Microsoft and NVIDIA’s update derailments have pushed a growing number of gamers to one blunt decision: stop trusting automatic updates and treat patches as optional, high‑risk events that must be staged, tested, or skipped entirely on gaming rigs. This shift isn’t a knee‑jerk reaction to a single bug — it’s the accumulation of months of regressions, hotfixes, and emergency out‑of‑band patches that together have eroded confidence in the update pipelines of two companies gamers count on most.
Windows and GPU drivers have always been complex, interdependent pieces of software. Historically, Windows cumulative updates and GPU vendor drivers have introduced new features and fixed security holes without destabilizing everyday use for most users. Lately that balance has shifted: Microsoft’s Windows 11 monthly cumulative rollups and occasional out‑of‑band emergency patches have become frequent flashpoints for regressions that touch real workloads, including gaming. At the same time, NVIDIA’s relatively aggressive driver cadence — including mainline Game Ready drivers and multiple hotfixes — has delivered more rapid fixes but also a higher rate of edge‑case regressions that impact overclocking, fan control, and monitoring.
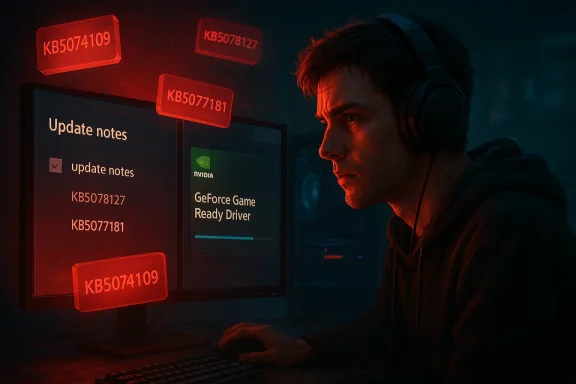
Community reporting and vendor advisories show this is not theoretical: the January and February 2026 Windows patches prompted emergency follow‑ups and user reports of installation failures, UI freezes, cloud‑storage file errors, and GPU‑related instability. Microsoft shipped an out‑of‑band update in January (KB5078127) to address cloud‑storage and related issues, and February’s cumulative (KB5077181) generated widespread reports of installation failures and GPU symptoms on some systems.
On the GPU side, GeForce driver releases around the mid‑590 series created their own controversy: users reported a hot streak of regressions — hardware monitoring and fan control problems and, separately, a driver that appeared to cap voltages and reduce manual overclocks on several RTX 40‑ and 50‑series cards. NVIDIA issued hotfixes and follow‑up drivers, but the oscillation between regressions and emergency fixes left many gamers frustrated and cautious.
Vendors must recognize that the currency of their product is trust. Repeated regressions — even when fixed rapidly — degrade that trust. The fix is not only technical (better QA, staged rollouts, coordinated advisories) but relational: transparent post‑mortems, clearer release notes, and a commitment to minimize surprise in real‑world use cases. Until that trust is rebuilt, many gamers will keep updates on a short leash — and that choice, for many, is the new normal.
Source: Windows Central I'm keeping NVIDIA and Microsoft's buggy updates away from my gaming PC
 Background
Background
Windows and GPU drivers have always been complex, interdependent pieces of software. Historically, Windows cumulative updates and GPU vendor drivers have introduced new features and fixed security holes without destabilizing everyday use for most users. Lately that balance has shifted: Microsoft’s Windows 11 monthly cumulative rollups and occasional out‑of‑band emergency patches have become frequent flashpoints for regressions that touch real workloads, including gaming. At the same time, NVIDIA’s relatively aggressive driver cadence — including mainline Game Ready drivers and multiple hotfixes — has delivered more rapid fixes but also a higher rate of edge‑case regressions that impact overclocking, fan control, and monitoring.Community reporting and vendor advisories show this is not theoretical: the January and February 2026 Windows patches prompted emergency follow‑ups and user reports of installation failures, UI freezes, cloud‑storage file errors, and GPU‑related instability. Microsoft shipped an out‑of‑band update in January (KB5078127) to address cloud‑storage and related issues, and February’s cumulative (KB5077181) generated widespread reports of installation failures and GPU symptoms on some systems.
On the GPU side, GeForce driver releases around the mid‑590 series created their own controversy: users reported a hot streak of regressions — hardware monitoring and fan control problems and, separately, a driver that appeared to cap voltages and reduce manual overclocks on several RTX 40‑ and 50‑series cards. NVIDIA issued hotfixes and follow‑up drivers, but the oscillation between regressions and emergency fixes left many gamers frustrated and cautious.
What actually broke: concise account of major incidents
Windows: KB5074109 → KB5078127 → KB5077181 — a chain of rollups and fixes
- January cumulative KB5074109 (January 13, 2026) was associated with reports of visual artifacts, black screens, and frame‑rate regressions on some NVIDIA GeForce systems. NVIDIA acknowledged it was investigating and advised affected users that uninstalling KB5074109 in reproduced cases restored normal behavior.
- Microsoft published an out‑of‑band January patch, KB5078127, to fix cloud‑storage and other urgent issues introduced by earlier updates; this package explicitly addressed file‑open/save problems for cloud clients and bundled previous fixes. The out‑of‑band release reflects Microsoft’s recognition that some regressions required expedited remediation.
- February cumulative KB5077181 (February 10, 2026) arrived as the next monthly rollup but quickly accumulated reports: installation failures (error codes like 0x800f0983 and related failure codes), UI freezes in taskbar/Start interactions for some machines, and gaming regressions on systems with NVIDIA GPUs or external display setups. These symptoms spawned troubleshooting threads, vendor notes, and a wave of community posts describing reboots, rollbacks, and hotfix hunts.
NVIDIA: 595.59 → 595.71 → 595.76 (hotfixes and regressions)
- GeForce 595.59 was widely reported to contain a hardware monitoring and fan control regression that, on some systems, prevented fans from spinning correctly or interfered with fan curves. Users posted alarming reports describing fans not ramping up under load, a potentially catastrophic symptom if it led to overheating. NVIDIA took these reports seriously and released follow‑up drivers.
- Shortly after, GeForce 595.71 introduced different problems for a subset of cards: users observed that manual overclocks were being muted — clocks and core voltages appeared capped around certain thresholds, limiting the effective headroom for manual tuning. The release notes did not call out any intentional voltage limits, which raised red flags in the enthusiast community. Media outlets and testing labs correlated user telemetry with these behaviors.
- NVIDIA responded with a targeted hotfix (e.g., 595.76 and other expedited packages) to address the voltage/boost behavior and restore expected fan monitoring for affected configurations. The hotfix model is fast but inherently risky because these packages are distributed with abbreviated QA compared with full WHQL Game Ready releases. That tradeoff — speed versus thorough testing — is central to the trust problem many users now describe.
Why trust has declined: structural causes and practical realities
1) Increased complexity, expanded feature surface
Modern GPUs and OS kernels expose many more layers of programmability: telemetry, power management, variable boosting behavior, RT/AI features, and vendor‑specific extensions. Every new feature increases the chance of surprising interactions across drivers, firmware, BIOS, and applications. That complexity translates to a larger testing surface and more potential edge cases that evade pre‑release QA.2) Faster release cadence with hotfix culture
Both Microsoft and NVIDIA have reflexes that emphasize rapid mitigation — rolling out hotfixes, emergency out‑of‑band patches, and expedited driver packages. This approach reduces time‑to‑fix for high‑impact issues but also increases the likelihood of follow‑on regressions because abbreviated QA cycles are, by definition, abbreviated. The community notices these oscillations quickly, and repeated cycles erode confidence.3) Visibility and social amplification
Platforms like Reddit, vendor forums, and specialist outlets make it fast to surface real‑world regressions. While that’s a net positive for troubleshooting, it also amplifies the perception of frequency and severity of bugs when dozens or hundreds of vocal users publish failures within hours. The social signal — “many reports = serious problem” — often translates into immediate behavioral change (disable updates), even where only a minority of configurations are affected.4) Unverifiable / speculative causes (AI, outsourcing, staffing)
A recurring lay theory is that AI‑assisted coding or changes in code ownership and QA staffing contributed to lower quality. Those claims are tempting but largely unverified in the open record. Microsoft’s public remarks about increasing AI use in development are factual in broad strokes, but directly linking specific regressions to AI code generation is unprovable with public evidence today; we should treat those claims as plausible hypotheses, not demonstrated causes. Flag this as an area that requires vendor transparency and better post‑mortems.The risks and tradeoffs of disabling automatic updates
Many gamers have already accepted the tradeoff: reduced risk of new breakages in exchange for deferred security fixes. That decision is defensible for some rigs but not without measurable downsides.- Security exposure: delaying critical cumulative updates exposes your system to newly patched vulnerabilities. Kernel or platform patches may close privilege escalation, remote code execution, or elevation vulnerabilities that are actively exploited in the wild. Skipping these updates indefinitely is not recommended for machines that handle sensitive data, financial tasks, or work profiles.
- Stability vs. currency: by freezing drivers and OS versions, you gain short‑term stability but lose access to performance optimizations, game‑specific launch drivers, and new security mitigations that can benefit your system. Over time, the delta grows and the risk that a future update will cause a much larger compatibility problem increases.
- Vendor support limitations: some game developers and anti‑cheat vendors increasingly expect a modern driver and OS baseline. If you intentionally run an older stack, you might encounter compatibility problems or limited support when diagnosing complex issues. That reality informs whether rolling back is an acceptable long‑term tactic.
Practical, actionable guidance for gamers and enthusiasts
If you’ve reached the point of disabling automatic updates — or are contemplating it — here is a pragmatic checklist to protect your PC while minimizing the chance of surprise regressions.Short term (daily / weekly)
- Delay OS updates by at least two weeks: this gives community testing a chance to expose regressions. Windows Update has built‑in options (Pro/Enterprise) and Group Policy settings to defer feature and quality updates. For many gamers, a two‑week delay is a good balance.
- Set NVIDIA/AMD drivers to manual in the vendor app and avoid automatic driver installs through Windows Update unless you test them in a controlled environment. Keep a known‑good driver installer archived so you can roll back quickly.
- Enable System Restore and create a full image before applying major updates. Tools like the built‑in System Restore, a third‑party imaging tool, or a simple disk image can shrink the recovery time from hours to minutes. This is the simplest insurance policy.
Medium term (monthly)
- Build a two‑system habit: if you’re a serious gamer and value stability, consider splitting roles — keep one machine for live gaming with hardened updates, and use a second testbed to validate new OS and driver combinations. This is the strategy used by many streamers and content creators.
- Follow vendor advisories and hotfix notes: when Windows publishes an out‑of‑band update or NVIDIA issues a hotfix, read the release notes and community reaction before applying. Hotfixes exist for real regressions, but they carry their own risks. Balanced application works best.
Troubleshooting sequence (if you encounter regression)
- Reboot and check Event Viewer for error patterns.
- Test with a clean driver install (DDU uninstall + driver re‑install).
- If symptoms appeared immediately after a Windows update, test uninstalling the offending KB temporarily while you gather telemetry (but only after understanding the security tradeoffs). NVIDIA support previously advised this rollback route as a diagnostic step.
- When in doubt, reproduce the issue with screenshots, logs, and timestamps — this helps vendor triage and speeds up hotfixes.
What Microsoft and NVIDIA should do (and what they’re already doing)
Both vendors have operational reasons for their current approaches: Microsoft’s cumulative model bundles many fixes for enormous scale, while NVIDIA must balance rapid game‑ready releases with broader compatibility. But the community expects more transparency and better communication.- Clearer release annotations and impact scope: Microsoft should add more granular “known issues” and affected component lists in rollups. Users want to know — upfront — whether multimedia, GPU drivers, DisplayPort chains, or third‑party anti‑cheat systems are likely to be affected. KB5077181’s real‑world regressions illustrate how a generic changelog leaves users blind.
- Longer staged rollouts for high‑risk subsystems: both vendors could improve signal quality by extending staged rollouts for kernel or power management changes and monitoring telemetries more aggressively for gaming workloads. A small percentage of early recipients running a “gamer” profile could function as a canary population.
- Vendor coordinated advisories: when the OS vendor and GPU vendor coordinate messaging (e.g., “this KB interacts with driver X and may require hotfix Y”), users benefit and the ecosystem stabilizes faster. We’ve seen ad hoc coordination during past incidents, but a standard operating procedure would help.
- Post‑mortems and transparency: communities want concise post‑mortems describing root cause (when known), affected configurations, and mitigation steps. This builds trust and reduces speculation about causes like rushed QA or AI‑generated code. Transparency is the single best trust‑repair mechanism.
How big is the problem — and is it getting worse?
Quantifying the frequency of regressions is hard because of reporting bias: users who experience issues are far more likely to post about them than those with uneventful updates. That said, the clustering of several high‑impact incidents across a short timeframe — January’s KB5074109 issues, the January KB5078127 emergency patch, and February’s KB5077181 installation/stability reports, plus multiple NVIDIA driver regressions — argues that we are in a noisy period where vendor speed and product complexity collide. The pragmatic conclusion: risk is elevated, and cautious users are right to adapt their update posture.Final analysis: realistic expectations and recommendations
- For casual users who value simplicity and security, automatic updates remain the right default: the majority of installations will update without incident and receive important security patches. For gaming enthusiasts and creators with complex toolchains, the “delay + staged install + test” approach is the most rational tradeoff.
- NVIDIA and Microsoft are capable of fixing serious regressions quickly, but the “fix now” model creates oscillation. Vendors should pair rapid mitigation with clearer QA signaling (which builds trust) and better inter‑vendor coordination (which reduces blame cycles that confuse users).
- Gamers who opt out of automatic updates should adopt an explicit maintenance cadence: weekly security scans, monthly patch reviews, archival of known‑good installers, and a documented rollback plan. Treat updates as a planned operation, not a background convenience.
Conclusion
The move to keep NVIDIA and Microsoft updates at arm’s length on a gaming PC is both understandable and defensible in 2026’s noisy update climate. It’s a rational reaction to repeated high‑visibility regressions and the tension between rapid fixes and thorough QA. But it’s not risk‑free: delaying updates increases attack surface and can complicate future support. The healthiest path forward is a hybrid: vendor vigilance, better communication, and user discipline.Vendors must recognize that the currency of their product is trust. Repeated regressions — even when fixed rapidly — degrade that trust. The fix is not only technical (better QA, staged rollouts, coordinated advisories) but relational: transparent post‑mortems, clearer release notes, and a commitment to minimize surprise in real‑world use cases. Until that trust is rebuilt, many gamers will keep updates on a short leash — and that choice, for many, is the new normal.
Source: Windows Central I'm keeping NVIDIA and Microsoft's buggy updates away from my gaming PC