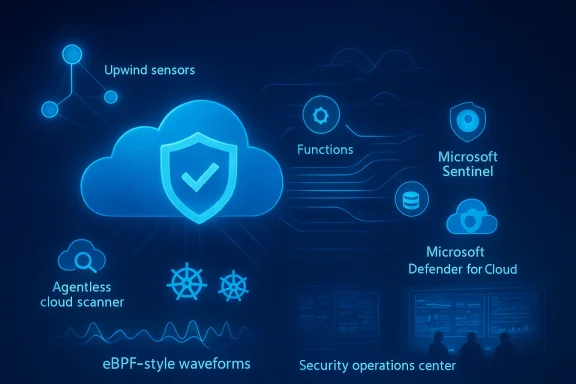
Microsoft Azure customers now have a new native option to close a longstanding visibility gap: Upwind’s runtime-first security platform is officially integrated into the Azure ecosystem, available through the Azure Marketplace and engineered to feed runtime telemetry into Microsoft Sentinel and Microsoft Defender for Cloud so teams can move from theoretical risk to what’s actually happening right now inside workloads.
Cloud security tooling has historically divided into two camps: posture and static analysis tools that inspect configurations, IaC, images, and known CVEs; and runtime defenders—EDR, runtime application self-protection (RASP), and newer kernel-level observability agents—that watch live behavior. Each plays a role, but a blind spot persists when posture tools flag a misconfiguration or a vulnerable library without telling security teams whether that vulnerability is in a running, reachable path an attacker can exploit.
Microsoft’s Defender for Cloud supplies a broad, integrated CSPM/CWPP baseline inside Azure, covering posture, container scanning, and some runtime protections. What Upwind brings to that table is a runtime-first telemetry fabric based on eBPF (extended Berkeley Packet Filter) that observes in-memory execution, syscall and API-level activity, and host-to-service network flows—then correlates that telemetry with cloud, identity, and orchestration signals to produce prioritized, contextual incidents.
This move follows a year-plus of product activity from Upwind—product launches, the acquisition of an eBPF engine, and major fundraising—positioning the company as a runtime-first CNAPP (cloud native application protection platform) vendor that now has an Azure-native delivery path.
eBPF’s advantages for cloud runtime security are clear:
The CNAPP market will likely bifurcate into vendors emphasizing posture + developer security (shift-left, SBOMs, IaC), and vendors that centralize runtime observability and in-memory behavior. Buyers with dynamic, cloud-native environments will increasingly expect both—integrated to provide exploitability-aware prioritization.
Operational requirements for MSPs include:
That said, some vendor claims deserve careful testing:
For Azure-native customers already invested in Defender for Cloud and Sentinel, the partnership offers a pragmatic path to add runtime clarity without duplicating core telemetry pipelines. For MSPs, the multi-tenant design and partner-first commercial model make Upwind a candidate for managed runtime security services.
But success will depend on execution: real-world PoVs are essential to validate performance, compatibility with managed Azure nodes and Windows workloads, and the quality of the vendor’s correlation logic in noisy environments. Runtime instrumentation introduces both operational complexity and powerful new signals; teams that validate carefully and integrate those signals into playbooks will extract the most value.
The partnership is another signal of where cloud security is headed: not just checking “what could be wrong,” but proving what is happening now and whether it can actually be exploited. For security teams wrestling with high-scale cloud operations, that proof can make the difference between hunting in the dark and responding to a precisely described, evidence-backed incident.
Source: ChannelE2E Upwind and Microsoft Partner to Bring Runtime Security to Azure
 Background
Background
Cloud security tooling has historically divided into two camps: posture and static analysis tools that inspect configurations, IaC, images, and known CVEs; and runtime defenders—EDR, runtime application self-protection (RASP), and newer kernel-level observability agents—that watch live behavior. Each plays a role, but a blind spot persists when posture tools flag a misconfiguration or a vulnerable library without telling security teams whether that vulnerability is in a running, reachable path an attacker can exploit.Microsoft’s Defender for Cloud supplies a broad, integrated CSPM/CWPP baseline inside Azure, covering posture, container scanning, and some runtime protections. What Upwind brings to that table is a runtime-first telemetry fabric based on eBPF (extended Berkeley Packet Filter) that observes in-memory execution, syscall and API-level activity, and host-to-service network flows—then correlates that telemetry with cloud, identity, and orchestration signals to produce prioritized, contextual incidents.
This move follows a year-plus of product activity from Upwind—product launches, the acquisition of an eBPF engine, and major fundraising—positioning the company as a runtime-first CNAPP (cloud native application protection platform) vendor that now has an Azure-native delivery path.
Overview: What the Microsoft–Upwind partnership delivers
- A transactable Upwind offering in the Azure Marketplace, simplifying procurement for Azure customers.
- Direct integrations that forward Upwind detections and enriched telemetry into Microsoft Sentinel and correlate with signals in Microsoft Defender for Cloud.
- Runtime visibility across Azure workloads—VMs, containers (AKS), serverless functions—without modifying application code.
- A multi-tenant management model designed for MSPs and MSSPs to deliver managed runtime security services at scale.
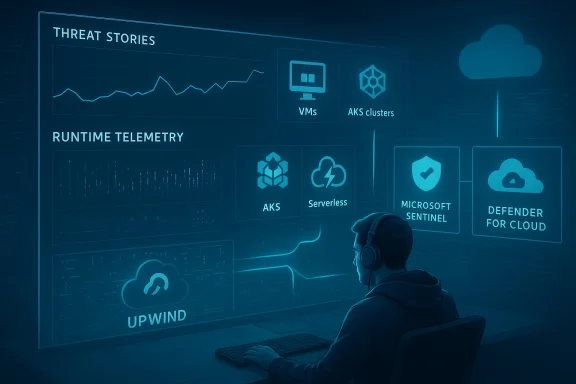
- A runtime correlation model (Upwind’s Threat Stories) that aggregates events into an investigative timeline with root-cause context and response recommendations.
Technical architecture: eBPF as the primary source of truth
Why eBPF matters
At the heart of Upwind’s offering is eBPF, a kernel-level hook-and-observe mechanism that runs sandboxed programs in the Linux kernel to capture rich telemetry from system events—process execution, syscalls, network events, and file operations—without deploying heavyweight kernel modules.eBPF’s advantages for cloud runtime security are clear:
- High fidelity: eBPF captures system-level events that expose what a workload actually does, not just what’s packaged in an image.
- Low overhead: When implemented correctly, eBPF can collect data with a smaller performance footprint than traditional user-space agents.
- Real-time context: Kernel hooks allow detection close to the source of activity, enabling faster, more precise correlation.
From telemetry to action: Threat Stories
A common failure in security operations is alert fragmentation: hundreds of disparate signals that are hard to stitch into a meaningful incident. Upwind addresses this by consolidating related telemetry into structured incident narratives it calls Threat Stories. Each Threat Story contains:- A dynamic timeline of events that led to the detection.
- Cross-signal correlation: runtime events tied to cloud logs, identity actions, and network flows.
- Root-cause context and an assessment of exploitability—whether a finding represents a pathway an attacker can actually use.
- Suggested response actions that reference concrete runtime artifacts (process IDs, container names, API calls).
What the Azure integration looks like in practice
Marketplace and operational plumbing
Upwind is available as a transactable solution on the Azure Marketplace, which reduces procurement friction for organizations already buying cloud services through Microsoft channels. Beyond commerce, the integration points Upwind highlights include:- Microsoft Sentinel ingestion: Upwind can forward enriched alerts and telemetry to Sentinel for SIEM correlation, hunting, and playbook automation.
- Microsoft Defender for Cloud complementarity: Upwind maps runtime detections to posture, asset, and vulnerability signals so teams can understand which cloud posture or config issues are actually being exercised at runtime.
- Microsoft Entra ID integration for identity-based correlation and single-sign-on to manage user provisioning into Upwind.
- Coverage claims for Azure Virtual Machines, AKS (Kubernetes), and Azure Functions, enabling runtime visibility across common Azure compute primitives.
MSP / MSSP enablement
Upwind’s platform includes multi-tenant policies, centralized onboarding, and partner enablement features tailored for managed service providers. This suggests two things:- MSPs can roll runtime visibility across multiple customer environments from a single control plane.
- Upwind’s GTM motions include partner incentives and co-sell readiness on Azure Marketplace—important signals for service providers evaluating a partner-first commercial model.
The practical upside: What security teams gain
- Actionable prioritization: Rather than a long list of possible problems, teams receive consolidated, context-rich incidents that identify reachable attack paths and the exact code or service elements involved.
- Faster detection-to-response: Real-time runtime evidence lets teams trace from an anomalous syscall or unexpected outbound connection to the cloud controls and identity events that enabled it.
- Lower noise and fewer false positives: By correlating runtime events with cloud posture and identity logs, Upwind aims to reduce noisy alerts that are inactive or irrelevant.
- Stronger protection for dynamic workloads: In environments where containers and serverless functions spin up and down quickly, runtime telemetry captures behavior that static scans miss.
- A managed services playbook: For partners, the multi-tenant runtime view enables packaged, repeatable managed runtime security offerings.
Risks, constraints, and what to validate in a proof-of-value
No technology is a silver bullet. eBPF-based runtime platforms add meaningful value but also bring trade-offs and operational considerations security teams should vet.Performance, compatibility, and operational risk
- Kernel-level instrumentation has consequences. While eBPF runs in a sandbox and typically has low overhead, poorly written eBPF probes or misconfigurations can increase CPU usage or induce instability in extreme cases. Validation under production load is essential.
- Managed nodes and immutable environments. In tightly controlled PaaS offerings or in environments where host changes are restricted (e.g., some AKS node pools, managed Windows workloads), deploying kernel-level observability may require coordination with platform teams or selecting compatible node types.
- Windows coverage is different. eBPF originated on Linux and provides deep visibility there; while eBPF ports and Windows equivalents are emerging, Windows runtime visibility remains a different engineering problem. Organizations with large Windows server estates should confirm the vendor’s coverage matrix rather than assume parity.
- Scaling telemetry volume. Kernel-level events are granular and can produce large volumes of telemetry. Buyers should clarify which data is kept locally, what is sampled or aggregated, and how long evidence is retained—particularly for cost and compliance reasons.
Threat-model and false assurance
- Not everything “seen” is exploitable. Vendors will often present high-fidelity telemetry as a catch-all; security leaders should be careful not to conflate visibility with total protection. An environment with excellent runtime telemetry still needs robust identity controls, network segmentation, and secure CI/CD pipelines.
- Vendor consolidation and single point of failure. Integrating runtime telemetry deeply into your security posture increases dependence on that vendor’s accuracy and availability. Ensure incident response plans account for possible gaps or outages in that stream.
- Cloud provider constraints and policy limits. Some cloud customers operate in regulated spaces where introducing new telemetry pipelines requires approvals. Upwind’s partnerships with FedRAMP advisory firms indicate a push into regulated markets, but teams should still confirm compliance posture and auditability.
Questions to put to any vendor during evaluation
- Which Azure compute types and OS versions are supported today, and what's roadmapped for the next 90–180 days?
- What are the agent or sensor deployment patterns? Are node-level changes required for AKS node pools?
- What is the expected CPU, memory, and storage overhead under our workload mix?
- How does the platform define retention, sampling, and redaction for sensitive telemetry?
- Can the platform forward normalized events to Sentinel with native parsers and playbook triggers?
- For MSPs: how is tenant separation enforced, and what are the role and billing models?
The bigger picture: CNAPP evolution and market dynamics
Upwind’s Azure integration is emblematic of two broader market shifts:- A move from purely cloud-posture-first CNAPPs to runtime-first platforms that treat live execution telemetry as a primary input to risk prioritization.
- Increased hyperscaler-native delivery—vendors are packaging deeper capabilities to be consumed through cloud marketplaces and SIEM integrations, reducing friction for enterprise adoption.
The CNAPP market will likely bifurcate into vendors emphasizing posture + developer security (shift-left, SBOMs, IaC), and vendors that centralize runtime observability and in-memory behavior. Buyers with dynamic, cloud-native environments will increasingly expect both—integrated to provide exploitability-aware prioritization.
What MSPs and MSSPs should know
For managed service providers, the proposition is attractive: runtime detection and event-rich Threat Stories allow MSP teams to deliver higher-value managed detection and response with clearer SLAs and escalations that reference reproducible runtime evidence.Operational requirements for MSPs include:
- Centralized onboarding and policy templates for rapid tenant activation.
- Cost controls for telemetry ingestion and per-tenant retention.
- Playbook automation hooks to streamline containment and remediation actions across tenants.
- Audit and compliance features that map evidence to customer-specific retention and data residency needs.
Independent validation and notable claims to verify
Upwind’s positioning—and the marketing claims that runtime-first telemetry cuts noise and exposes reachable attack paths—are consistent with a broader industry trend where eBPF is increasingly used for high-fidelity security telemetry. Multiple technical communities and vendors (Linux Foundation eBPF work, Sysdig, Datadog engineering blogs) corroborate eBPF’s suitability for runtime observation.That said, some vendor claims deserve careful testing:
- Any assertion that a runtime sensor “sees everything” should be taken with caution; observability is constrained by kernel hook points, orchestration boundaries, and cloud platform restrictions.
- Performance and operational stability claims must be measured against your workload mix and scale.
- Compatibility with managed Azure services (certain PaaS or edge-managed nodes) must be validated ahead of wide deployment.
How to run a short, effective PoV with Azure + Upwind
- Define representative workload targets: one AKS cluster with mixed system/user node pools, one Azure VM scale set with Linux nodes, and one Azure Functions deployment if serverless coverage is needed.
- Baseline metrics: capture current alert volumes and mean time-to-investigate for container and VM incidents in Sentinel and Defender for Cloud.
- Deploy Upwind sensors to a subset of nodes (staging) and enable Azure integrations with Sentinel and Defender correlation.
- Run a two-week monitoring window that includes routine traffic patterns and a controlled set of red-team or synthetic anomalies to exercise syscall, network, and identity correlation.
- Compare outcomes: alert noise, time-to-evidence, and fidelity of attack paths reconstructed by Threat Stories.
- Measure overhead: CPU, memory, container startup times, and impact on developer pipelines.
Final assessment
Integrating runtime runtime telemetry into the Azure security stack is a sensible next step for cloud defenders. Upwind’s eBPF-first architecture and Threat Stories model address real operational pain points: noisy alerts, lack of exploitability context, and fractured telemetry across the cloud stack.For Azure-native customers already invested in Defender for Cloud and Sentinel, the partnership offers a pragmatic path to add runtime clarity without duplicating core telemetry pipelines. For MSPs, the multi-tenant design and partner-first commercial model make Upwind a candidate for managed runtime security services.
But success will depend on execution: real-world PoVs are essential to validate performance, compatibility with managed Azure nodes and Windows workloads, and the quality of the vendor’s correlation logic in noisy environments. Runtime instrumentation introduces both operational complexity and powerful new signals; teams that validate carefully and integrate those signals into playbooks will extract the most value.
The partnership is another signal of where cloud security is headed: not just checking “what could be wrong,” but proving what is happening now and whether it can actually be exploited. For security teams wrestling with high-scale cloud operations, that proof can make the difference between hunting in the dark and responding to a precisely described, evidence-backed incident.
Source: ChannelE2E Upwind and Microsoft Partner to Bring Runtime Security to Azure