Microsoft’s brief product attestation — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is a precise, product‑scoped inventory statement, not a technical guarantee that no other Microsoft product could include the same vulnerable component; defenders must treat Azure Linux as a confirmed carrier while performing artifact‑level checks across other Microsoft‑distributed images and runtimes. view
CVE‑2024‑43796 is an XSS (cross‑site scripting) weakness in the widely used Node.js web framework Express: in versions prior to 4.20.0 (and certain pre‑release 5.x alphas), passing untrusted user input to
Express is a pervasive open‑source dependency in Node.js application stacks, tooling, and many packaged images. When a vendor such as Microsoft issues a product mapping that names a particular distribution — for example Azure Linux — as including an upstream open‑source library, that mapping is a statement of inventory for that product only. It tells you where Microsoft has already checked and found the component; it does not certify that other Microsoft artifacts were exhaustively scanned and found clean. Multiple independent vulnerability trackers and distribution advisories corroborate the technical details of CVE‑2024‑43796 and its remediation.
Defenders must therefore act on two fronts: (1) treat Azure Linux images as in‑scope and patch them promptly, and (2) conduct artifact‑level inventory and scanning across other Microsoft‑published images and tools in your environment. Upgrade Express to 4.20.0 or newer where present, avoid unsafe use of
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE‑2024‑43796 is an XSS (cross‑site scripting) weakness in the widely used Node.js web framework Express: in versions prior to 4.20.0 (and certain pre‑release 5.x alphas), passing untrusted user input to
response.redirect() can cause a reflected XSS condition because the redirect target may be reflected into an HTML anchor or otherwise rendered, allowing execution of attacker‑controlled script under some browser behaviors. The Express project patched the flaw in Express 4.20.0 and later.Express is a pervasive open‑source dependency in Node.js application stacks, tooling, and many packaged images. When a vendor such as Microsoft issues a product mapping that names a particular distribution — for example Azure Linux — as including an upstream open‑source library, that mapping is a statement of inventory for that product only. It tells you where Microsoft has already checked and found the component; it does not certify that other Microsoft artifacts were exhaustively scanned and found clean. Multiple independent vulnerability trackers and distribution advisories corroborate the technical details of CVE‑2024‑43796 and its remediation.
 What the MSRC wording actually means
What the MSRC wording actually means
Product attestation versus ecosystem sweep
When Microsoft’s Security Response Center (MSRC) writes that “Azure Linux includes this open‑source library and is therefore potentially affected,” they are doing two things:- Confirming that Microsoft‑published Azure Linux images or packages contain the upstream component identified by the CVE.
- Informing customers that they should prioritize patching those Azure Linux artifacts.
Why Microsoft limits the scope
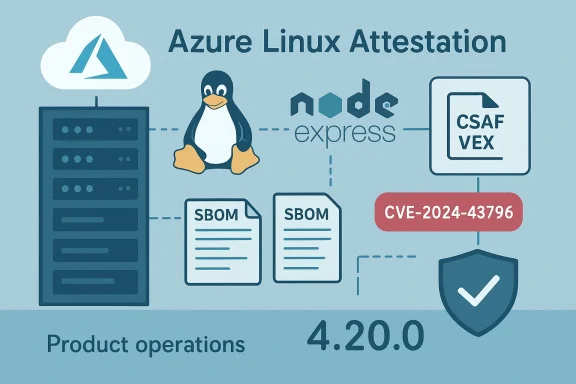
There are practical reasons for this approach. Modern vendors ship thousands of artifacts — kernels, container images, SDK runtimes, agents, and appliance images — each built at different times with different upstream components. Microsoft’s public attestation signals a completed check for a named product; extending that attestation to every Microsoft artifact would require thorough, time‑consuming per‑artifact inspection and the publication of machine‑readable attestations (CSAF/VEX) to remove ambiguity. Microsoft has stated an intention to expand machine‑readable attestations (CSAF/VEX) so that downstream automation can more reliably answer “which Microsoft artifacts actually include the vulnerable component?” — but until those attestations are published and ion is product‑scoped and partial.The technical reality: could other Microsoft products include Express?
Short answer: Yes, possibly — but not necessarily. The public MSRC attestation confirms only what Microsoft has inventory‑checked and is willing to declare publicly for that CVE at that time.Why other Microsoft artifacts might carry Express
- Microsoft publishes many container images and SDK runtimes. Some of these images are thin wrappers around upstream Node.js application stacks and may include npm packages such as Express either directly or transitively.
- Microsoft services and developer tools rely on Node.js ecosystems. Internals of developer tooling, CLI tools, or service frontends (including telemetry, proxies, or admin consoles) may include Node.js dependencies.
- Windows and cloud artifacts can carry Linux‑based images. The Windows Subsystem for Linux (WSL) kernel and Microsoft‑published Linux images used by Azure services or appliances can ship upstream components that include the Express package in support tooling or sample applications.
What the MSRC attestation does imply operationally
- If you run Azure Linux images, you should assume they are confirmed carriers for the implicated component and treat them as in‑scope for remediation.
- If you run other Microsoft‑supplied artifacts — WSL kernels, Microsoft container images, Azure Marketplace appliances, or agent images — you should not assume they are clean simply because they are not named by MSRC. Instead, verify with SBOMs or image scans.
Deep dive: CVE‑2024‑43796 technical details and scope
What is vulnerable and under what conditions
- Affected versions: express < 4.20.0 and certain pre‑release 5.x versions (>=5.0.0‑alpha.1 and <5.0.0).
- The vulnerability stems from
response.redirect()reflecting the redirect target in certain response modes (notably HTML fallbacks where an anchor is rendered). If the target URL contains attacker‑controlled content and the application fails to neutralize or avoid reflecting that input, a browser may render script in the anchor context or otherwise interpret malicious payloads. - Exploitation conditions are non‑trivial: it requires control of a redirect target, and browsers must behave in particular ways (e.g., when a status code does not cause automatic navigation and the HTML anchor is presented). The Express project and multiple security advisories classify the CVE as Moderate and provide the patch in Express 4.20.0.
Real‑world risk profile
- For typical web apps that pass untrusted input directly into
response.redirect()without additional validation, the impact is real and may enable reflected XSS. - Many applications already use defensive controls (server‑side sanitizers, CSP, or deny‑list redirect logic), which reduce attack surface — but the core library behavior increases the chance that developers will inadvertently create an exploitable reflection.
- The remediation is straightforward and low‑risk: upgrade to Express 4.20.0 or newer, or to 5.0.0 when stable. Where upgrades are not immediately possible, avoid using
response.redirect()with untrusted input or ensure stricter allow‑lists for redirect targets.
Practical guidance for administrators and developers
1. Treat Microsoft’s Azure Linux attestation as an operational priority
- If you run Azure Linux images in production, assume those images are in‑scope and patch or update them according to Microsoft’s update guidance.
- Confirm the presence and version of Express in Azure Linux hosts by checking installed npm packages, container images, or application manifests.
2. Don’t assume other Microsoft artifacts are safe — verify them
- Inventory all Microsoft‑supplied artifacts you run:
- WSL kernel builds and WSL‑provided images
- Microsoft‑maintained container images (runtime or SDK images)
- Azure Marketplace images and appliances published by Microsoft
- Agent/daemon images and tools that Microsoft ships
- For each artifact, obtain the SBOM (if available) or perform a package scan for
expressand its transitive dependencies. - If you cannot obtain an SBOM, pull the image into a staging environment and run an automated dependency scan.
3. Immediate mitigations for applications that can’t upgrade instantly
- Avoid calling
response.redirect()with untrusted input. If your code must redirect to user‑supplied targets, implement a server‑side allow‑list of safe domains and exact paths. - Ensure responses that could reflect user input are subject to strict Content Security Policy (CSP) to reduce the impact of reflected XSS.
- Use proper HTML encoding when rendering input into fallback anchor elements; remove any place where a user‑controlled value is included unescaped in HTML text or attributes.
- If possible, use status codes that cause immediate browser redirection (e.g., 302/303/307) rather than rendering HTML fallbacks that may reflect the target.
4. Automate detection and remediation
- Add dependency scanning for Express in CI/CD pipelines and image builds.
- Use SBOMs and machine‑readable VEX/CSAF mappings when vendors publish them to automate artifact‑level decisions about which images and builds are impacted.
- Where vendors (including Microsoft) publish CSAF/VEX attestations, ingest them into invce manual effort. Microsoft has stated an intent to publish CSAF/VEX attestations to make this process more deterministic.
Cross‑product risk scenarios to watch
Even if Microsoft’s current public mapping names only Azure Linux, there are realistic scenarios where other Microsoft artifacts could carry Express:- Microsoft‑published container images (for example, Node.js base images that Microsoft maintains) may include Express as part of example apps or bundled modules.
- Azure services that host multi‑tenant apps might use Node.js front‑end agents or management consoles that depend on Express internally.
- Developer tooling and product onboarding experiences (CLI tools, dashboards) can bundle Node modules for local servers or development servers that include Express.
Strengths and limits of Microsoft’s current approach
Strengths
- Targeted, actionable information: By naming Azure Linux explicitly, MSRC gives immediate operational direction to customers using that product.
- Commitment to transparency: Microsoft’s public statements and the stated plan to publish CSAF/VEX attestatiotoward machine‑readable inventories that are useful for automation.
- Practical workload prioritization: For organizations that run many different artifacts, a product‑level attestation reduces ambiguity for the named artifact and helps prioritize patch windows.
Limits and potential risks
- Scope ambiguity: Customers may misread a product attestation as an ecosystem sweep. That ambiguity increases the risk of overlooked exposures in other artifacts.
- Time lag and coverage: The pace at which Microsoft can inventory and attest every image, kernel, and agent is finite; until CSAF/VEX coverage is broad, blind spots remain.
- Automation dependencies: Many customers rely on vendor‑published attestations to feed their automation — gaps or delays in attestations increase the burden of manual verification and can slow remediation.
Recommended checklist for security teams (actionable)
- Inventory Azure Linux instances and apply updates that include Express 4.20.0 or later if Express is installed.
- Scan all Microsoft‑published images and artifacts in your environment for
express(use image scanners, SBOMs, or npm list commands). - For apps that cannot be upgraded immediately:
- Replace
response.redirect()calls that accept uncontrolled input with explicit allow‑lists. - Apply strict CSP and set HTTP-only cookies to reduce attack surface.
- Ingest vendor CSAF/VEX attestations as they become available; until then, perform artifact‑level scanning for every Microsoft image you run.
- Add dependency checks and alerts to CI pipelines to catch vulnerable Express versions during build time rather than at runtime.
- Communicate the scope to stakeholders: Azure Linux = confirmed; other Microsoft artifacts = verify.
Conclusion
The MSRC statement that Azure Linux includes the open‑source library and is therefore potentially affected is a valuable, authoritative product‑level attestation: it confirms a confirmed hit for that product and gives Azure Linux customers a clear remediation priority. However, this language is not an exhaustive declaration about every Microsoft artifact and should not be interpreted as proof that no other Microsoft product includes the vulnerable Express library.Defenders must therefore act on two fronts: (1) treat Azure Linux images as in‑scope and patch them promptly, and (2) conduct artifact‑level inventory and scanning across other Microsoft‑published images and tools in your environment. Upgrade Express to 4.20.0 or newer where present, avoid unsafe use of
response.redirect() with untrusted input, and automate detection through SBOMs and dependency scanning. Those steps, combined with vendor‑provided CSAF/VEX attestations when available, will close the practical gaps that a product‑scoped attestation leaves open.Source: MSRC Security Update Guide - Microsoft Security Response Center