On March 31, 2026, one of the JavaScript ecosystem’s most ubiquitous utilities became the center of a supply chain crisis: malicious versions of axios were published to npm and used to deliver a cross-platform remote access trojan to developers and CI environments. The incident matters far beyond a single package because Axios sits deep inside modern web, cloud, and enterprise build pipelines, which means a compromise at this layer can propagate quickly and quietly. By the time defenders had finished triaging, the event had already become a case study in how account takeover, install-time scripts, and dependency trust can combine into a high-impact software supply chain attack.
Axios is a small library with an outsized footprint. It is a JavaScript HTTP client used in browsers, Node.js applications, test harnesses, scripts, and build tooling, so a compromise affects far more than typical front-end code. Microsoft described Axios as a popular HTTP client with more than 70 million weekly downloads, while other reporting placed it even higher, underscoring the scale of its reach across the ecosystem.
The basic trust model of npm is what makes incidents like this so consequential. Developers tend to assume that a package name, a version number, and a familiar maintainer identity mean the release is safe, especially when updates are routine and automated. That assumption is precisely what attackers exploit: they do not need to break every application, only the distribution path that many applications share.
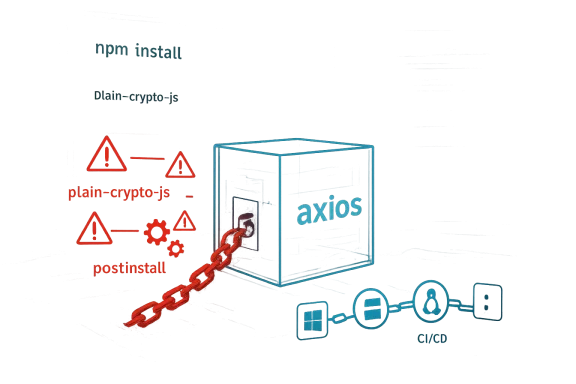
In the Axios case, the malicious code did not need to alter the project’s visible application logic. Instead, the attackers introduced a dependency that existed primarily to trigger an install-time script, allowing the malicious payload to execute during
The timing also matters. The Axios maintainers’ postmortem says the malicious versions were live for about three hours before removal, and Microsoft’s analysis explains that the fake dependency was engineered to pull down a second-stage RAT from attacker infrastructure. A short exposure window does not make the event minor; in supply chain attacks, even brief publication windows can affect thousands of developer endpoints, build agents, and ephemeral CI runs.
This incident landed at a moment when software supply chain security was already under intense scrutiny. Organizations had spent the prior year hardening around lockfiles, dependency scanning, and script suppression, but the Axios compromise showed how quickly a single maintainer account takeover can bypass many of those controls. The result is a reminder that the weakest link is often not the code repository itself, but the release identity and publishing workflow surrounding it.
Microsoft’s description shows that the malicious release path was carefully staged. First came a benign-looking dependency publication, then a follow-up release that added the real install-time logic, and finally the poisoned Axios versions that referenced the dependency. That sequencing suggests premeditation rather than opportunistic abuse, and it also highlights how much patience modern attackers are willing to invest in plausible release histories.
A particularly unsettling feature of the incident is that the attacker did not need to break application code to create harm. The malicious dependency was never meant to be imported by runtime code; it existed to awaken during installation, fetch the payload, and then disappear into normal package-manager noise. In other words, the danger was not in the app’s logic, but in the trust chain around its installation.
Another important point is that the incident exposed a mismatch between how developers perceive package updates and how attackers exploit them. Many teams still think of
The post-install behavior was cross-platform by design. Microsoft’s detections cover artifacts on Windows, macOS, and Linux, reflecting a payload set intended to provide persistence, command execution, or follow-on downloads on all three major developer environments. That is an important escalation from commodity malware that only targets one operating system.
The malware also pursued stealth. Axios’s postmortem says the malicious versions were removed within about three hours, and Microsoft’s analysis shows the threat actors seeded a fake dependency history to make the release appear less suspicious. Short-lived malicious packages are not safer packages; they are often better-packaged attacks.
Axios’s own postmortem adds a human dimension: the compromise began with targeted social engineering against the lead maintainer. That detail reinforces how often supply chain attacks start with people, not code. A maintainer’s desktop can become the gateway to a package registry, and once the publishing channel is hijacked, the attacker inherits the trust of the ecosystem.
There is also an important lesson here for open-source stewardship. Project maintainers are often volunteers or small teams, yet they are expected to defend artifacts that can affect millions of downstream systems. That asymmetry is structural, and it is one reason why more repositories are moving toward stronger publishing workflows, hardware-backed credentials, and immutable release processes.
The danger is not merely that code executes, but that it executes in a trusted automation context. Many organizations run dependency updates automatically, accept lockfile refreshes without human inspection, and cache build artifacts for speed. In that setting, a compromised package can move from test workspace to published artifact with very little friction.
The incident also exposes a deeper tension in modern engineering: the more automated dependency management becomes, the more attractive the automation itself becomes as an attack surface. Security teams have spent years trying to reduce “human in the loop” toil, but supply chain attacks show that removing human friction can also remove a critical point of review. Convenience scales both productivity and risk.
The guidance to disable dependency bots for Axios is equally telling. Tools like Dependabot and Renovate are useful, but in a fast-moving incident they can become a distribution amplifier if teams review dependency PRs too casually. Security teams should not abandon automation, but they should scope and govern it carefully.
Microsoft also advised using
In a mature environment, the best response flow is sequential and explicit. First, identify exposure through package inventory and lockfiles. Second, determine whether the install or update actually ran during the affected window. Third, rotate secrets and inspect egress traffic. Fourth, reinstall cleanly from trusted sources. That sequence matters because it avoids both underreaction and panic.
Microsoft’s reference to trusted publishing is also important because it reflects a broader industry shift. If packages can be published through short-lived, identity-bound workflows rather than stored tokens, then credential theft becomes harder to monetize. The Axios case strengthens the argument that package ecosystems should adopt stronger release attestations and more restrictive publish paths.
Another ecosystem lesson is that maintainers need more support. The compromise began with social engineering and endpoint compromise, which means even a technically excellent maintainer can be outmaneuvered if they lack layered protections. Security at the ecosystem level therefore includes device hardening, phishing resistance, MFA, and better account hygiene for the humans who publish widely used software.
Consumer impact is more indirect but still real. End users may never see Axios by name, yet their apps, browser tools, desktop utilities, or internal SaaS products may depend on it downstream. In that sense, the compromise is a reminder that software risk increasingly reaches consumers through invisible layers of dependency.
The consumer-facing impact is also mostly about trust erosion. When a popular package is turned into malware delivery infrastructure, users start to question whether routine software updates are safe. That skepticism is understandable, but the right answer is stronger software supply chain engineering, not paralysis.
For organizations, the practical takeaway is clear: dependency management must now be treated as a security discipline with inventory, policy, and monitoring. The Axios compromise is a reminder that a version bump can be as sensitive as a code deploy, and sometimes more so. Teams that adjust their governance now will be better positioned for the next attack, which is almost certainly already in motion.
Source: CISA Supply Chain Compromise Impacts Axios Node Package Manager | CISA
 Background
Background
Axios is a small library with an outsized footprint. It is a JavaScript HTTP client used in browsers, Node.js applications, test harnesses, scripts, and build tooling, so a compromise affects far more than typical front-end code. Microsoft described Axios as a popular HTTP client with more than 70 million weekly downloads, while other reporting placed it even higher, underscoring the scale of its reach across the ecosystem.The basic trust model of npm is what makes incidents like this so consequential. Developers tend to assume that a package name, a version number, and a familiar maintainer identity mean the release is safe, especially when updates are routine and automated. That assumption is precisely what attackers exploit: they do not need to break every application, only the distribution path that many applications share.
In the Axios case, the malicious code did not need to alter the project’s visible application logic. Instead, the attackers introduced a dependency that existed primarily to trigger an install-time script, allowing the malicious payload to execute during
npm install or npm update. That design is especially effective because it turns the package manager itself into the delivery mechanism, while the software a developer expected to install may appear functionally normal.The timing also matters. The Axios maintainers’ postmortem says the malicious versions were live for about three hours before removal, and Microsoft’s analysis explains that the fake dependency was engineered to pull down a second-stage RAT from attacker infrastructure. A short exposure window does not make the event minor; in supply chain attacks, even brief publication windows can affect thousands of developer endpoints, build agents, and ephemeral CI runs.
This incident landed at a moment when software supply chain security was already under intense scrutiny. Organizations had spent the prior year hardening around lockfiles, dependency scanning, and script suppression, but the Axios compromise showed how quickly a single maintainer account takeover can bypass many of those controls. The result is a reminder that the weakest link is often not the code repository itself, but the release identity and publishing workflow surrounding it.
Overview
The compromise followed a simple but dangerous pattern: a maintainer account was hijacked, malicious releases were published, and the poisoned packages were distributed through the standard npm mechanism that developers rely on every day. Axios’s own postmortem says the attacker gained access through a targeted social engineering campaign and RAT malware, then used the compromised credentials to publish the malicious versions. That makes the event a classic identity-driven supply chain attack rather than a codebase intrusion in the traditional sense.Why the attack worked
The malicious packages targeted both modern and legacy Axios branches. The attacker published [email protected] and [email protected], which meant environments pinned to either the current major line or an older one could still be affected if they accepted fresh installs. This dual-branch approach is a useful signal for defenders: attackers understand how organizations pin dependencies differently, and they design their releases to maximize reach.Microsoft’s description shows that the malicious release path was carefully staged. First came a benign-looking dependency publication, then a follow-up release that added the real install-time logic, and finally the poisoned Axios versions that referenced the dependency. That sequencing suggests premeditation rather than opportunistic abuse, and it also highlights how much patience modern attackers are willing to invest in plausible release histories.
A particularly unsettling feature of the incident is that the attacker did not need to break application code to create harm. The malicious dependency was never meant to be imported by runtime code; it existed to awaken during installation, fetch the payload, and then disappear into normal package-manager noise. In other words, the danger was not in the app’s logic, but in the trust chain around its installation.
The broader significance
Axios is not the first package to be abused in this way, but it is one of the clearest examples of how trusted publish rights can be weaponized. For defenders, the lesson is not simply “check versions,” but “treat publishing credentials as production-grade assets.” The same applies to build pipelines, because the attack path extends into developer laptops, CI runners, and any environment that automatically installs dependencies.Another important point is that the incident exposed a mismatch between how developers perceive package updates and how attackers exploit them. Many teams still think of
npm install as a routine maintenance task, yet in the wrong moment it can become the execution step for hostile code. That is why the security guidance emphasized exact version pinning, override controls, and script suppression rather than only endpoint detection.How the Malicious Package Worked
Microsoft’s technical writeup explains that the malicious Axios releases injected [email protected], a fake runtime dependency designed to execute automatically through a post-install hook. The key trick was that the package’s visible application behavior did not need to change, because the malicious activity happened during installation rather than at normal runtime. That makes the compromise especially hard to spot during casual code review.Install-time execution as the pivot point
The setup depended onsetup.js, which reconstructed strings and commands at runtime through layered obfuscation. Microsoft noted that the malicious logic triggered when a developer or CI job ran npm install or npm update and the affected package versions were resolved. The attacker effectively turned a package update into an execution event.The post-install behavior was cross-platform by design. Microsoft’s detections cover artifacts on Windows, macOS, and Linux, reflecting a payload set intended to provide persistence, command execution, or follow-on downloads on all three major developer environments. That is an important escalation from commodity malware that only targets one operating system.
The malware also pursued stealth. Axios’s postmortem says the malicious versions were removed within about three hours, and Microsoft’s analysis shows the threat actors seeded a fake dependency history to make the release appear less suspicious. Short-lived malicious packages are not safer packages; they are often better-packaged attacks.
Indicators defenders should care about
The security guidance repeatedly points to a small set of concrete indicators. Those include the malicious Axios versions, the fake dependency, and outbound traffic to attacker infrastructure. The practical takeaway is that incident response teams should look at package metadata, build logs, and egress telemetry together rather than searching only for filesystem residue.- [email protected] and [email protected]
- [email protected]
- Connections to sfrclak[.]com
- Connections to 142.11.206.73 on port 8000
- Install logs showing suspicious
npm installornpm ciactivity - Unexpected
postinstallexecution during dependency resolution
node_modules, they may miss the real compromise path. That is why both Microsoft and the Axios maintainer advised checking lockfiles, pipeline logs, and network logs, not just scanning local package directories.Attribution and Threat Actor Context
Microsoft attributed the infrastructure and the Axios compromise to Sapphire Sleet, a North Korean state actor. Google-linked reporting and subsequent analysis in the security community tied the activity to a North Korea-nexus cluster as well, showing that the attribution picture quickly converged around a well-known supply chain threat ecosystem. That kind of alignment matters because attribution affects how organizations prioritize response, especially when the same infrastructure or tradecraft may appear in future campaigns.Why attribution matters operationally
Attribution is not just a geopolitical label. It can influence whether defenders treat an incident as a one-off account compromise or as part of a broader, repeatable campaign with familiar tooling, infrastructure, and victimology. In this case, Microsoft’s writeup explicitly describes second-stage delivery, remote access tooling, and cross-platform execution patterns that fit a mature intrusion operation rather than random vandalism.Axios’s own postmortem adds a human dimension: the compromise began with targeted social engineering against the lead maintainer. That detail reinforces how often supply chain attacks start with people, not code. A maintainer’s desktop can become the gateway to a package registry, and once the publishing channel is hijacked, the attacker inherits the trust of the ecosystem.
There is also an important lesson here for open-source stewardship. Project maintainers are often volunteers or small teams, yet they are expected to defend artifacts that can affect millions of downstream systems. That asymmetry is structural, and it is one reason why more repositories are moving toward stronger publishing workflows, hardware-backed credentials, and immutable release processes.
What the case reveals about actor capability
The operation showed patience, sequencing, and cross-platform payload delivery. Those are signs of a group that understands the mechanics of software ecosystems and the operational habits of developers. The attack also appears to have been optimized for broad downstream exposure rather than a single target list, which is exactly why security teams across industries paid attention so quickly.Impact on Developers and CI/CD Pipelines
The immediate impact fell on developers, build servers, and CI/CD jobs that performed a fresh install during the exposure window. Microsoft warned that projects using Axios versions above the safe threshold could connect to the malicious infrastructure during installation, and Axios’s maintainer said anyone who ran a fresh install between the relevant UTC times should treat affected systems as compromised. That means the blast radius extends far beyond production servers.Why CI environments are especially exposed
CI systems are attractive targets because they often possess tokens, signing keys, package publish credentials, and access to internal artifacts. A malicious install in that environment can expose more than developer convenience; it can provide attackers with the keys to later stages of the software delivery chain. That is why the incident response guidance emphasizes rotating secrets that may have been injected during affected builds.The danger is not merely that code executes, but that it executes in a trusted automation context. Many organizations run dependency updates automatically, accept lockfile refreshes without human inspection, and cache build artifacts for speed. In that setting, a compromised package can move from test workspace to published artifact with very little friction.
The incident also exposes a deeper tension in modern engineering: the more automated dependency management becomes, the more attractive the automation itself becomes as an attack surface. Security teams have spent years trying to reduce “human in the loop” toil, but supply chain attacks show that removing human friction can also remove a critical point of review. Convenience scales both productivity and risk.
Practical organizational implications
For enterprise defenders, the most important question is not whether Axios was used directly in a project, but whether any automated process could have resolved the malicious versions. A single internal template or base image that refreshed dependencies during the compromise window could spread exposure to dozens of repositories. That is why inventory and dependency graphing matter as much as endpoint forensics.- Audit CI logs for installs and updates during the exposure window
- Rotate secrets used in any runner that resolved the malicious versions
- Review dependency caching behavior across shared pipelines
- Identify transitive Axios usage, not just direct references
- Treat unattended upgrade jobs as high-value attack paths
Microsoft’s Detection and Mitigation Guidance
Microsoft’s blog was notable not only for attribution but for the breadth of mitigation advice. The company recommended rolling back to safe versions, using overrides, cleaning caches, rotating secrets, and disabling post-install scripts where feasible. That breadth reflects a sober recognition that there is no single control that stops every software supply chain attack.Version pinning and override controls
One of Microsoft’s clearest recommendations was to stop Axios from auto-upgrading by using exact version pins rather than caret or tilde ranges. The company also recommended override controls so that transitive dependencies could not silently pull in compromised versions. This is a classic security tradeoff: fewer implicit upgrades means more manual maintenance, but also a smaller attack surface.The guidance to disable dependency bots for Axios is equally telling. Tools like Dependabot and Renovate are useful, but in a fast-moving incident they can become a distribution amplifier if teams review dependency PRs too casually. Security teams should not abandon automation, but they should scope and govern it carefully.
Microsoft also advised using
npm ci --ignore-scripts when possible. That recommendation is important because the attack relied on a post-install hook, which means preventing script execution can blunt a whole class of threats. Of course, not every build system can ignore install scripts, but the guidance highlights a high-value control that many organizations still underuse.Hunting for exposure
Microsoft’s hunting guidance in Defender XDR provides a useful model for response teams. It recommends searching software inventory for the malicious versions and plain-crypto-js, then correlating that data with network telemetry and device activity. That is a practical blueprint for how to connect supply chain indicators to endpoint and identity evidence.In a mature environment, the best response flow is sequential and explicit. First, identify exposure through package inventory and lockfiles. Second, determine whether the install or update actually ran during the affected window. Third, rotate secrets and inspect egress traffic. Fourth, reinstall cleanly from trusted sources. That sequence matters because it avoids both underreaction and panic.
- Pin Axios to a known safe version.
- Remove or override transitive references to compromised versions.
- Search CI logs and developer machines for the malicious package names.
- Treat suspicious installs as potential endpoint compromises.
- Rotate any secrets used on affected systems.
- Rebuild from clean sources rather than trying to “clean” a tainted tree.
What This Means for the npm Ecosystem
The Axios compromise is part of a larger pattern: attackers keep probing the trust assumptions that make package ecosystems work at scale. npm has strong benefits — speed, reuse, collaboration — but those same strengths create cascading risk when a package at the center of many downstream builds is compromised. The lesson is not that npm is broken, but that ecosystem-scale trust needs ecosystem-scale controls.Publishing trust is now a first-class security issue
The Axios maintainer postmortem says the project is moving toward reset devices, immutable release setup, and better adoption of OIDC publishing flows. That is a strong signal that the community increasingly views publishing identity as a security control, not just a convenience feature. In practice, this means fewer long-lived secrets and more verifiable release provenance.Microsoft’s reference to trusted publishing is also important because it reflects a broader industry shift. If packages can be published through short-lived, identity-bound workflows rather than stored tokens, then credential theft becomes harder to monetize. The Axios case strengthens the argument that package ecosystems should adopt stronger release attestations and more restrictive publish paths.
Another ecosystem lesson is that maintainers need more support. The compromise began with social engineering and endpoint compromise, which means even a technically excellent maintainer can be outmaneuvered if they lack layered protections. Security at the ecosystem level therefore includes device hardening, phishing resistance, MFA, and better account hygiene for the humans who publish widely used software.
Downstream trust is the real target
Attackers know that the package itself may be small, but its downstream trust is enormous. A tiny patch release can land in thousands of repositories within hours if dependency automation is configured to accept it. That is why supply chain resilience must include provenance, signing, and policy gates, not just vulnerability scanning after the fact.Enterprise vs. Consumer Impact
For enterprises, the Axios event is primarily a build and identity problem. The real risks are credential exposure, CI runner compromise, package provenance, and cross-team propagation through shared templates and caches. Enterprises should see the incident as a reason to inventory dependency policies, not just to patch a single library.Enterprise consequences
Enterprise security teams may need to review whether their artifact repositories, internal package mirrors, or build caches pulled the malicious versions during the exposure window. If so, the remediation burden may include more than software rollback; it may require credential rotation, pipeline rebuilds, and forensic review of connected systems. That is a much larger operational burden than the average vulnerability patch.Consumer impact is more indirect but still real. End users may never see Axios by name, yet their apps, browser tools, desktop utilities, or internal SaaS products may depend on it downstream. In that sense, the compromise is a reminder that software risk increasingly reaches consumers through invisible layers of dependency.
The consumer-facing impact is also mostly about trust erosion. When a popular package is turned into malware delivery infrastructure, users start to question whether routine software updates are safe. That skepticism is understandable, but the right answer is stronger software supply chain engineering, not paralysis.
A useful distinction
Enterprises can often absorb the cost of rebuilding environments, rotating credentials, and tightening policy. Smaller teams and individual developers may struggle more, especially if they rely on temporary or undocumented build systems. That disparity is one more reason this story resonates beyond large companies: the ecosystem’s weakest operational maturity can become everyone’s problem.Strengths and Opportunities
The Axios incident is serious, but it also exposes opportunities to strengthen the software ecosystem in practical ways. The response from Microsoft and the Axios maintainers shows that organizations can move quickly when they have the right telemetry and publishing controls. The challenge is to convert this episode into durable improvements rather than one-time patching.- Exact version pinning reduces accidental adoption of malicious patch releases.
- OIDC-based trusted publishing reduces reliance on long-lived credentials.
- Post-install script controls can block a major execution path used by attackers.
- Override policies help protect transitive dependencies.
- CI log review can reveal whether the malicious versions were ever resolved.
- Centralized hunting improves blast-radius analysis across endpoints and identities.
- Security advisories help translate a package event into actionable defense steps.
Risks and Concerns
Despite the speedy takedown of the malicious releases, several risks remain. The most obvious is that a brief exposure window can still infect build systems that are recreated often or automatically. Another concern is that package managers and CI platforms vary widely in how they handle scripts, caching, and transitive upgrades, which means one organization’s hardening may leave another one exposed.- Short exposure windows still affect ephemeral builds and auto-scaling runners.
- Credential theft can outlast package removal if secrets are not rotated.
- Install-time scripts remain a dangerous blind spot in many pipelines.
- Transitive dependencies can reintroduce risk after direct remediation.
- Cache contamination may preserve compromised artifacts beyond the release window.
- Maintainer account takeover remains a high-leverage attack path.
- Alert fatigue may cause teams to miss a real package compromise.
Looking Ahead
The next phase of this story is not the removal of the malicious package; it is whether the ecosystem changes its defaults. We should expect more pressure on package registries, more adoption of trusted publishing, and more explicit controls around install scripts and dependency automation. Those changes will not eliminate supply chain attacks, but they can make them harder, noisier, and easier to detect.For organizations, the practical takeaway is clear: dependency management must now be treated as a security discipline with inventory, policy, and monitoring. The Axios compromise is a reminder that a version bump can be as sensitive as a code deploy, and sometimes more so. Teams that adjust their governance now will be better positioned for the next attack, which is almost certainly already in motion.
- Audit package locks and dependency graphs for Axios exposure.
- Enforce exact version pins on critical packages.
- Restrict or disable post-install scripts where possible.
- Adopt trusted publishing and stronger maintainer identity controls.
- Rotate secrets from any build system that may have resolved the malicious versions.
Source: CISA Supply Chain Compromise Impacts Axios Node Package Manager | CISA