Microsoft’s short MSRC note that “Azure Linux includes this open‑source library and is therefore potentially affected” is factually correct for the Azure Linux images Microsoft has inspected — but it’s an inventory attestation, not a guarantee that no other Microsoft product or image could contain the same vulnerable kernel driver.
CVE-2025-38123 is a kernel-level robustness defect fixed in the Linux net/wwan t7xx driver. The bug is a classic race/invalid-reference issue in the driver’s NAPI RX poll path: while the driver is handling NAPI RX polling, the associated network device can be released by dellink logic triggered by a user-plane disconnect. The polling path can then continue to reference an invalid netdev and process sk_buffs (skb) through net/GRO code, causing a kernel NULL-pointer dereference and a panic. The upstream maintainer patch sequence for the t7xx driver, and the CVE record, both describe the same symptom chain: invalid netdev reference during napi_rx polling, followed by dev_gro_receive / napi_gro_receive oops traces and a host kernel panic.
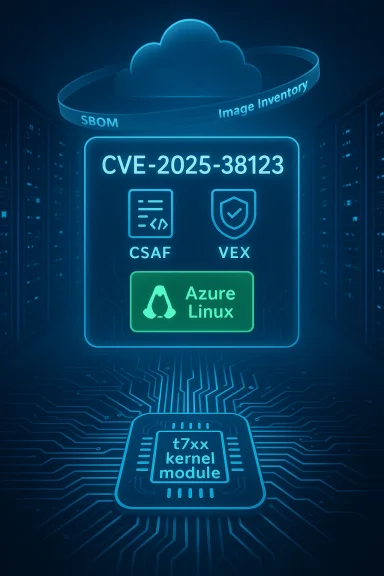
Microsoft’s MSRC advisory for this CVE contains the now-familiar short attestation: it confirms that Azure Linux includes the implicated open-source component and is therefore potentially affected, and it adds that Microsoft began publishing machine‑readable CSAF/VEX attestations and will update the CVE entry if additional Microsoft products are found to ship the same component. That phrasing is important, deliberate, and operationally useful — but it is also narrowly scoped. In practical terms it means:
Why this distinction matters for defenders:
Microsoft’s short line on the CVE page is good news: it tells Azure Linux customers exactly where to act. It is not, however, an all-clear bell for the rest of Microsoft’s artifact portfolio. Operational security means combining vendor attestations with your own artifact discovery, prioritization, and patching discipline — and doing so quickly whenever a kernel-level CVE can trigger host panics or denial-of-service conditions.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / overview
Background / overview
CVE-2025-38123 is a kernel-level robustness defect fixed in the Linux net/wwan t7xx driver. The bug is a classic race/invalid-reference issue in the driver’s NAPI RX poll path: while the driver is handling NAPI RX polling, the associated network device can be released by dellink logic triggered by a user-plane disconnect. The polling path can then continue to reference an invalid netdev and process sk_buffs (skb) through net/GRO code, causing a kernel NULL-pointer dereference and a panic. The upstream maintainer patch sequence for the t7xx driver, and the CVE record, both describe the same symptom chain: invalid netdev reference during napi_rx polling, followed by dev_gro_receive / napi_gro_receive oops traces and a host kernel panic.Microsoft’s MSRC advisory for this CVE contains the now-familiar short attestation: it confirms that Azure Linux includes the implicated open-source component and is therefore potentially affected, and it adds that Microsoft began publishing machine‑readable CSAF/VEX attestations and will update the CVE entry if additional Microsoft products are found to ship the same component. That phrasing is important, deliberate, and operationally useful — but it is also narrowly scoped. In practical terms it means:
- Azure Linux images that Microsoft maintains were inspected and were found to include the upstream t7xx code mapped to CVE-2025-38123. Those images are a confirmed remediation target.
- Microsoft has not said that no other Microsoft product or artifact can include the vulnerable driver; the company has said it will expand attestations as inventory checks complete.
Why the MSRC wording matters — attestation versus exclusivity
Large vendors ship thousands of images, kernels, and appliance artifacts. A single upstream kernel file can appear in many places depending on three concrete, verifiable factors for each image or binary:- The kernel version / commit range used to build the kernel (did the snapshot include the vulnerable commit before the upstream fix?).
- The kernel configuration used when compiling (was the driver compiled in or built as a loadable module for that build?).
- Any local backports or vendor patches that may have either introduced or already corrected the code (is the relevant fix already backported?).
Why this distinction matters for defenders:
- Patch windows should prioritize attested carriers because they are confirmed; but
- Asset owners must verify other Microsoft artifacts in their own estate (via SBOMs, image scanning, kernel inspection) because the same upstream code can appear in unexpected places.
The technical hit list: where this vulnerable code usually lives
The t7xx driver (sometimes referenced by its in-tree driver names such as mtk_t7xx or net/wwan/t7xx) is an in-kernel WWAN driver used for MediaTek/partner modem hardware and similar PCI/USB modems on Linux platforms. It commonly appears in:- Distribution kernel builds (Ubuntu, Fedora/RHEL derivatives, Debian, etc.) as either a built-in driver or a loadable module.
- OEM or appliance kernels (embedded gateways, IoT appliances, router/edge firmware).
- Cloud VM images and marketplace images that include a Linux kernel binary compiled from upstream trees.
- Microsoft-distributed kernel images and appliances (Azure Linux, WSL2 kernel builds, Azure node images) if those builds included the driver and predate the patch or lack the backport.
Short, direct answer to the user’s question
No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable open-source library referenced in CVE-2025-38123. Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include that specific upstream component, and that attestation is authoritative for those Azure Linux images — but it is not an exclusivity guarantee for every Microsoft artifact. Other Microsoft-distributed kernels and images could also include the same driver and be affected until they are inventoried and declared Not Affected or Fixed.What to do right now — prioritized remediation and verification steps
If you are responsible for Linux images, cloud VMs, containers, or Microsoft-distributed artifacts, follow this prioritized checklist. These are practical actions you can run immediately to find, mitigate, and remediate potential exposure to the t7xx/NAPI issue.1) Prioritize Azure Linux images first
- Apply Microsoft’s recommended updates for Azure Linux immediately. Microsoft’s attestation means these images were inspected and are confirmed carriers until patched.
- Schedule reboots as required after kernel updates and confirm kernel versions post-update.
2) Inventory and identify candidate Microsoft artifacts
- Enumerate Microsoft-supplied images you run: Azure Marketplace images, AKS node images, any Microsoft-supplied VM images, WSL2 kernels distributed by Microsoft, Microsoft-published container base images, and appliance images.
- Produce an SBOM or use existing image metadata for each artifact if available.
3) Artifact-level verification (fast checks)
For each Linux image or kernel artifact you suspect, run these checks to detect presence of the t7xx driver:- Check loaded modules on a running system:
- uname -r
- lsmod | grep -i t7xx
- Check whether a t7xx module exists in the kernel modules directory:
- find /lib/modules/$(uname -r) -type f -name 't7xx' -print
- modinfo mtk_t7xx (or try modinfo t7xx) — returns module metadata if present
- Search the kernel config distributed with the image:
- zcat /proc/config.gz | grep -i t7xx || true
- or inspect /boot/config-$(uname -r)
- On package-based systems:
- rpm -q --whatprovides '*/mtk_t7xx.ko' (RHEL/Fedora/Amazon Linux)
- dpkg -S $(modinfo -n mtk_t7xx) (Debian/Ubuntu) — to map module to package
4) Image / offline checks (containers, offline VMs)
- For container images: run a quick container and inspect /lib/modules and /boot in the image, or scan the image filesystem with a simple grep for “t7xx” or the module filename.
- For offline VM images or snapshots, mount the filesystem and inspect /lib/modules and the packaged kernel config.
5) Short-term mitigations while you patch
If you identify an affected artifact but cannot immediately patch, consider these temporary mitigations:- Blacklist the t7xx module so it cannot be loaded:
- Create /etc/modprobe.d/blacklist-t7xx.conf with the line: blacklist mtk_t7xx
- Rebuild initramfs if the module is built into the initramfs or set system policy to prevent loading.
- Enforce strict USB / PCI device policies on hosts where WWAN modems are not expected (disable USB WWAN, block modems via udev rules).
- Isolate workloads that must interact with modems onto patched hosts only.
- If available, apply vendor-provided kernel livepatches or Ksplice-type hotpatches that include the fix — but verify the hotpatch covers the exact commit range.
6) Rollout plan and verification
- Replace or patch kernels with vendor-supplied fixed kernels; reboot into the patched kernel and verify:
- uname -a shows the patched kernel version
- modinfo mtk_t7xx shows the patched module version (if module-based)
- Test known triggers in a controlled environment to ensure the panic no longer reproduces (do not test on production hosts).
Detection and triage: what logs and telemetry to watch
- Kernel oops/panic traces that include call sites like dev_gro_receive, napi_gro_receive, t7xx_ccmni_recv_skb, or function names with t7xx are strong indicators.
- dmesg and system journal entries showing immediate kernel oops stack traces and “BUG: kernel NULL pointer dereference” on hosts with WWAN hardware.
- Unexpected reboots, watchdog resets, or host crashes correlated to WWAN modem detach/connect cycles.
- Telemetry from device-management agents or host-level monitoring showing abrupt kernel crashes in hosts that service modem-attached workloads.
Why Microsoft named Azure Linux first — and the strengths of the VEX/CSAF approach
Microsoft’s decision to start publishing machine-readable CSAF and VEX attestations with Azure Linux follows a pragmatic “crawl, walk, run” approach: pick a product family, inventory it fully, and publish per-CVE attestations that say whether that product is Known Affected, Not Affected, Under Investigation, or Fixed. That provides important benefits:- It reduces false positives for customers: security scanners can consult VEX to avoid noisy alerts for products Microsoft declares Not Affected.
- It gives customers actionable, machine-readable data to prioritize patching.
- The per-product attestation approach makes remediation work concrete and tractable for both vendor and customer.
- Clear, product-scoped guidance for customers who run the named product.
- Machine-readable format enables automation (patch orchestration, vulnerability management).
- Public commitment to expand attestations gives customers a clear roadmap.
- A phased rollout necessarily leaves many artifacts un-attested for some time; these un-attested artifacts remain unverified, not safe.
- Customers who rely solely on vendor attestations without internal artifact scanning can miss exposure in third-party or Microsoft-distributed images that are not yet covered by VEX.
- Large cloud vendors publish many artifacts (marketplace images, node images, appliance kernels) — auditing them all takes time, and attackers can exploit any unpatched artifact in the meantime.
Operational implications for customers and defenders
A practical, risk-focused posture — what to do differently after seeing such an MSRC attestation:- Treat attestations as high-confidence instructions for the listed product. If you run Azure Linux, patch immediately.
- Simultaneously treat other Microsoft artifacts used in your estate as unverified until your own verification or Microsoft’s VEX attestation proves them Not Affected or Fixed.
- Expect the vendor’s attestation program to expand; maintain a workflow that re-checks vendor VEX/CSAF entries and reconciles them against your asset inventory.
- Integrate VEX/CSAF consumption into your automation: vulnerability management tools can consume vendor attestations to reduce false positives and focus remediation where it matters.
Practical detection playbook (quick reference)
- Inventory
- Export list of all Microsoft-supplied images and kernels you run (Marketplace images, AKS nodes, WSL2, Azure Linux VMs, etc.).
- Quick artifact scan (on each suspect image)
- uname -r
- find /lib/modules/$(uname -r) -name 't7xx'
- lsmod | grep -i t7xx
- modinfo mtk_t7xx || modinfo t7xx
- zcat /proc/config.gz | grep -i t7xx
- If module present:
- Identify package owning the module (rpm/dpkg) and update package or kernel.
- If you cannot patch immediately:
- Blacklist module and enforce device policies; isolate affected hosts.
- Post-patch validation:
- Reboot into patched kernel, confirm uname and module metadata, verify crash no longer reproducible in test environment.
Why you should not assume “only Azure Linux”
It’s tempting to interpret Microsoft’s sentence as an exclusivity statement. That would be a mistake for three reasons:- Binary-level divergence: The same upstream source file can be compiled into many different kernel binaries. Whether a product is practically vulnerable depends on the build-time choices described earlier (version, config, backports).
- Product proliferation: Microsoft distributes kernels and images across multiple programs (WSL2, Azure Marketplace images, device kernels for appliances) and also consumes third-party images in Marketplace; any of these could have included the vulnerable driver at build time.
- Time-lag in attestations: Inventorying every artifact is large work. MSRC’s phased VEX rollout means attestations arrive over time; absence of an attestation is simply a gap in the vendor’s inventory process, not a security guarantee.
Risks & trade-offs: vendor transparency vs operational burden
Microsoft’s VEX/CSAF commitment is a net positive for customers: it gives machine-readable, authoritative clarity for at least parts of Microsoft’s portfolio. But the model transfers some burdens to customers:- Customers must continue to run artifact-level inventories (SBOMs, image scans, module checks) to cover the time window between a CVE announcement and the vendor’s VEX coverage for all artifacts.
- Automation that consumes vendor attestations needs to be paired with internal discovery; otherwise you risk a false sense of security.
- Large organizations with hybrid estates (on-prem, Azure, Marketplace images, containers) should assume mixed coverage and prioritize remediation by exposure and criticality.
Final takeaways — a concise action list
- Azure Linux images are a confirmed carrier for CVE-2025-38123: patch those images now.
- Do not assume other Microsoft artifacts are safe; treat them as unverified until Microsoft’s VEX/CSAF attestations or your own scans say Not Affected.
- Run fast artifact-level checks for t7xx presence (lsmod, modinfo, /lib/modules scan, kernel config) across any Microsoft-supplied kernels, Marketplace images, and containers.
- If you find the driver and cannot patch immediately, blacklist the module and lock down device exposure (USB/PCI policies, udev rules, isolate workloads).
- Integrate vendor VEX/CSAF consumption into your vulnerability orchestration, but pair it with internal image and binary discovery — both are necessary.
- Validate patch success by rebooting into the patched kernel and confirming crash traces no longer appear in controlled tests.
Microsoft’s short line on the CVE page is good news: it tells Azure Linux customers exactly where to act. It is not, however, an all-clear bell for the rest of Microsoft’s artifact portfolio. Operational security means combining vendor attestations with your own artifact discovery, prioritization, and patching discipline — and doing so quickly whenever a kernel-level CVE can trigger host panics or denial-of-service conditions.
Source: MSRC Security Update Guide - Microsoft Security Response Center