Microsoft’s attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is an authoritative, product‑level statement — but it is not a blanket guarantee that no other Microsoft product contains the same open‑source component. Azure Linux (the CBL‑Mariner lineage) is the only Microsoft product Microsoft has publicly inventory‑checked and attested to for CVE‑2024‑29018, yet multiple Microsoft product families and published artifacts are known to ship or depend on the Moby container stack (moby, moby‑engine, moby‑cli, BuildKit, runc and related pieces). Practically, that means Azure Linux customers must treat Microsoft’s attestation as definitive for Azure Linux, while defenders across the Microsoft ecosystem should assume other Microsoft images and runtimes may also be carriers until those artifacts are explicitly inventoried or shown otherwise.
CVE‑2024‑29018 is a DNS handling flaw in the Moby project (the open‑source foundation of Docker Engine). The vulnerability stems from how dockerd handles name resolution for containers attached only to internal networks: instead of preserving the container network namespace and its intended isolation, dockerd can forward DNS lookups to the host loopback, which in some configurations causes lookups to escape to external authoritative nameservers. An attacker who controls a container attached to an internal network could register a domain with authoritative nameservers under their control and exfiltrate arbitrary data by encoding it into DNS queries.
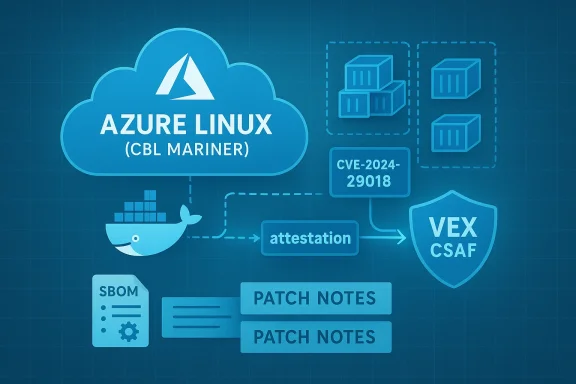
The fix is implemented upstream in Moby releases and in downstream vendor packages. Microsoft’s security advisory for the CVE explicitly states that Azure Linux includes the implicated open‑source library and therefore may be affected. Microsoft also noted it has started publishing machine‑readable VEX/CSAF attestations to clarify which of its products include specific open‑source components — beginning with Azure Linux and expanding over time.
This report explains what Microsoft’s wording does — and does not — mean, catalogues Microsoft product families that are plausibly impacted, lays out detection and mitigation steps, and offers a critical assessment of the practical risks and the transparency program.
Why this matters operationally: Microsoft ships many, distinct artifacts — kernels, appliance images, pre‑baked VM/marketplace images, developer toolkits, and managed service stacks — and whether any particular artifact contains the vulnerable component is an artifact‑level property. Until each artifact is inventoried and attested, defenders should not assume they are unaffected.
CVE‑2024‑29018 is particularly tricky because the insecure behavior is an intentional part of the runtime’s networking plumbing: the daemon’s choice to forward DNS lookups via the host loopback defeats namespace isolation semantics. That design choice is why a simple configuration or packaging fix at the runtime level is an effective mitigation — but it also means many installations that depend on distributed default configuration may remain exposed until patched.
Operationally, defenders should treat the MSRC attestation as a high‑confidence signal for Azure Linux and immediately remediate that product. Simultaneously, organizations must aggressively inventory Microsoft‑supplied artifacts in their estates, apply upstream patches where moby is present, enforce DNS egress controls, and hunt for DNS‑based exfiltration indicators. The vendor’s machine‑readable VEX/CSAF program is a welcome step for supply‑chain transparency, but it must be paired with rapid, broad artifact coverage and explicit messaging so that customers can act decisively across all Microsoft artifacts they rely upon.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑29018 is a DNS handling flaw in the Moby project (the open‑source foundation of Docker Engine). The vulnerability stems from how dockerd handles name resolution for containers attached only to internal networks: instead of preserving the container network namespace and its intended isolation, dockerd can forward DNS lookups to the host loopback, which in some configurations causes lookups to escape to external authoritative nameservers. An attacker who controls a container attached to an internal network could register a domain with authoritative nameservers under their control and exfiltrate arbitrary data by encoding it into DNS queries.The fix is implemented upstream in Moby releases and in downstream vendor packages. Microsoft’s security advisory for the CVE explicitly states that Azure Linux includes the implicated open‑source library and therefore may be affected. Microsoft also noted it has started publishing machine‑readable VEX/CSAF attestations to clarify which of its products include specific open‑source components — beginning with Azure Linux and expanding over time.
This report explains what Microsoft’s wording does — and does not — mean, catalogues Microsoft product families that are plausibly impacted, lays out detection and mitigation steps, and offers a critical assessment of the practical risks and the transparency program.
What Microsoft’s attestation means — and the important limits
Azure Linux: an authoritative product attestation
When Microsoft says “Azure Linux includes this open‑source library,” that is a high‑fidelity, product‑level inventory statement. For customers running Azure Linux images or packages, Microsoft’s attestation is the authoritative signal: treat the product as potentially affected and follow Microsoft’s published remediation guidance for that product.Attestation is not proof of exclusivity
Microsoft’s phrasing is carefully scoped: it is a confirmation that Microsoft inspected Azure Linux artifacts and found the vulnerable upstream software. It is not an engineered proof that every other Microsoft product has been scanned and found clean. Microsoft has committed to update CVE mappings and VEX/CSAF attestations as it inventories additional product lines, which means absence of other Microsoft product names in the advisory is absence of attestation, not a technical guarantee of absence.Why this matters operationally: Microsoft ships many, distinct artifacts — kernels, appliance images, pre‑baked VM/marketplace images, developer toolkits, and managed service stacks — and whether any particular artifact contains the vulnerable component is an artifact‑level property. Until each artifact is inventoried and attested, defenders should not assume they are unaffected.
Which Microsoft products are plausibly affected by Moby / dockerd?
Microsoft’s attestation confirms Azure Linux as a carrier; other Microsoft product families are known to ship or depend on Moby‑derived components and therefore should be considered plausible carriers pending artifact‑level verification:- Azure Linux (CBL‑Mariner) — Microsoft has publicly attested this product contains the Moby packages. Microsoft’s package repositories for this distro include moby packages and downstream security advisories have been released for these packages.
- Azure IoT Edge / EFLOW (IoT Edge for Linux on Windows) — Microsoft publishes and distributes a Moby‑based runtime (moby‑engine) as the supported container engine for Azure IoT Edge and provides EFLOW VM compositions that come pre‑installed with the IoT Edge runtime and moby‑engine. Devices and Windows images using EFLOW therefore may ship a Microsoft‑packaged Moby runtime.
- IoT distributions and validated images — Microsoft provides curated images for IoT and edge scenarios that include moby‑engine as the container runtime for managed edge scenarios (these are often validated and supported by Microsoft).
- Azure Marketplace VM images and partner appliances — Microsoft‑published Marketplace images (some of which are built from Azure Linux or include additional packages) can include moby packaging depending on the image composition.
- Windows Subsystem for Linux (WSL) userlands — while WSL itself is a kernel/service on Windows, WSL distributions are user‑space images that customers can install packages into; a distro published or curated by Microsoft may include Moby packages if they were added to that userland.
- Developer images and tooling that Microsoft distributes — tools that ship prebuilt images or example stacks may include container tooling; these should be inventoried.
- Managed service artifacts — parts of some managed services (for example, VM images or agent bundles used by container‑orchestration or IoT services) may include or depend on Moby binaries or libraries.
How defenders should treat Microsoft’s statement — practical guidance
Treat Microsoft’s Azure Linux attestation as the first, high‑confidence signal for that product, and do the following immediately across your Microsoft footprint:- Inventory: Identify every Microsoft‑supplied image and runtime you run.
- Query package inventories in Azure VM Marketplace images, CBL‑Mariner images, EFLOW/IoT images, and any Microsoft‑maintained appliance images.
- Search for installed packages named moby, moby‑engine, moby‑cli, docker.io, dockerd, or binary names like dockerd or docker‑engine.
- Verify via SBOM/VEX: Request or download the SBOM/VEX/CSAF attestations for each Microsoft product you use where available. Microsoft’s VEX rollout began with Azure Linux and will expand; obtain attestations for other artifacts when published.
- Apply patches: Where moby/moby‑engine is present, update to vendor‑patched versions. Upstream Moby releases that included fixes were minted; apply the patched package versions distributed by your distro or vendor.
- Mitigate network exposure: Until patched, adopt network controls and container configuration workarounds:
- Disallow or tightly control outbound DNS from hosts and containers; enforce egress rules that only permit DNS via trusted resolvers.
- For containers attached to internal networks, set explicit DNS upstream addresses (the runtime accepts --dns configuration) to ensure lookups resolve within the network namespace.
- Consider using network policies, service meshes, or DNS filtering appliances that log and prevent anomalous DNS queries.
- Monitor and hunt: Look for indicators of DNS‑based exfiltration and anomalous DNS behavior:
- Unusual DNS queries with long or semi‑structured labels.
- DNS queries for externally authoritative nameservers for domains controlled by untrusted parties.
- Unexpected DNS egress originating from hosts or containers attached to internal networks.
- Replace runtime where feasible: For controlled environments, prefer containerd (the de facto runtime in many cloud and orchestrated environments) if it meets your operational needs and is supported by the service — but only as a considered migration after verifying compatibility and support.
Detection techniques — concrete actions
Quick detection checks you can run right now:- Process discovery: scan host filesystem and package manager output for dockerd, docker‑engine, moby‑engine, moby‑cli binaries or packages.
- Network observability:
- Log all outgoing DNS traffic from hosts and container bridges; flag DNS queries exiting the expected resolver IP range or resolving to uncommon authoritative names.
- Use flow collectors or host‑level packet captures to identify DNS requests from container bridge interfaces or from loopback addresses that are unexpected.
- Container namespace tracing:
- Inspect container network namespaces to confirm whether upstream DNS queries are being resolved inside the namespace or being proxied to the host loopback.
- Instrument with eBPF tools or namespace‑aware tcpdump to capture where DNS traffic exits.
- Runtime telemetry:
- Enable debug/logging for dockerd if safe to do so (in a controlled environment) and review how it handles DNS lookups for internal networks.
- SIEM hunting:
- Create rules to highlight DNS queries with encoded payload characteristics (e.g., high entropy labels, repeated long‑label patterns).
- Correlate container start events + internal network attachments + outbound DNS anomalies.
Mitigations and remediations — prioritized steps
- Immediate (hours):
- Apply network egress controls that restrict DNS to managed resolvers.
- Configure critical containers attached to internal networks with explicit DNS upstreams (--dns) so lookups remain local.
- Identify and isolate any host or image that ships moby packages if you cannot apply patches immediately.
- Short term (days):
- Patch moby/moby‑engine to the vendor‑supplied, patched packages distributed to your environment (use the distro or vendor’s package repositories).
- Rotate credentials or secrets that might have been exposed to containers with weaker isolation.
- Medium term (weeks):
- Replace or harden affected workflows to avoid attaching sensitive workloads to internal networks without explicit DNS controls.
- Where possible, move workloads to container runtimes and node images that are not shipping vulnerable moby versions or that are under tighter management.
- Long term (policy):
- Incorporate SBOM and VEX/CSAF verification into procurement and deployment pipelines.
- Adopt egress‑only network policies for internal containers that should never contact the public internet.
- Demand machine‑readable attestations from vendors for critical artifacts.
Why this class of vulnerability is realistic and dangerous
DNS is an attractive covert channel. DNS queries are ubiquitous, often allowed through firewalls, and permit relatively large data payloads when encoded across label segments. A compromised container without direct outbound access can still leak data if the runtime or host forwards DNS to an external resolver under attacker control.CVE‑2024‑29018 is particularly tricky because the insecure behavior is an intentional part of the runtime’s networking plumbing: the daemon’s choice to forward DNS lookups via the host loopback defeats namespace isolation semantics. That design choice is why a simple configuration or packaging fix at the runtime level is an effective mitigation — but it also means many installations that depend on distributed default configuration may remain exposed until patched.
Critical analysis: Microsoft’s transparency program — strengths and gaps
Strengths
- Product‑level attestation is useful: Microsoft’s decision to publish VEX/CSAF attestations provides a machine‑readable, authoritative inventory for customers of attested products like Azure Linux. That materially reduces triage time for administrators who run attested product families.
- Phased rollout is pragmatic: Starting with Azure Linux gives Microsoft a manageable scope to validate automation and attestation tooling before scaling to the rest of the product portfolio.
Gaps and risks
- Phased rollout creates interim ambiguity: Customers seeing an attestation for Azure Linux but not for other Microsoft products may misread the absence of attestations as evidence of safety. The attestation model needs explicit messaging that absence of mention ≠ absence of vulnerable code.
- Supply‑chain complexity demands per‑artifact checks: Microsoft ships many images and binaries across its clouds, services, and device stacks. A product‑level attestation is necessary but insufficient for defenders who must inventory per artifact (VM images, marketplace appliances, agent bundles).
- Timing and cadence: Vulnerabilities in widely used upstream components like Moby require rapid, broad attestations. Phased programs can leave windows where customers remain uncertain about whether the vendor has verified their other artifacts.
- Operational burden on customers: Where vendors have not yet attested, the remediation burden falls to customers to proactively inventory and scan each image and runtime. This consumes significant operational resources for large estates.
What Microsoft should do next (recommended)
- Accelerate artifact scanning and attestation cadence across high‑risk product families (IoT/edge, Marketplace images, container runtimes).
- Provide clear, prominent language on each advisory stating whether other product families have been scanned, and publish an explicit list of unscanned product families that may plausibly ship the component.
- Give customers easy ways to request SBOM/VEX for specific artifacts and publish per‑artifact SBOMs for widely distributed images (Marketplace, EFLOW, VM images).
- Offer official remediation playbooks for commonly used product families (AKS node images, Azure IoT Edge, EFLOW, Marketplace images) explaining whether they ship moby or containerd and how to remediate.
Practical examples: where to look for Moby in Microsoft environments
- Check CBL‑Mariner package indices and distro repos for moby packages in Azure Linux images.
- Review EFLOW / Azure IoT Edge supported platforms and appliance manifests — Microsoft documents that moby‑engine is the supported runtime for IoT Edge scenarios and EFLOW VM compositions include the IoT Edge runtime.
- Audit Azure Marketplace images and community/partner appliances for included moby or docker packages.
- Inspect any Windows images that run IoT Edge for Linux on Windows (EFLOW) compositions — these often come preinstalled with moby‑engine within the Linux VM layer.
Conclusion
Microsoft’s statement that Azure Linux includes the open‑source library implicated by CVE‑2024‑29018 is an authoritative and actionable attestation for Azure Linux customers. However, it is not a blanket exclusion of other Microsoft products. Multiple Microsoft offerings — notably Azure IoT Edge and EFLOW, certain Marketplace images, and curated CBL‑Mariner packages — are known to include or distribute Moby‑derived components and therefore represent plausible carriers until each artifact is individually inventoried and attested.Operationally, defenders should treat the MSRC attestation as a high‑confidence signal for Azure Linux and immediately remediate that product. Simultaneously, organizations must aggressively inventory Microsoft‑supplied artifacts in their estates, apply upstream patches where moby is present, enforce DNS egress controls, and hunt for DNS‑based exfiltration indicators. The vendor’s machine‑readable VEX/CSAF program is a welcome step for supply‑chain transparency, but it must be paired with rapid, broad artifact coverage and explicit messaging so that customers can act decisively across all Microsoft artifacts they rely upon.
Source: MSRC Security Update Guide - Microsoft Security Response Center