Microsoft’s brief FAQ line — “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate as a product‑level inventory statement, but it is not a technical guarantee that no other Microsoft product can include the same vulnerable code; the true blast radius for CVE‑2024‑43897 is determined by kernel version, build configuration, and whether the vulnerable virtio handling code was compiled into any given Microsoft‑distributed kernel image. ps://www.microsoft.com/en-us/msrc/blog/2025/10/toward-greater-transparency-machine-readable-vulnerability-exploitability-xchange-for-azure-linux)
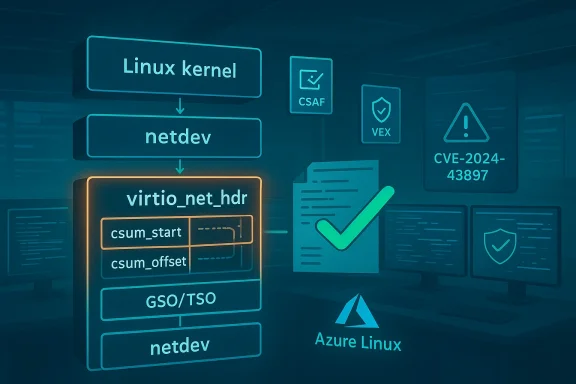
CVE‑2024‑43897 is a medium‑severity Linux kernel networking bug that was disclosed in August 2024. The defect lives in the virtio network header handling path: when Generic Segmentation Offload (GSO) packets are processed, the kernel did not validate certain checksum metadata fields tightly enough — specifically the csum_start and csum_offset values inside the virtio_net_hdr — which could allow malformed offload metadata to produce kernel warnings and instability during segmentation and checksum processing. Upstream maintainers tightened those checks and published targeted fixes to drop or reject packets with invalid checksum offsets. (cvefeed.io)
This article explains the technical problem and its fixes, decodes Microsoft’s wording about Azure Linux and product scope, and gives security teams a practical, prioritized checklist to discover, triage, and remediate risk across Microsoft‑supplied artifacts. Where a statement cannot be verified from public records we will flag that uncertainty and recommend concrete verification steps.
The issue was identified by automated kernel fuzzing (Syzkaller) which surfaced WARN_ON conditions when checksum offsets exceeded skb_headlen for GSO packets. The upstream fixes therefore focused on strengthening input validation for csum_start/csum_offset for GSO packets and on deriving the correct offset from segmentation parsing where feasible — avoiding introducing a new parser but reusing existing segmentation logic and the SKB_GSO_DODGY mechanism to flag and drop dodgy packets. (cvefeed.io)
Important clarifications:
Longer answer: Microsoft has publicly attested Azure Linux as including the upstream kernel code mapped to CVE‑2024‑43897; that is authoritative for customers who run Azure Linux images and kernels. However, other Microsoft‑distributed artifacts could carry the same vulnerable code depending on build-time choices. Examples of artifacts you should treat as unknown until verified include:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑43897 is a medium‑severity Linux kernel networking bug that was disclosed in August 2024. The defect lives in the virtio network header handling path: when Generic Segmentation Offload (GSO) packets are processed, the kernel did not validate certain checksum metadata fields tightly enough — specifically the csum_start and csum_offset values inside the virtio_net_hdr — which could allow malformed offload metadata to produce kernel warnings and instability during segmentation and checksum processing. Upstream maintainers tightened those checks and published targeted fixes to drop or reject packets with invalid checksum offsets. (cvefeed.io)This article explains the technical problem and its fixes, decodes Microsoft’s wording about Azure Linux and product scope, and gives security teams a practical, prioritized checklist to discover, triage, and remediate risk across Microsoft‑supplied artifacts. Where a statement cannot be verified from public records we will flag that uncertainty and recommend concrete verification steps.
What the bug actually is (technical summary)
The defect in plain English
At packet receive time, virtual NICs (virtio) hand metadata to the kernel through a small header structure known as struct virtio_net_hdr. That header can carry information used for offloading work — for example, telling the kernel where the transport checksum begins (csum_start) and where the checksum is located (csum_offset). For non‑segmented packets those offsets can be validated easily relative to the skb linear buffer. But when a packet uses GSO (Generic Segmentation Offload) — for example, TSO (TCP segmentation offload) — the packet will be segmented by the stack, and naive checks against the original skb head length are insufficient: offsets that were valid for the original aggregated skb can be invalid (out of range) after segmentation. The specific code path (virtio_net_hdr_to_skb and the later skb_checksum_help / segmentation logic) could therefore encounter an invalid offset and trigger kernel warnings or instability. (cvefeed.io)The issue was identified by automated kernel fuzzing (Syzkaller) which surfaced WARN_ON conditions when checksum offsets exceeded skb_headlen for GSO packets. The upstream fixes therefore focused on strengthening input validation for csum_start/csum_offset for GSO packets and on deriving the correct offset from segmentation parsing where feasible — avoiding introducing a new parser but reusing existing segmentation logic and the SKB_GSO_DODGY mechanism to flag and drop dodgy packets. (cvefeed.io)
Why this is not an immediate remote RCE
Two important mitigations reduce exploitability in practice:- The defect is a validation/robustness problem in the kernel’s networking code: it leads to warnings, potential crashes, or denial‑of‑service conditions (availability). It does not introduce a direct, generic remote code‑execution primitive on its own. Public trackers assigned a CVSS v3.1 base score in the mid‑5 range, mapping to local/adjacent attack vectors and availability impact. (cvefeed.io)
- The vulnerability requires crafting or delivering malformed offload metadata (TSO/UFO/USO style inputs) in the context of virtio or similar network front‑ends; in many cloud or hardened deployments, hypervisor and NIC offload paths are constrained or monitored. Nevertheless, any host that receives untrusted L2/L3 traffic and exposes virtual NICs that accept offload metadata should treat the issue seriously.
The upstream fix and vendor patches
Upstream Linux maintainers adopted surgical patches that:- Tighten checks on csum_start and csum_offset in virtio_net_hdr_to_skb for GSO packets.
- Reuse existing segmentation parsing logic (and SKB_GSO_DODGY) to deduce correct offsets for TSO packets rather than adding a new transport parser.
- Extend the same defensive approach already present for UDP segmentation offload (USO) to TSO. (cvefeed.io)
Microsoft’s wording: what es not say
Microsoft’s MSRC CVE pages for Linux‑component CVEs commonly include a short FAQ line that reads in effect: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” That phative product‑level inventory attestation — it says Microsoft inspected the build outputs for Azure Linux and found the implicated upstream code there. Microsoft has also explicitly committed to publishing machine‑readable CSAF and VEX attestations (a phased rollout that began with Azure Linux) and to update CVE mappings if impact to additional Microsoft productsrosoft.com]Important clarifications:
- The MSRC line is a statement of what Microsoft has checked and attested so far. It confirms Azure Linux images are a known carrier and therefore an operational priority for patching.
- It is not a technical proof that the vulnerable code cannot appear in other Microsoft artifacts. Whether any other Microsoft product includes the vulnerable virtio handling code depends on the kernel version, configuration flags used in the build, and whether local backports or patches were applied. In short: absence of public attestation ≠ proof of absence.
- Microsoft’s public VEX rollout is phased and product‑by‑product. The company has signaled that it will publish machine‑readable attestations and update the CVE mapping where additional Microsoft products are discovered to ship the component. That reduces ambiguity over time, but a gap remains while inventorying thousands of artifacts.
Is Azure Linux the only Microsoft product that could be affected?
Short answer: No — not necessarily.Longer answer: Microsoft has publicly attested Azure Linux as including the upstream kernel code mapped to CVE‑2024‑43897; that is authoritative for customers who run Azure Linux images and kernels. However, other Microsoft‑distributed artifacts could carry the same vulnerable code depending on build-time choices. Examples of artifacts you should treat as unknown until verified include:
- WSL2 kernel images that Microsoft publishes for Windows clients (those kernels are built independently and may or may not include particular drivers or upstream commit ranges).
- Microsoft‑curated VM images in the Azure Marketplace that include their own kernel packages or vendor kernels.
- Any Microsoft‑maintained container base images or platform node images that embed a Linux kernel or kernel modules (less common for container base images, but possible for images containing kernel modules or initramfs).
- Bespoke kernel builds that Microsoft uses inteatform services or appliances.
- Kernel version / commit range: the vulnerable code must be present in the upstream tree used to bresent in a backported patch that reintroduced the issue).
- Kernel configuration: the relevant code must be compiled in or provided as a module (CONFIG_* flags determine this).
- Vendor backports or local patches: a vendor may have already applied a fix or may have backported older behavior that leaves systems unaffected.
Practical guidance — how to triage and remediate across Microsoft artifacts
If you manage systems that may run Microsoft‑distributed Linux artifacts, follow this prioritized checklist.1. Prioritize Azure Linux images (immediate)
- If you run Azure Linux VMs or Azure Marketplace images explicitly labelled Azure Linux, treat them as known affected until you confirm the vendor’s patch state. Microsoft’s attestation makes these images the highest immediate priority.
2. Run artifact discovery and SBOM checks (parallel)
- Enumerate all Microsoft‑provided images and binaries in your estate: WSL2 kernels, Marketplace images, container base images published by Microsoft, Azure node images (e.g., AKS node pools), and any Microsoft agent packages.
- Harvest SBOMs where available; consume Microsoft’s CSAF/VEX feeds (they are being published and will expand over time). The Microsoft VEX initiative gives automated signals to mark artifacts as Known Affected / Not Affected / Under Investigation / Fixed.
3. Kernel/version scanning (artifact‑level)
- Script a scan that collects /proc/version, uname -a, and /boot/config-* across Linux hosts. For images you cannot boot, inspect package metadata or image manifests to determine the kernel package and version.
- Cross‑reference discovered kernel versions with the upstream commit ranges and distribution advisories for CVE‑2024‑43897 to determine whether a build predates the fix. Public trackers and distro advisories list the fixed ranges and package versions. (cvefeed.io)
4. For WSL2 and managed endpoints: check Microsoft‑distributed kernels
- WSL2 ships a Microsoft‑maintained kernel binary for Windows; verify which kernel version Microsoft published for your Windows build, and whether the published WSL kernel includes the virtio code path implicated by the CVE. If you cannot verify from MSRC/VEX data, treat the WSL kernel as “unknown” and reach out to Microsoft support or apply the fixed WSL kernel when Microsoft publishes one. This is an area where vendor attestation matters; absent attestation, internal inspection is required.
5. Patch and deploy (apply vendor updates)
- Where vendor kernel updates are available (Azure Linux, mainstream distributions), apply them and schedule reboots as required.
- If you maintain custom kernels (for appliances, specialized VMs, or in‑house builds), apply the upstream patch or backport the fix, rebuild the kernel, and redeploy. Upstream patch diffs are small and targeted to virtio_net_hdr handling. (cvefeed.io)
6. Validate after patching
- After updating, reboot into the patched kernel and run the kselftests and network stack tests (especially tests exercising GSO/TSO paths) to confirm the fix is active.
- Monitor kernel logs for the specific WARN_ON signatures seen kb_checksum_help / ip_finish_output_gso stack frames) and for abnormal network errors. (cvefeed.io)
7. Operational compensations (where patching is delayed)
- If you cannot patch immediately, consider disabling offload features on interfaces exposed to untrusted networks, where feasible (disable TSO/GSO/UFO on affected interfaces). This is a blunt tool and may have performance consequences, but it reduces attack surface in the short term.
- Use host‑based network monitoring and intrusion detection signatures to watch for unusual fragmentation/segmentation patterns that could be abusive. Document mitigations in change control so you can restore performance when patches are applied.
How to read vendor attestation language (best practices for security teams)
Microsoft’s succinct FAQ sentence is useful — it tells you that Microsoft inspected Azure Linux and found the component. But security teams must treat such sentences as:- Authoritative for the named product (act on it promptly for that product).
- Not exhaustive for the vendor’s entire portfolio (do not assume other artifacts are safe).
- A prompt to run artifact discovery and SBOM validation to reduce unknowns.
- Ingest Microsoft’s CSAF/VEX outputs as they arrive and map attestations to your CI/CD and inventory tooling.
- Mark artifacts Microsoft lists as Known Affected for fast triage and remediation.
- Treat any Microsoft artifact that is not yet attested as “unknown” and subject it to the same scanning/verification pipeline rather than assuming “not affected.”
What we verified and how
Key technical points in this article were cross‑checked against upstream kernel commit discussions and multiple independent trackers:- The technical symptom, the Syzkaller findings, and the corrective approach (tightening csum_start/csum_offset checks and using segmentation parsing for offsets) are documented in the CVE description and patch discussion. Upstream commit references and stable backport notes show the precise fixes. (cvefeed.io)
- Distribution trackers and vendor advisories confirm the issue and list fixed package versions for affected kernel series; for example, Amazon Linux advisory entries and other distro announcements record fixed kernels or backports. Those advisories were checked to validate vendor patch rollouts.
- Microsoft’s public guidance pattern and its VEX/CSAF rollout plan were validated against Microsoft’s published blog announcing machine‑readable attestations and archived MSRC CVE pages that use the same FAQ phrasing. This confirms that Microsoft’s phrase is an inventory attestation and that Microsoft has committed to expand attestations beyond Azure Linux.
Risk assessment and final recommendations
- Impact: CVE‑2024‑43897 is primarily a robustness/availability vulnerability in the Linux networking stack related to GSO/TSO checksum handling. It was scored as medium by public trackers and requires local/adjacent conditions and crafted offload metadata to trigger kernel warnings or crashes. (cvefeed.io)
- Blast radius inside Microsoft: Azure Linux is a confirmed carrier and therefore a top priority to patch for Azure customers. However, other Microsoft artifacts (WSL2 kernels, Marketplace images, specialized platform kernels) could include the vulnerable code depending on kernel version and build configuration. Treat other Microsoft artifacts as d, and run automated artifact discovery.
- For defenders: prioritize patching Azure Linux images first, run a rapid inventory for Microsoft artifacts in your estate, patch or rebuild custom kernels, and consider temporary offload mitigations for exposed interfaces while you patch. Consume Microsoft’s CSAF/VEX feeds as they publish them and map attestations into your vulnerability management pipeline.
- For transparency and automation: customers should rely on both vendor attestations (VEX/CSAF) and internal SBOM/scan evidence. Vendor attestations accelerate triage but do not remove the requirement for artifact‑level verification.
Conclusion
Microsoft’s MSRC statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is a useful and accurate product‑level inventory attestation: if you run Azure Linux images, treat them as in‑scope and apply Microsoft’s kernel updates promptly. However, that same sentence is not an exclusivity claim — other Microsoft artifacts may also carry the same vulnerable virtio handling code depending on kernel version, build configuration, and backports. Security teams must therefore combine vendor VEX attestations with their own artifact discovery, SBOM inspection, and kernel/version scans to move from “unknown” to “known good” across the estate. The upstream fix is targeted and available; the immediate operational task is to find every copy of the affected kernel code you run, update or rebuild, and validate the remediation. (cvefeed.io)Source: MSRC Security Update Guide - Microsoft Security Response Center