Azure’s container story is shifting from “you manage the plumbing” to “we manage the plumbing — and the plumbing auto‑scales, auto‑secures, and plugs into AI,” and that shift was on full display in the Azure CTO Mark Russinovich keynote and follow‑ups that outlined what’s next for Azure containers: tighter serverless integration, new runtime sandboxes for untrusted code, radical scaling patterns for bursty workloads, and a continued push to make Kubernetes less of a battlefield and more of a platform for everyday cloud-native developers.
Azure began its life as a PaaS-first cloud: abstract the infrastructure, present a portal and APIs, and let developers deploy code without wrestling servers. Over the past decade that PaaS ethos coexisted with growing IaaS and container ecosystems — virtual machines, Azure Kubernetes Service (AKS), and Infrastructure as Code (IaC) — but the underlying drive toward a serverless Azure continued to shape new services.
The most recent wave of announcements and demos reasserts that serverless vision while bringing containers — traditionally tied to Kubernetes and VMs — closer to the serverless experience. That means:
Key points:
This is not about killing Kubernetes; it’s about extending the cloud developer surface so that Kubernetes is an option when its strengths are needed and invisible when they are not. Expect a landscape where:
Azure’s container future is not a single product, but a layered approach: safer sandboxes for code, faster serverless scale for ephemeral tasks, hardened Kubernetes hosts for production, and application‑level frameworks to tame complexity. The net effect, if realized, will be to let developers concentrate more on code and less on the operational scaffolding. The transition brings opportunities — and integration risks — so measured pilots, rigorous benchmarking, and solid security posture are the best way to turn the keynote demos into dependable production reality.
Source: InfoWorld What’s next for Azure containers?
 Background / Overview
Background / Overview
Azure began its life as a PaaS-first cloud: abstract the infrastructure, present a portal and APIs, and let developers deploy code without wrestling servers. Over the past decade that PaaS ethos coexisted with growing IaaS and container ecosystems — virtual machines, Azure Kubernetes Service (AKS), and Infrastructure as Code (IaC) — but the underlying drive toward a serverless Azure continued to shape new services.The most recent wave of announcements and demos reasserts that serverless vision while bringing containers — traditionally tied to Kubernetes and VMs — closer to the serverless experience. That means:
- fast, ephemeral execution for container workloads (spin up and tear down in seconds),
- managed sandboxes for running untrusted or dynamically generated code safely,
- platform features that let developers treat many containers as a single logical group instead of thousands of individual instances,
- and infrastructure-level improvements (OS and networking) that reduce operational friction for production workloads.
The new serverless primitives: Azure Container Apps dynamic sessions
What changed and why it matters
Azure Container Apps has been Microsoft’s opinionated, serverless platform for microservices and containerized apps. The big platform move since the last Ignite: Dynamic Sessions, a feature that provides short‑lived, highly isolated compute sandboxes you can call via REST to run arbitrary code or custom container images.Key points:
- Python code interpreter and custom container dynamic sessions moved to General Availability on November 19, 2024, while a JavaScript (Node.js) interpreter entered public preview at the same time. These sessions are protected by Hyper‑V isolation.
- Dynamic Sessions are designed to run untrusted code safely — a critical capability when you want to allow customer‑submitted scripts, to execute model‑generated code from an LLM, or to run ephemeral analysis jobs without standing containers.
- Sessions can authenticate via managed identities, pull images from Azure Container Registry, and are automatically cleaned up when they finish to avoid resource leakage.
- It closes a longstanding gap between serverless function platforms (e.g., Functions) and containerized workloads: dynamic sessions give you the flexibility of a container with the operational simplicity and security posture of serverless.
- It enables new AI workflows — for example, Copilot and Advanced Data Analytics features that need to run code generated by models in a safe environment — without forcing developers to build and manage sandboxes themselves.
Technical specifics and limitations to verify
- Isolation: Microsoft documents that Hyper‑V is used for session isolation; this yields strong tenant separation but will have cost and cold‑start tradeoffs compared with mere process isolation. Confirm your threat model and latency tolerance before relying on sessions for tight‑latency paths.
- Runtime support: Python and custom containers are GA; JavaScript (Node.js) was announced in public preview on the same day. If your app depends on specific language runtimes or binary dependencies, the custom container path is the reliable route.
- Lifecycle: Sessions are ephemeral by design; long‑running processes should use standard container services or AKS. The session model is best for short computations, LLM code execution, and one‑off tasks.
ACI, standby pools, NGroups and the 10,000‑container demo
What Azure Container Instances (ACI) is becoming
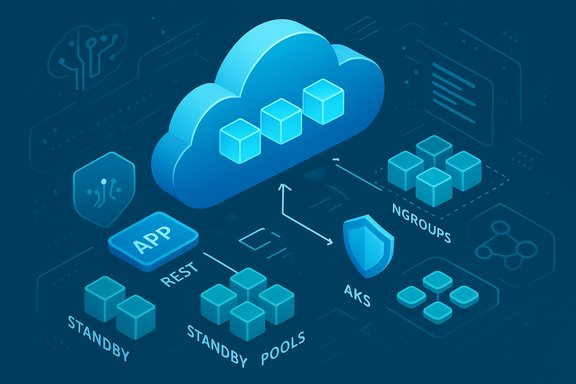
Azure Container Instances (ACI) historically offered a serverless way to run single containers without managing VMs. Recent work shown in the keynote and platform posts pushes ACI toward being a serious serverless orchestration substrate for bursty, high‑scale workloads:- Standby pools / virtual nodes v2: Microsoft demonstrated the concept of pre‑warmed standby pools (virtual nodes) that let Kubernetes launch containers into capacity that is already standing by. This reduces cold‑start time and makes scale‑up almost instantaneous for many workloads.
- NGroups: A new construct that lets you manage collections of containers as a single logical unit — useful for availability zones, policy enforcement, or grouping related microservices. This reduces operational boilerplate when deploying large fleets of containers.
The demo numbers — what to believe, and what to test
Russinovich demoed ACI launching 10,000 containers (pods) in roughly 90 seconds using standby pools and virtual nodes. That number is compelling and has been repeated in several reports and writeups. However, demos show feasibility and engineering progress, not production SLAs:- The 10,000‑pod demo was presented as a capability demonstration; Microsoft and independent coverage confirm the demo but also note that real‑world behavior will vary by region, cluster configuration, networking, and image pull patterns. Treat the demo as directional evidence that ACI can scale rapidly, not as a deployment guarantee without performance verification.
- Customers planning similar bursts should benchmark with representative images and network topologies, and validate image caching, regional capacity, and quotas for their tenancy before relying on this pattern for production traffic.
Use cases where this matters
- unpredictable, viral traffic (campaigns, gaming events),
- large parallel inference jobs where many stateless model servers spawn for short windows,
- CI/CD workloads that need fast, disposable runners,
- event‑driven compute where many small containers run concurrently.
AKS, Azure Linux, and the Kubernetes hygiene story
Making Kubernetes easier to run and maintain
Azure isn’t displacing Kubernetes; it’s making Kubernetes more approachable and production‑grade:- AKS Virtual Node v2 approximates native node behavior so AKS clusters can treat ACI capacity as first‑class nodes. That means better node semantics and easier burst scaling without the cost of running huge node pools 24/7.
- Azure Linux 3.0 is now the modern OS baseline for AKS (available in preview and then GA across AKS versions), bringing an updated kernel (6.6), newer containerd, updated OpenSSL and systemd versions, and better performance and security defaults for container hosts. Microsoft’s AKS and Azure Linux announcements provide migration paths and timelines for adoption. If you operate AKS, you must plan your node OS lifecycle accordingly.
Operational benefits and caveats
- Benefits:
- Fewer surprises when upgrading: AKS’ lifecycle and the Azure Linux support policy provide clear upgrade paths.
- Improved observability and network policy primitives (Cilium growth in AKS and Advanced Container Networking Services) reduce the operational burden of securing and troubleshooting service meshes.
- Caveats:
- Node OS upgrades may require new node pools; preview limitations historically have required nodes to be recreated for major OS jumps.
- Vendors and partner images may have varying support for the new OS; validate CI pipelines and container base images.
Bigger platform moves: Project Radius, Drasi, Fabric integration
Azure’s container roadmap isn’t just about runtime primitives — it’s about tooling and application definitions that let platform engineering teams package apps once and deploy them everywhere.- Project Radius: an incubation effort to create application recipes that declare how an app should be bound to infrastructure and governed across clouds. Radius aims to reduce the friction of porting a cloud‑native app between AKS, ACI, and other target environments — an attempt to restore developer ergonomics to multi‑cloud and hybrid scenarios. Treat Radius as an evolving incubation; it’s promising but not yet a drop‑in replacement for current deployment pipelines.
- Drasi: addresses continuous queries and complex change detection as a declarative engine — a niche but powerful tool for event‑heavy architectures and real‑time telemetry. Both efforts show a willingness to tackle application lifecycle and observability at higher levels of abstraction.
- Fabric and OneLake: Microsoft’s data platform Fabric is increasingly integrated with Azure compute and agentic AI tooling. For containerized applications that rely on data, Fabric’s security model (OneLake security, data agents) and CLI/CI capabilities promise a tighter developer experience between data, AI agents, and runtime services. These are platform signals: containers are only one part of a broader, AI‑driven application stack.
Security, confidentiality, and isolation — a front‑and‑center theme
Microsoft emphasized confidential computing, TEEs (Trusted Execution Environments), and robust isolation for multi‑tenant container workloads.- Dynamic Sessions use Hyper‑V sandboxes specifically to minimize risk when running untrusted code — a practical design choice that trades a little more overhead for much stronger isolation. This model is attractive for managed services that embed user code execution or for running LLM‑generated code safely.
- ACI’s “hostile multitenant safe” design language indicates strong attention to preventing lateral movement between tenants even on shared substrate; however, operational security still requires careful configuration of identity, network policies, and secrets management on every stack. Demos and marketing language should be validated against threat modeling and penetration tests.
Strengths: What’s genuinely promising
- End‑to‑end serverless for containers: Dynamic Sessions + ACI standby pools + NGROUPS point to a coherent strategy where developers can treat containers as code-level primitives without managing the entire orchestration layer.
- AI-native workflows: Container sandboxes tightly coupled with LLMs and Fabric data agents create new, safer paths to run model‑produced code or pipeline transformations.
- Operational simplification: Virtual node v2 and grouping constructs shrink the operational surface area of bursty Kubernetes need‑cases, lowering cost and complexity for many teams.
- Platform alignment: OS lifecycle with Azure Linux 3.0 and AKS versioning shows Microsoft investing in predictable upgrade paths and improved host-level components.
Risks and practical cautions
- Demo vs. production: High‑scale demonstrations (10,000 containers in ~90 seconds) are impressive but must be validated in customer environments. Regional capacity, image pull times, and quota limits can change effective scale dramatically. Always benchmark with your own images and networking.
- Potential lock‑in through higher‑level primitives: Features like Dynamic Sessions and NGROUPS deliver developer velocity but introduce more Azure‑specific idioms. Cross‑cloud portability will rely on emerging standards or tooling layers (e.g., Project Radius aims to help here), but teams should weigh integration speed versus long‑term portability.
- Cost model complexity: Serverless for containers can lower baseline costs but create unpredictable bills under extreme bursts unless governed via quotas, prewarmed pool limits, or other governance tools.
- Security posture expectations: “Hostile multitenant safe” and Hyper‑V isolation are major positives, but they are not a substitute for correct secrets handling, least privilege identity, and robust ingress/egress filtering. Validate assumptions with security testing.
Practical guidance for platform teams and developers
- Start with workload classification:
- Use Dynamic Sessions for ephemeral, short‑lived code runs (LLM‑generated code, untrusted customer scripts, one‑off analyses).
- Use ACI standby pools for bursty, stateless workloads that must launch quickly.
- Use AKS (with Azure Linux 3.0) for stateful, long‑running, complex microservices.
- Benchmark and validate:
- Reproduce scale tests with representative images and network topologies.
- Measure image pull times, registry throughput, and cold‑start latencies.
- Validate that managed identity, Key Vault access, and network policies behave under scale.
- Adopt lifecycle rules:
- Track AKS and Azure Linux support windows and perform orderly node OS migrations. Azure Linux 3.0 is migrating to GA across AKS versions — plan upgrades accordingly.
- Guardrails and cost controls:
- Use quotas, budgets, and automated scaling policies.
- Prewarm standby pools intentionally and set TTLs to avoid runaway costs.
- Audit logs and observability to catch anomalous scale or function usage early.
- Security baseline:
- Enforce managed identity for session pools and containers,
- Use Azure Policy to prevent unsafe resource exposure,
- Pen test dynamic execution paths where you allow end‑user or model‑produced code to run.
The long view: containers as composable serverless primitives
Microsoft’s container roadmap — from Dynamic Sessions to ACI standby pools and NGroups, plus OS modernization and higher‑level application packaging projects like Radius — signals an important architectural thesis: containers should be first‑class development primitives, but developers shouldn’t have to manage the infrastructure complexity those primitives historically required.This is not about killing Kubernetes; it’s about extending the cloud developer surface so that Kubernetes is an option when its strengths are needed and invisible when they are not. Expect a landscape where:
- serverless container sandboxes power AI agents and user‑facing features,
- Kubernetes remains the platform of record for persistent, complex systems,
- platform teams use higher‑level application recipes to define governance and portability,
- and infrastructure improvements (networking offload cards, DPUs, OS updates) continue to buy lower overhead and higher throughput for production workloads.
Azure’s container future is not a single product, but a layered approach: safer sandboxes for code, faster serverless scale for ephemeral tasks, hardened Kubernetes hosts for production, and application‑level frameworks to tame complexity. The net effect, if realized, will be to let developers concentrate more on code and less on the operational scaffolding. The transition brings opportunities — and integration risks — so measured pilots, rigorous benchmarking, and solid security posture are the best way to turn the keynote demos into dependable production reality.
Source: InfoWorld What’s next for Azure containers?