Microsoft’s brief public note — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate for the product it names, but it is a product‑scoped attestation, not proof that no other Microsoft product could contain the same vulnerable kernel code.
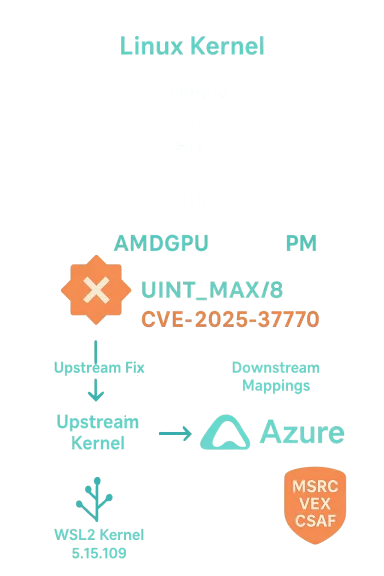
CVE-2025-37770 is a medium‑severity Linux kernel vulnerability discovered in the AMD DRM power‑management code (the
At the same time Microsoft’s Security Response Center (MSRC) published an advisory mapping the upstream component to Microsoft’s Azure Linux distribution and included a standard FAQ line: Azure Linux “includes this open‑source library and is therefore potentially affected.” Microsoft also announced that it began publishing machine‑readable CSAF/VEX attestations in October 2025 and committed to updating CVE/VEX records if other Microsoft products are later identified as carriers of the same upstream code. That combination of product‑level mapping plus an explicit promise to expand attestations is the context for the question many administrators are asking: is Azure Linux the only Microsoft product that ships the vulnerable code?
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2025-37770 is a medium‑severity Linux kernel vulnerability discovered in the AMD DRM power‑management code (the drm/amd/pm path). The root cause is a missing validation when user‑supplied speed values are interpreted: if a user provides a value larger than UINT_MAX/8, a division‑by‑zero can occur, producing a kernel crash (availability impact). This defect was reported by the Linux Verification Center and fixed in upstream kernel branches shortly after disclosure.At the same time Microsoft’s Security Response Center (MSRC) published an advisory mapping the upstream component to Microsoft’s Azure Linux distribution and included a standard FAQ line: Azure Linux “includes this open‑source library and is therefore potentially affected.” Microsoft also announced that it began publishing machine‑readable CSAF/VEX attestations in October 2025 and committed to updating CVE/VEX records if other Microsoft products are later identified as carriers of the same upstream code. That combination of product‑level mapping plus an explicit promise to expand attestations is the context for the question many administrators are asking: is Azure Linux the only Microsoft product that ships the vulnerable code?
What Microsoft’s wording actually means
Microsoft’s phrasing is deliberately narrow and procedural.- Authoritative for the named product: When MSRC says Azure Linux includes the library, treat that as an accurate, machine‑readable inventory item for Azure Linux — Microsoft inspected those artifacts and confirmed presence of the upstream component.
- Not an exclusivity claim: That inventory result does not logically imply every other Microsoft product does not include the same upstream files. In practice, the presence of a particular upstream source file or compiled module is an artifact‑level property depending on build configuration, kernel version and backports. Microsoft’s public text explicitly promises to update VEX/CSAF records if additional Microsoft products are found to ship the component — which is a process commitment, not a statement of universal absence.
- Operational takeaway: For organizations running Azure Linux, MSRC’s attestation is an actionable signal to prioritize patching. For other Microsoft‑distributed artifacts (WSL kernels, Marketplace VM images, AKS node images, Windows Shipping kernel artifacts that embed Linux kernels), the safe operational posture is to assume unknown until verified rather than assume safe because Microsoft named only one product.
The technical facts on CVE‑2025‑37770
What the bug is and where it lives
- The vulnerability sits in the AMD DRM power‑management code in the Linux kernel (files under
drivers/gpu/drm/amd, commonly described asdrm/amd/pm). - The bug arises from insufficient input validation: a speed value supplied by a user can be used as a divisor without a proper bounds check; values greater than
UINT_MAX/8can therefore trigger a division by zero. The impact is an availability (DoS) condition — the kernel can crash.
How upstream handled it
Upstream Linux kernel maintainers accepted and merged defensive fixes. The public CVE metadata and stable‑branch commits show the fixes were applied across the relevant stable series; downstream distributions then map those upstream commits to package versions and ship patched kernels. Most major vendors and distros had advisories and backports following the upstream fixes. Use upstream commit identifiers and the vendor package mapping to determine whether a particular kernel binary includes the fix.Why Azure Linux is the product named (and why Microsoft named it first)
There are two pragmatic reasons vendors commonly name one product first in their inventory attestations:- Inventory completeness: Azure Linux is Microsoft’s own Linux distribution and the one product set they began cataloging for VEX/CSAF in October 2025. Starting with a single, internally owned distribution lets the vendor produce high‑confidence, machine‑readable attestations earlier than trying to inventory many diverse artifacts at once. Microsoft described this “crawl, walk, run” rollout in their VEX blog.
- Actionability: Azure Linux customers directly rely on the distro’s update channel and MSRC mapping provides a clear immediate remediation path for those customers. Microsoft’s statement commits to adding additional product mappings as their inventory work proceeds, which is why the MSRC FAQ says they will update the CVE if other Microsoft products are identified.
Where the same upstream code can also appear inside Microsoft artifacts
Microsoft distributes — or publishes artifacts that contain — Linux kernels in multiple places. That matters because the AMD DRM code in question is part of upstream Linux kernel sources and can appear in any Microsoft product or image that includes that kernel code with the amdgpu DRM driver enabled.- WSL2 kernel sources and builds: Microsoft maintains the WSL2 kernel source tree publicly and ships WSL2 kernel binaries. The WSL2 repo is an actively maintained kernel tree and includes the
drivers/gpu/drm/amdsources in branches used to generate WSL kernels. That makes WSL kernels an obvious artifact to inventory for this class of DRM vulnerabilities. - Azure VM images and linux‑azure kernels: Some Azure service images include vendor kernels or Microsoft‑provided kernel builds for cloud‑optimized images. Depending on the kernel version and configuration, those builds may include the amdgpu code paths.
- Marketplace images / AKS node images / custom images Microsoft publishes: Any image that contains a Linux kernel with the affected driver compiled in is a candidate to carry the vulnerable code until verified.
- Other Microsoft‑distributed kernel artifacts: Microsoft sometimes publishes kernel builds or patches used by appliance images or partner integrations; each of those artifacts requires verification.
Operational checklist: how to determine whether a Microsoft product you run is affected
Here is a practical, short checklist your operations or security team can use to move from uncertainty to verification and remediation.- Inventory Microsoft‑supplied Linux artifacts in your environment:
- List Azure VM images, Marketplace images, AKS node images, and any Microsoft‑provided kernels in use.
- Identify WSL2 instances and record the WSL kernel version (run
uname -rinside WSL2 or read the WSL kernel binary version on the Windows host). - Map kernel versions to upstream fixes:
- Compare the running kernel version (for each artifact) against the upstream kernel versions that incorporate the CVE fix (use the commit IDs published in the CVE references and vendor advisories).
- If the running kernel predates the fixed upstream release or lacks the backport, treat the artifact as vulnerable.
- Inspect kernel configuration / modules if you cannot easily upgrade:
- For booted systems, check whether the
amdgpudriver ordrmmodules are present (lsmod | grep amdgpuor check/lib/modules/$(uname -r)/kernel/drivers/gpu/drm/amd). - If the
amdgpucode is built as a module and not loaded, the immediate exploitation surface may be limited, but modules can be loaded later — so long‑term remediation is to apply the vendor’s patch. Vendor advisories and distro security pages will indicate package versions that contain the fix. - Patch or mitigate:
- Apply vendor patches or upgraded kernel packages that contain the upstream fix.
- If a full kernel update isn’t immediately possible, consider temporary mitigations such as blacklisting
amdgpuwhen it’s not required, or restricting local access that would allow unprivileged users to trigger the vulnerable path — but treat these as stopgaps, not solutions. - Subscribe to VEX/CSAF feed and vendor advisories:
- Subscribe to Microsoft’s CSAF/VEX feed (MSRC) to see product‑level attestations expand over time.
- Track upstream kernel commits and distro security advisories to confirm which package versions include fixes.
Why absence of an attestation is not proof of safety
It’s important to be explicit about this logical point: a vendor’s published attestations cover what the vendor has completed checking and declared. Lack of a VEX/CSAF entry for a given product is absence of attestation, not evidence of absence of the vulnerable code.- A product may be affected but un‑attested simply because the vendor has not completed inventory work for that product family.
- Conversely, a product may be attested as Not Affected when the vendor has validated the absence of the upstream component or verified a fix/backport.
Risk analysis and likely exposure scenarios
- High‑confidence exposure: Any system running a kernel version older than the upstream fixed releases and with
amdgpubuilt‑in or available as a loadable module is plausibly vulnerable. Many cloud images and on‑premises Linux hosts fall into this category until patched. Upstream advisories and distro security pages (Ubuntu, Debian, Red Hat, etc.) already map fixes to package releases; if your system’s package version predates those fixes, assume risk. - Microsoft artifact exposure: Azure Linux is a known carrier per MSRC’s inventory — treat Azure Linux images as in‑scope. For other Microsoft artifacts (WSL2 kernels, Azure Marketplace images, AKS images), exposure depends on:
- whether the kernel build used to create the artifact included the
drm/amdsources; and - whether the build’s version contains the upstream fix or a vendor backport.
- Exploitability: The vulnerability requires local access (non‑network remote exploitation is not indicated); its primary result is denial of service (kernel crash). EPSS/KEV signals for similar CVEs have shown low probability of large‑scale remote exploitation for this class of driver robustness bugs, but local access or multi‑tenant cloud scenarios still create meaningful risk.
Practical recommendations for Windows and Azure administrators
- Immediately apply MSRC guidance for Azure Linux images: patch image families and redeploy nodes that use the affected images. Microsoft’s attestation gives Azure Linux customers a single, high‑priority remediation path.
- For WSL customers:
- Check your WSL kernel version and the
WSL2kernel image that Windows is using. Microsoft publishes WSL2 kernel releases and tags; if your WSL kernel predates the fixes, update the WSL kernel or apply the appropriate patched release. - For Azure users running Marketplace images, AKS, or custom images:
- Identify which kernel artifact is used in your irnel version to upstream fixes. If it’s older than the fixed release, treat it as vulnerable and schedule updates.
- Maintain an inventory and automation pipeline that:
- Collects
uname -rand loaded module lists across Microsoft‑distributed artifacts you run. - Compares those versions to a curated mapping of CVE → fixed upstream release(s).
- Automates patching and redeployment for affected images.
Strengths and risks of Microsoft’s VEX/CSAF approach
Strengths
- Machine‑readable attestations reduce noise: Publishing CSAF/VEX files lets automation triage CVE applicability for Azure Linux customers quickly and reliably. Microsoft’s blog announcing the VEX rollout emphasized the value of clear exploitability state and product mapping for customers and partners.
- Process transparency: Promising to expand attestations as additional products are inventoried gives a clear, auditable path for customers to expect updated mappings.
Risks and limits
- Partial coverage during rollout: Early rollout to a single product family (Azure Linux) necessarily leaves other Microsoft artifacts un‑attested for a period of time; that window creates operational ambiguity for customers who consume other Microsoft‑distributed kernel artifacts.
- Customer expectation mismatch: Some customers may read the attestation as a blanket statement that only Azure Linux is affected; that misreading risks leaving other Microsoft artifact instances unverified and unpatched. Clear communication and automation checks are required to avoid that mistake.
When a vendor statement is enough — and when it is not
- If you run only Azure Linux images in your environment, Microsoft’s atte evidence to prioritize patching immediately.
- If you run other Microsoft artifacts — especially WSL2 instances, linux‑azure kernels, or Marketplace images — you must independently verify kernel contents or wait for Microsoft to publish an explicit VEX/CSAF attestation for each named product family before concluding those artifacts are unaffected.
- For high‑security environments, do not rely solely on the absence of an attestation to accept a “Not Affected” posture.
Conclusion
Microsoft’s public advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is a precise and useful inventory statement for Azure Linux customers. It is also intentionally narrow: Microsoft has started its CSAF/VEX rollout with Azure Linux and promised to update CVE records as they identify additional Microsoft products that ship the same upstream component. That means:- Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the specific
drm/amd/pmcomponent implicated by CVE‑2025‑37770. - However, Azure Linux is not necessarily the only Microsoft product that could contain the vulnerable code — Microsoft publishes and ships Linux kernel artifacts in other places (most notably the WSL2 kernel) and many Microsoft images use vendor or Microsoft kernel builds; any of these artifacts may or may not include the affected
amdgpucode depending on their kernel version and configuration. Treat the MSRC attestation as authoritative for Azure Linux, and treat other Microsoft artifacts as unverified until checked.
Source: MSRC Security Update Guide - Microsoft Security Response Center