Microsoft hat die KI‑Unterstützung in Windows 11 einen nennenswerten Schritt weitergedreht: Mit dem Preview‑Update KB5074105 erweitert das Unternehmen die Settings Agent-Funktionalität und bringt erstmals eine offizielle deutsche Sprachsteuerung für die KI‑gestützten Windows‑Einstellungen in den Release‑Preview‑Ring. Das bedeutet: Nutzerinnen und Nutzer können nun in Alltagssprache auf Deutsch beschreiben, welche Systemoption sie ändern möchten — und Copilot bzw. der Settings Agent liefert nicht nur Erklärungen, sondern direkte Verknüpfungen, die die passende Einstellungsseite in der nativen Settings‑App öffnen. Diese Neuerung ist Teil eines größeren, mehrsprachigen Rollouts und wird aktuell schrittweise, kanal‑ und hardwareabhängig verteilt.
Seit dem Herbst 2025 arbeitet Microsoft daran, Copilot tiefer in Windows 11 zu integrieren — nicht länger als isoliertes Chatfenster, sondern als systemweit verfügbares Assistenz‑Ökosystem mit Voice, Vision, Actions und eben Settings‑Agent‑Funktionen. Das Ziel ist pragmatisch: weniger Menü‑Hopping, mehr Konversations‑ oder Absichtssprache, mit der Anwender schneller zu konkreten Einstellungen gelangen. Die jüngste Preview‑Welle (Builds 26100.7701 und 26200.7701, kumulativ als KB5074105 aufgeführt) trägt diese Funktion in den Release Preview Channel — und erweitert zugleich die sprachliche Abdeckungrachen, darunter Deutsch.
Kurz zusammengefasst, was diese Änderung für Windows‑Nutzer bedeutet:
Kurzfristorientierte Empfehlungen:
Abschließend: Probieren Sie die neue Funktion in einer Testumgebung aus, dokumentieren Sie Auffälligkeiten und behalten Sie die offiziellen Ankündigungen im Blick — die Funktion wird stapelweise ausgerollt und kann Ihr Windows‑Support‑Alltag langfristig erleichtern, wenn Governance und Monitoring von Anfang an mitgedacht werden.
Source: BornCity Microsoft bringt KI-Assistenten für Windows-Einstellungen auf Deutsch - BornCity
 Hintergrund / Übersicht
Hintergrund / Übersicht
Seit dem Herbst 2025 arbeitet Microsoft daran, Copilot tiefer in Windows 11 zu integrieren — nicht länger als isoliertes Chatfenster, sondern als systemweit verfügbares Assistenz‑Ökosystem mit Voice, Vision, Actions und eben Settings‑Agent‑Funktionen. Das Ziel ist pragmatisch: weniger Menü‑Hopping, mehr Konversations‑ oder Absichtssprache, mit der Anwender schneller zu konkreten Einstellungen gelangen. Die jüngste Preview‑Welle (Builds 26100.7701 und 26200.7701, kumulativ als KB5074105 aufgeführt) trägt diese Funktion in den Release Preview Channel — und erweitert zugleich die sprachliche Abdeckungrachen, darunter Deutsch. Kurz zusammengefasst, was diese Änderung für Windows‑Nutzer bedeutet:
- Direkte Navigation zu Einstellungen: Natürliche Spracheingabe → KI‑Interpretation → Take‑me‑there‑Deep‑Link zur Settings‑Seite.
- Mehrsprachigkeit: Deutsch ist jetzt offiziell als unterstützte Locale gelistet; weitere Sprachen wie Portugiesisch, Spanisch, Koreanisch, Japanisch, Hindi, Italienisch und vereinfachtes Chinesisch wurden ebenfalls ergänzt.
- Gestaffelte Verfügbarkeit: Die Funktionen werden zuerst für Copilot+‑optimierte Geräte und im Insider‑Ring verteilt; ein weltweiter GA‑Termin ist noch nicht für alle Varianten fixiert.
Was genau bringt KB5074105 — die technischen Eckpunkte
Kernfunktionen im Update
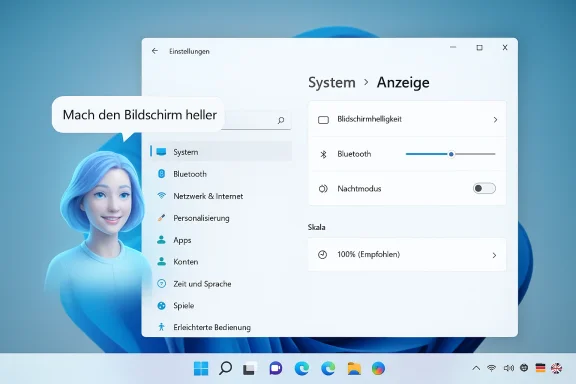
Das Preview‑Paket KB5074105 (Rollout Ende Januar 2026 in den Release Preview Channel) enthält mehrere, teils graduell freigeschaltete Verbesserungen:- Settings Agent: Sprachunterstützung erweitert, inkl. Deutsch. Die Agent‑Funktion interpretiert Outcome‑Anfragen wie „Bildschirm heller machen“ und öffnet die passende Settings‑Seite.
- Cross‑Device Resume (erweiterte Handoff‑Szenarien): Resume‑Karten erlauben das Fortsetzen von Smartphone‑Aktivitäten (z. B. Spotify, geöffnete Tabs oder M365‑Dokumente) auf dem PC.
- On‑device / Copilot+‑Gating: Einige der neuen KI‑Erlebnisse sind für Copilot+ PCs vorgesehen, also Geräte mit NPU‑Fähigkeiten und Microsoft‑zertifizierter Hardware‑/Software‑Stack. Das hat Auswirkungen auf Latenz, Datenschutz und Verfügbarkeit.
- Barrierefreiheit und Systempflege: Verbesserungen am Narrator, Voice Access sowie erhöhte Unterstützung für MIDI‑2.0 und ESS (Enhanced Sign‑in Security) gehören ebenfalls zu den Änderungen.
Versionen und Voraussetzungen
Die Settings‑Agent‑Erweiterung ist sowohl in Windows 11 Version 24H2 als auch 25H2 in Preview‑Builds enthalten; die Kopplung an Copilot‑Versionen (beispielsweise Copilot app Version ≥ 1.25095.161 für Settings‑Deep‑Links) wird in Insider‑Dokumenten erwähnt. Die Verfügbarkeit ist kanal‑, account‑ und hardware‑abhängig; Microsoft nutzt Controlled Feature Rollouts (server‑seitige Gates), sodass ein installiertes Update nicht automatisch die Sichtbarkeit garantiert.Wie der Settings Agent funktioniert — aus Nutzer‑ und Technikersicht
Nutzererlebnis: eine typische Interaktion
- Nutzer tippt oder sagt in Copilot: „Mach den Bildschirm heller“ oder „Aktiviere Bluetooth“.
- Der Settings Agent interpretiert die Absicht (Intent‑Erkennung) und generiert eine Antwort, die eine direkte, klickbare Verknüpfung zur relevanten Settings‑Seite enthält.
- Ein Klick öffnet die native Settings‑App genau an der Stelle, an der die gewünschte Kontrolle liegt — der Anwender macht die Änderung manuell oder folgt der Anleitung.
Technischer Unterbau (vereinfacht)
- Intent‑Erkennung: Lokale oder hybride Modelle (je nach Gerät) analysieren den Text oder das gesprochene Kommando.
- Settings‑Mapping: Die KI übersetzt die Absicht in eine canonical Settings URI oder ein Navigationsziel innerhalb der Settings‑App.
- Deep Link: Ergebnis ist ein Settings‑Deep‑Link, der die native UI‑Route öffnet (z. B. System → Display → Brightness).
Sprachunterstützung: Warum Deutsch wichtig ist
Deutsch gehört zu Microsofts Prioritätenmärkten; lokale Sprachunterstützung ist nicht nur Komfort, sondern ein Faktor für Zugänglichkeit, Akzeptanz und Support‑Aufwände. Die Integration von Deutsch in den Settings Agent hat drei unmittelbare Vorteile:- Niedrigere Support‑Kosten: Anwender, die ihre Probleme direkt in Muttersprache beschreiben können, benötigen weniger Hand‑holding durch Support‑Mitarbeiter.
- Bessere Zugänglichkeit: Für Menschen mit Einschränkungen ist die natürliche Sprache oft wesentlich barrierefreier als verschachtelte Menüs.
- Marktstrategie: Deutschland ist ein Kernmarkt; lokalisiertes KI‑Verhalten stärkt Wettbewerbsposition und Vertrauen.
Risiken, Datenschutz und Governance — was IT‑Teams beachten sollten
Die Einführung dieser KI‑Erweiterungen bringt Chancen, aber auch messbare Risiken mit sich. IT‑Verantwortliche müssen vor einem breiten Rollout folgende Punkte prüfen:- Datenflüsse & Modell‑Routing
Es ist entscheidend zu verstehen, welche Anfragen lokal auf dem Gerät verarbeitet werden und welche in die Cloud wandern. Microsoft unterscheidet zwischen lokalen Small Language Models (z. B. Phi‑Silica‑Klassen für Copilot+ PCs) und cloudbasierten, größeren Modellen. Organisationen sollten klären, ob und wann Telemetrie oder Nutzereingaben außerhalb ihrer Tenant‑Region verarbeitet werden. Nicht alle Details sind auf Betriebsebene standardisiert veröffentlicht; testen Sie und fordern Sie bei Bedarf zusätzliche Dokumentation an. - Lizenzierung & Entitlement
Einige Copilot‑Funktionen sind an Microsoft‑365‑Copilot‑Lizenzen oder Copilot+‑Hardware gebunden. IT‑Teams müssen Entitlement‑Regeln prüfen, um Überraschungen bei Verfügbarkeit und Support zu vermeiden. - Auditierung und Nachvollziehbarkeit
Wenn Agenten Aktionen oder Empfehlungen ausgeben, benötigen Unternehmen Audit‑Logs, um Entscheidungen nachvollziehen zu können. Das Speichern von Chatlogs und die Möglichkeit, Kopien aus Compliance‑Gründen zu archivieren, sind in vielen Branchen Pflicht. - Fehlertoleranz und Rollback
Features werden graduell ausgerollt; stellen Sie sicher, dass Piloten auf repräsentativer Hardware laufen, dass Imaging‑ und Rollback‑Pläne vorhanden sind und dass kritische Workflows nicht von experimentellen Agenten abhängig sind. KB‑Updates wie KB5074105 sollten zunächst in Testphasen geprüft werden — es gab in jüngster Vergangenheit Berichte über Problemfälle mit Preview‑Patches.
Praktische Checkliste für Administratoren und Power‑User
- 1.) Pilot zuerst: Rollen Sie KB5074105 und Copilot‑Updates zunächst auf nicht‑kritischen Geräten im Release Preview oder einem isolierten Test‑Ring aus.
- 2.) Hardware‑Profil prüfen: Identifizieren Sie Copilot+‑PCs in Ihrer Flotte; diese Geräte haben bessere lokale KI‑Erlebnisse.
- 3.) Entitlement‑Mapping: Dokumentieren Sie, welche Nutzergruppen Microsoft‑365‑Copilot Lizenzen und welche Funktions‑Gates benötigen.
- 4.) Datenschutz‑Review: Klären Sie, ob gewünschte Agent‑Interaktionen sensiblen Input enthalten können und ob diese lokal bleiben.
- 5.) Audit‑Prozesse aktivieren: Aktivieren Sie Protokollierung für Copilot‑Interaktionen in geschäftskritischen Bereichen.
- 6.) Benutzer‑Schulung: Informieren Sie Endanwender über Unterschiede zwischen „Guided Navigation“ und „Automated Actions“ sowie über Opt‑out‑Möglichkeiten.
Für Heimanwender: Wie man die neue deutsche Settings‑AI ausprobiert
- Voraussetzungen: Windows 11 (24H2 oder 25H2), Copilot‑App aktualisiert (Version ≥ 1.25095.161 für Settings‑Deep‑Links) und Zugang zum Release Preview Channel oder die schrittweise Freischaltung durch Microsoft.
- Schritt‑für‑Schritt:
- Einstellungen → Update & Sicherheit → Windows Insider Program → Release Preview (nur auf Testmaschinen aktivieren).
- Microsoft Store → Copilot App aktualisieren.
- Copilot öffnen und eine natürliche Anfrage auf Deutsch stellen (z. B. „Reduziere Ablenkungen – Fokusmodus aktivieren“).
- Auf den eingeblendeten Link klicken, der die passende Settings‑Seite öffnet.
- Hinweis: Wenn die Verknüpfung nicht erscheint, liegt das oft an serverseitig gesteuerten Rollout‑Gates oder an Hardware‑Einschränkungen. Geduld bzw. ein Gerät in einem Insider‑Ring erhöht die Chancen, die Funktion zu sehen.
Einschränkungen und offene Fragen
- Nicht alle Aktionen sind agentisch: Der Settings Agent liefert primär Navigationshilfen; komplexe, automatisch ausgeführte Agent‑Actions bleiben experimentell und sind bewusst begrenzt. Dies ist wichtig für Vertrauen und Kontrolle.
- Regionale/Entitlement‑Unterschiede: Einige Funktionen — insbesondere jene, die tiefer in Microsoft 365 integriert sind — werden in der EEA oder China initial zurückhaltender ausgerollt. IT‑Teams sollten lokale Compliance‑Regeln berücksichtigen.
- Stabilitätsrisiken von Preview‑KBs: Vorsicht bei der Installation von Preview‑Patches auf Produktionsmaschinen; KB5074105 ist optional und wurde bereits in einigen Community‑Berichten auf Problemfälle untersucht. Testen Sie sorgfältig.
- Transparenz über Modell‑Routing: Microsoft beschreibt Hybrid‑Architekturen, aber die genaue Routing‑Policy (wann was lokal bleibt und wann in die Cloud geroutet wird) ist auf hoher Ebene gehalten — größere Unternehmen benötigen detailliertere Nachweise. Chancen vs. Risiken
Stärken
- Praktischer Mehrwert: Das direkte Ansteuern von Einstellungsseiten per natürlicher Sprache reduziert Such‑ und Navigationsaufwand massiv — ein klarer UX‑Gewinn.
- Mehrsprachigkeit: Die Erweiterung auf Deutsch und andere Sprachen ist ein strategisch richtiger Schritt, um breite Nutzersegmente zu bedienen.
- On‑device Potenzial: Copilot+‑Hardware bietet niedrige Latenz und bessere Privacy‑Eigenschaften, wenn Modelle lokal laufen.
Risiken
- Rollout‑Fragmentierung: Unterschiedliche Verfügbarkeit nach Region, Hardware und Lizenzierung führt zu Support‑Overhead und Inkonsistenzen.
- Unklare Modell‑Governance: Für regulatorisch sensible Umgebungen sind die bislang veröffentlichten Details nicht immer ausreichend. Unternehmen sollten zusätzliche Nachfragen an Microsoft stellen.
- Preview‑Instabilität: Preview‑KBs können Nebenwirkungen haben; administrativer Pragmatismus ist gefragt (Pilot → Validate → Deploy).
Fazit und Handlungsempfehlungen
Die Integration eines deutschsprachigen KI‑Assistenten für Windows‑Einstellungen ist aus Nutzersicht ein sinnvoller Evolutionstraum: weniger Klicks, bessere Auffindbarkeit und ein zugänglicheres System für Menschen, die nicht mit den tiefen Menüstrukturen vertraut sind. Gleichzeitig verlangt diese neue Ebene der Intelligenz nach sorgfältiger Governance: IT‑Teams, Compliance‑Beauftragte und Security‑Verantwortliche sollten Pilot‑Rollouts definieren, Audit‑Capabilities sicherstellen und genau dokumentieren, welche Interaktionen lokal verbleiben und welche in die Cloud gehen.Kurzfristorientierte Empfehlungen:
- Aktivieren Sie KB5074105 nur in kontrollierten Testumgebungen; führen Sie Kompatibilitäts‑ und Stabilitätstests durch.
- Klären Sie Entitlements (Copilot Lizenzen, Copilot+ Hardware) bevor Sie Anwender informieren.
- Schulen Sie Endnutzer in der Unterscheidung zwischen Guided Navigation (was der Settings Agent hauptsächlich macht) und automatisierten Actions.
Abschließend: Probieren Sie die neue Funktion in einer Testumgebung aus, dokumentieren Sie Auffälligkeiten und behalten Sie die offiziellen Ankündigungen im Blick — die Funktion wird stapelweise ausgerollt und kann Ihr Windows‑Support‑Alltag langfristig erleichtern, wenn Governance und Monitoring von Anfang an mitgedacht werden.
Source: BornCity Microsoft bringt KI-Assistenten für Windows-Einstellungen auf Deutsch - BornCity