Microsoft’s brief MSRC note that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑scoped attestation, not proof that Azure Linux is the only Microsoft product that could carry the vulnerable Linux kernel code implicated by CVE‑2025‑37992.
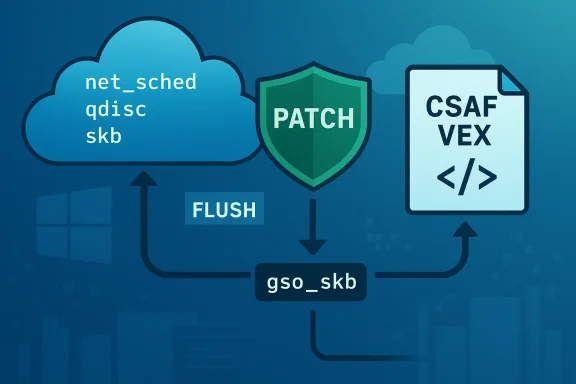
CVE‑2025‑37992 was assigned after an upstream Linux kernel fix that addresses a correctness and robustness problem in the networking queuing discipline (net_sched) code: when reducing a qdisc’s limit via the ->change() operation, the kernel trimmed only the main skb queue while leaving entries in the gso_skb list. That mismatch could lead to a NULL pointer dereference and kernel crash. Upstream maintainers introduced a helper (qdisc_dequeue_internal()) so both the main queue and the gso_skb list are flushed together; patches were applied to common qdiscs including codel, fq, fq_codel, fq_pie, hhf and pie.
The vulnerability’s technical impact is primarily availability (kernel crash / DoS from a NULL dereference) and is categorized as a local‑vector issue: an attacker must have the ability to influence qdisc parameters or enqueue crafted traffic under conditions where qdisc ->change() reduces the limit. Public trackers (NVD‑indexed aggregators, distro advisories and cloud vendor notices) record the fix and map affected kernel trees and distribution kernels.
Microsoft’s MSRC entry for the related CVE wording — the line quoted by many administrators — is deliberate and narrowly scoped: it confirms Microsoft’s inventory check for Azure Linux, and it explains Microsoft’s intent to publish machine‑readable CSAF/VEX attestations and to update CVE mappings if further Microsoft products are found to contain the upstream component. That transparency pledge began with the October 2025 CSAF/VEX rollout.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑37992 was assigned after an upstream Linux kernel fix that addresses a correctness and robustness problem in the networking queuing discipline (net_sched) code: when reducing a qdisc’s limit via the ->change() operation, the kernel trimmed only the main skb queue while leaving entries in the gso_skb list. That mismatch could lead to a NULL pointer dereference and kernel crash. Upstream maintainers introduced a helper (qdisc_dequeue_internal()) so both the main queue and the gso_skb list are flushed together; patches were applied to common qdiscs including codel, fq, fq_codel, fq_pie, hhf and pie.The vulnerability’s technical impact is primarily availability (kernel crash / DoS from a NULL dereference) and is categorized as a local‑vector issue: an attacker must have the ability to influence qdisc parameters or enqueue crafted traffic under conditions where qdisc ->change() reduces the limit. Public trackers (NVD‑indexed aggregators, distro advisories and cloud vendor notices) record the fix and map affected kernel trees and distribution kernels.
Microsoft’s MSRC entry for the related CVE wording — the line quoted by many administrators — is deliberate and narrowly scoped: it confirms Microsoft’s inventory check for Azure Linux, and it explains Microsoft’s intent to publish machine‑readable CSAF/VEX attestations and to update CVE mappings if further Microsoft products are found to contain the upstream component. That transparency pledge began with the October 2025 CSAF/VEX rollout.
Short answer: Is Azure Linux the only Microsoft product that includes the library and is potentially affected?
No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the particular upstream Linux kernel component referenced by the CVE; that means Microsoft has inspected and confirmed Azure Linux images/kernels carry the implicated code. But an attestation is an inventory statement for a specific product, not an exclusivity guarantee. Any Microsoft product, service, kernel image, or binary that ships a Linux kernel build containing the same net_sched code (or the affected qdisc implementations) could also be affected until it is explicitly inventory‑checked and listed by Microsoft. Treat the MSRC statement as authoritative for Azure Linux, but not as proof that other Microsoft artifacts are free of exposure.Why the distinction matters (attestation vs. exclusivity)
Microsoft’s wording follows a pattern increasingly used by vendors to be precise and actionable while avoiding inaccurate over‑claims:- A product‑scoped attestation (e.g., “Azure Linux includes this open‑source library and is therefore potentially affected”) confirms an inventory result for that product. It tells customers: if you run that product, you must take remediation steps.
- It does not by itself assert that Microsoft’s other products (WSL kernels, Azure Marketplace VM images, container base images, device firmware, on‑prem appliances, etc.) do not also include the same upstream code. Thoifferent kernel builds or configurations and are only declared affected if Microsoft’s mapping process finds the same upstream component inside them. This is a practical, operational difference: absence of a mapping ≠ absence of exposure.
Technical context: where this code appears and why Microsoft products could carry it
To assess cross‑product risk, defenders must understand how the vulnerable code travels through the software supply chain:- The vulnerable code lives in upstream Linux kernel sources (net/sched and qdisc implementations). Any downstream kernel build that incorporates those sources — even if rebuilt, backported, or lightly modified — can carry the same vulnerability. Several distro and vendor kernels were patched upstream and then backported into distribution kernels.
- Microsoft’s Azure Linux is a Microsoft‑maintained distro (CBL‑Mariner lineage) used for cloud images and services. If Azure Linux kernels contained the affected net_sched code at the time of the inventory check, MSRC rightly lists Azure Linux as potentially affected. That same kernel code may appear elsewhere inside Microsoft if identical or similar kernel trees are used — for instance:
- WSL2 kernels that Microsoft distributes or recommends.
- Azure Marketplace VM images based on different distros that Microsoft curates or rehosts.
- Container base images or automation tooling that build kernels from identical source trees.
- nels included in Microsoft‑managed appliances.
- Kernel configuration matters: a kernel build that disables certain qdiscs or prunes net_sched functionality may not be vulnerable even if it includes nearby code. Conversely, many default kernels enable the common qdiscs named in the upstream patch.
What the public ecosystem says (independent corroboration)
Multiple independent trackers and vendor advisories align on the technical facts and on remediation guidance:- Distribution and cloud vendor advisories (Ubuntu, Amazon/ALAS, Red Hat, Debian) describe the same root cause and list the affected qdiscs and kernel trees; many published fixed package updates for their respective kernel packages. This shows the vulnerability is not vendor‑exclusive — it’s a kernel defect fixed upstream and then handled by distributors.
- Security aggregators and databases (CVE aggregators, Snyk/Wiz) reflect the same description and the same mitigation (patch upstream/kernel packages), and they track the CVSS/impact as predominantly availability (DoS).
Practical implications for Microsoft customers and admins
If you run Microsoft cloud or client artifacts, take the following approzure Linux systems: apply the kernel updates Microsoft publishes for Azure Linux images and restart or redeploy as directed. Microsoft’s attestation is a direct instruction for Azure Linux operators.- Audit other Microsoft‑supplied Linux kernels and images in your environment:
- Check WSL2 kernel versions and the kernel build configuration used; if you use Microsoft‑supplied WSL kernels derived from Microsoft tooling, validate whether they include the relevant qdisc code.
- For Azure VM images, examine the image publisher and kernel package versions; if an image is based on Azure Linux, it’s in scope. If it’s based on other distros, rely on the distro provider’s advisory and Microsoft’s VEX/CSAF updates.
- For container images and CI pipelines: rebuild base images from patched OS/base images and ensure automated builds pull patched kernel‑dependent packages (if your container workloads use host namespaces or rely on host kernel behavior, focus on host kernel patching).
- For specialized Microsoft appliances or managed services that include Linux kernels, consult the vendor/product bulletins and Microsoft’s VEX outputs — do not assume the inventory for Azure Linux covers those artifacts unless Microsoft explicitly lists them.
Remediation checklist (operational steps)
- Identify: inventory all Microsoft‑provided Linux artifacts running in your estate (Azure Linux VMs, WSL instances, Marketplace images, container hosts, appliance images). Use package/kernel version scanning and SBOMs where available.
- Verify: compare kernel versions and applied patches against the CVE’s affected version ranges reported by distributors. Many distro advisories publish exact fixed package versions you can match.
- Patch: apply vendor‑provided kernel updates or livepatch feeds where available. Reboot or redeploy per vendor guidance to ensure the patched kernel is active.
- Mitigate (short term): where patching is delayed, limit local untrusted workloads, harden container isolation, and restrict who can change network qdisc parameters (only privileged users/processes). The vulnerability is local in vector, so reducing the surface that can trigger qdisc ->change() helps.
- Monitor: watch MSRC’s CVE record and Microsoft’s CSAF/VEX mappings for updates that add other Microsoft products to the attestation list. Microsoft has committed to update the CVE mapping as additional products are identified.
- List all systems running any Microsoft‑supplied Linux artifact.
- Query kernel version and qdisc-related package versions on each host.versions against the vendor/distro advisories.
- Apply updates to Azure Linux first (since MSRC attested it).
- Patch or rebuild container images and CI images.
- Reboot or redeploy where required, and validate via kernel version checks.
- Repeat weekly until your SBOM/VEX mapping shows no outstanding Microsoft artifacts carrying the vulnerable code.
Risk analysis: strengths and limitations of Microsoft’s advisory and VEX/CSAF approach
Strengths- **Clarity for Azure Linux cust naming Azure Linux, Microsoft gives operators a clear remediation priority. That reduces ambiguity for cloud customers running those images.
- CSAF/VEX commitment increases transparency: The move to publish machine‑readable attestations (CSAF/VEX) is a strong, modern supply‑chain practice: it allows automated mapping between CVEs and product inventories, and it provides an auditable trail. Microsoft’s public commitment to update attestations when scope changes is a net positive.
- Upstream fixes are available and widely distributed: Multiple distributions and cloud vendors published patches once upstream changes landed, giving administrators actionable remediation paths.
- Attestation ≠ comprehensive scanning: An attestation for one product only proves Microsoft checked that product. It doesn’t prove absence elsewhere. Administrators who assume “not listed = not affected” risk leaving systems unpatched.
- Downstream divergence complicates mapping: Microsoft and other vendors sometimes ship kernels with backports, vendor changes, and configuration differences. Those variations make automated matching imperfect and require careful version/configuration audits.
- Local‑vector exploits still matter in multi‑tenant clouds: While remote exploitation is unlikely, in cloud or multi‑tenant contexts a local DoS can be impactful if a neighbor or compromised agent can trigger the condition. Treat kernel robustness fixes seriously in places where local code execution boundaries are porous.
How to confirm whether other Microsoft products are affected (detailed verification)
- Use Microsoft’s published CSAF/VEX artifacts as your starting point. Microsoft’s machine‑readable attestations will enumerate product SKUs and build artifacts that Microsoft has inventory‑checked. Monitor those VEX feeds for additions that expand the list beyond Azure Linux.
- For each Microsoft artifact in your environment:
- Extract kernel version and build identifiers.
- If possible, obtain a vendor SBOM for the artifact. SBOM data accelerates component matching.
- Compare against upstream kernel commits and distribution advisories. Distribution advisories list the fixed package versions; if your artifact’s kernel version predates the fix or matches an affected package, it’s in scope.
- If the artifact is proprietary or opaque (for example, a managed appliance), contact Microsoft or the product owner requesting a VEX mapping or clarification. Microsoft’s advisory explicitly says it will update CVE mappings if more products are identified, which creates an escalation path.
Recommended posture for security teams (policy and monitoring)
- Treat vendor attestations as actionable but not exhaustive. Use attestations to prioritize patching but maintain independent inventory and scanning to find artifacts the vendor hasn’t yet attested.
- Automate kernel and package scanning across your estate. Regularly reconcile those scans with upstream advisories and Microsoft’s VEX outputs.
- Maintain an incident playbook for kernel DoS risks: isolate affected hosts, collect kernel oops logs, and roll forward to patched images swiftly.
- For cloud tenants, apply image replacement policies for Azure Marketplace images and enforce least‑privilege for processes that can alter network qdiscs or system network configuration.
Conclusion
Microsoft’s MSRC advisory correctly identifies Azure Linux as a product that includes the implicated upstream Linux kernel component — and Microsoft has committed to publishing CSAF/VEX attestations and to updating CVE mappings if further Microsoft products are found to include the same component. That is valuable and clear guidance for Azure Linux operators. However, the advisory is product‑scoped, not an exclusivity declaration: the underlying vulnerability lives in upstream Linux kernel code and can appear in any downstream Microsoft artifact that ships the same kernel sources and configuration. In short, treat the MSRC statement as an authoritative assertion for Azure Linux and as a prompt to inventory and verify other Microsoft artifacts in your estate. Proactive scanning, patching according to distributor advisories, and monitoring Microsoft’s CSAF/VEX feeds will close the gap between attestation and assurance.Source: MSRC Security Update Guide - Microsoft Security Response Center