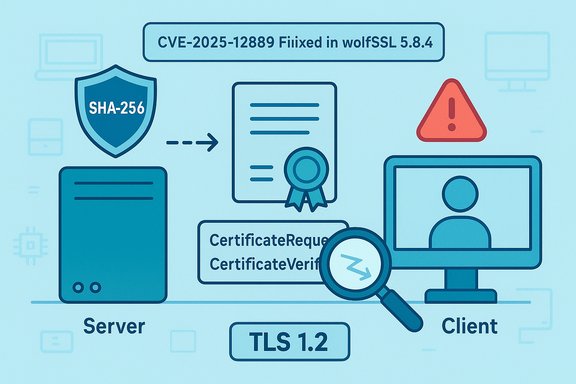
A newly recorded flaw in TLS 1.2 implementations lets a client deliberately choose a weaker message digest than the server requested during client-certificate authentication — a subtle but real violation of the TLS 1.2 handshake rules that has been cataloged as CVE-2025-12889 and fixed in the wolfSSL 5.8.4 release.
TLS handshakes are a negotiation of mutually acceptable algorithms: cipher suites, key-exchange methods, and — crucial for client certificates — the hash+signature algorithm pairs that servers advertise in CertificateRequest messages. RFC 5246 (TLS 1.2) is explicit: the hash and signature algorithms used in CertificateVerify must be one of the pairs present in the server’s supported_signature_algorithms field. Implementations that fail to enforce that rule open a narrow window where a client (or a malicious middlebox impersonating a client) can sign with a weaker digest than the server allowed. The RFC language and requirement are documented in the TLS 1.2 specification. CVE-2025-12889 describes exactly this class of bug: during TLS 1.2 CertificateVerify processing, an implementation accepted a signature that used a digest algorithm not constrained by the server’s CertificateRequest — effectively allowing a client to “downgrade” the digest. The issue was reported to wolfSSL and tracked into their codebase; the maintainers merged a corrective patch in November 2025 and shipped the fix in wolfSSL 5.8.4. wolfSSL’s advisory and release notes explicitly list CVE-2025-12889 and reference the merged pull request that corrects CertificateVerify parsing/validation.
The client responds with its certificate and a CertificateVerify message which contains a signature over transcript data. The signature carries a pair that indicates the hash algorithm used (for TLS 1.2 this is encoded explicitly). The receiver (server) must validate that the pair used in CertificateVerify is present in the CertificateRequest list and that the chosen algorithm is compatible with the client’s key type per RFC 5246. Failure to make that check is a protocol violation.
For Windows administrators, the immediate question is: do any Windows-facing services or client applications in the environment embed wolfSSL or an affected TLS stack? If yes, they must prioritize update; if not, the direct Windows-side exposure is likely low, but downstream supply-chain risks (e.g., third-party VPN concentrators, network appliances, or unmanaged IoT) still exist. wolfSSL lists the fix in 5.8.4 and documents CVE-2025-12889 in its security page.
CVE-2025-12889 is a smaller but conceptually related mis-step: it’s not version downgrade, but digest selection downgrade — and the fix is the same idea: enforce the protocol contract strictly. Past incidents also show that vendor ecosystems that ship many embedded products are the ones most likely to carry exploitable build variants for longer; the Windows world has seen analogous supply-chain and update problems in the past.
The vulnerability is not currently reported as widely exploited in the wild, and public scoring places it at low severity; nevertheless, because the attack model involves downgrading cryptographic strength, organizations that rely on client-certificate TLS for high-value operations should remediate without delay. Where vendor patches are not immediately available for appliances, apply the compensating controls listed above and push for firmware updates from your vendors.
This advisory synthesizes the technical record visible in the public repositories and vendor advisories: RFC 5246’s signature-algorithm requirement, the wolfSSL pull request and release that address the defect, and public indexing of the CVE. The recommended path is clear: patch the TLS library or device firmware now, verify server-side signature-algorithm checks, and harden negotiation policies moving forward.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
TLS handshakes are a negotiation of mutually acceptable algorithms: cipher suites, key-exchange methods, and — crucial for client certificates — the hash+signature algorithm pairs that servers advertise in CertificateRequest messages. RFC 5246 (TLS 1.2) is explicit: the hash and signature algorithms used in CertificateVerify must be one of the pairs present in the server’s supported_signature_algorithms field. Implementations that fail to enforce that rule open a narrow window where a client (or a malicious middlebox impersonating a client) can sign with a weaker digest than the server allowed. The RFC language and requirement are documented in the TLS 1.2 specification. CVE-2025-12889 describes exactly this class of bug: during TLS 1.2 CertificateVerify processing, an implementation accepted a signature that used a digest algorithm not constrained by the server’s CertificateRequest — effectively allowing a client to “downgrade” the digest. The issue was reported to wolfSSL and tracked into their codebase; the maintainers merged a corrective patch in November 2025 and shipped the fix in wolfSSL 5.8.4. wolfSSL’s advisory and release notes explicitly list CVE-2025-12889 and reference the merged pull request that corrects CertificateVerify parsing/validation. What the vulnerability actually is — technical primer
The TLS 1.2 CertificateRequest / CertificateVerify sequence
When a TLS server asks a client for a certificate, it can (and should) send a CertificateRequest that includes a restricted list of acceptable signature+hash pairs (the supported_signature_algorithms extension). That is a server-controlled policy to prevent the client from using weak hashes (for example, SHA-1) or legacy signature schemes.The client responds with its certificate and a CertificateVerify message which contains a signature over transcript data. The signature carries a pair that indicates the hash algorithm used (for TLS 1.2 this is encoded explicitly). The receiver (server) must validate that the pair used in CertificateVerify is present in the CertificateRequest list and that the chosen algorithm is compatible with the client’s key type per RFC 5246. Failure to make that check is a protocol violation.
How the implementation bug manifests
CVE-2025-12889 arises when the client-side implementation (or code-paths that parse/accept a CertificateVerify) does not check that the signature’s hash algorithm matches one of the algorithms advertised in the server’s CertificateRequest. Concretely, a client — or a malicious actor able to influence the client’s TLS library — can produce a CertificateVerify that uses a weaker digest (e.g., a SHA-1 variant) despite the server advertising only SHA-256/384/512. If the server accepts that CertificateVerify, the server’s assurance about the signature strength is undermined. wolfSSL’s maintainer notes and the pull request show the fix: stop parsing and accepting CertificateVerify signatures when the signature/hash pair is incompatible with the peer key or absent from the supported list.Practical impact and risk model
Severity and current score
Multiple aggregators and the vendor assessment mark CVE-2025-12889 as a low-severity issue (CVSS v4 base score reported around 2.3). The root cause is protocol validation rather than a remote code execution fault, and the immediate exploitation requires conditions where a weaker digest would materially worsen security. NVD and other indexers list the entry as undergoing enrichment; wolfSSL credits the report to a researcher at POSTECH and has incorporated the fix in 5.8.4. Low CVSS does not mean “no concern.” The practical risk depends on the ecosystem and whether an attacker can exploit the weaker digest to mount further attacks:- If the weaker digest is cryptographically broken (e.g., SHA‑1 in contexts where collision attacks are practical) and the attacker can either coerce the client or manipulate the client’s environment, they can weaken the authenticity guarantees of the handshake.
- Where TLS client certificates protect high-value operations (automated mutual-TLS for network appliances, device provisioning, VPN authentication), signature downgrades could create realistic attack paths if combined with other weaknesses.
- Many deployments are unaffected because servers and clients already enforce modern policies (disallowing SHA‑1, requiring TLS 1.3, or delegating TLS to hardened stacks).
Where this matters most: embedded and third‑party stacks
wolfSSL is widely used in embedded systems, IoT devices, VPN clients, TLS-enabled middleware, and a variety of non-Windows and cross-platform products. A bad TLS client implementation in an embedded device can be exploited by an attacker with network position (MITM capability) or local access to the client to cause the service to accept a weaker signature than the server intended.For Windows administrators, the immediate question is: do any Windows-facing services or client applications in the environment embed wolfSSL or an affected TLS stack? If yes, they must prioritize update; if not, the direct Windows-side exposure is likely low, but downstream supply-chain risks (e.g., third-party VPN concentrators, network appliances, or unmanaged IoT) still exist. wolfSSL lists the fix in 5.8.4 and documents CVE-2025-12889 in its security page.
Historic context: why “downgrade” bugs matter
Downgrade attacks and negotiation flaws have a long history in TLS/SSL. POODLE, TLS version fallback attacks, and other interoperability-preserving behaviors have been abused to force weaker protocols or ciphers. The industry learned the hard way that backwards compatibility without strict guardrails frequently produces attack paths. Historical notes and community threads covering earlier downgrade problems (for example, POODLE and FalseStart protocol negotiations) make the pattern clear: negotiation semantics must be strict, and both sides must verify the other follows the constraints.CVE-2025-12889 is a smaller but conceptually related mis-step: it’s not version downgrade, but digest selection downgrade — and the fix is the same idea: enforce the protocol contract strictly. Past incidents also show that vendor ecosystems that ship many embedded products are the ones most likely to carry exploitable build variants for longer; the Windows world has seen analogous supply-chain and update problems in the past.
Vendor response — wolfSSL and the public record
- wolfSSL accepted a report (credited to a researcher at POSTECH) and merged a PR that tightens CertificateVerify parsing for TLS 1.2. The PR explicitly checks signature algorithm compatibility with the key and rejects mismatches. The PR was merged in early November 2025.
- wolfSSL released version 5.8.4 on November 20, 2025, and its release notes and security page list CVE-2025-12889 as fixed in that release. The security page and release notes group this CVE with a set of low/medium TLS fixes included in the 5.8.4 bundle. Administrators and vendors using wolfSSL should upgrade to 5.8.4 or later.
- Public vulnerability aggregates (NVD, cvedetails, cvefeed) have indexed the CVE and recorded low severity, CWE-20 (improper input validation), and the wolfSSL PR reference. NVD recorded the entry and marks it as undergoing analysis; aggregator pages show the published date in late November 2025.
- Microsoft’s Security Update Guide hosts a CVE entry page for CVE-2025-12889; that page is present in the MSRC database though JavaScript might be needed to render its full content via browsers. Regardless, public vulnerability feeds list the Microsoft entry for tracking. Administrators relying on MSRC should consult the MSRC vulnerability pages for any later mapping to Windows components (none are directly mapped as of initial publication).
Detection, mitigation and remediation guidance
Immediate remediation steps (for IT teams & Windows admins)
- Inventory affected software and devices.
- Search your environment for components and appliances that ship with wolfSSL or other TLS libraries that might have been updated in the 5.8.x timeframe. Prioritize VPN clients, embedded management appliances, IoT gateways, and vendor-supplied TLS clients.
- Patch wolfSSL-based components.
- Upgrade any directly-managed wolfSSL libraries to wolfSSL 5.8.4 or later; request patched firmware from vendors for appliances and embedded devices that embed wolfSSL. wolfSSL’s release explicitly lists the fix.
- Harden server-side validation where possible.
- Servers that request client authentication should strictly validate that the CertificateVerify signature algorithm is one of the algorithms they advertised in CertificateRequest, and abort the handshake if not. This is RFC-mandated behavior; if your TLS termination point is under your control (load balancer, reverse proxy, Windows-based TLS termination), ensure your TLS stack enforces the rule.
- Prefer TLS 1.3 and modern cipher suites.
- Where you can control both sides, migrate away from TLS 1.2 client-certificate paths toward TLS 1.3 — TLS 1.3 changes negotiation semantics and reduces a class of algorithm-negotiation pitfalls (though TLS 1.3 does its own careful checks and has different extension names). Note: migration may not be immediately practical for all devices or services.
- Network-level compensations.
- Use TLS-capable enterprise proxies or TLS inspection appliances to enforce signature algorithm policies for outbound client connections if you cannot patch devices immediately. This adds complexity and privacy concerns, so treat it as a temporary compensating control.
Hunting and detection ideas
- Search TLS logs and packet captures for CertificateVerify messages that carry deprecated signature/hash pairs (e.g., sha1WithRSAEncryption, DSA-based pairs, or other legacy encodings).
- On systems and appliances, detect wolfSSL version strings in banners, binaries, or firmware images using file scans and software composition analysis (SCA) tools.
- Monitor vendor advisories for firmware updates and apply them quickly to appliances that cannot be updated by replacing a shared library.
- Use network baselining to spot unusual TLS negotiation patterns (clients repeatedly negotiating deprecated signature algorithms) and correlate with endpoint inventory.
Why servers should still check the signature algorithm
Even though the bug is in the client-side acceptance/selection of digest, servers are the logical gatekeeper: if servers enforce the supported_signature_algorithms constraint by rejecting CertificateVerify values that do not match their CertificateRequest, the attack is blocked. The TLS spec expects both endpoints to follow the protocol — servers that are lax or rely solely on TLS stack defaults may be more exposed. RFC 5246 is clear on the server’s expectation.Who should care (prioritization)
- High priority: Vendors and integrators who embed wolfSSL into appliances, routers, VPN endpoints, or industrial devices — these products must be patched and firmware updates pushed to customers.
- Medium priority: Enterprises that use third-party appliances (especially TLS-terminating devices) where the vendor has not published a patch — follow vendor advisories and plan compensating controls.
- Lower but non‑zero priority: Desktop Windows environments that rely on mainstream stacks (Schannel, OpenSSL via well-patched clients) and where wolfSSL is not in use. The immediate risk to native Windows TLS stacks is minimal unless a third-party component in the environment uses wolfSSL. wolfSSL’s own security page and the 5.8.4 release are the authoritative fix paths.
Strengths of the response and remaining risks
What’s good about the situation now
- The bug was responsibly reported and fixed quickly by wolfSSL; the PR and release timeline show a prompt vendor response. This reduces the window for broad exploitation.
- The vulnerability is classified as low-severity in public scoring and is a protocol-enforcement defect rather than a memory corruption or RCE bug, limiting its direct catastrophic impact in many environments.
- There is clear remediation: upgrade wolfSSL to 5.8.4 or obtain patched firmware from vendors.
What still worries defenders
- The exposure surface is not limited to servers or laptops; embedded devices, IoT, and industrial products often lag in patch cadence and can remain vulnerable on networks for months or years.
- This bug is an example of subtle protocol mis-implementation that escapes aggressive fuzzing if test suites do not validate the supported_signature_algorithms cross-check; it suggests the need for better test harnesses around negotiation semantics.
- Public scoring downplays the exploitability in the short term, but a low-severity protocol bug can become an escalator when combined with other weaknesses (legacy cert chains, poor key management, or devices that accept weak hashes). Defenders must treat it as a supply-chain/patch-management problem in affected ecosystems.
Recommended action checklist (concise)
- Identify all products and devices that embed wolfSSL or ship with wolfSSL-based firmware.
- Apply wolfSSL 5.8.4 (or later) to your codebases and request patched firmware from vendors for appliances and IoT devices.
- Ensure your TLS terminators (proxies, load balancers) validate that CertificateVerify uses the same signature/hash pair advertised in CertificateRequest.
- Raise detection rules to spot CertificateVerify messages with deprecated or unexpected digest algorithms.
- Where practical, accelerate migration to TLS 1.3 for mutual-authentication flows, but do so with a tested rollout plan.
Final analysis and caution
CVE-2025-12889 is a textbook example of a small protocol-validation bug with outsized design implications: the TLS handshake rules exist to prevent precisely this sort of weakening of authentication guarantees, and the fix is to enforce the protocol strictly. The immediate remediation is straightforward for library consumers — upgrade to wolfSSL 5.8.4 — but the long-term lesson is broader: supply-chain inventory and vendor-pushed firmware remain the weakest link for many enterprises. Administrators should treat this CVE as an urgent reminder to catalog embedded TLS endpoints and enforce strict negotiation policies at TLS termination points.The vulnerability is not currently reported as widely exploited in the wild, and public scoring places it at low severity; nevertheless, because the attack model involves downgrading cryptographic strength, organizations that rely on client-certificate TLS for high-value operations should remediate without delay. Where vendor patches are not immediately available for appliances, apply the compensating controls listed above and push for firmware updates from your vendors.
This advisory synthesizes the technical record visible in the public repositories and vendor advisories: RFC 5246’s signature-algorithm requirement, the wolfSSL pull request and release that address the defect, and public indexing of the CVE. The recommended path is clear: patch the TLS library or device firmware now, verify server-side signature-algorithm checks, and harden negotiation policies moving forward.
Source: MSRC Security Update Guide - Microsoft Security Response Center