generation, and automated incident workflows. These features, if executed well, can materially accelerate investigations and lower the entry bar for staff who lack deep KQL knowledge.Key technical assertions to validate in a proof-of-concept (POC):
- Accuracy of automated triage — How often does the AI correctly prioritize true incidents versus false positives?
- KQL generation fidelity — Are generated queries efficient and safe (i.e., do they avoid heavy, tenant-wide queries that could spike costs)?
- Explainability and auditability — Can analysts review the steps the AI took, and is there a clear audit trail for regulatory or incident response needs?
Commercial credibility and verifiable claims
SecQube’s public messaging includes several high-impact claims — e.g., rapid deployment in minutes, automation of 70–90% of routine monitoring, and a dedicated NHS instance. These are meaningful selling points, but organizations evaluating SecQube should ask for evidence.Recommended verification steps during procurement:
- Reference checks: Speak with existing customers (especially those with similar scale or regulatory posture) to validate deployment timelines and automation percentages.
- Technical POC: Run a scoped POC against a production or representative Sentinel dataset to measure false positive reduction, analyst time saved, and query performance under real load.
- Compliance review: Verify certificates and third-party attestations (SOC 2 reports, HIPAA compliance statements, cyber essentials) and request region-specific deployment proofs for healthcare or public sector instances.
- Model governance: Request model cards and information on how the AI is trained, updated, and validated, plus whether any third-party LLMs are used under the hood.
Competition and market context
SecQube enters a crowded field. U.S. buyers will compare it to several alternatives:- Native Microsoft investments: Microsoft is continuously enhancing Sentinel with automation playbooks, built-in analytics, and Copilot-like assistant features that reduce friction for customers who prefer first-party tooling.
- Large SIEM/XDR incumbents: Established vendors with broad telemetry ingestion and large detection engineering teams (XDR platforms, managed detection providers) will remain options for enterprises seeking single-vendor simplicity or deeper cross-product correlation.
- Startups and specialist automation players: Numerous startups are building AI-first triage and investigation assistants; SecQube will need to differentiate on integration depth with Sentinel, partner enablement, and operational maturity.
Risk analysis: technical, legal, and operational
Technical risks
- Model drift and correctness: AI assistants must be continuously validated to avoid degrading performance as telemetry patterns and attacker techniques evolve.
- Query performance and cost: Auto-generated KQL can be powerful but may inadvertently execute expensive queries that increase Azure consumption costs.
- Dependence on Microsoft platform stability: Deep integration with Sentinel and Defender exposes SecQube to API or compatibility changes that could require fast remediation.
Legal and compliance risks
- Data residency claims: In-tenant deployment mitigates many residency concerns, but customers should confirm where metadata, tickets, and ancillary logs are stored and whether any support processes leak PII or other sensitive data.
- Intellectual property / branding: The use of the Harvey® name by multiple companies in adjacent AI domains could create trademark friction. Buyers in regulated sectors prefer clear provenance for model and data handling.
- Regulatory auditability: Automated decisions in security workflows may need to be explainable for auditors; the platform must retain full audit trails and human-in-the-loop override capabilities.
Operational risks
- Over-automation: Automating too much without proper governance risks closing alerts prematurely or missing nuanced incidents that require human judgment.
- Staffing and change management: Tools that alter workflows require careful onboarding; MSSPs must account for change-management costs when migrating analysts to a new portal and process model.
- Vendor lock-in via platform-specific features: Heavy customization or use of proprietary enrichment features could make switching vendors difficult later.
Practical buying checklist — what to demand in a POC
- Define success metrics: False positive rate reduction, time-to-triage improvement, and cost per incident before and after deployment.
- Run a blind POC: Use historical incidents and a stretch of live telemetry to test triage decisions without tipping off the AI (measure precision and recall).
- Validate KQL and performance: Inspect generated queries, run performance tests, and verify that queries do not exceed cost budgets.
- Examine model governance: Ask for documentation about model training data, update cadence, and safeguards against hallucination or unsafe actions.
- Audit support and escalation paths: Confirm how SecQube handles escalations, what level of support (24/7 vs. business hours) is included, and SLAs for incidents caused by automation missteps.
- Verify compliance and attestation: Obtain SOC 2 Type II or equivalent reports, and request the platform’s boundary diagrams showing what remains in-tenant.
- Check Marketplace billing mechanics: Understand how Azure Marketplace billing interacts with your procurement (pay-as-you-go, commitment, reseller margins).
Partner strategy and MSSP implications
SecQube is explicit about partnering with MSSPs and resellers, offering reseller-friendly billing and multi-tenant controls. For channel partners, the platform promises:- Faster onboarding of new clients,
- Branded/white-labeled portals to preserve customer relationships,
- The potential to monetize automation and reduce the variability of labor-based services.
- The lift for initial integration into existing managed services stacks,
- How security incidents are handled when multiple tenants and customers are involved,
- Revenue share and margin math when the solution is purchased via Marketplace vs. direct portal billing.
Strengths and opportunities
- Azure-native, in-tenant model addresses a real compliance and trust requirement for many customers.
- Microsoft alignment reduces integration friction for the growing number of Sentinel adopters.
- Partner-first design (multi-tenancy, white-labeling) appeals to MSSPs and channel resellers looking to scale SOC services.
- Rapid deployment narrative and Marketplace availability lower procurement and evaluation barriers.
Weaknesses and areas to watch
- Claims need independent validation — automation percentages and ROI figures should be verified through customer references and a rigorous POC.
- Branding ambiguity around "Harvey" could confuse buyers and raise questions about model provenance and vendor distinctness.
- Heavy dependence on Microsoft’s roadmap could compress differentiation over time if Microsoft continues to add similar automation and Copilot capabilities inside Sentinel.
Conclusion — who should evaluate SecQube now
SecQube’s U.S. launch positions it as a pragmatic contender for organizations that are already invested in the Microsoft security stack and are actively seeking automation to relieve SOC staff shortages. The value proposition is strongest for:- MSSPs seeking multi-tenant, white-label portals to scale managed detections and response,
- Enterprises that want a Sentinel-first augmentation rather than a rip-and-replace of their telemetry stack,
- Regulated organizations that require in-region data residency and serverless, tenant-resident tooling.
Source: ChartMill https://www.chartmill.com/news/MSFT...nt-with-official-launch-in-the-united-states/