Microsoft’s advisory that lists CVE-2026-20948 as a “Microsoft Word Remote Code Execution Vulnerability” is not mistaken when a published CVSS vector shows Attack Vector = Local (AV:L); the two labels answer different operational questions and together give a fuller picture of exploit impact and mechanics.
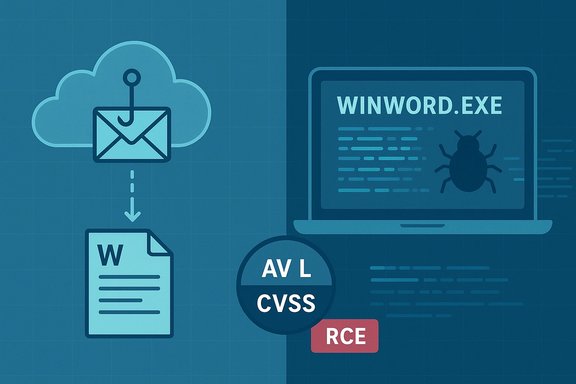
Microsoft’s CVE title — “Remote Code Execution” — is shorthand for the attacker’s origin and worst-case impact: an off-host adversary can cause arbitrary code to run on a victim machine when the exploit chain completes. CVSS’s Attack Vector (AV) metric, by contrast, is a formal measure of where the vulnerable code executes at the moment of exploitation (Network, Adjacent, Local, or Physical). For many Word and Office document‑parsing vulnerabilities, the vulnerable component runs inside a local application process (for example, WINWORD.EXE) when a user opens or previews a file; CVSS therefore records AV:L even though the malicious file may have been delivered remotely (phishing, cloud share, or web download). This distinction — remote delivery, local execution — is deliberate. Vendor advisories use plain‑English high‑signal language to prompt rapid triage, while CVSS supplies standardized, mechanistic scoring for automated risk systems and comparative analysis. Misreading AV:L as “low risk” is the real danger: AV:L for a document RCE often simply means remote delivery is trivial but the actual execution step occurs on the victim’s machine, typically requiring user interaction.
Practical implications:
That communication trade‑off is practical but risky if readers only scan the headline and ignore the CVSS details and advisory prose. The correct operational behavior is to treat an RCE headline as an immediate high‑priority, then use CVSS and the advisory body to craft targeted mitigations.
Flag: If a technical write‑up or exploit proof‑of‑concept is not yet public for CVE‑2026‑20948, refrain from accepting low‑level exploitability claims until they are corroborated by vendor documentation or multiple independent, reputable researcher analyses. Where advisories are terse or dynamically rendered, rely on vendor patch mappings and authoritative CVSS guidance for operational decision‑making.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Microsoft’s CVE title — “Remote Code Execution” — is shorthand for the attacker’s origin and worst-case impact: an off-host adversary can cause arbitrary code to run on a victim machine when the exploit chain completes. CVSS’s Attack Vector (AV) metric, by contrast, is a formal measure of where the vulnerable code executes at the moment of exploitation (Network, Adjacent, Local, or Physical). For many Word and Office document‑parsing vulnerabilities, the vulnerable component runs inside a local application process (for example, WINWORD.EXE) when a user opens or previews a file; CVSS therefore records AV:L even though the malicious file may have been delivered remotely (phishing, cloud share, or web download). This distinction — remote delivery, local execution — is deliberate. Vendor advisories use plain‑English high‑signal language to prompt rapid triage, while CVSS supplies standardized, mechanistic scoring for automated risk systems and comparative analysis. Misreading AV:L as “low risk” is the real danger: AV:L for a document RCE often simply means remote delivery is trivial but the actual execution step occurs on the victim’s machine, typically requiring user interaction.Why the title says “Remote Code Execution” while CVSS uses AV:L
Two complementary questions
- CVE/advisory title (Remote Code Execution): What can an attacker ultimately achieve, and where can they start? If a remote actor can deliver a crafted document that results in arbitrary code running on a target, vendor headlines use “Remote Code Execution” to signal high impact and remote initiation.
- CVSS Attack Vector (AV): Where must the vulnerable code run at the moment the exploit triggers? If the vulnerable logic executes only when a local application parses a file, the correct formal value is Local (AV:L), even if that file was obtained via the internet. This keeps CVSS consistent and avoids double‑counting delivery channels.
A compact example
- Attacker crafts a malicious Word document that targets a parser bug (use‑after‑free, heap overflow, type confusion).
- Attacker delivers that file remotely (phishing attachment, cloud share link, compromised download).
- Victim opens (or a preview handler renders) the file in the local Word process.
- The Word parser triggers the bug; attacker‑controlled code executes inside WINWORD.EXE under the user’s privileges.
The CVSS rule explained: why document parsing bugs are usually AV:L
The CVSS user guide explicitly explains that vulnerabilities which require a local program to parse malicious content should typically be scored with AV:L, regardless of how the file was distributed (email, web download, USB). CVSS measures the exploitability of the vulnerable component at trigger time, not the entire delivery chain. That guidance is the reason document‑parsing RCEs frequently show AV:L even when vendor headlines call them “remote.” Key takeaways from CVSS guidance:- Use AV:N only when the vulnerable functionality itself is network‑reachable (e.g., a network service or a web server that parses uploads server‑side).
- If malicious data is received over the network by one component and then passed to a separate local component that contains the flaw, the vulnerable component’s AV is Local.
- The CVSS approach avoids “double‑counting” network delivery and yields consistent, repeatable scoring across different vulnerability classes.
The important exception: when AV becomes Network (AV:N)
There is a critical operational exception that materially changes exposure: if a network‑facing server or service parses user‑supplied documents on behalf of remote clients (mail gateways that generate previews, Office Online Server, CMS preview processors, document‑conversion services), the vulnerable parser may execute inside a network‑exposed process. In that configuration, exploitation can occur without a user opening a file locally and the Attack Vector should be Network (AV:N). Vendor advisories will call this out when applicable because it dramatically increases risk.Practical implications:
- Inventory any server‑side rendering, mail gateway, or collaboration service that performs previews or conversions.
- Treat any such server that uses the same vulnerable parser as a higher priority for patching and isolation.
- If a vendor advisory explicitly states that preview handlers or server components are affected, assume AV:N exposure until proven otherwise.
Why vendors choose “Remote Code Execution” in short headlines
Vendor and MSRC headlines are written to be short, urgent, and actionable for defenders and managers. “Remote Code Execution” is a concise signal: the vulnerability class allows an external actor to cause arbitrary code execution on endpoints. This triage signal stimulates fast remediation workflows across large organizations and non‑technical stakeholders. The advisory body and CVSS vector then supply the technical context — how exploitation must occur.That communication trade‑off is practical but risky if readers only scan the headline and ignore the CVSS details and advisory prose. The correct operational behavior is to treat an RCE headline as an immediate high‑priority, then use CVSS and the advisory body to craft targeted mitigations.
Verifying the technical facts (what we can and can’t confirm)
- Microsoft’s Security Update Guide entry for CVE-2026-20948 lists it as a Microsoft Word Remote Code Execution Vulnerability; the MSRC advisory headline therefore correctly highlights attacker origin and impact. Note: the MSRC page is dynamically rendered; retrieving the full CVSS vector directly via an automated fetch may be blocked by JavaScript, so consult the MSRC UI, NVD, or vendor advisory for the exact vector string.
- The CVSS specification and user guide (FIRST.org) explicitly direct scorers to use AV:L for document parsing vulnerabilities that are triggered by local programs, even when malicious data was delivered over a network. This authoritative guidance corroborates the semantic distinction between a “Remote Code Execution” headline and CVSS’s AV:L.
- Independent operational analyses and security community write‑ups reinforce the same interpretation: RCE in the title refers to the attacker’s location (remote delivery capability) and outcome (arbitrary code), while AV:L describes the execution context (local parsing). These community analyses are consistent with both MSRC advisories and CVSS guidance.
Operational risk analysis: why AV:L document RCEs remain high impact
Even though AV:L reduces the exploitability component compared to AV:N in CVSS, real‑world exposure for Office RCEs remains high because:- Delivery channels are numerous and trivial at scale: phishing emails, cloud‑share links, shared drives, web downloads, and supply‑chain attachments.
- User interaction requirements (UI:R) are often satisfied by social‑engineering lures or automatic preview features (Outlook preview pane, file manager thumbnails). Preview handlers can sometimes trigger parsing without explicit “open,” raising practical exposure.
- Post‑exploit steps from a local RCE (credential theft, lateral movement, persistence, ransomware staging) are common and highly impactful.
- Many organizations centralize previewing or conversion services; if those services use the vulnerable parser, the effective exposure changes to network‑facing.
Practical mitigation checklist (prioritized)
- Patch first
- Identify affected Microsoft Word / Office SKUs using MSRC’s Security Update Guide and deploy updates across endpoints and server systems immediately. Vendor patches are the definitive fix.
- Harden ingestion and previewing
- Disable or quarantine automatic attachment previews in mail gateways and user clients.
- Enable sandbox/detonation for suspicious attachments in mail and file ingestion platforms.
- Isolate or patch any server‑side rendering/conversion services that may parse uploaded documents.
- Enforce Office hardening
- Turn on Protected View for files from the internet.
- Disable unneeded macros and block unsigned macros by policy.
- Enforce Application Control policies (AppLocker, WDAC) and attack surface reduction rules to limit Office from launching child processes.
- Least privilege and containment
- Ensure users run under least‑privilege accounts; avoid local admin by default.
- Use endpoint containment features and network segmentation to limit lateral movement in case of compromise.
- Detection and hunting
- Monitor and alert for Office processes (winword.exe, excel.exe, powerpnt.exe) spawning non‑standard child processes (cmd.exe, powershell.exe, mshta.exe, wscript.exe).
- Watch for Office processes initiating unusual outbound network connections shortly after file open.
- Add EDR rules that detect in‑memory code injection and anomalous module loads by Office processes.
- User awareness
- Reinforce phishing‑resistance training and encourage caution with unexpected attachments or cloud‑share links.
- Teach users to prefer viewing documents in safe, sandboxed viewers or web‑based viewers that do not use the vulnerable parsers (but verify server‑side parsing risk first).
Detection recipes and forensic indicators
- EDR detections to prioritize:
- Parent process: winword.exe (or excel.exe/powerpnt.exe) → Child process: cmd.exe, powershell.exe, regsvr32.exe, mshta.exe, wscript.exe.
- Office process loading unusual native DLLs or performing suspicious memory injection.
- Office processes initiating outbound C2‑style connections immediately after opening a file.
- SIEM/hunt queries:
- ProcessCreation events where ParentImage endswith \winword.exe and CommandLine contains encoded PowerShell or download‑and‑execute patterns.
- File creation events for suspicious office documents coming from external email or cloud storage buckets and then opened by users.
Critical analysis — strengths and potential risks of the current labeling approach
Strengths- High‑signal triage: “Remote Code Execution” quickly communicates worst‑case impact and remote delivery capability to defenders and executives, prompting rapid patch cycles.
- Standardized scoring: CVSS’s AV metric provides consistent mechanistic scoring that supports automated prioritization and cross‑CVE comparisons.
- Advisory detail: When vendors include User Interaction (UI), Privileges Required (PR), and notes about preview handlers or server‑side parsing, defenders receive useful context for planning mitigations.
- Misinterpretation by non‑technical audiences: Teams that see AV:L and assume the vulnerability is less urgent can dangerously deprioritize RCE‑class advisories. AV:L does not imply low impact.
- Overreliance on headlines: Quick scans of “Remote Code Execution” without reading advisory bodies and CVSS details lead to misaligned mitigation choices.
- Preview and server‑side blind spots: Organizations that centralize document previewing may inadvertently expose network‑accessible attack surfaces; missing this during triage substantially increases compromise risk.
Short FAQ (practical answers)
- Why does the CVE title say “Remote” when CVSS is AV:L?
- “Remote” in the title refers to the attacker’s origin/delivery capability, not the exact execution locality at trigger time. CVSS AV:L documents where the vulnerable code runs when exploited. Both are correct and complementary.
- Does AV:L mean we can wait to patch?
- No. Because remote delivery is trivial (phishing, cloud shares) and user interaction is often the only requirement, AV:L document RCEs are frequently weaponized rapidly. Prioritize patching.
- When should I treat the vector as AV:N?
- When a network‑facing component or server parses documents on behalf of remote users (mail servers generating previews, Office Online Server, CMS preview engines). If the vulnerable parser runs server‑side, exploitation can be network‑triggered and the correct score is AV:N.
- Where can I confirm the exact CVSS vector for CVE-2026-20948?
- Confirm via the MSRC Security Update Guide entry for the CVE, the NVD record, or your trusted vulnerability feed. Note that vendor pages may be dynamically rendered; use the official mapping to affected SKUs for patch planning.
Conclusion
The apparent contradiction — CVE titled “Remote Code Execution” versus CVSS Attack Vector = Local (AV:L) — is a matter of language and measurement, not a vendor error. The CVE title succinctly signals attacker reach (remote delivery) and impact (arbitrary code execution), while CVSS AV documents the exploit mechanics and where the vulnerable code is executed (local parsing in the Word process). Both signals are essential for correct triage: treat RCE headlines as urgent, consult CVSS and the advisory body for exploitation constraints, verify whether any server‑side components perform parsing (which would change exposure to network), and apply the prioritized mitigation checklist (patching, ingestion hardening, Office hardening, detection, and user controls) without delay.Flag: If a technical write‑up or exploit proof‑of‑concept is not yet public for CVE‑2026‑20948, refrain from accepting low‑level exploitability claims until they are corroborated by vendor documentation or multiple independent, reputable researcher analyses. Where advisories are terse or dynamically rendered, rely on vendor patch mappings and authoritative CVSS guidance for operational decision‑making.
Source: MSRC Security Update Guide - Microsoft Security Response Center