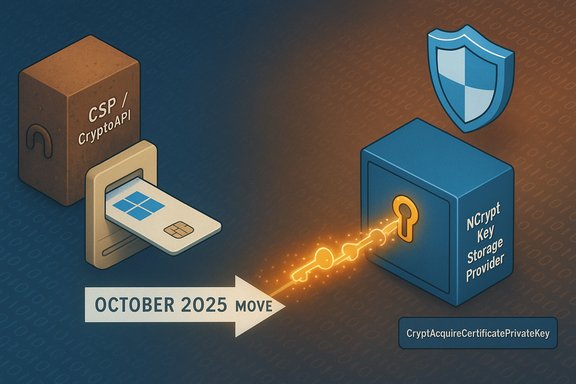
Microsoft’s October security rollout made a deliberate, platform‑level change to how certificates propagated from smart cards are handled — and the change has immediate consequences for applications, middleware vendors, and administrators who still rely on legacy Cryptographic Service Provider (CSP) semantics. The update stops special‑case CSP handling for RSA smart‑card certificates and enforces the Key Storage Provider (KSP) / Cryptography API: Next Generation (CNG) path; where applications continue to assume CAPI/CSP behavior they will fail to access private keys, causing signing, authentication, and certificate‑based workflows to break until those applications are updated.
Smart cards in Windows are surfaced to applications by the Certificate Propagation Service (CertPropSvc), which reads certificates from an inserted smart card and writes them into the user’s Personal certificate store for active use. Historically, that propagation could leave a certificate bound to a provider exposed via the legacy CryptoAPI (CAPI) / CSP model or via the modern CNG / KSP model; Microsoft documented the propagation behavior and governance for certificate propagation in its platform documentation. For RSA keys, Windows previously used a compatibility rule that favored CSP in many propagation scenarios. That behavior limited the cryptographic capabilities available to those keys — CAPI lacks support for several modern algorithm and padding options — creating a practical and security‑relevant mismatch between stored certificates and the stronger cryptography the platform supports. The October 14, 2025 security updates removed the RSA→CSP special case and now prefer KSP for all propagated smart‑card certificates, closing the attack vector addressed by CVE‑2024‑30098. This deliberate hardening improves cryptographic hygiene, but it does not magically update third‑party middleware, CSP providers, or legacy applications. Where those components still assume CSP semantics, operations fail: CryptAcquireCertificatePrivateKey and related calls can return errors such as “invalid provider type specified” or “Keyset does not exist,” and 32‑bit processes that query CSP providers directly are especially exposed. Field reports and Microsoft’s guidance show real‑world symptom sets across desktop, server, and embedded workflows.
Below are specific, actionable developer steps to detect provider type reliably and to migrate code paths. The steps are written for native Windows APIs (C/C++), but the same design principles apply for managed runtimes that interop with platform crypto.
Refer to the official CryptAcquireCertificatePrivateKey documentation for the exact semantics and flags.
For developers, the path is clear: implement Key Storage Retrieval and update code to use the NCrypt/Key Storage API surface. For administrators, the practical plan is to inventory, detect via event logs, coordinate vendor updates, and use enterprise deployment tooling for any temporary mitigations. Treat April 2026 as a hard deadline in project plans — do not rely on further compatibility escapes.
Source: Microsoft Support Guidance for certificate handling for Smart Card propagated certificates - Microsoft Support
 Background / Overview
Background / Overview
Smart cards in Windows are surfaced to applications by the Certificate Propagation Service (CertPropSvc), which reads certificates from an inserted smart card and writes them into the user’s Personal certificate store for active use. Historically, that propagation could leave a certificate bound to a provider exposed via the legacy CryptoAPI (CAPI) / CSP model or via the modern CNG / KSP model; Microsoft documented the propagation behavior and governance for certificate propagation in its platform documentation. For RSA keys, Windows previously used a compatibility rule that favored CSP in many propagation scenarios. That behavior limited the cryptographic capabilities available to those keys — CAPI lacks support for several modern algorithm and padding options — creating a practical and security‑relevant mismatch between stored certificates and the stronger cryptography the platform supports. The October 14, 2025 security updates removed the RSA→CSP special case and now prefer KSP for all propagated smart‑card certificates, closing the attack vector addressed by CVE‑2024‑30098. This deliberate hardening improves cryptographic hygiene, but it does not magically update third‑party middleware, CSP providers, or legacy applications. Where those components still assume CSP semantics, operations fail: CryptAcquireCertificatePrivateKey and related calls can return errors such as “invalid provider type specified” or “Keyset does not exist,” and 32‑bit processes that query CSP providers directly are especially exposed. Field reports and Microsoft’s guidance show real‑world symptom sets across desktop, server, and embedded workflows. What changed in practical terms
- The smart‑card certificate propagation and retrieval path will use KSP (CNG) by default for RSA certificates; the previous behavior that routed certain RSA certificates through CSP has been removed.
- Microsoft enabled this enforcement as part of the October 14, 2025 updates; the change was the remediation for CVE‑2024‑30098, a Windows Cryptographic Services security feature bypass.
- Microsoft published a temporary, per‑machine compatibility toggle — the DisableCapiOverrideForRSA DWORD under HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Calais — that, when set to 0, restores the older CSP behavior for compatibility testing. That registry escape is not present by default and is described as temporary.
- Microsoft has communicated a firm timeline: the compatibility toggle is intended as a short‑term bridge and is scheduled for removal in April 2026; after that removal, only applications and middleware that use KSP/Key Storage Retrieval will interoperate with RSA smart‑card certificates on updated systems.
Why Microsoft made the change (security rationale)
Microsoft’s published justification is straightforward: the legacy RSA→CSP override reduced the cryptographic capabilities available to propagated certificates and created a feature‑bypass risk class exploited by attackers in scenarios related to CVE‑2024‑30098. By requiring that private key retrieval go through the Key Storage APIs (KSP/CNG), Windows constrains how keys are exposed and ensures access flows that support modern algorithms, properties, and hardware security back‑ends. This reduces the attack surface and aligns platform behavior with current cryptographic standards. That move reflects a core tradeoff in platform security: applying an improvement at OS scale forces third parties to modernize, but it also creates short‑term compatibility pain. Microsoft chose an aggressive posture with a temporary compatibility mechanism rather than perpetuating the unsafe default.Who is affected and how it manifests
Typical affected components
- Legacy smart‑card middleware that only implements CSP interfaces.
- 32‑bit applications that call CAPI/CSP semantics directly and do not perform Key Storage Retrieval.
- Custom or proprietary certificate‑auth flows (VPN clients, SSO agents, signing utilities) that assume provider semantics exposed by CSP.
Common symptoms observed in the field
- Certificate‑based sign operations fail in document and code‑signing tools.
- “CryptAcquireCertificatePrivateKey” errors and “invalid provider type specified” logs appear in application traces and the System event log.
- Smart cards no longer appear usable in certain 32‑bit apps or browsers that rely on legacy CAPI flows.
- Automated build or release pipelines that embed smart‑card signing break until middleware is updated.
Early detection
Microsoft advised searching the System event log for Smart Card Service / Microsoft‑Windows‑Smartcard‑Server Event ID 624 (an indicator that the system used CAPI for RSA cryptography prior to the update) as a detection vector for cards/middleware that will be impacted. Administrators who find this event pre‑patch should treat those systems as high‑priority for testing and mitigation.Developer guidance — how to detect the correct handler and fix code
The long‑term and correct fix is to make applications and middleware use the Key Storage APIs and to implement Key Storage Retrieval semantics so keys on cards are exposed via KSP / CNG.Below are specific, actionable developer steps to detect provider type reliably and to migrate code paths. The steps are written for native Windows APIs (C/C++), but the same design principles apply for managed runtimes that interop with platform crypto.
Key concepts to remember
- CryptAcquireCertificatePrivateKey will attempt different provider models based on flags; use it with the right flags to ask for the CNG path.
- CERT_KEY_PROV_INFO and CertGetCertificateContextProperty / CertSetCertificateContextProperty expose provider metadata for a certificate and are the canonical way to inspect how a key is bound to the certificate context.
Detection checklist (recommended sequence)
- Use CertGetCertificateContextProperty with CERT_KEY_PROV_INFO_PROP_ID to retrieve the certificate’s provider info and inspect the provider name and key container fields. This tells you whether the cert originally referenced a CSP or a KSP.
- Call CryptAcquireCertificatePrivateKey with the flag CRYPT_ACQUIRE_ALLOW_NCRYPT_KEY_FLAG. If you receive an NCRYPT handle (the function can return an NCrypt handle alongside flags indicating the provider type), then the key was obtained via KSP; if you get an HCRYPTPROV, you are on the CAPI/CSP path. Examine the dwKeySpec and provider info returned by the function to make a robust decision.
- Where the key is returned as a CNG handle, use NCrypt APIs (NCryptSignHash, NCryptGetProperty, NCryptSetProperty) and avoid CAPI primitives. Where you receive an HCRYPTPROV, do not* assume the modern algorithm surface is available; prefer to move to NCrypt APIs.
Example (pseudo‑code)
Below is compact pseudo‑C demonstrating the detection pattern. Use this pattern to detect and branch cleanly rather than hard‑coding provider names.
Code:
PCCERT_CONTEXT pCert = /* certificate context */;
DWORD dwKeySpec = 0;
BOOL fCallerFreeProv = FALSE;
HCRYPTPROV_OR_NCRYPT_KEY_HANDLE hKey = 0; if (CryptAcquireCertificatePrivateKey(pCert, CRYPT_ACQUIRE_ALLOW_NCRYPT_KEY_FLAG | CRYPT_ACQUIRE_SILENT_FLAG, NULL, &hKey, &dwKeySpec, &fCallerFreeProv)
{ if (dwKeySpec & CERT_NCRYPT_KEY_SPEC) { // hKey is an NCrypt handle — use NCrypt* APIs } else { // hKey is an HCRYPTPROV — legacy CAPI path (CSP) } if (fCallerFreeProv) { // Release handles appropriately: NCryptFreeObject / CryptReleaseContext }
}
else { // Handle failure (log error codes, fallback, user guidance)
}Migration steps for vendors / libraries
- Audit all code paths that call CryptoAPI (CAPI) functions for RSA keys (CryptSignHash, CryptAcquireCertificatePrivateKey, CryptGetUserKey, etc.. Search both 32‑bit and 64‑bit builds.
- Replace or wrap legacy calls with Key Storage API calls (NCryptOpenKey, NCryptSignHash, NCryptExportKey where applicable) so the code asks CNG to operate on keys. Build and test in both process bitness contexts.
- For smart‑card middleware: provide a KSP implementation or update the middleware to expose keys via KSP/CNG interfaces. If the vendor cannot deliver an update before the compatibility key removal, provide clear mitigation guidance or an alternative product.
Short‑term mitigations and administrative playbook
Microsoft documented mitigation options; treat these as emergency, temporary steps while you remediate applications.- Detection: scan System event logs for Event ID 624 from the Smart Card Service to find devices that previously used CAPI for RSA. Prioritise remediation for remote access, signing services, and critical authentication clients.
- Temporary workaround (use only when necessary): set HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Calais\DisableCapiOverrideForRSA to DWORD 0 to opt back into CSP‑style behavior. Deploy this with configuration management tooling (Group Policy, Intune, SCCM / MECM, or infrastructure automation) and treat every affected host as an exception to be tracked and reverted. Microsoft warned that the key is not created by default and will be removed in April 2026.
- Preferred path: obtain vendor patches, upgrade middleware, and test updated clients so that KSP/CNG is supported. Use Known Issue Rollback (KIR) packages where Microsoft supplies them instead of per‑host registry edits where feasible.
- Inventory smart‑card middleware and apps that use certificate‑based auth (VPN, SSO, signing).
- Search for Event ID 624 in System logs; tag devices showing that event as likely impacted.
- Pilot vendor updates in a controlled lab; prefer vendor KSP updates over registry workarounds.
- If continuity requires it, deploy the DisableCapiOverrideForRSA = 0 registry value as a targeted, temporary mitigation using enterprise tooling and track exceptions.
- Schedule and complete application updates before the compatibility toggle removal date; document rollback and incident plans.
Risks, limitations, and what to watch for
- The registry workaround lowers protection against the very vulnerability Microsoft is mitigating. Use it sparingly and only where needed for immediate continuity. Keep the list of hosts with the workaround applied short and under active change control.
- Some community reports indicate the registry workaround itself can produce driver or Smart Card Service errors in certain environments; test thoroughly before broad rollout and maintain recovery options (offline boot media).
- The April 2026 removal date is real and has been published in Microsoft’s advisories and CVE FAQ updates; treat that deadline as non‑negotiable for vendor remediation planning. If you still rely on CSP‑only middleware after the removal date, the impacted workflows will permanently fail on updated systems.
Case studies and real‑world impact (illustrative)
- Build and signing farms: Several organizations reported automatic failures of code‑signing steps that previously used CSP‑backed smart cards; unattended signing jobs either stopped or returned “no matching certificates” errors until middleware vendors published KSP‑aware drivers. These disruptions emphasize the need to test CI/CD signing pipelines after the October updates.
- Browser and web authentication: Browsers that rely on the OS certificate selection dialogs (Edge, Chrome) can be affected when CSP semantics are no longer available for the presented certificate; users may observe missing selection popups or failed client certificate negotiation. Administrators saw these failures in synchronous web auth flows.
Timeline and deadlines — what must be calendared now
- Immediately (if not already done): identify smart‑card dependent apps, search for Event ID 624, and begin vendor outreach.
- Short term (next 30–90 days): pilot vendor KSP updates and validate workflows; use the registry workaround only for critical systems where no vendor fix exists.
- Before April 2026: complete migration of all production clients and middleware to KSP/Key Storage Retrieval or replace with alternative authentication methods. After this date Microsoft plans to remove the compatibility toggle and CSP‑only flows will cease to function for RSA smart‑card certificates.
Summary and editorial assessment
Microsoft’s change to prefer KSP for smart‑card propagated certificates corrects a longstanding platform inconsistency and closes a tangible security gap addressed by CVE‑2024‑30098. The technical rationale — consolidate key retrieval via the Key Storage APIs and retire risky CAPI overrides — is sound and aligns Windows with modern cryptography practices. However, the operational impact is non‑trivial. The ecosystem contains many legacy CSP‑only components and 32‑bit applications that expect CAPI semantics. Microsoft’s choice to ship the enforcement and provide a short‑term registry escape is pragmatic, but it places a heavy burden on vendors and IT teams to coordinate fixes, test widely, and manage targeted rollouts. The registry workaround is a necessary, but risky, stop‑gap: it re‑introduces some exposure to the vulnerability being mitigated and must be removed as soon as practical.For developers, the path is clear: implement Key Storage Retrieval and update code to use the NCrypt/Key Storage API surface. For administrators, the practical plan is to inventory, detect via event logs, coordinate vendor updates, and use enterprise deployment tooling for any temporary mitigations. Treat April 2026 as a hard deadline in project plans — do not rely on further compatibility escapes.
Final, practical checklist (one‑page action items)
- Inventory all smart‑card middleware and certificate‑auth applications.
- Search System event logs for Smart Card Service Event ID 624 and prioritize affected hosts.
- Contact vendors; request KSP/CNG‑compatible drivers and timeline commitments.
- Pilot vendor updates; validate signing/auth flows in 32‑bit and 64‑bit contexts.
- If necessary for continuity, deploy HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Calais\DisableCapiOverrideForRSA = 0 as a targeted, tracked temporary mitigation — do not use as a long‑term solution.
- Schedule remediation work to complete before April 2026; document rollback plans and maintain recovery media to guard against unexpected regressions.
Source: Microsoft Support Guidance for certificate handling for Smart Card propagated certificates - Microsoft Support