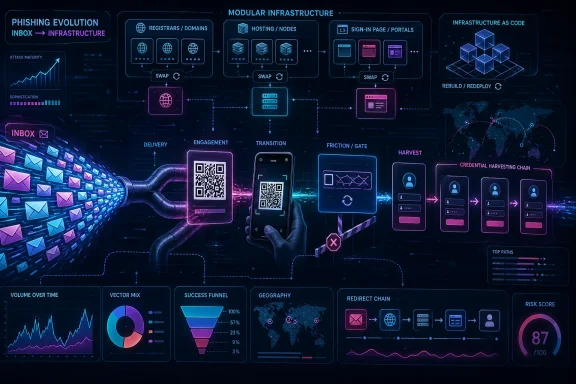
Microsoft said on April 30, 2026, that its threat intelligence teams detected about 8.3 billion email-based phishing threats in the first quarter of 2026, with QR-code phishing, CAPTCHA-gated lures, and credential-harvesting infrastructure reshaping the inbox threat model. The headline number is enormous, but the more important story is not volume. It is that attackers are moving the decisive part of the attack out of the email itself and into infrastructure that can be swapped, screened, redirected, and rebuilt. The modern phishing email is increasingly just a delivery receipt for a much larger criminal service economy.
For years, email security has been described as a fight over attachments, macros, executables, and suspicious links. That framing is now too small. Microsoft’s Q1 2026 telemetry shows a market that is still flooding inboxes at industrial scale, but the center of gravity has shifted toward hosted credential theft and evasive web infrastructure.
The figures tell the story. Microsoft observed roughly 2.9 billion email-based phishing threats in January, 2.8 billion in February, and 2.6 billion in March. That slight decline in monthly volume might tempt a casual reader into thinking the threat cooled. It did not. Under the surface, the delivery mechanics became more agile.
Link-based attacks accounted for 78 percent of email threats across the quarter. Malicious payloads were more prominent in January, when they represented 19 percent of attacks during large HTML and ZIP campaigns, but then settled at 13 percent in both February and March. In other words, the attacker’s favorite payload became less a file and more a path: click here, scan this, pass this check, land there, surrender credentials.
That matters because security teams are good at thinking in artifacts. They can hash files, detonate attachments, strip macros, sandbox payloads, and block known malicious domains. But the Q1 phishing pattern is less artifact-centric and more workflow-centric. The malicious object is no longer always the attachment; sometimes it is the sequence of interactions that follows.
Microsoft’s data also reinforces a grim truth for defenders: credential theft remains the backbone of email crime because identity remains the softest route into the enterprise. Traditional malware delivery fell to just 5–6 percent of payloads by the end of the quarter. The criminal economy is telling us, again, that stolen credentials, session cookies, and user interaction are often more valuable than getting code to execute on a machine.
That phrase, “non-phishing-resistant MFA,” should make every IT administrator wince. It is the gap between having MFA and having MFA that can withstand modern proxy-based credential theft. SMS codes, push prompts, and one-time passwords raised the floor against basic password spraying. They did not end the game.
Tycoon2FA is notable not because it invented these ideas, but because it productized them. Microsoft’s earlier reporting on Tycoon2FA described a subscription-style ecosystem with evasion features such as browser fingerprinting, anti-bot checks, obfuscation, decoy pages, and CAPTCHA screens. That is not a lone operator with a clever lure. It is a criminal SaaS stack.
Q1 2026 showed both the power and fragility of that stack. January Tycoon2FA volumes were down 54 percent from December 2025, a decline Microsoft says may have reflected both seasonal effects and disruption of RedVDS, a service used by many Tycoon2FA customers. In February, attacks pointing to Tycoon2FA surged 44 percent. Then came March.
In early March, Microsoft’s Digital Crimes Unit, working with Europol and industry partners, moved against Tycoon2FA infrastructure and operations. Microsoft says phishing attacks pointing to Tycoon2FA fell 15 percent in March, with nearly one-third of the month’s total volume concentrated in a three-day period early in the month. After the disruption, daily volumes were lower than historical averages, and targets were less able to reach active phishing pages.
That is the good news. The more complicated news is that disruption did not erase the platform. Tycoon2FA adapted by shifting domain patterns and hosting providers. In January and February, Microsoft saw Tycoon2FA domains moving toward newer generic top-level domains such as .DIGITAL, .BUSINESS, .CONTRACTORS, .CEO, and .COMPANY. After the March disruption, .RU registrations increased sharply, representing more than 41 percent of Tycoon2FA domains since the last week of March.
The platform also moved away from Cloudflare and scattered domains across alternative hosting services. That is what partial recovery looks like in 2026: not a triumphant return to prior capacity, but a rapid search for replacement infrastructure, registrar tolerance, and anti-analysis cover. The defenders knocked the business off balance. The business looked for new suppliers.
A 15 percent decline after the March action is not cosmetic when the baseline is tens of millions of malicious messages. More important, Microsoft says access to active phishing pages was significantly reduced. In credential phishing, delivery volume is only one metric. If users cannot reach the final harvest page, or if infrastructure churn breaks campaign reliability, the attacker’s conversion rate suffers.
That is why the anti-takedown argument often misses the economics. Criminal platforms depend on predictability. They sell customers the expectation that campaigns will launch, pages will load, credentials will be captured, and stolen access will be monetized. Every forced infrastructure migration increases cost, friction, and uncertainty.
But defenders should not mistake disruption for containment. Tycoon2FA’s domain and hosting changes show the resilience of a service-based criminal model. The people operating the platform do not need to rebuild from first principles; they need to rewire supply chains. The same broader ecosystem that makes cloud services flexible for legitimate businesses makes phishing infrastructure flexible for criminals.
For enterprise IT, the lesson is not “Microsoft took care of it.” The lesson is that centralized disruption can buy time, but organizations still need phishing-resistant authentication, conditional access discipline, post-click detection, and incident response muscle. Law enforcement and vendor action can degrade a platform. They cannot make weak identity controls strong.
The technique is effective because it exploits the seams between systems. An email lands on a managed corporate mailbox, but the QR code invites the user to continue on a personal phone. The company’s email gateway may inspect text and links; the camera app simply sees a code. The user is no longer just clicking through a corporate security stack. They are crossing devices.
PDF attachments dominated QR-code phishing delivery throughout the quarter, rising from 65 percent of QR-code attacks in January to 70 percent in March. DOC and DOCX files containing malicious QR codes grew in raw volume, but their share fell from 31 percent to 24 percent. The more interesting late-quarter signal was direct embedding of QR codes in email bodies, which surged 336 percent in March.
That direct-in-body method was still only 5 percent of total QR-code phishing volume. But small shares can be strategically important. Removing the attachment removes one inspection opportunity and reduces friction for the attacker. The email becomes visually simple: read this, scan that, continue elsewhere.
Defenders have improved QR-code detection since the first major enterprise wave appeared in 2023, and Microsoft has written before about building QR-specific detection capabilities into Defender for Office 365. Attackers are responding as attackers always do: by changing containers, varying file types, and shifting where the scannable object appears. The QR code is not the trick; mobility between trust zones is the trick.
For users, QR-code phishing is particularly dangerous because it feels modern and routine. Restaurants trained everyone to scan codes. Package delivery services trained everyone to scan codes. Office workflows trained employees to move between desktop and phone without thinking much about it. Threat actors did not create that behavior; they merely monetized it.
The numbers are striking. CAPTCHA-gated phishing volumes fell in January and February, down 45 percent and 8 percent respectively, then more than doubled in March to 11.9 million attacks. Microsoft says that was the highest volume observed over the prior year.
The delivery methods rotated quickly. HTML attachments began the year as the most common vehicle for CAPTCHA-gated phishing, making up 37 percent in January, then dropped sharply in February before more than doubling in March. SVG files spiked in February, becoming the month’s most common method, then fell 57 percent in March. PDFs, after months of decline, more than quadrupled in March and retook the top spot. DOC and DOCX files also surged in March, rising 373 percent to account for 15 percent of payloads.
This is what experimentation looks like at scale. Attackers are not merely choosing between file formats; they are testing which combinations of container, lure, gate, redirect, and landing page survive defenses long enough to harvest credentials. A file type that looks dominant one month may be discarded the next if detection catches up or infrastructure changes.
CAPTCHA also has a psychological role. A fake “security check” reassures the victim that the process is legitimate. It makes the user perform a small act of compliance before the real theft begins. That is classic social engineering, updated for a web shaped by bot checks and login interstitials.
The ClickFix variant makes this darker. In those attacks, fake CAPTCHA or verification pages trick users into copying and executing malicious commands under the guise of proving they are human. The user is not just fooled into entering credentials; they can be recruited into launching the attack chain against themselves.
Banal works. Most employees are not fooled by outlandish stories; they are worn down by routine. A 401K update during a busy day, a payment notice near month-end, a voicemail notification between meetings — these are not cinematic hacker plots. They are office noise sharpened into a weapon.
The attached SVG files were named to match the message theme, and the filenames included Base64-encoded versions of recipient email addresses. When opened, the SVG launched locally in the browser and fetched content from attacker-controlled hostnames. Users saw a fake security CAPTCHA, then a fraudulent sign-in page designed to steal credentials.
The fake confidentiality disclaimer in many messages is particularly telling. It served two purposes: it made the email look like corporate boilerplate, and it gave recipients a reason not to overthink why they received it. A disclaimer that supposedly protects privacy becomes a tool for lowering suspicion.
SVG is attractive because it sits in an awkward category. It is an image format, but it can contain active content and link out to external resources. Security teams that treat it as a harmless graphic can miss how useful it is as a redirector and staging object. Again, the payload is less a file than a process.
That dominance matters more than any single file type. HTML, PDF, ZIP, GZIP, and SVG all moved sharply during the quarter, but their shared purpose was increasingly the same: get the user into a credential-harvesting flow. Malware delivery remained present, but it was no longer the main act in this dataset.
HTML attachments started the quarter as the leading file type, representing 37 percent of payloads in January. They then fell to an annual low in February before nearly tripling in March. Microsoft ties the volatility to large campaigns, including concentrated activity in the first half of January and the third week of March.
PDFs followed a steadier path, increasing 38 percent in February and another 50 percent in March to reach their highest monthly volume in more than a year. By March, PDFs represented 29 percent of payloads, up from 19 percent in January. That should not surprise anyone who has watched business workflows: PDFs remain the lingua franca of invoices, statements, notices, forms, and “secure documents.”
ZIP and GZIP attachments were more erratic, nearly doubling in January, dropping in February, and then surging again in March. Microsoft notes that attackers commonly use ZIP files to circumvent Mark of the Web protections. The persistence of compressed files is a reminder that old tricks do not disappear simply because newer tricks become fashionable.
The March 17 HTML campaign shows how coordinated this has become. Microsoft observed more than 1.5 million confirmed malicious messages sent to over 179,000 organizations across 43 countries. The campaign accounted for about 7 percent of all malicious HTML attachments Microsoft saw in March.
The messages used little or no body content. Their subject lines impersonated ordinary business workflows: ACH notices, EFT updates, wire transfers, invoice statements, e-signature requests, and document delivery prompts. Sender usernames were comically long, stuffed with keywords, tracking strings, service references, and URL-like fragments designed to resemble transactional systems.
When opened, the HTML attachment launched locally and redirected users to an external staging page. That page performed basic screening and sent them onward to a secondary landing page with the phishing content. A CAPTCHA challenge appeared before the fraudulent sign-in page. The campaign’s final phishing endpoints were tied not just to Tycoon2FA, but also to Kratos, formerly Sneaky2FA, and EvilTokens infrastructure.
That multi-platform detail is crucial. It suggests common tooling and delivery behavior can feed multiple phishing-as-a-service back ends. The criminal market is modular. One actor, tool, or service can handle mail distribution, while several other platforms host the final theft experience.
BEC is often less glamorous than adversary-in-the-middle phishing, but it remains one of the most financially consequential forms of email crime. Microsoft defines BEC as a text-based attack targeting enterprise users, impersonating a trusted entity to persuade the recipient to initiate a fraudulent financial transaction or send sensitive documents. The key word is “text-based.” Sometimes the payload is simply persuasion.
The composition of BEC attacks was remarkably stable. Generic outreach messages such as “Are you at your desk?” accounted for 82–84 percent of initial contact emails each month. Explicit requests for specific financial transactions or documents represented only 9–10 percent.
That distribution is the whole strategy. BEC operators do not usually open with the wire fraud. They begin with a conversational hook, then escalate once a human has responded. Replying is the first compromise because it confirms attention, context, and a live target.
Within the smaller category of explicit financial requests, Microsoft saw seasonal motion. Payroll update requests rose 15 percent in February, reaching their highest level in eight months, plausibly reflecting tax-season social engineering. Gift card requests fell sharply in February before rebounding in March, though they remained less than 3 percent of overall BEC messages.
The lesson for defenders is uncomfortable: not every meaningful email threat can be solved by scanning files and links. A message asking whether someone is available may contain no malicious URL, no attachment, no malware, and no obvious technical indicator. It is malicious because of intent and context, which are harder to automate.
Adversary-in-the-middle phishing is designed to sit between the user and the legitimate service. The victim thinks they are signing into Microsoft 365, Outlook, SharePoint, Gmail, or another familiar platform. The attacker relays the interaction, captures credentials, and may steal session tokens or cookies. If the MFA method can be proxied or tricked, the attacker can still win.
That does not mean ordinary MFA is useless. It remains far better than passwords alone, and it stops many attacks. But in high-risk roles and mature environments, the standard has moved. Phishing-resistant MFA — such as passkeys, FIDO2 security keys, and certificate-based approaches when properly implemented — is becoming the baseline for serious identity defense.
Device code phishing is another signal worth watching. Microsoft says Defender Research saw early indications of emerging techniques such as device code phishing, sometimes enabled by offerings like EvilTokens. These attacks abuse legitimate device authorization flows, persuading users to enter codes that grant attackers access. They are not yet at the scale of QR-code or CAPTCHA trends in Microsoft’s Q1 data, but they fit the same pattern: attackers target authentication workflows rather than endpoints alone.
The problem is not merely that users can be tricked. It is that many authentication systems still assume the user’s browser session is a reliable expression of intent. Modern phishing platforms are built to counterfeit that intent convincingly.
This is why “train users harder” is not a strategy. User education matters, but the attack surface has moved into protocol design, session handling, access policy, and device trust. A well-trained employee can still be caught by a convincing AiTM flow during a chaotic workday. A phishing-resistant authentication architecture reduces the blast radius when attention fails.
That is uncomfortable because it crosses organizational boundaries. Email security teams watch mail flow. Identity teams watch sign-ins. Endpoint teams watch devices. Network teams watch connections. Attackers, naturally, do not respect these divisions.
The March HTML campaign illustrates the problem. A sparse email with an HTML attachment led to a local browser launch, then an external staging page, then screening, then a secondary landing page, then CAPTCHA, then a credential page. If each security control sees only one slice, the campaign may appear ambiguous until credentials are already gone.
The same is true for QR-code phishing. The corporate email system may see a PDF with an embedded image. The user’s phone sees a scannable code. The identity system sees a login attempt, perhaps from an unusual location or device. No single layer owns the whole story unless telemetry is connected.
That is why Microsoft emphasizes Defender detections across endpoint, Office 365, identity, apps, and XDR. The vendor angle is obvious, but the architectural point is sound. Email attacks are now cross-surface attacks, and defending them with siloed controls gives attackers room to move.
For WindowsForum readers running small businesses, labs, or hybrid Microsoft 365 environments, the practical lesson is not that everyone needs the most expensive stack tomorrow. It is that email security cannot end at the gateway. Safe Links, attachment detonation, anti-phishing policies, conditional access, risky sign-in alerts, impossible travel logic, token revocation, and user reporting all matter because the attack unfolds in stages.
Tycoon2FA shifted TLDs and hosting providers after disruption. CAPTCHA-gated phishing rotated from HTML to SVG to PDF and DOC/DOCX. QR-code delivery leaned on PDFs but began pushing directly into email bodies. Malicious payload formats swung sharply from month to month, driven by concentrated campaigns. BEC operators kept their conversational structure stable while adjusting seasonal pretexts.
That combination — stable objectives, flexible delivery — is the signature of a mature criminal market. The goal is still credential theft, fraud, and access. The packaging changes constantly.
There is a tendency in security commentary to chase the newest technique. That is understandable, but it can obscure the operational layer beneath. QR-code phishing matters because it moves the user across devices. CAPTCHA matters because it gates automated analysis and normalizes interaction. SVG matters because it blurs the line between image and active content. PhaaS matters because it packages all of this for buyers.
Taken together, these are not separate curiosities. They are parts of a credential-theft supply chain that is becoming more resilient under pressure.
Source: Microsoft Email threat landscape: Q1 2026 trends and insights | Microsoft Security Blog
 The Inbox Is Becoming a Launchpad, Not the Crime Scene
The Inbox Is Becoming a Launchpad, Not the Crime Scene
For years, email security has been described as a fight over attachments, macros, executables, and suspicious links. That framing is now too small. Microsoft’s Q1 2026 telemetry shows a market that is still flooding inboxes at industrial scale, but the center of gravity has shifted toward hosted credential theft and evasive web infrastructure.The figures tell the story. Microsoft observed roughly 2.9 billion email-based phishing threats in January, 2.8 billion in February, and 2.6 billion in March. That slight decline in monthly volume might tempt a casual reader into thinking the threat cooled. It did not. Under the surface, the delivery mechanics became more agile.
Link-based attacks accounted for 78 percent of email threats across the quarter. Malicious payloads were more prominent in January, when they represented 19 percent of attacks during large HTML and ZIP campaigns, but then settled at 13 percent in both February and March. In other words, the attacker’s favorite payload became less a file and more a path: click here, scan this, pass this check, land there, surrender credentials.
That matters because security teams are good at thinking in artifacts. They can hash files, detonate attachments, strip macros, sandbox payloads, and block known malicious domains. But the Q1 phishing pattern is less artifact-centric and more workflow-centric. The malicious object is no longer always the attachment; sometimes it is the sequence of interactions that follows.
Microsoft’s data also reinforces a grim truth for defenders: credential theft remains the backbone of email crime because identity remains the softest route into the enterprise. Traditional malware delivery fell to just 5–6 percent of payloads by the end of the quarter. The criminal economy is telling us, again, that stolen credentials, session cookies, and user interaction are often more valuable than getting code to execute on a machine.
Tycoon2FA Shows the Platformization of Phishing
The Tycoon2FA story is the most useful lens through which to read the quarter. Microsoft tracks the group behind the phishing-as-a-service platform as Storm-1747, and the platform has been active since August 2023. Its core proposition is blunt: rent infrastructure and phishing kits that impersonate enterprise sign-in pages, then use adversary-in-the-middle techniques to target accounts protected by non-phishing-resistant MFA.That phrase, “non-phishing-resistant MFA,” should make every IT administrator wince. It is the gap between having MFA and having MFA that can withstand modern proxy-based credential theft. SMS codes, push prompts, and one-time passwords raised the floor against basic password spraying. They did not end the game.
Tycoon2FA is notable not because it invented these ideas, but because it productized them. Microsoft’s earlier reporting on Tycoon2FA described a subscription-style ecosystem with evasion features such as browser fingerprinting, anti-bot checks, obfuscation, decoy pages, and CAPTCHA screens. That is not a lone operator with a clever lure. It is a criminal SaaS stack.
Q1 2026 showed both the power and fragility of that stack. January Tycoon2FA volumes were down 54 percent from December 2025, a decline Microsoft says may have reflected both seasonal effects and disruption of RedVDS, a service used by many Tycoon2FA customers. In February, attacks pointing to Tycoon2FA surged 44 percent. Then came March.
In early March, Microsoft’s Digital Crimes Unit, working with Europol and industry partners, moved against Tycoon2FA infrastructure and operations. Microsoft says phishing attacks pointing to Tycoon2FA fell 15 percent in March, with nearly one-third of the month’s total volume concentrated in a three-day period early in the month. After the disruption, daily volumes were lower than historical averages, and targets were less able to reach active phishing pages.
That is the good news. The more complicated news is that disruption did not erase the platform. Tycoon2FA adapted by shifting domain patterns and hosting providers. In January and February, Microsoft saw Tycoon2FA domains moving toward newer generic top-level domains such as .DIGITAL, .BUSINESS, .CONTRACTORS, .CEO, and .COMPANY. After the March disruption, .RU registrations increased sharply, representing more than 41 percent of Tycoon2FA domains since the last week of March.
The platform also moved away from Cloudflare and scattered domains across alternative hosting services. That is what partial recovery looks like in 2026: not a triumphant return to prior capacity, but a rapid search for replacement infrastructure, registrar tolerance, and anti-analysis cover. The defenders knocked the business off balance. The business looked for new suppliers.
Disruption Works, But It Does Not Mean Victory
There is a fashionable cynicism in cybersecurity that takedowns are pointless because the criminals always come back. Q1’s Tycoon2FA data argues for a more serious position. Disruption is not victory, but it can be operationally meaningful.A 15 percent decline after the March action is not cosmetic when the baseline is tens of millions of malicious messages. More important, Microsoft says access to active phishing pages was significantly reduced. In credential phishing, delivery volume is only one metric. If users cannot reach the final harvest page, or if infrastructure churn breaks campaign reliability, the attacker’s conversion rate suffers.
That is why the anti-takedown argument often misses the economics. Criminal platforms depend on predictability. They sell customers the expectation that campaigns will launch, pages will load, credentials will be captured, and stolen access will be monetized. Every forced infrastructure migration increases cost, friction, and uncertainty.
But defenders should not mistake disruption for containment. Tycoon2FA’s domain and hosting changes show the resilience of a service-based criminal model. The people operating the platform do not need to rebuild from first principles; they need to rewire supply chains. The same broader ecosystem that makes cloud services flexible for legitimate businesses makes phishing infrastructure flexible for criminals.
For enterprise IT, the lesson is not “Microsoft took care of it.” The lesson is that centralized disruption can buy time, but organizations still need phishing-resistant authentication, conditional access discipline, post-click detection, and incident response muscle. Law enforcement and vendor action can degrade a platform. They cannot make weak identity controls strong.
QR Codes Are No Longer a Gimmick
QR-code phishing has spent the last few years moving from novelty to normal. Microsoft’s Q1 data suggests it has crossed another threshold. QR-code phishing attacks rose from 7.6 million in January to 18.7 million in March, a 146 percent increase over the quarter.The technique is effective because it exploits the seams between systems. An email lands on a managed corporate mailbox, but the QR code invites the user to continue on a personal phone. The company’s email gateway may inspect text and links; the camera app simply sees a code. The user is no longer just clicking through a corporate security stack. They are crossing devices.
PDF attachments dominated QR-code phishing delivery throughout the quarter, rising from 65 percent of QR-code attacks in January to 70 percent in March. DOC and DOCX files containing malicious QR codes grew in raw volume, but their share fell from 31 percent to 24 percent. The more interesting late-quarter signal was direct embedding of QR codes in email bodies, which surged 336 percent in March.
That direct-in-body method was still only 5 percent of total QR-code phishing volume. But small shares can be strategically important. Removing the attachment removes one inspection opportunity and reduces friction for the attacker. The email becomes visually simple: read this, scan that, continue elsewhere.
Defenders have improved QR-code detection since the first major enterprise wave appeared in 2023, and Microsoft has written before about building QR-specific detection capabilities into Defender for Office 365. Attackers are responding as attackers always do: by changing containers, varying file types, and shifting where the scannable object appears. The QR code is not the trick; mobility between trust zones is the trick.
For users, QR-code phishing is particularly dangerous because it feels modern and routine. Restaurants trained everyone to scan codes. Package delivery services trained everyone to scan codes. Office workflows trained employees to move between desktop and phone without thinking much about it. Threat actors did not create that behavior; they merely monetized it.
CAPTCHA Has Become a Phishing Middleware Layer
CAPTCHA-gated phishing is often described as an evasion tactic, but Microsoft’s Q1 findings show it functioning as something broader: a middleware layer between the email and the payload. It slows automated scanning, creates a thin illusion of legitimacy, and forces user interaction before the phishing page appears.The numbers are striking. CAPTCHA-gated phishing volumes fell in January and February, down 45 percent and 8 percent respectively, then more than doubled in March to 11.9 million attacks. Microsoft says that was the highest volume observed over the prior year.
The delivery methods rotated quickly. HTML attachments began the year as the most common vehicle for CAPTCHA-gated phishing, making up 37 percent in January, then dropped sharply in February before more than doubling in March. SVG files spiked in February, becoming the month’s most common method, then fell 57 percent in March. PDFs, after months of decline, more than quadrupled in March and retook the top spot. DOC and DOCX files also surged in March, rising 373 percent to account for 15 percent of payloads.
This is what experimentation looks like at scale. Attackers are not merely choosing between file formats; they are testing which combinations of container, lure, gate, redirect, and landing page survive defenses long enough to harvest credentials. A file type that looks dominant one month may be discarded the next if detection catches up or infrastructure changes.
CAPTCHA also has a psychological role. A fake “security check” reassures the victim that the process is legitimate. It makes the user perform a small act of compliance before the real theft begins. That is classic social engineering, updated for a web shaped by bot checks and login interstitials.
The ClickFix variant makes this darker. In those attacks, fake CAPTCHA or verification pages trick users into copying and executing malicious commands under the guise of proving they are human. The user is not just fooled into entering credentials; they can be recruited into launching the attack chain against themselves.
The SVG Campaign Was a Warning Shot
Microsoft’s account of the February 23–25 SVG campaign deserves attention because it captures the modern phishing assembly line in miniature. Over three days, attackers sent more than 1.2 million messages to users at more than 53,000 organizations across 23 countries. The lures were banal by design: 401K updates, credit hold warnings, payment questions, overdue invoice requests, and voice message notifications.Banal works. Most employees are not fooled by outlandish stories; they are worn down by routine. A 401K update during a busy day, a payment notice near month-end, a voicemail notification between meetings — these are not cinematic hacker plots. They are office noise sharpened into a weapon.
The attached SVG files were named to match the message theme, and the filenames included Base64-encoded versions of recipient email addresses. When opened, the SVG launched locally in the browser and fetched content from attacker-controlled hostnames. Users saw a fake security CAPTCHA, then a fraudulent sign-in page designed to steal credentials.
The fake confidentiality disclaimer in many messages is particularly telling. It served two purposes: it made the email look like corporate boilerplate, and it gave recipients a reason not to overthink why they received it. A disclaimer that supposedly protects privacy becomes a tool for lowering suspicion.
SVG is attractive because it sits in an awkward category. It is an image format, but it can contain active content and link out to external resources. Security teams that treat it as a harmless graphic can miss how useful it is as a redirector and staging object. Again, the payload is less a file than a process.
HTML, PDFs, and ZIPs Are Campaign Dials Now
The malicious payload landscape in Q1 was dominated by credential phishing. Microsoft says credential phishing grew from 89 percent of payload-based attacks in January to 95 percent in February before settling at 94 percent in March. These payloads either linked users to phishing pages or locally loaded spoofed sign-in screens.That dominance matters more than any single file type. HTML, PDF, ZIP, GZIP, and SVG all moved sharply during the quarter, but their shared purpose was increasingly the same: get the user into a credential-harvesting flow. Malware delivery remained present, but it was no longer the main act in this dataset.
HTML attachments started the quarter as the leading file type, representing 37 percent of payloads in January. They then fell to an annual low in February before nearly tripling in March. Microsoft ties the volatility to large campaigns, including concentrated activity in the first half of January and the third week of March.
PDFs followed a steadier path, increasing 38 percent in February and another 50 percent in March to reach their highest monthly volume in more than a year. By March, PDFs represented 29 percent of payloads, up from 19 percent in January. That should not surprise anyone who has watched business workflows: PDFs remain the lingua franca of invoices, statements, notices, forms, and “secure documents.”
ZIP and GZIP attachments were more erratic, nearly doubling in January, dropping in February, and then surging again in March. Microsoft notes that attackers commonly use ZIP files to circumvent Mark of the Web protections. The persistence of compressed files is a reminder that old tricks do not disappear simply because newer tricks become fashionable.
The March 17 HTML campaign shows how coordinated this has become. Microsoft observed more than 1.5 million confirmed malicious messages sent to over 179,000 organizations across 43 countries. The campaign accounted for about 7 percent of all malicious HTML attachments Microsoft saw in March.
The messages used little or no body content. Their subject lines impersonated ordinary business workflows: ACH notices, EFT updates, wire transfers, invoice statements, e-signature requests, and document delivery prompts. Sender usernames were comically long, stuffed with keywords, tracking strings, service references, and URL-like fragments designed to resemble transactional systems.
When opened, the HTML attachment launched locally and redirected users to an external staging page. That page performed basic screening and sent them onward to a secondary landing page with the phishing content. A CAPTCHA challenge appeared before the fraudulent sign-in page. The campaign’s final phishing endpoints were tied not just to Tycoon2FA, but also to Kratos, formerly Sneaky2FA, and EvilTokens infrastructure.
That multi-platform detail is crucial. It suggests common tooling and delivery behavior can feed multiple phishing-as-a-service back ends. The criminal market is modular. One actor, tool, or service can handle mail distribution, while several other platforms host the final theft experience.
BEC Remains the Low-Tech Profit Center
If QR codes and CAPTCHA pages show the technical evolution of phishing, business email compromise shows why low-tech attacks persist. Microsoft counted roughly 10.7 million BEC attacks in Q1 2026. Volumes rose 24 percent in January, dipped 8 percent in February, then surged 26 percent in March.BEC is often less glamorous than adversary-in-the-middle phishing, but it remains one of the most financially consequential forms of email crime. Microsoft defines BEC as a text-based attack targeting enterprise users, impersonating a trusted entity to persuade the recipient to initiate a fraudulent financial transaction or send sensitive documents. The key word is “text-based.” Sometimes the payload is simply persuasion.
The composition of BEC attacks was remarkably stable. Generic outreach messages such as “Are you at your desk?” accounted for 82–84 percent of initial contact emails each month. Explicit requests for specific financial transactions or documents represented only 9–10 percent.
That distribution is the whole strategy. BEC operators do not usually open with the wire fraud. They begin with a conversational hook, then escalate once a human has responded. Replying is the first compromise because it confirms attention, context, and a live target.
Within the smaller category of explicit financial requests, Microsoft saw seasonal motion. Payroll update requests rose 15 percent in February, reaching their highest level in eight months, plausibly reflecting tax-season social engineering. Gift card requests fell sharply in February before rebounding in March, though they remained less than 3 percent of overall BEC messages.
The lesson for defenders is uncomfortable: not every meaningful email threat can be solved by scanning files and links. A message asking whether someone is available may contain no malicious URL, no attachment, no malware, and no obvious technical indicator. It is malicious because of intent and context, which are harder to automate.
MFA Is Splitting Into Two Classes
The Tycoon2FA and EvilTokens references in Microsoft’s reporting point to a broader identity problem. The enterprise world now has two categories of MFA: MFA that resists phishing and MFA that mainly stops unsophisticated password theft. Attackers know the difference.Adversary-in-the-middle phishing is designed to sit between the user and the legitimate service. The victim thinks they are signing into Microsoft 365, Outlook, SharePoint, Gmail, or another familiar platform. The attacker relays the interaction, captures credentials, and may steal session tokens or cookies. If the MFA method can be proxied or tricked, the attacker can still win.
That does not mean ordinary MFA is useless. It remains far better than passwords alone, and it stops many attacks. But in high-risk roles and mature environments, the standard has moved. Phishing-resistant MFA — such as passkeys, FIDO2 security keys, and certificate-based approaches when properly implemented — is becoming the baseline for serious identity defense.
Device code phishing is another signal worth watching. Microsoft says Defender Research saw early indications of emerging techniques such as device code phishing, sometimes enabled by offerings like EvilTokens. These attacks abuse legitimate device authorization flows, persuading users to enter codes that grant attackers access. They are not yet at the scale of QR-code or CAPTCHA trends in Microsoft’s Q1 data, but they fit the same pattern: attackers target authentication workflows rather than endpoints alone.
The problem is not merely that users can be tricked. It is that many authentication systems still assume the user’s browser session is a reliable expression of intent. Modern phishing platforms are built to counterfeit that intent convincingly.
This is why “train users harder” is not a strategy. User education matters, but the attack surface has moved into protocol design, session handling, access policy, and device trust. A well-trained employee can still be caught by a convincing AiTM flow during a chaotic workday. A phishing-resistant authentication architecture reduces the blast radius when attention fails.
Security Teams Need to Watch the Redirect Chain, Not Just the Message
Microsoft’s Q1 report should push defenders toward a more complete model of email defense. The email is the starting point, but not necessarily where the meaningful evidence lives. The decisive signals may appear in redirects, CAPTCHA interactions, landing page infrastructure, domain registration shifts, hosting changes, and post-click identity telemetry.That is uncomfortable because it crosses organizational boundaries. Email security teams watch mail flow. Identity teams watch sign-ins. Endpoint teams watch devices. Network teams watch connections. Attackers, naturally, do not respect these divisions.
The March HTML campaign illustrates the problem. A sparse email with an HTML attachment led to a local browser launch, then an external staging page, then screening, then a secondary landing page, then CAPTCHA, then a credential page. If each security control sees only one slice, the campaign may appear ambiguous until credentials are already gone.
The same is true for QR-code phishing. The corporate email system may see a PDF with an embedded image. The user’s phone sees a scannable code. The identity system sees a login attempt, perhaps from an unusual location or device. No single layer owns the whole story unless telemetry is connected.
That is why Microsoft emphasizes Defender detections across endpoint, Office 365, identity, apps, and XDR. The vendor angle is obvious, but the architectural point is sound. Email attacks are now cross-surface attacks, and defending them with siloed controls gives attackers room to move.
For WindowsForum readers running small businesses, labs, or hybrid Microsoft 365 environments, the practical lesson is not that everyone needs the most expensive stack tomorrow. It is that email security cannot end at the gateway. Safe Links, attachment detonation, anti-phishing policies, conditional access, risky sign-in alerts, impossible travel logic, token revocation, and user reporting all matter because the attack unfolds in stages.
The Quarter’s Real Message Is Infrastructure Agility
The most important trend in Microsoft’s Q1 data is not QR codes, CAPTCHA, PDFs, or HTML attachments. It is agility. Threat actors moved between file formats, infrastructure providers, domain patterns, and phishing platforms with the confidence of operators managing a service business.Tycoon2FA shifted TLDs and hosting providers after disruption. CAPTCHA-gated phishing rotated from HTML to SVG to PDF and DOC/DOCX. QR-code delivery leaned on PDFs but began pushing directly into email bodies. Malicious payload formats swung sharply from month to month, driven by concentrated campaigns. BEC operators kept their conversational structure stable while adjusting seasonal pretexts.
That combination — stable objectives, flexible delivery — is the signature of a mature criminal market. The goal is still credential theft, fraud, and access. The packaging changes constantly.
There is a tendency in security commentary to chase the newest technique. That is understandable, but it can obscure the operational layer beneath. QR-code phishing matters because it moves the user across devices. CAPTCHA matters because it gates automated analysis and normalizes interaction. SVG matters because it blurs the line between image and active content. PhaaS matters because it packages all of this for buyers.
Taken together, these are not separate curiosities. They are parts of a credential-theft supply chain that is becoming more resilient under pressure.
The Defender’s Inbox Playbook Has to Catch Up to March 2026
The concrete takeaways from Microsoft’s Q1 report are less about panic than prioritization. Security teams cannot block every malicious message before delivery, but they can make campaigns less likely to convert, less likely to persist, and less profitable after a click.- Organizations should treat QR-code phishing as a mainstream email threat, not as an edge case or user-awareness footnote.
- CAPTCHA-gated pages should be investigated as suspicious infrastructure signals, especially when they appear between an email lure and an enterprise sign-in page.
- Phishing-resistant MFA should be prioritized for administrators, finance staff, executives, help desk personnel, and anyone with broad access to sensitive systems.
- PDF, SVG, HTML, ZIP, and DOC/DOCX payloads should be evaluated in terms of campaign behavior and redirect chains, not merely file reputation.
- BEC defenses should include process controls for payment, payroll, gift card, and document requests because many attacks contain no traditional malicious artifact.
- Post-click telemetry, risky sign-in detection, rapid token revocation, and user reporting workflows are now core email security controls.
Source: Microsoft Email threat landscape: Q1 2026 trends and insights | Microsoft Security Blog