Das U-Boot suffered a dangerous parsing bug that was disclosed in mid‑2019: an unbounded memcpy in the NFS reply handling code could be driven by attacker‑controlled packet fields, allowing remote memory corruption and, in many configurations, remote code execution on devices that use network boot (NFS/TFTP).
Das U‑Boot (commonly shortened to U‑Boot) is the universal boot loader used widely across embedded and IoT devices, development boards, and many specialized Linux appliances. It implements network boot protocols (TFTP and NFS) so devices can fetch a kernel or root filesystem before storage is available. That network capability—convenient for developers and diskless deployments—also exposes parsing code to attacker‑controlled packets.
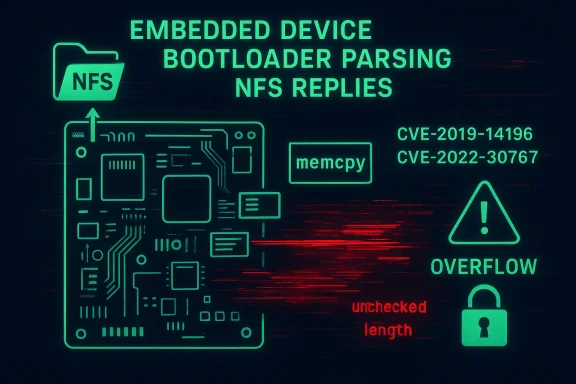
In July 2019 multiple integer‑validation and memcpy patterns were disclosed after a CodeQL‑assisted audit. Several CVEs were assigned across a family of related bugs; CVE‑2019‑14196 specifically describes an unbounded memcpy with a failed length check in the function nfs_lookup_reply in U‑Boot releases up to and including 2019.07. The vulnerability is classified as an out‑of‑bounds write / buffer overflow and was included in a broader set of NFS parsing issues affecting U‑Boot’s network NFS handler.
The GitHub / Semmle analysis shows the precise pattern: U‑Boot reads 32‑bit length fields from the network (via ntohl), stores them into local variables, performs an insufficient comparison against the destination buffer size, then uses that value directly in memcpy. The code paths of interest include nfs_readlink_reply, nfs_lookup_reply, and nfs_read_reply. In some cases the check was present but allowed a negative value to slip through and later be used as a huge unsigned length—an integer‑signedness trap common in network parsing code.
Security product trackers (Snyk, Rapid7, CVE Details) aggregated the data and frequently score the issue with high or critical ratings because the vulnerability is remote‑network‑facing and can result in arbitrary code execution on the bootloader stage. Organizations running vendor firmware or vendor‑supplied U‑Boot binaries should consult vendor advisories and apply firmware updates where available.
Caveat: the U‑Boot project is upstream open source; many embedded devices include vendor‑customized copies with different versioning and backports. That means patch availability for a device depends on the device vendor’s firmware update cadence. If a vendor does not supply updated firmware, owners must rely on vendor guidance or device re‑builds where feasible.
When a fix introduces new problems, it often reflects either missing unit/regression tests, incorrect assumptions about signedness, or incomplete validation of all parsing flows. For maintainers this means adding testcases that reproduce the malicious inputs should be part of the patch submission and acceptance workflow.
The U‑Boot NFS parsing vulnerabilities, including CVE‑2019‑14196, are a reminder that network‑facing parsing bugs in low‑level boot code produce disproportionate risk. For operators, the immediate priorities are inventory, isolation, and patching; for vendors and maintainers, the answer is disciplined fixes, regression tests, and automated analysis. If your environment uses U‑Boot‑based devices, treat the issue as high priority even if public exploitation remains rare—because the fallout from a bootloader compromise is hard to detect and even harder to remediate.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Das U‑Boot (commonly shortened to U‑Boot) is the universal boot loader used widely across embedded and IoT devices, development boards, and many specialized Linux appliances. It implements network boot protocols (TFTP and NFS) so devices can fetch a kernel or root filesystem before storage is available. That network capability—convenient for developers and diskless deployments—also exposes parsing code to attacker‑controlled packets.In July 2019 multiple integer‑validation and memcpy patterns were disclosed after a CodeQL‑assisted audit. Several CVEs were assigned across a family of related bugs; CVE‑2019‑14196 specifically describes an unbounded memcpy with a failed length check in the function nfs_lookup_reply in U‑Boot releases up to and including 2019.07. The vulnerability is classified as an out‑of‑bounds write / buffer overflow and was included in a broader set of NFS parsing issues affecting U‑Boot’s network NFS handler.
What the bug actually is — technical overview
The root cause in plain terms
At its core, CVE‑2019‑14196 is a classic unchecked length problem: the code parses length values from an NFS reply packet and then calls memcpy using those length values without robust validation of both the sign and range of the parsed integer. An attempted length cap exists, but the check could be bypassed by crafted inputs (for example a negative interpreted value that ends up being large when converted to an unsigned size). That results in a memcpy that copies more bytes than the destination buffer can hold, producing a stack or heap overflow depending on the call site.The GitHub / Semmle analysis shows the precise pattern: U‑Boot reads 32‑bit length fields from the network (via ntohl), stores them into local variables, performs an insufficient comparison against the destination buffer size, then uses that value directly in memcpy. The code paths of interest include nfs_readlink_reply, nfs_lookup_reply, and nfs_read_reply. In some cases the check was present but allowed a negative value to slip through and later be used as a huge unsigned length—an integer‑signedness trap common in network parsing code.
Why this matters for embedded devices
U‑Boot runs at a privileged early stage on the device, before the kernel and its later sandboxing/mitigations. Exploiting U‑Boot affords an attacker a powerful foothold: code execution in the bootloader can lead to persistent device compromise, unlocking firmware flashing, bypassing secure boot protections if signatures are checked later in the boot chain, or loading arbitrarily modified kernels and root filesystems. Because many embedded vendors ship devices with U‑Boot as part of their firmware, a remote‑exploitable bug in U‑Boot’s network stack can turn a seemingly innocuous NFS/TFTP service into a vector for device jailbreak or supply‑chain compromise.A closer look at impact and exploitability
- Attack surface: The attack requires U‑Boot to be configured to use network fetching (NFS/TFTP). Not every device or production system leaves those services enabled, but many development images, diskless deployments, and some IoT devices do. When enabled, the NFS reply parsing code is reachable from an attacker‑controlled NFS/TFTP server or a man‑in‑the‑network attacker.
- Attacker position: A local network attacker (same Layer‑2/LAN) or anyone who can trick the device into talking to a malicious NFS server (for example by DNS/DHCP manipulation) can attempt exploitation. The vulnerability is therefore network‑exposed in typical configurations.
- Severity: Different tracking sources assign different scores, but the underlying technical consequence is potentially catastrophic: arbitrary memory corruption in the bootloader can lead to remote code execution. Several vendors and vulnerability trackers reported CVSSv3 scores in the high/critical range for this family of bugs. The practical exploitability depends on device‑specific mitigations (stack cookies, compile‑time hardening) and the attacker’s ability to deliver suitable packet sequences, but the risk is real and material.
- Real‑world exploitation: Public evidence of widespread in‑the‑wild exploitation for CVE‑2019‑14196 specifically is limited, and exploit prediction systems (EPSS) gave relatively low short‑term exploitation probabilities for some of the individual CVEs. That said, the existence of reliable primitives at the boot stage makes the issue a top priority for vendors and device maintainers because the consequences for compromised appliances are severe. Treat low public exploit volume as no comfort for owners of vulnerable devices.
Timeline and disclosure — how this reached public view
- Initial discovery and aggregation: Researchers using CodeQL and manual review found a family of NFS/TFTP parsing bugs in U‑Boot’s network code. The public write‑ups (originally in Semmle / GitHub Security Lab and then mirrored in CVE trackers) describe 13 related vulnerabilities covering similar memcpy and integer‑parsing issues.
- Disclosure: The findings were coordinated with U‑Boot maintainers in mid‑2019 and the community disclosure followed in July 2019. MITRE assigned multiple CVE identifiers; CVE‑2019‑14196 covers the nfs_lookup_reply memcpy problem.
- Patching and follow‑on bugs: U‑Boot maintainers issued fixes over the following months and vendors released advisories and packages. However, follow‑up audits showed that an incorrect or incomplete fix in later releases reintroduced a similar unbounded memcpy pattern, producing a new CVE (CVE‑2022‑30767) in 2022 that specifically notes it originated from an incorrect fix for CVE‑2019‑14196. This highlights the persistent challenges of safe parsing code in low‑level C codebases.
Vendor responses and patch state
Vendors and distributions tracked the issue and published advisories and updates. For example, SUSE and Debian maintained advisories and release updates tied to the required upstream fixes and distribution packages. Ubuntu and other distributions also tracked and remediated vulnerable packaged versions. The public vulnerability databases (NVD, Debian, SUSE advisories) list the affected ranges as U‑Boot versions through 2019.07 and record downstream fixes and advisories.Security product trackers (Snyk, Rapid7, CVE Details) aggregated the data and frequently score the issue with high or critical ratings because the vulnerability is remote‑network‑facing and can result in arbitrary code execution on the bootloader stage. Organizations running vendor firmware or vendor‑supplied U‑Boot binaries should consult vendor advisories and apply firmware updates where available.
Caveat: the U‑Boot project is upstream open source; many embedded devices include vendor‑customized copies with different versioning and backports. That means patch availability for a device depends on the device vendor’s firmware update cadence. If a vendor does not supply updated firmware, owners must rely on vendor guidance or device re‑builds where feasible.
Why a bootloader bug is different from a userland CVE
- Privilege and persistence: U‑Boot runs before the OS and often has direct hardware access. A successful exploit can install firmware alterations or persistent boot chains that survive OS reinstall. This is materially more damaging than many userland bugs.
- Visibility: Bootloader compromise may be invisible to the operating system because the OS loads from a possibly modified kernel or rootfs that’s already been tampered with. Detection and remediation therefore require out‑of‑band firmware verification or factory reflash.
- Patch friction: Embedded vendors often lag on firmware updates. Many consumer devices are rarely patched by their OEMs, leaving vulnerable firmware in the field for extended periods. These practical realities transform a “theoretical” RCE into a long‑tail operational risk.
Practical mitigation and response guidance
Below are prioritized actions for different audiences: device owners, sysadmins, developers, and firmware maintainers.For device owners and operators
- Inventory: Identify any devices under your control that use U‑Boot and that may be configured to network‑boot (NFS/TFTP). Pay special attention to diskless deployments, development boards, and older IoT appliances.
- Vendor advisories: Check your device vendor for firmware updates or advisories. Apply vendor‑provided firmware updates promptly when available. If no update exists, contact the vendor for guidance.
- Disable network boot: Where feasible, disable NFS/TFTP and other network boot options in production devices. If you don’t need network boot, turn it off. This is the simplest and most immediate mitigation.
- Network controls: Block NFS/TFTP traffic to devices from untrusted networks and isolate development networks. Use VLANs and ACLs to limit which hosts can act as NFS servers to device subnets.
- Factory reset + reflash: If compromise is suspected, perform a full factory reset and reflash with a verified firmware image following vendor instructions; do not rely on an OS reinstallation alone.
For manufacturers and firmware maintainers
- Fix carefully and review fixes: As the later CVE shows, an incomplete fix can reintroduce the same class of bug. Implement defenses like explicit unsigned/signed conversions checks, length bounds checks that validate both the source buffer and destination buffer, and use safer parsing idioms.
- Hardened builds: Enable compiler protections (stack canaries, PIE, RELRO where feasible), and apply rigorous static analysis and fuzzing (e.g., AFL/libFuzzer, sanitizers) to network parsing code.
- Upstream coordination: Backport security fixes to vendor branches and make updates available to device owners; publish clear firmware update instructions and advisories.
- Testing and regression: Add regression tests that replicate the malformed NFS reply patterns used to reveal the bug to ensure fixes remain effective across releases.
For developers and embedded integrators
- Avoid unsafe memcpy patterns: Prefer memory helpers that include size and bounds checking, or explicitly implement checks that validate both the parsed length and the available source data length before copying.
- Treat network lengths as untrusted: Whenever parsing lengths from the wire, check for negative values, and prefer using unsigned types only after validating the raw numeric semantics.
- Adopt automated code scanning: Use static analysis tools and CodeQL‑style queries to detect the common pattern of “ntohl → unchecked memcpy” and other taint flows from the network to memory copy sinks. The original discoveries were CodeQL‑assisted and highlight how automation helps find deep systemic issues.
The uneasy lesson: fixes can fail
A hard lesson from this family of CVEs is that fixing parsing bugs in C is error‑prone. In this case, a later incorrect fix led to CVE‑2022‑30767, which reintroduced an unbounded memcpy in nfs_lookup_reply in U‑Boot through later versions. That follow‑on CVE underlines why aggressive regression testing and careful review of fixes are non‑optional for low‑level software—especially code that handles network input before any integrity checks occur.When a fix introduces new problems, it often reflects either missing unit/regression tests, incorrect assumptions about signedness, or incomplete validation of all parsing flows. For maintainers this means adding testcases that reproduce the malicious inputs should be part of the patch submission and acceptance workflow.
Quick checklist — immediate actions (for sysadmins and operators)
- Inventory U‑Boot devices and label which ones can network boot.
- If network boot is unnecessary, disable it immediately.
- Apply vendor firmware updates where available.
- Restrict NFS/TFTP access with network segmentation and ACLs.
- If a device is suspected compromised at boot stage, follow vendor firmware reflash + factory reset guidance rather than OS‑level cleanup alone.
- For vendors: run static analysis + fuzzing on net/nfs.c and all network parsing helpers; add regression tests for malformed NFS replies.
Final assessment — strengths, risks, and what to watch for
- Strengths of the initial response: The vulnerabilities were discovered via modern program analysis techniques and responsibly disclosed. Upstream maintainers produced patches and the open‑source security community was swift to aggregate advisories and track distribution packages. The collaboration between researchers and the U‑Boot custodian limited uncontrolled exposure in the immediate disclosure window.
- Remaining risks: The biggest ongoing risk is the long tail of devices in the field with unpatched firmware or vendor images that never receive updates. The bootloader role amplifies impact, so even low exploit probabilities warrant high operational urgency. The subsequent CVE that reintroduced the issue also signals that fixes must be validated against an expanded test harness—without it, regressions are likely.
- What to watch next: Monitor vendor firmware advisories for any devices you manage, watch distribution security trackers for backported patches, and pay attention to reports of practical exploitation in the wild. If you rely on U‑Boot in development or production, consider building a verification pipeline that checks firmware versions, enforces network isolation during deployment, and automates firmware updates where possible.
The U‑Boot NFS parsing vulnerabilities, including CVE‑2019‑14196, are a reminder that network‑facing parsing bugs in low‑level boot code produce disproportionate risk. For operators, the immediate priorities are inventory, isolation, and patching; for vendors and maintainers, the answer is disciplined fixes, regression tests, and automated analysis. If your environment uses U‑Boot‑based devices, treat the issue as high priority even if public exploitation remains rare—because the fallout from a bootloader compromise is hard to detect and even harder to remediate.
Source: MSRC Security Update Guide - Microsoft Security Response Center