Zilliz’s announcement that Zilliz Cloud BYOC (Bring Your Own Cloud) is now generally available on Microsoft Azure marks the company’s most significant multi‑cloud maneuver to date, bringing its managed Milvus-based vector database into customers’ own Azure subscriptions and completing BYOC coverage across the three major public clouds—AWS, Google Cloud Platform (GCP), and Microsoft Azure.
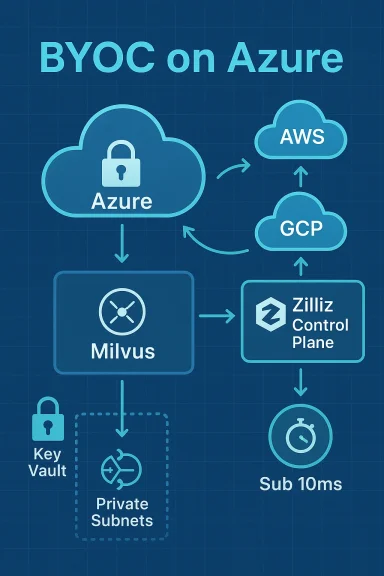
The move closes a practical gap that many enterprises face when building generative‑AI and retrieval‑augmented workflows: choosing between the operational simplicity of a managed service and the compliance, residency, and network isolation benefits of hosting data inside a customer‑controlled cloud account. Zilliz positions Zilliz Cloud BYOC as a hybrid approach that keeps the data plane inside the customer’s cloud tenancy while Zilliz manages control‑plane operations and platform capabilities. The company’s announcement and supporting documentation say BYOC is now GA on Azure after earlier rollouts on AWS and GCP.
This article examines what the Azure launch actually means for enterprise teams, verifies the technical claims that accompany the announcement, compares the offering with industry alternatives, and highlights the practical trade‑offs and risks organizations should evaluate before adopting a BYOC model for vector search and hybrid retrieval workloads.
However, organizations should treat vendor performance and “first” claims with due diligence: run representative benchmarks, validate security and governance controls in a staging environment, and calculate TCO including the operational overhead BYOC places on the customer side. Zilliz’s BYOC model is a powerful compromise—offering managed capabilities without surrendering the cloud tenancy—but it shifts certain responsibilities back to the customer, which is precisely the trade‑off many compliance‑conscious teams are willing to make.
In the short term, expect Zilliz to pitch BYOC as the go‑to model for regulated industries and for organizations standardizing on Azure; in the medium term, expect competitors to respond with their own multi‑cloud or BYOC‑like options. For WindowsForum readers planning deployments, the practical next steps are straightforward: run a constrained PoC, involve security and cloud governance teams early, and use the Terraform provider to treat BYOC infrastructure like any other reproducible, auditable cloud resource.
Source: Thailand Business News Zilliz Cloud Brings BYOC to Azure, Extending Availability Across Major Cloud Platforms - Thailand Business News
 Background / Overview
Background / Overview
The move closes a practical gap that many enterprises face when building generative‑AI and retrieval‑augmented workflows: choosing between the operational simplicity of a managed service and the compliance, residency, and network isolation benefits of hosting data inside a customer‑controlled cloud account. Zilliz positions Zilliz Cloud BYOC as a hybrid approach that keeps the data plane inside the customer’s cloud tenancy while Zilliz manages control‑plane operations and platform capabilities. The company’s announcement and supporting documentation say BYOC is now GA on Azure after earlier rollouts on AWS and GCP.This article examines what the Azure launch actually means for enterprise teams, verifies the technical claims that accompany the announcement, compares the offering with industry alternatives, and highlights the practical trade‑offs and risks organizations should evaluate before adopting a BYOC model for vector search and hybrid retrieval workloads.
What Zilliz announced — the essentials
- Zilliz Cloud BYOC is now generally available on Microsoft Azure, completing BYOC availability on AWS, GCP, and Azure. Zilliz frames this as making it the first managed vector database provider to support BYOC on all three major clouds. This claim appears in Zilliz’s press release and is repeated across company channels.
- The Azure BYOC option is offered as part of Zilliz Cloud’s full feature set, built on the open‑source Milvus engine, and is available in BYOC modes that locate the data plane fully within a customer’s Azure subscription. Official documentation and release notes describe a BYOC‑I deployment mode that places the data plane inside the customer subscription and a Terraform Provider to automate provisioning.
- Zilliz’s marketing reiterates key platform claims: support for billion‑scale workloads, sub‑10ms query latency in many configurations, auto‑scaling and optimized indexes for GenAI tasks (semantic search, RAG), and migration tooling from other vector engines (Pinecone, Qdrant, Weaviate, Elasticsearch/OpenSearch, PostgreSQL, or self‑hosted Milvus). Zilliz’s docs and support articles provide specific latency guidance across compute unit types.
Why this matters: enterprise implications
Data sovereignty and compliance
BYOC is a concrete solution for organizations that cannot, due to policy or regulation, move sensitive vector data into a third‑party tenant. By deploying the data plane inside their own Azure subscription, security teams retain:- Control over key management and encryption (customer‑managed keys where supported).
- Full visibility in their cloud billing and existing audit trails.
- The ability to keep data within a specific jurisdiction for regulatory compliance.
Co‑location with Azure AI services
For Azure‑first organizations, running the vector database in the same subscription reduces cross‑cloud network hops, avoids egress costs, and simplifies integration with services like Azure OpenAI Service, Blob Storage, and Azure Data Factory. Zilliz emphasizes the benefit of keeping AI pipelines inside one cloud environment, which is a practical operational win for latency‑sensitive scenarios.Faster time to production with compliance
Zilliz pitches BYOC as enabling production‑grade vector search in days, not months by eliminating the need for customers to build and maintain complex Milvus clusters. The degree to which that is true depends heavily on the customer’s cloud maturity—teams already operating Terraform or IaC pipelines and with well‑defined networking and IAM practices will see the fastest results. Zilliz’s Terraform Provider is designed to help automate this path.Verifying the technical claims
Zilliz and Milvus make specific performance and scale claims; here’s what we can verify from public documentation and independent sources.Sub‑10ms latency and billion‑scale support
- Zilliz’s support pages and public benchmark notes show sub‑10ms results for top‑k searches under defined test conditions (for example, performance‑optimized compute unit types with 1M vectors). The documentation clarifies the latency band can vary by CU type, dimensionality, and dataset size—e.g., capacity‑optimized CUs show higher latencies for larger datasets. These nuances appear in official support documentation.
- Case studies Zilliz publishes (and its customer examples) show real customers achieving low‑millisecond latencies at scale; however, these are vendor‑curated case studies and look best at illustrating what’s possible rather than guaranteeing identical performance in every environment. Independent APN coverage and analyst writeups confirm that Zilliz is capable of high performance through optimizations like Cardinal search and AutoIndex, but actual latency depends on workload characteristics and index choice.
BYOC architecture and automation
- Zilliz provides a Terraform Provider to automate BYOC deployments and a detailed "Deploy BYOC‑I on Microsoft Azure" guide demonstrating required IAM roles, networking constructs (VNet, subnets), and a BYOC agent that connects the customer data plane to Zilliz control functions. The docs explicitly state the Data Plane remains in the customer subscription for BYOC‑I.
- Release notes document when Azure BYOC moved from preview to GA, and reference additional enterprise features (audit logs, customer‑managed keys) that strengthen the compliance posture. Those release notes corroborate the timeline of Zilliz’s multi‑cloud BYOC expansion.
How Zilliz’s BYOC stacks up against alternatives
Vector databases and managed vectors services are a crowded and fast‑moving market. Key factors to evaluate when comparing Zilliz BYOC to alternatives:- Multi‑cloud BYOC coverage: Zilliz now claims BYOC on AWS, GCP, and Azure—if an organization requires unified operations across clouds with BYOC, Zilliz’s offering is purpose‑built for that scenario as of this announcement. Independent business coverage and Zilliz’s own release notes confirm the coverage, although definitive accounting that makes Zilliz uniquely “first” across every vendor depends on private product roadmaps and competitor claims. Exercise caution before treating “first” as an uncontestable industry fact.
- Managed vs. self‑hosted trade‑offs: Runnings ultimate control but requires deep SRE skills. Zilliz BYOC removes operational overhead while keeping the data plane in your tenancy—positioned between pure SaaS and DIY. The AWS Partner Network blog and DBTA coverage highlight this middle ground as a practical enterprise compromise.
- Ecosystem and integrations: Zilliz supports migration from other vector services and integrates with embedding pipelines and model hosting. If your architecture depends on native integrations with a cloud provider’s AI stack, check whether you need provider‑native services (e.g., proprietary index features) or an external vector engine that co‑operates with those services through standard networking and APIs. Zilliz’s BYOC mitigates many integration headaches by co‑locating with Azure AI services.
Deployment scenarios and a recommended checklist
Organizations evaluating Zilliz BYOC on Azure should walk through a structured checklist. Below are recommended steps and considerations:- Identify the deployment mode: choose between BYOC‑I (data plane in your subscription) and other Zilliz modes depending on control and ease of use.
- Inventory regulatory and residency requirements: confirm whether your jurisdiction requires data to remain in a specific region, and verify Azure region availability for Zilliz BYOC where required.
- Exercise the Terraform provider in a staging environment: validate the IaC workflows and ensure your CI/CD pipeline can manage Zilliz resources and rotate credentials securely.
- Test indexing and query patterns with representative datasets: benchmark different index types and compute unit combinations to confirm latency and cost profiles. Zilliz support pages provide latency guidance to start from.
- Design key management and network controls: plan use of customer‑managed keys (CMK), private subnets, NSGs, and optional WAFs to meet security and audit requirements. Zilliz release notes note CMK and audit log availability.
- Validate integration with Azure AI stack: co‑locate retrieval with Azure OpenAI Service where necessary, then test full RAG pipelines end‑to‑end to measure latency and cost.
Cost and billing considerations
One of the selling points for BYOC is transparent billing: infrastructure costs flow through the customer’s cloud bill while Zilliz invoices for control‑plane management and feature access.- Advantages:
- Use existing enterprise agreements, reserved instances, or committed use discounts on Azure to reduce total cost.
- Predictable cloud billing for compute and storage; Zilliz’s managed fee sits separately for control‑plane and platform services.
- Caveats:
- Egress and cross‑region traffic still cost money if you must move data between regions or clouds.
- Operational costs for managing IAM, VNet, key rotation, and the BYOC agent lifecycle fall on the customer—even if the database itself is managed.
- Benchmark real workloads: some index choices and high‑QPS scenarios may require more capacity than naïve estimates suggest.
Security, governance and risk analysis
Zilliz highlights enterprise security features—RBAC, TLS, audit logs, customer‑managed keys, and the ability to keep the data plane inside the customer subscription. These are meaningful controls, but they do not eliminate risk; they change its locus.- Positive controls:
- Data plane in customer tenancy reduces the attack surface that goes through a vendor‑managed public endpoint.
- Customer‑managed keys and integration with Azure’s key vaults give security teams separation of duty and governance control.
- Residual risks:
- The BYOC model relies on a BYOC agent and control‑plane communication between Zilliz and the customer network. Teams must validate network flows, outbound firewall rules, and minimum‑privilege IAM roles to prevent over‑privileged access or unexpected lateral movement.
- Operational misconfiguration (open subnets, overly broad IAM roles, leaked API keys) remains a primary risk vector—not solved automatically by BYOC. Zilliz provides IAM and role documentation, but enforcement and regular audits are the customer’s responsibility.
- Verification:
- Security and compliance teams should perform threat modeling and a hands‑on penetration test of BYOC deployments before production use. Vendor audit artifacts (SOC2, ISO) are helpful but do not substitute for environment‑specific validation.
Migration path from other vector engines
Zilliz says BYOC includes migration paths from Pinecone, Qdrant, Elasticsearch, PostgreSQL, OpenSearch, Weaviate, or self‑hosted Milvus. Migration feasibility depends on:- Data format alignment: vectors and metadata models must be translated; Zilliz claims tool‑assisted migration and supports multiple import routes.
- Consistency and downtime: migrations of large datasets may require staged strategies (bulk import, reconciliation, DNS switchovers).
- Query logic and index parity: different vector engines use different nearest‑neighbor algorithms and accuracy/speed trade‑offs; expect tuning work after migration.
- Export vectors + metadata from source and validate schema mapping.
- Load into a staging Zilliz BYOC cluster and compare recall/latency against the source.
- Run A/B testing on application traffic, measure costs, and iterate on index parameters.
- Cut over with rollback plans and data reconciliation jobs.
Competitive and market context
Zilliz’s BYOC pitch sits at the intersection of several trends:- Enterprises are increasingly sensitive to data residency and governance around LLMs and RAG pipelines.
- Vector databases have become critical infra for retrieval and multi‑modal AI workflows.
- Multi‑cloud and hybrid strategies remain common; vendors that can operate in customers’ clouds without forcing data movement have a commercial edge.
Practical caveats and where to apply caution
- “First managed vector database provider to support BYOC on all three major clouds” is a vendor claim. It is reported widely in Zilliz channels and press syndication, and it is supported by Zilliz’s rollout chronology (AWS, GCP, Azure). However, a definitive industry audit confirming it as an uncontested first is not present in public records; similar features or adjacent approaches from other vendors may exist in specialized forms. Companies should evaluate feature parity, not only marketing language.
- Performance claims are context sensitive. Benchmarks in vendor documentation and customer case studies show impressive figures, but real‑world performance requires workload‑specific validation—especially for high‑dimensional embeddings, high top_k queries, or mixed real‑time and batch workloads.
- BYOC reduces some third‑party exposure but increases your operational responsibilities around IAM, network hardeand lifecycle maintenance. Ensure those teams are staffed and processes are automated prior to production rollout.
Recommended evaluation plan for WindowsForum readers and IT teams
- Shortlist critical acceptance criteria before any PoC: latency/SLA thresholds, region/residency requirements, cost targets, and disaster recovery objectives.
- Run a controlled PoC with representative queries and model embeddings. Validate both query latency and accuracy (recall/precision) alongside cost.
- Use Zilliz’s Terraform Provider in a sandbox to check whether your Ops pipeline can provision, monitor, and tear down BYOC resources reproducibly.
- Validate security posture via tabletop exercises and a penetration test focusing on the BYOC agent and control‑plane channels.
- Compare total cost of ownership across three scenarios: Zilliz SaaS (control plane + vendor data plane), Zilliz BYOC (control plane + customer data plane), and self‑hosted Milvus (customer data plane + full ops). Account for engineering staff time and risk premiums for each option.
Bottom line
Zilliz’s GA of BYOC on Azure is an important, practical step for enterprises that want the ease of a managed vector database while retaining strict control over where vector data lives. The combination of a documented Terraform Provider, BYOC‑I data plane deployments, and explicit security features makes Zilliz a credible option for regulated and large enterprises that need to co‑locate vector search with the rest of their Azure AI stack. Official Zilliz documentation and release notes verify the Azure GA and the Terraform automation; independent coverage in industry outlets and partner blogs corroborates the offering’s practical value for enterprises.However, organizations should treat vendor performance and “first” claims with due diligence: run representative benchmarks, validate security and governance controls in a staging environment, and calculate TCO including the operational overhead BYOC places on the customer side. Zilliz’s BYOC model is a powerful compromise—offering managed capabilities without surrendering the cloud tenancy—but it shifts certain responsibilities back to the customer, which is precisely the trade‑off many compliance‑conscious teams are willing to make.
In the short term, expect Zilliz to pitch BYOC as the go‑to model for regulated industries and for organizations standardizing on Azure; in the medium term, expect competitors to respond with their own multi‑cloud or BYOC‑like options. For WindowsForum readers planning deployments, the practical next steps are straightforward: run a constrained PoC, involve security and cloud governance teams early, and use the Terraform provider to treat BYOC infrastructure like any other reproducible, auditable cloud resource.
Source: Thailand Business News Zilliz Cloud Brings BYOC to Azure, Extending Availability Across Major Cloud Platforms - Thailand Business News