A design oversight in Microsoft’s Azure API Management Developer Portal now allows attackers to create accounts on tenants where administrators have visually disabled sign‑up, enabling cross‑tenant account creation and potentially exposing subscription keys and API access unless operators act quickly.
Azure API Management (APIM) is widely used to publish API documentation, onboard developers, and issue subscription keys from a central, managed Developer Portal. The portal supports multiple identity models: Basic authentication (APIM‑managed username/password accounts), delegated sign‑in via Entra ID, Azure AD B2C, or custom identity providers. Microsoft’s documentation and community responses make two points central to this issue: certain backend portal endpoints cannot be removed from the managed Developer Portal, and the vendor explicitly recommends disabling built‑in basic auth in favour of Entra ID for production scenarios.
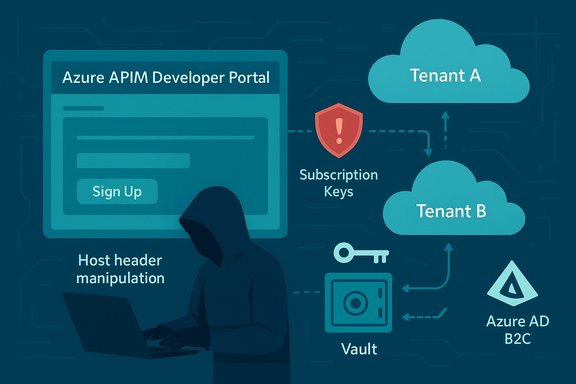
Security researchers and practitioners have demonstrated a practical signup bypass that exploits this combination: UI‑level controls that hide sign‑up can give a false sense of tenant‑level protection while backend registration endpoints remain active and continue to accept requests. When Basic authentication is enabled, attackers can craft or forward those registration requests to create accounts on otherwise protected tenants. The behaviour has been described by vendors and community responders as a management‑plane design limitation rather than a removable feature, which places responsibility on tenant owners to harden configuration and processes.
One caution: third‑party reporting has assigned numeric severity scores (for example a CVSS in the mid‑6s) to this behaviour, but a vendor‑issued CVE or formal NVD entry was not present at the time of those writeups. Treat externally reported numeric scores as third‑party assessments unless or until a formal CVE/advisory is published.
Key signals to monitor:
The pragmatic path for defenders is clear: treat the presence of Basic auth on managed Developer Portals as an emergency misconfiguration. Disable it, audit for unexpected accounts and keys, and apply network and policy controls while planning a move to delegated identity or a self‑hosted portal. Enhance telemetry and hunt for the signals described above to detect abuse early.
Cloud management services sometimes expose mismatches between UI affordances and backend enforcement. This incident is a reminder that UI state is not security policy—the backend is. Operational teams that assume otherwise risk exposure.
Conclusion
For Windows and Azure administrators responsible for APIM, the immediate imperative is to treat Basic authentication on managed Developer Portals as unacceptable for production‑grade APIs. Apply the emergency mitigations, implement the detection playbook, and plan a controlled migration to Entra ID or a self‑hosted Developer Portal. Doing so will close the most practical exploitation path for cross‑tenant account creation and greatly reduce the chance that a cosmetic UI change becomes an operational breach.
Source: Cyber Press https://cyberpress.org/microsoft-azure-api-management-flaw/
 Background / Overview
Background / Overview
Azure API Management (APIM) is widely used to publish API documentation, onboard developers, and issue subscription keys from a central, managed Developer Portal. The portal supports multiple identity models: Basic authentication (APIM‑managed username/password accounts), delegated sign‑in via Entra ID, Azure AD B2C, or custom identity providers. Microsoft’s documentation and community responses make two points central to this issue: certain backend portal endpoints cannot be removed from the managed Developer Portal, and the vendor explicitly recommends disabling built‑in basic auth in favour of Entra ID for production scenarios.Security researchers and practitioners have demonstrated a practical signup bypass that exploits this combination: UI‑level controls that hide sign‑up can give a false sense of tenant‑level protection while backend registration endpoints remain active and continue to accept requests. When Basic authentication is enabled, attackers can craft or forward those registration requests to create accounts on otherwise protected tenants. The behaviour has been described by vendors and community responders as a management‑plane design limitation rather than a removable feature, which places responsibility on tenant owners to harden configuration and processes.
What the flaw is — technical summary
At its core, the issue is an authorization / access‑control gap between the Developer Portal’s user interface and its backend registration APIs:- The “disable sign‑up” UI option removes or hides sign‑up widgets from the portal, but does not remove the underlying registration REST endpoints in the managed portal.
- If Basic authentication is enabled as an identity option, the backend registration endpoint will accept user creation requests even when the UI is configured to hide sign‑up.
- A practical exploit modifies the HTTP request (notably the Host header) of a legitimate sign‑up sequence captured from a permissive portal and forwards it to the target tenant’s portal endpoint; the backend processes the request and creates the account.
Step‑by‑step: how an attacker would exploit the signup bypass
- Find an APIM Developer Portal that permits sign‑up (many partner or public onboarding portals do).
- Register a test account while intercepting the HTTP POST to the portal’s signup endpoint with a proxy (e.g., Burp Suite).
- Modify the captured POST so the Host header and destination point to the APIM tenant where sign‑up is disabled.
- Resend the crafted request; the backend registration endpoint accepts it and creates the account on the target tenant.
- Use the new account to view Developer Portal content, and if product settings permit automatic subscriptions, obtain subscription keys that may grant API access without administrative approval.
Real‑world impact — why this matters to Windows and Azure admins
The practical consequences vary by portal configuration, but the attack surface is significant:- Unauthorized subscription keys: If a product is configured for automatic subscription approval, a newly created account may receive a subscription key that grants access to production APIs. That key can be used to call sensitive endpoints, exfiltrate data, or run billing‑impacting operations.
- Intelligence and tooling exposure: Even without keys, the Developer Portal often contains API documentation, examples, and an interactive test console that reveal endpoints, request formats, and parameters—information that aids attackers in credential stuffing, targeted requests, or social engineering.
- Cross‑tenant reconnaissance and enumeration: The technique allows attackers to target many tenants cheaply by reusing intercepted request templates and altering headers, broadening the blast radius of reconnaissance campaigns.
- False sense of security: Operator reliance on the UI state (“sign‑up disabled”) is misplaced; the backend remains authoritative for requests and must be hardened or eliminated for robust protection.
Verified vendor position — design or bug?
Microsoft’s published Developer Portal documentation explicitly lists certain portal routes and resources that are not removable from the managed portal, including sign‑up related pages and endpoints. The vendor’s recommended mitigation is to move away from Basic username/password accounts, and instead delegate authentication to Entra ID or Azure AD B2C, or to self‑host the Developer Portal when tenants require complete control. Community support posts and product responses confirm there is no native way to wholly remove the registration REST route from the managed portal. This has led many observers to characterise the behaviour as a managed‑service design limitation rather than a classic code bug—meaning customers must apply configuration and process controls to compensate.One caution: third‑party reporting has assigned numeric severity scores (for example a CVSS in the mid‑6s) to this behaviour, but a vendor‑issued CVE or formal NVD entry was not present at the time of those writeups. Treat externally reported numeric scores as third‑party assessments unless or until a formal CVE/advisory is published.
Immediate mitigation checklist (0–24 hours)
These actions should be prioritized for any tenant running the managed Developer Portal:- Disable Basic (username/password) authentication for the Developer Portal immediately. Switch to Entra ID or Azure AD B2C for portal authentication. This is the single most effective immediate mitigation.
- Audit Developer Portal accounts: list all users created since the moment sign‑up was disabled and remove or disable unexpected accounts. Rotate any subscription keys or secrets issued to suspicious accounts.
- Lock down product subscription settings: change product subscription mode from automatic to approval required for any product that yields keys or broad access.
- Rotate secrets: assume subscription key compromise if there is any doubt; rotate keys, regenerate credentials, and force reissue of tokens for impacted resources.
Short and medium‑term hardening (1 day → 3 months)
- Use Azure Policy to enforce identity configuration in IaC templates so Basic auth cannot be enabled in new deployments. Integrate this check into CI/CD gates.
- Where possible, restrict public network access to the Developer Portal and management endpoints. Use private endpoints, VNET integration, or firewall rules to limit the reachable surface.
- Apply request‑level protections: where you can place a WAF or APIM policy in front of registration endpoints, drop or challenge requests with suspicious or altered Host/X‑Forwarded‑Host headers, or require stricter Origin/Referer checks for signup flows. Note: these controls are limited in a managed portal; self‑hosting gives full control.
- Consider self‑hosting the Developer Portal if your security posture requires removal of built‑in signup endpoints or custom endpoint validation. Self‑hosting increases operational overhead but gives full control over which routes exist.
Detection, hunting, and logging playbook
Operational detection should focus on the signup path and subscription issuance signals.Key signals to monitor:
- HTTP POST requests to signup endpoints (paths like /signup, /confirm-v2/identities/basic/signup, /confirm/invitation) observed in Application Insights, WAF logs, or Storage analytics. Flag requests with anomalous or mismatched Host and X‑Forwarded‑Host headers.
- APIM management logs: list of users created in a window, correlated with client IP addresses and creation times. Flag accounts created after the sign‑up UI was disabled.
- Subscription issuance and key usage: newly issued subscription keys or first use of a subscription key coming from unexpected geographies or volumes. Rotate keys where suspicious activity is found.
- WAF and reverse proxy logs showing forwarded requests with Host header manipulation or strange referer values.
- Query APIM user list for accounts created in the last 30 days; sort by creation time and inspect accounts created after sign‑up UI was disabled.
- Search proxy/WAF logs for HTTP POSTs to /signup with Host/X‑Forwarded‑Host header values that do not match the observed client destination.
- Correlate subscription key issuance events with new user creation events; investigate keys issued without an admin approval action.
Operational governance: IaC, policy, and process changes
Security is not just technical controls; it’s governance. Recommended changes:- Enforce policy-as-code to disallow Basic auth enablement in APIM modules; add checks into ARM/Bicep/Terraform templates and CI/CD pipelines.
- Add a mandatory approval workflow for any Product that allows automatic subscription issuance; require a change advisory board or ticket to enable auto‑subscribe.
- Integrate APIM account‑creation events into your SIEM and create an automated playbook that disables suspect accounts and rotates keys when anomalous signups are detected.
- Maintain an inventory of all APIM instances, identity configurations, and whether the Developer Portal is managed or self‑hosted. Treat the self‑hosted option as the default for sensitive APIs that require strict endpoint control.
Strengths and limitations of Microsoft’s position
Strengths:- Microsoft documents the managed portal behaviour and prescribes delegated identity (Entra ID/B2C) and self‑hosting as vendor‑recommended mitigations, which are sensible, well‑understood controls.
- Treating the existence of backend signup endpoints as a design choice rather than an inadvertent vulnerability places heavy burden on customers to protect themselves. For many organisations, especially those running semi‑public developer portals or partner onboarding flows, disabling Basic auth may not be a simple migration path.
- The managed portal’s inability to remove registration routes reduces the parity between UI state and backend enforcement, creating an operational trap for teams that assume UI changes block backend actions.
Risk scenarios and what to prioritise
Prioritise remediation based on exposure and use cases:- Publicly visible developer portals with auto‑approve subscriptions — highest priority. These portals can issue keys to anonymous accounts and should switch to approval or disable Basic auth immediately.
- Partner portals that rely on self‑registration and Basic auth — medium priority. Require partners to federate via Entra ID or use invitation‑based flows.
- Internal portals behind corporate networks — lower immediate urgency but still require auditing to ensure no accidental auto‑subscription or documentation leakage.
Caveats and unverifiable claims
- Some public reports assigned a numeric CVSS score to this behaviour and referenced CVE assignments in third‑party writeups; however, at the time of the assessments cited here a vendor‑issued CVE or authoritative NVD entry was not found. Treat third‑party severity scores as useful heuristics but not definitive evidence until a formal advisory is published.
- Because vendor support responses and documentation may evolve, operational teams should verify current Microsoft guidance in the official product documentation or support channels—especially if planning changes such as migrating to a self‑hosted portal or adjusting identity flows. The managed‑service behaviour described has been documented in community and vendor responses, but cloud services change rapidly.
Practical remediation roadmap (recommended sequence)
- Emergency (hours): Disable Basic auth on all managed Developer Portals; set products to approval required; audit and remove unexpected accounts; rotate exposed keys.
- Short term (days–weeks): Deploy Azure Policy to prevent Basic auth enablement in IaC; add WAF or APIM policy checks where possible; integrate account‑creation alerts into SIEM.
- Medium term (1–3 months): For high‑value APIs, self‑host the Developer Portal or delegate all authentication to Entra ID/B2C; consolidate subscription workflows to require admin approval for broad scopes.
- Long term: Reassess developer onboarding models—favor invitation/sponsored developer flows, enforce least‑privilege product scoping, and instrument continuous detection for API key issuance and abnormal usage.
Final analysis and takeaways
This APIM Developer Portal signup bypass is an operationally significant problem because it combines a persistent backend endpoint, an identity option that allows locally managed accounts (Basic authentication), and common product configurations (automatic subscription approval) into an exploitable pattern. Microsoft’s explicit guidance to avoid Basic auth and to self‑host where tighter controls are required is useful, but many organisations will find migration costly or disruptive.The pragmatic path for defenders is clear: treat the presence of Basic auth on managed Developer Portals as an emergency misconfiguration. Disable it, audit for unexpected accounts and keys, and apply network and policy controls while planning a move to delegated identity or a self‑hosted portal. Enhance telemetry and hunt for the signals described above to detect abuse early.
Cloud management services sometimes expose mismatches between UI affordances and backend enforcement. This incident is a reminder that UI state is not security policy—the backend is. Operational teams that assume otherwise risk exposure.
Conclusion
For Windows and Azure administrators responsible for APIM, the immediate imperative is to treat Basic authentication on managed Developer Portals as unacceptable for production‑grade APIs. Apply the emergency mitigations, implement the detection playbook, and plan a controlled migration to Entra ID or a self‑hosted Developer Portal. Doing so will close the most practical exploitation path for cross‑tenant account creation and greatly reduce the chance that a cosmetic UI change becomes an operational breach.
Source: Cyber Press https://cyberpress.org/microsoft-azure-api-management-flaw/