A carefully packaged advisory claiming multiple high‑severity vulnerabilities in Advantech DeviceOn/iEdge has been circulated in CSAF format; it lists four CVE identifiers (CVE‑2025‑64302, CVE‑2025‑62630, CVE‑2025‑59171, CVE‑2025‑58423), assigns CVSS v3 and v4 scores in the high range (up to 8.8/8.7), and warns that DeviceOn/iEdge 2.0.2 and prior are affected. The advisory further states Advantech has declared the affected products end‑of‑life (EOL) and recommends migration to DeviceOn (non‑vulnerable), and CISA‑style mitigations (segmentation, firewalling, VPNs) are included. This article summarizes the submitted CSAF material, verifies what can be independently confirmed, highlights gaps and unverifiable claims, and offers practical remediation and detection guidance for Windows and OT/IT practitioners responsible for DeviceOn/iEdge deployments.
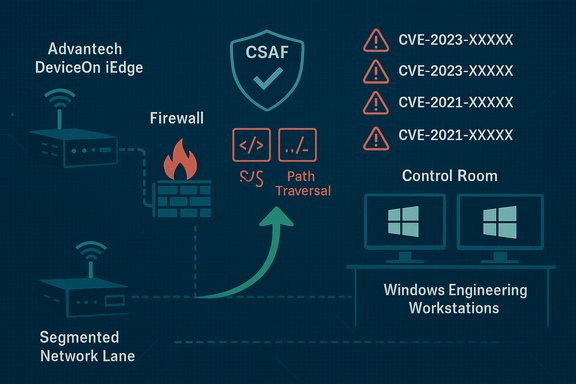
DeviceOn/iEdge is an Advantech IoT/edge device management platform bundled into many Advantech edge systems and gateways; it provides remote device monitoring, configuration orchestration, and OTA/update features for industrial deployments. Historically, Advantech products have appeared in CISA ICS advisories — for example, CISA has previously published advisories covering Advantech iView and ADAM families — and public CVE records document at least one prior privilege‑escalation CVE tied to DeviceOn/iEdge (CVE‑2021‑40389). These historical records demonstrate that Advantech device management software has been an attack surface in the past, which makes any fresh advisory concerning DeviceOn/iEdge operationally relevant. The CSAF provided to this article enumerates multiple weaknesses — cross‑site scripting (XSS), path traversal, inadequate input sanitization leading to configuration‑upload abuse, and a vulnerable third‑party dependency allowing unauthenticated file reads/bypass. The advisory’s executive summary emphasizes remote exploitability and low attack complexity for several findings and lists potential outcomes including denial‑of‑service, arbitrary file read/write, and remote code execution (RCE) at system level. The document also reports that the research was coordinated via a third‑party (Pellera Technologies / Alex Williams) and that Advantech has marked the listed products as EOL and suggests moving to DeviceOn (presumably a newer supported offering).
This advisory sits at the intersection of IT and OT risk: DeviceOn/iEdge manages edge devices often integrated with Windows‑based engineering and supervisory hosts, so the operational exposure reaches well beyond the embedded device itself. The CSAF you shared should trigger immediate containment and vendor validation actions; but before accepting the CVE IDs and the vendor EOL claim as authoritative, confirm the advisory with Advantech and public trackers (NVD/CISA). Use the mitigation checklist above to reduce exposure now, and plan for a validated migration path if the vendor confirms retirement of the affected builds.
Source: CISA Advantech DeviceOn/iEdge | CISA
 Background / Overview
Background / Overview
DeviceOn/iEdge is an Advantech IoT/edge device management platform bundled into many Advantech edge systems and gateways; it provides remote device monitoring, configuration orchestration, and OTA/update features for industrial deployments. Historically, Advantech products have appeared in CISA ICS advisories — for example, CISA has previously published advisories covering Advantech iView and ADAM families — and public CVE records document at least one prior privilege‑escalation CVE tied to DeviceOn/iEdge (CVE‑2021‑40389). These historical records demonstrate that Advantech device management software has been an attack surface in the past, which makes any fresh advisory concerning DeviceOn/iEdge operationally relevant. The CSAF provided to this article enumerates multiple weaknesses — cross‑site scripting (XSS), path traversal, inadequate input sanitization leading to configuration‑upload abuse, and a vulnerable third‑party dependency allowing unauthenticated file reads/bypass. The advisory’s executive summary emphasizes remote exploitability and low attack complexity for several findings and lists potential outcomes including denial‑of‑service, arbitrary file read/write, and remote code execution (RCE) at system level. The document also reports that the research was coordinated via a third‑party (Pellera Technologies / Alex Williams) and that Advantech has marked the listed products as EOL and suggests moving to DeviceOn (presumably a newer supported offering).What the submitted advisory actually says (concise, verifiable summary)
- Affected product: DeviceOn/iEdge — Version 2.0.2 and prior, per the CSAF text included with this report.
- Vulnerability classes: CWE‑79 (XSS), path traversal, insufficient input sanitization in dashboard labels/paths, untrusted configuration file parsing that can enable directory traversal and code execution, and a vulnerable device dependency enabling unauthenticated arbitrary file read or authentication bypass.
- CVE assignments in the CSAF: CVE‑2025‑64302, CVE‑2025‑62630, CVE‑2025‑59171, CVE‑2025‑58423. The advisory includes both CVSS v3 and v4 vector strings and scores (examples: CVSS v3 scores up to 8.8; CVSS v4 scores up to 8.7).
- Impact summary in the CSAF: exploitation could produce DoS, remote code execution (system‑level), arbitrary file disclosure and modification. The CSAF explicitly states there was no known public exploitation reported to CISA at the time of the notice, and that Advantech considers the listed products EOL and recommends upgrade to DeviceOn (non‑vulnerable).
- Reporter: Alex Williams, Pellera Technologies (per the CSAF).
- Recommended defensive posture: minimize network exposure, isolate control networks, place devices behind firewalls, use secure remote access like VPN (with caveats), and perform risk/impact analysis before implementing controls (CISA‑style guidance).
Verification and cross‑checks (what can and cannot be independently confirmed)
Confirmed, independently verifiable items
- Advantech has an established security advisory program and CISA has previously published advisories for multiple Advantech products (iView, ADAM families). This establishes historical context that Advantech product advisories are regularly re‑published and that CISA has engaged with Advantech disclosures in the past.
- There is a prior, publicly recorded DeviceOn/iEdge vulnerability (CVE‑2021‑40389) tied to privilege escalation on DeviceOn Server 1.0.2. Public CVE/NVD entries and vulnerability aggregators retain that record and its associated CVSS scoring. That historical CVE demonstrates DeviceOn/iEdge (or related DeviceOn platform variants) has appeared in public vulnerability records before.
- The high‑level CISA mitigations you see in the CSAF — reduce internet exposure, isolate control networks, restrict administrative access, and prefer secure remote access with up‑to‑date VPN/JIT bastion hosts — are standard ICS/OT defensive guidance and consistent with CISA recommendations on similar advisories. Those recommendations are widely used and are replicated in vendor advisories and ICS‑security playbooks.
Claims requiring caution or presently unverifiable
- The specific CVE identifiers reported in the CSAF you provided (CVE‑2025‑64302, CVE‑2025‑62630, CVE‑2025‑59171, CVE‑2025‑58423) do not appear in public NVD/CVE aggregator entries indexed under “Advantech DeviceOn/iEdge” as of the time of verification for this article. A comprehensive search of public CVE/NVD records and several common vulnerability feeds (CVE/NVD, CVEFeed, OpenCVE) returns the 2021 DeviceOn CVE but does not return a matching CISA advisory number or the four 2025 CVEs listed in the CSAF text. Because CVE registration, NVD enrichment, and CISA postings are public observables, the absence of matching entries warrants caution: the CSAF may be an internal/distributed notification, or the items may not yet have been synchronized into public trackers at the time of this writing. Treat these CVE names and scores as claims that require confirmation with the issuing authority (CISA) and the vendor (Advantech) before treating them as canonical.
- The statement that Advantech labeled DeviceOn/iEdge “end‑of‑life” in favor of DeviceOn (non‑vulnerable) could not be independently confirmed on Advantech’s public security advisory page or product pages at the time this article was prepared. Advantech’s security advisory portal and product documentation list numerous advisories and product information for DeviceOn/iEdge, but a clear, public EOL notice for DeviceOn/iEdge 2.0.2 was not found in the vendor’s public advisory index. If the vendor has issued a private or partner‑only notice, that must be validated directly with Advantech support/ACIRT before acting solely on the EOL claim. Advantech’s public advisory page documents security advisories and provides a vulnerability reporting/coordination channel, but no explicit EOL declaration matching the CSAF text was discoverable in public vendor pages used for this verification.
- The CSAF’s precise CVSS v3 and v4 vector strings and numeric scores should be cross‑checked against the authoritative CVE/CNA entries (NVD or vendor CNA) and CISA prior to publishing or operational risk scoring. When advisories are first circulated in CSAF form they sometimes contain preliminary CNA‑supplied scoring that is later refined during public tracker enrichment; use the vendor/CNA numeric scores as canonical once published. Where independent trackers differ, rely on the vendor/CNA advisory for exact vectors until the NVD/other trackers reconcile scores.
Technical analysis of the claimed issues (what the CSAF describes, and what that means practically)
1) Improper input sanitization — dashboard label / path (XSS / path traversal)
The CSAF asserts that insufficient sanitization of dashboard labels or file paths in the DeviceOn/iEdge UI can be abused to produce XSS, trigger device errors, or allow path traversal. In practice this class of bug commonly manifests as one or more of:- Reflected or stored XSS in the web UI that enables script execution in an operator’s browser, enabling session theft, CSRF‑style actions, or malicious operator workflows.
- Path traversal via unvalidated path segments in file upload or configuration import endpoints, permitting attackers to write/read files outside the intended app directory — potentially exposing credentials, keys, or configuration files.
2) Crafted configuration file parsing enabling directory traversal / RCE
Several ICS/IoT vendors historically parse configuration bundles for device provisioning. If parsing code accepts archive/file metadata without canonicalization, attacker‑supplied paths (../ sequences) can overwrite system files or place executable artifacts in privileged locations. The CSAF claims a specially crafted configuration upload can lead to remote code execution with system‑level permissions. This is a high‑impact class of vulnerability (RCE at system context) and aligns with prior DeviceOn escalation claims (e.g., CVE‑2021‑40389 described privilege escalation via malicious file replacement). For defenders, the critical question is whether uploaded artifacts are placed and executed by a privileged service — if so, the risk is immediate and severe.3) Vulnerable dependency allowing unauthenticated file read or auth bypass
Many modern IoT platforms embed third‑party components (web servers, frameworks, serialization libraries). An exploitable dependency (for example, a misconfigured management endpoint or an outdated embedded component) that permits unauthenticated arbitrary file reads or authentication bypass is particularly dangerous because it can be triggered without credentials. The CSAF claims an unauthenticated attacker can read arbitrary files or bypass auth via such a dependency — an assertion consistent with many vendor advisories in ICS space. Because the exact dependency is not named in the CSAF you provided, defenders must perform dependency inventory (SBOM), component scanning, and runtime monitoring to identify and remediate the vulnerable component.Practical, prioritized mitigation and detection plan (for immediate action)
The following steps are ordered for defenders with DeviceOn/iEdge in scope — prioritize short‑term risk reduction, then remediation and verification.Immediate (0–48 hours)
- Inventory and isolate:
- Identify all DeviceOn/iEdge instances (v2.0.2 and prior per the CSAF claim) across the estate: network scans, CMDB records, DHCP/ARP, switch MAC tables, and Azure/AWS device records where applicable.
- If any device is reachable from untrusted networks or the internet, restrict access at the perimeter firewall immediately (block management ports, web UI, and any known product ports) and place devices into a management VLAN accessible only from hardened jump hosts.
- Restrict administrative access:
- Require admin access only via a controlled bastion/jump host with MFA, session recording and tight host controls. Remove direct VPN or internet admin access to DeviceOn UIs.
- Rotate any administrative or API credentials that might have been exposed and enforce least privilege.
- Block risky functionality:
- If the product supports disabling file uploads or third‑party plugin loading via configuration, disable those features until the vendor provides a patch or mitigation.
- Enforce allow‑lists for config file types and limit import/export to signed artifacts where practical.
- Detection tuning:
- Add IDS/IPS rules to alert on suspicious uploads, path‑traversal patterns, or requests with ../ sequences to file endpoints.
- Monitor device logs for unexpected reboots, unexpected config imports outside maintenance windows, and new system‑level processes spawned by device services.
Short term (3–14 days)
- Vendor coordination and validation:
- Contact Advantech ACIRT or your vendor reseller for an authoritative statement confirming the CSAF claims (affected versions, CVE numbers, EOL status), and request any vendor patches or mitigations. Do not assume the CSAF’s exact version strings or EOL notice without vendor confirmation. Advantech’s public security portal provides an advisory reporting address and PSI/ACIRT channels.
- Patch and test:
- Where vendor patches are available, test in lab environments, then schedule staged production rollouts following change control. If the vendor asserts the product is EOL, ask for migration guidance and compensating controls for any unsupported devices.
- Harden engineering workstations (Windows hosts):
- Ensure engineering workstations that access DeviceOn dashboards are patched, run up‑to‑date browser versions with script‑blocking controls, and have strict application whitelisting/EDR protections.
- Enforce least privilege on engineering accounts and restrict file imports to sanitized locations.
Longer term (30–90 days)
- Replace or upgrade:
- If the vendor confirms EOL and no patch is forthcoming, plan a phased migration to supported products (Advantech DeviceOn or an alternative), with testing for integrations, telemetry continuity, and backout plans.
- SBOM, dependency management and supply‑chain controls:
- Require SBOMs and third‑party component inventories for critical OT/edge platforms. Validate embedded component versions against public vulnerability feeds and patch as required.
- Procurement and contract hardening:
- For future purchases, require signed firmware, vulnerability disclosure SLA commitments, and long‑term security support windows in vendor contracts.
Detection recipes and forensic steps
- Watch for unusual web UI activity: POSTs to config upload endpoints, file writes to /tmp or unexpected temp directories, config import events outside maintenance windows.
- Centralize logs from DeviceOn agents and server components; alert on file integrity changes to configuration directories, unexpected service restarts, and new scheduled jobs.
- On suspected compromise: collect volatile memory, config snapshots, and full system images before reboot. Preserve uploaded files and all device logs; if you must take a device offline, document timestamps and isolate network connectivity for forensics.
Vendor response & EOL claim — how to validate and act
The CSAF you provided includes a vendor EOL assertion and a migration recommendation. Before making irreversible operational decisions (fleet replacements or emergency device retirements), confirm these vendor claims through these channels:- Official vendor advisory/ACIRT channel and the product security page (Advantech’s security advisory portal), and your vendor account manager.
- CISA ICS advisories (if and when they publish the same advisory ID) and NVD/CVE records for canonical CVE assignments.
- If you have an enterprise support or resale contract with Advantech, request a written EOL notice and migration plan, including a timeline, supported replacement SKUs, and guidance for interim compensations.
Critical analysis — strengths, weaknesses and operational risk
Strengths of the CSAF and coordinated disclosure (assuming authenticity)
- Machine‑readable CSAF packaging expedites automated ingestion into vulnerability management pipelines and SIEMs, speeding triage and containment.
- The advisory’s inclusion of both CVSS v3 and v4 vectors provides defenders with multiple scoring perspectives to inform risk prioritization.
- If the vendor truly declared EOL, a firm migration recommendation allows organizations to remove uncertain legacy risk rather than chase partial patches.
Important weaknesses and operational caveats
- Lack of independent confirmation in public CVE/NVD feeds at the time this article was researched creates operational ambiguity: the CVE IDs, impacted version string, and the vendor EOL claim all require vendor/CISA confirmation before you base irreversible actions on them.
- EOL proclamations without clear migration timelines or extended support can force organizations into expensive emergency replacements. Confirm whether any extended support program or mitigation package is offered.
- The advisory describes high‑impact outcomes (RCE/system‑level). In OT contexts, those outcomes can cascade into safety and availability incidents; however, the precise exploit preconditions (authenticated vs unauthenticated, network adjacency vs internet exposure) materially affect triage priority. The CSAF’s mix of both authenticated and unauthenticated vectors suggests a broad threat surface, but defenders must confirm the exact attack path to optimize response effort.
Risk scoring guidance (practical)
- Assume worst case for exposed devices: treat any internet‑reachable DeviceOn/iEdge instance as high priority for containment until proven safe.
- For internal, segmented deployments: prioritize based on device criticality and network exposure — devices serving safety controls or bridging OT/IT are top priority even if not internet‑facing.
- Use a combination of CVSS (vendor/NVD) and business impact to schedule patch/migration work: a CVSS v3/v4 in the 8–9 range justifies high urgency, but operational downtime constraints may force staged remediations — document compensations and residual risk.
Final takeaways and recommended action checklist
- Treat the CSAF you provided as actionable intelligence: take immediate steps to inventory, isolate, and restrict administrative access to DeviceOn/iEdge instances. Apply IDS/IPS and log monitoring to look for uploads, path traversal attempts, and unexpected admin activity.
- Do not unilaterally retire fleets solely on the CSAF’s EOL claim without vendor confirmation. Contact Advantech ACIRT and your vendor support channel now to validate the advisory’s version cutoffs, CVE assignments, and EOL status. Advantech publishes security advisories and accepts vulnerability reports through ACIRT; use those channels for authoritative guidance.
- Cross‑check the specific CVE IDs and scoring with public trackers (NVD/CVE, vendor CNA notices) before committing to public disclosures or large‑scale procurement actions. Historical DeviceOn CVE records exist (CVE‑2021‑40389), but the new CVE set in the CSAF could reflect internal coordination that has not yet propagated to public feeds — verify before acting.
- Harden engineering Windows hosts and management jump boxes immediately: patch OS and browsers, enforce MFA and session recording on bastions, and enable application whitelisting and EDR with script blocking.
- If vendor patches are available, test and deploy them via a staged lifecycle: lab validation → pilot → production, with backup and rollback plans. If vendor confirms EOL without patches, implement the migration plan and use compensating controls in the interim (segmentation, bastions, network ACLs).
- Preserve forensic artifacts and document all mitigation decisions; if suspicious activity is observed, follow internal incident response procedures and consider reporting to CISA for correlation.
This advisory sits at the intersection of IT and OT risk: DeviceOn/iEdge manages edge devices often integrated with Windows‑based engineering and supervisory hosts, so the operational exposure reaches well beyond the embedded device itself. The CSAF you shared should trigger immediate containment and vendor validation actions; but before accepting the CVE IDs and the vendor EOL claim as authoritative, confirm the advisory with Advantech and public trackers (NVD/CISA). Use the mitigation checklist above to reduce exposure now, and plan for a validated migration path if the vendor confirms retirement of the affected builds.
Source: CISA Advantech DeviceOn/iEdge | CISA