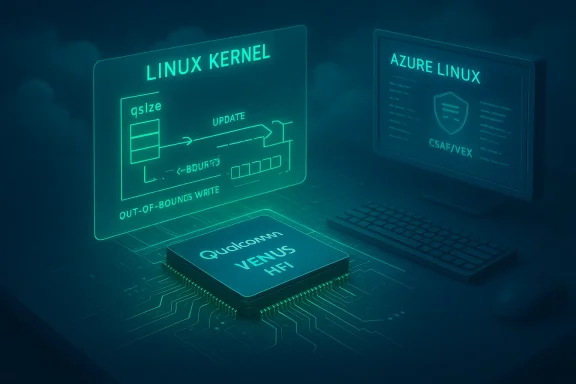
CVE-2025-23158 is a high‑impact Linux kernel defect in the Qualcomm/VENUS video driver (the venus hfi subsystem) that allows firmware‑controlled corruption of a queue size field to trigger an out‑of‑bounds write; Microsoft’s public advisory names Azure Linux as a product that “includes this open‑source library and is therefore potentially affected,” but that wording is a product‑scoped attestation — not a technical guarantee that no other Microsoft product could contain the vulnerable code.
CVE‑2025‑23158 was assigned for an out‑of‑bounds write in the Linux kernel’s media: venus: hfi code path. The bug appears when the shared queue size (qsize) — a value the device firmware can influence — is either incorrect or maliciously increased. The driver’s calculation of empty space then becomes incorrect, and because the updated write index (new_wr_idx) is not adequately bounded, a subsequent memcpy can write past the allocated queue buffer. Upstream and distribution advisories classify the defect as an OOB write (CWE‑787) and give it a high severity rating in several trackers.
This vulnerability class is dangerous: OOB writes in kernel drivers can corrupt kernel memory, cause crashes or data integrity failures, and — depending on exploitation complexity and context — may lead to local privilege escalation. The typical attack surface for venus HFI is local and relies on untrusted or buggy firmware or a privileged user that can interact with the device; exploitability is therefore strongly conditioned on the deployment scenario (embedded devices, mobile SoCs, VM passthrough, or cloud images that include vendor drivers). Multiple distributions and vendors patched the upstream kernel fixes shortly after disclosure.
Microsoft’s short FAQ answer on the MSRC product page (the phrasing quoted in the question) is consistent with Microsoft’s October 2025 rollout of machine‑readable that began with Azure Linux; in that rollout Microsoft explicitly explained that it will expand product mappings as additional inventories are completed, and that the initial attestations should be treated as authoritative for the named product only. That procedural context matters to answering whether Azure Linux is “the only Microsoft product” that includes the component.
Some vulnerability aggregators and vendor bulletins specifically show that CBL‑Mariner/Azure Linux families were tracked for related venus HFI issues in the past, and several cloud vendors and Linux distributors added fixes to their kernel packages once the upstream patch was released. That is consistent with Microsoft focusing its initial VEX inventory on Azure Linux and promising to expand mappings.
Practically, that means Azure Linux customers receive the clearest, machine‑readable guidance now; other Microsoft customers should either verify their artifacts directly (as outlined earlier) or wait for Microsoft to publish additional attestations for the products they consume — while treating the absence of an attestation as not yet validated rather than as safe.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑23158 was assigned for an out‑of‑bounds write in the Linux kernel’s media: venus: hfi code path. The bug appears when the shared queue size (qsize) — a value the device firmware can influence — is either incorrect or maliciously increased. The driver’s calculation of empty space then becomes incorrect, and because the updated write index (new_wr_idx) is not adequately bounded, a subsequent memcpy can write past the allocated queue buffer. Upstream and distribution advisories classify the defect as an OOB write (CWE‑787) and give it a high severity rating in several trackers.This vulnerability class is dangerous: OOB writes in kernel drivers can corrupt kernel memory, cause crashes or data integrity failures, and — depending on exploitation complexity and context — may lead to local privilege escalation. The typical attack surface for venus HFI is local and relies on untrusted or buggy firmware or a privileged user that can interact with the device; exploitability is therefore strongly conditioned on the deployment scenario (embedded devices, mobile SoCs, VM passthrough, or cloud images that include vendor drivers). Multiple distributions and vendors patched the upstream kernel fixes shortly after disclosure.
Microsoft’s short FAQ answer on the MSRC product page (the phrasing quoted in the question) is consistent with Microsoft’s October 2025 rollout of machine‑readable that began with Azure Linux; in that rollout Microsoft explicitly explained that it will expand product mappings as additional inventories are completed, and that the initial attestations should be treated as authoritative for the named product only. That procedural context matters to answering whether Azure Linux is “the only Microsoft product” that includes the component.
What Microsoft actually said — and what it means
Microsoft’s wording (operational reading)
Microsoft’s update guide language — paraphrased in the user’s quote — contains two disosoft has performed an inventory for Azure Linux and found that the Azure Linux images include the implicated upstream component; therefore Azure Linux customers should treat the CVE as potentially relevant to their deployments.- Microsoft has not claimed that every Microsoft product was inventory‑scanned; rather, Microsoft committed to updating the CVE/VEX mapping if additional Microsoft products are identified as carriers. This is a phased transparency approach that started with Azure Linux in October 2025.
Why Microsoft framed it this way
Microsoft’s CSAF/VEX rollout deliberately started with a single product family (Azure Linux) to establish machine‑readable attestations and workflows. VEX documents describe the exploitability/impact relationship between a vulnerability and a named product family; they are authoritative for the artifacts they cover but only cover those artifacts. Microsoft’s public documentation on the VEX rollout explains the phased nature of the program and that additional products will be added as inventories are completed. Tasis for Microsoft’s FAQ wording on product scope.The short, practical answer
No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable venus hfi code. It is the only Microsoft product Microsoft has publicly attested (via CSAF/VEX) to include the implicated upstream component at the time of the advisory; Microsoft will update the CVE/VEX mapping if additional Microsoft‑shipped artifacts are found to carry the same upstream files. In operational terms: treat Azure Linux as a confirmed carrier to prioritize patching, and also assume other Microsoft Linux artifacts might be carriers until you verify them.Why other Microsoft products might also be affected
Several technical and organizational facts make it plausible that other Microsoft artifacts could include the venus driver:- The fix is upstream kernel code. The venus HFI driver is part of the upstream Linux kernel tree and has been widely distributed across device vendors and Linux distros; once patched upstream, distributions and vendor kernels adopt the fix on varying schedules. Because the code is upstream, any Microsoft artifact that ships or compiles a Linux kernel from affected upstream versions could include the same buggy code until patched.
- Microsoft ships multiple Linux‑based artifacts. Microsoft maintains or distributes several kernel‑bearing artifacts beyond Azure Linux, including: Azure Marketplace images, curated VM images, AKS node images, the WSL2 kernel binary distributed with Windows, linux‑azure kernel builds used for certain VM SKUs, and the historical CBL‑Mariner lineage used by Azure Linux. Each of those artifacts is a separate build with its own kernel version and CONFIG_ build flags; the presence of a given driver is an artifact‑by‑artifact* property. That make‑time variability means a driver present in one Microsoft kernel build could be absent in another.
- Kernel build configuration varies by product. Whether the venus hfi drivers are built into a kernel image or compiled as modules — and whether they are enabled at all — depends on the kernel config used when building that artifact. Two Microsoft kernel images built from the same upstream tree can differ substantially in included subsystems. This is why a product‑scoped attestation is necessary to avoid blanket statements that either under‑ or over‑represent risk.
Evidence from distributions and trackers (what independent sources show)
Security trackers, distribution advisories, and the NVD uniformly identify CVE‑2025‑23158 as a venus HFI OOB write and list multiple Linux distributions as affected or patched. Ubuntu, Debian, Red Hat and downstream trackers catalog the defect and the upstream patch; several vendor advisories show fixes landing in kernels used by different distributions. That broad footprint in Linux vendors reinforces the conclusion that an upstream kernel defect can appear in many different downstream images depending on their kernel lineage.Some vulnerability aggregators and vendor bulletins specifically show that CBL‑Mariner/Azure Linux families were tracked for related venus HFI issues in the past, and several cloud vendors and Linux distributors added fixes to their kernel packages once the upstream patch was released. That is consistent with Microsoft focusing its initial VEX inventory on Azure Linux and promising to expand mappings.
How to check whether your Microsoft environment is affected (practical verification)
If you operate Microsoft artifacts or images in your environment, treat this as a per‑artifact verification problem. The following steps will help you determine exposure and prioritize remediation.1. Identify the kernel artifact and version
- Check the exact kernel version in the image or VM: run uname -a (or inspect the image metadata).
- Compare the kernel version and stable‑trehe upstream commit that fixed CVE‑2025‑23158 to see whether the fix is included. Distribution security trackers (Ubuntu, Debian, etc.) list the patched package versions and advisories.
2. Search the kernel config / modules for venus/hfi
- If you have shell access to the image or VM, search /lib/modules/$(uname -r) for drivers/media/platform/qcom/venus or for module names that mention venus or hfi.
- If the kernel image includes a config file (e.g., /boot/config-$(uname -r)), grep for CONFIG_VENUS or for generic Qualcomm video driver flags. Presence of the driver module or built‑in symbol is an immediate signal of potential exposure.
3. Inspect SBOMs and CSAF/VEX outputs
- If you use Azure Linux, ingest Microsoft’s published CSAF/VEX attestation for the CVE and the Azure Linux product family to automate triage — Microsoft published its VEX rollout notes starting October 2025. If you manage other Microsoft‑supplied artifacts, check MSRC’s CVE entries and the company’s VEX/CSAF feeds for new attestations.
- If you have an SBOM or Microsoft‑provided inventory for your image or appliance, locate the kernel package and cross‑reference against distro advisories that list patched package names.
4. If you find a vulnerable kernel, take prioritized action
- Prioritize patching or replacing Azure Linux images with updated kernel packages if the attestation says Azure Linux is potentially affected. Microsoft’s attestation is the authoritative guide for Azure Linux artifacts.
- For other Microsoft artifacts, if the kernel contains the vulnerable driver or upstream kernel version, apply the vendor patch or rebuild the kernel with the upstream fix.
- If you cannot immediately patch, mitigate by restricting access to device nodes, limiting who can load modules or open the media device nodes, and isolating workloads that require direct device firmware interaction.
Remediation and mitigations (technical options)
- Install vendor/kernel updates. The canonical fix is the upstream kernel patch that bounds qsize and validates new_wr_idx; distro maintainers have already released updated kernel packages in many trees. Apply the distribution‑provided updated kernel for your image.
- Rebuild or repackage images with patched kernels. For custom images (Marketplace, AKS node images, etc.), rebuild the kernel deliverable with the upstream fix applied; ensure kernels are built with an up‑to‑date stable tree that contains the patch.
- Unload or blacklist the driver if the hardware and workload permit (note: this may not be possible for built‑in drivers or when the driver is required by the hardware). Use module blacklist and kernel command‑line options where appropriate, but validate that this doesn't break required functionality.
- Harden least privilege for device access. Limit which processes or users can access the device interface; for cloud images, enforce VM isolation and restrict privileged containers from accessing host devices.
- Monitor for exploitation indicators. Watch for kernel oopses, memory corruption logs, unexplained reboots, or abnormal vdec/venus device activity in logs; consider adding temporary kernel integrity monitoring rules for suspicious memory corruption patterns.
Detection and monitoring ideas (operators’ checklist)
- Audit /lib/modules and kernel config files for venus/hfi symbols.
- Run automated SBOM/cross‑reference checks against the CVE and patchedned by your distro vendor.
- Use Microsoft’s CSAF/VEX feed for Azure Linux to automate decisions for Azure Linux images; subscribe to upstream distro CVEs for other images.
- Track kernel oops and dmesg for venus/hfi traces that might indicate attempted exploitation or failure modes.
- For cloud operators, inventory the kernel versions used by Marketplace images, AKS node pools, and custom VM SKUs — treat each as a separate artifact.
What to expect from Microsoft going forward
Microsoft has signaled and begun a phased program of machine‑readable VEX/CSAF attestations that started with Azure Linux in October 2025. The explicit design of that rollout is to publish authoritative attestations for a product family and then expand to additional product families as inventories are completed. Becaproach, further CVE entries may be updated with additional Microsoft product mappings over time as Microsoft completes more inventories. In short: you should expect Microsoft to add product mappings if it finds the component in other Microsoft artifacts.Practically, that means Azure Linux customers receive the clearest, machine‑readable guidance now; other Microsoft customers should either verify their artifacts directly (as outlined earlier) or wait for Microsoft to publish additional attestations for the products they consume — while treating the absence of an attestation as not yet validated rather than as safe.
Risks and limitations of relying on a single product attestation
- Attestation is only as broad as the inventory. Product‑scoped attestations are deliberately narrow to avoid false positives; they cannot substitute for per‑artifact verification across a large enterprise estate that uses multiple Microsoft images and kernels.
- Operational lag. A phased inventory rollout introduces lag between a CVE’s disclosure and the mapping of every vendor artifact. During that window, many images shipped prior to inventory completion could be carrying vulnerable code.
- Build variability. Two images labeled “linux” by the same vendor may include different drivers because of differing kernel configs, kernel versions, or backports. This makes blanket statements about vendor artifacts unsafe.
Recommended action plan for WindowsForum readers and IT teams
- Treat **nfirmed, high priority to patch — follow Microsoft’s guidance and the Azure Linux update path. Azure Linux has been inventoried and attested by MSRC; patch accordingly.
- Inventory all Microsoft‑supplied Linux artifacts in your environment (Marketplace images, AKS node images, VM images, WSL kernels). For each artifact, check kernel version, module list, and vendor advisories.
- For artifacts you control, apply distribution kernel updates or rebuild with patched kernel trees that include the CVE fix.
- If immediate patching isn’t possible, mitigate by reducing privileged access to devices, blacklisting the module (when safe), and monitoring for kernel instability.
- Subscribe to vendor (Microsoft, distro) CSAF/VEX/CSAF feeds and distro security trackers so you are alerted when Microsoft publishes additional product attestations for this CVE or related venus HFI CVEs.
- If you are uncertain whether a Microsoft artifact includes the driver and you cannot inspect it yourself, open a formal support or security inquiry with Microsoft and request a product‑level attestation or SBOM for the specific artifact.
Conclusion
CVE‑2025‑23158 is an upstream Linux kernel defect in the venus hfi media driver with real potential for kernel memory corruption. Microsoft’s public statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is authoritative for Azure Linux customers and reflects Microsoft’s October 2025 CSAF/VEX rollout; but it should not be read as a categorical guarantee that no other Microsoft product includes the vulnerable code. Other Microsoft artifacts that ship a Linux kernel could include the same upstream source if their kernel version and build configuration include the venus HFI driver — and Microsoft has committed to expanding its attestations as inventories are completed. For defenders, the right operational approach is twofold: prioritize patching Azure Linux images per Microsoft’s attestation, and perform per‑artifact verification (or seek Microsoft attestation) for any other Microsoft‑distributed images you run.Source: MSRC Security Update Guide - Microsoft Security Response Center