Microsoft’s MSRC advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate for the Azure Linux product family, but it is a product‑scoped attestation — not a categorical guarantee that no other Microsoft product can include the same vulnerable kernel component.
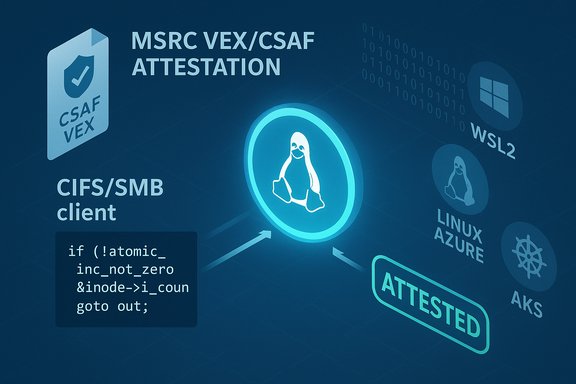
Microsoft recently began publishing machine‑readable CSAF/VEX attestations and has started the rollout with the Azure Linux (CBL‑Mariner / Azure Linux lineage) product family. That rollout means Microsoft will explicitly declare which internal product artifacts have been inventory‑checked and mapped to a given CVE; in the case of CVE‑2025‑40103 (the SMB client refcount leak in the Linux kernel’s CIFS/SMB client code), Microsoft’s public guidance names Azure Linux as including the implicated open‑source component and therefore being potentially affected.
This wording is intentionally precise: it reports the result of Microsoft’s inventory work for Azure Linux at the moment of publication and commits to update the CVE/VEX records if additional Microsoft products are later found to ship the same component. It does not, however, prove that other Microsoft artifacts cannot include the vulnerable kernel code.
This is a kernel reliability/availability issue rather than a standard remote code execution primitive; the primary risk is denial‑of‑service or memory exhaustion in multi‑tenant or untrusted local contexts where the vulnerable code path can be exercised. Multiple distribution advisories and kernel trackers have mapped the upstream commits and classified the practical impact accordingly.
However, the phrasing does not mean Microsoft has scanned every Microsoft product or that other Microsoft artifacts are proven clean. The VEX/CSAF rollout is phased; the initial coverage focused on Azure Linux and Microsoft pledged to update CVE entries and attestations if additional products are identified as carriers of the same code. Practically, absence of an attestation for another product is absence of attestation, not evidence of absence of the vulnerable component.
Caveat: Specific presence of the vulnerable code in any particular Microsoft product other than Azure Linux requires either a Microsoft VEX/CSAF attestation for that product or direct artifact inspection (kernel version, config, SBOM); absent that, claims of presence are unverifiable and must be treated cautiously.
Further reading and continuous monitoring should include Microsoft’s VEX/CSAF feed for updates, your distro/vendor advisories, and kernel stable trees to identify the exact patched commits and backports applicable to your deployments.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Microsoft recently began publishing machine‑readable CSAF/VEX attestations and has started the rollout with the Azure Linux (CBL‑Mariner / Azure Linux lineage) product family. That rollout means Microsoft will explicitly declare which internal product artifacts have been inventory‑checked and mapped to a given CVE; in the case of CVE‑2025‑40103 (the SMB client refcount leak in the Linux kernel’s CIFS/SMB client code), Microsoft’s public guidance names Azure Linux as including the implicated open‑source component and therefore being potentially affected.This wording is intentionally precise: it reports the result of Microsoft’s inventory work for Azure Linux at the moment of publication and commits to update the CVE/VEX records if additional Microsoft products are later found to ship the same component. It does not, however, prove that other Microsoft artifacts cannot include the vulnerable kernel code.
What the vulnerability is (concise technical summary)
CVE‑2025‑40103 is a kernel‑space issue in the Linux SMB client implementation (the CIFS/SMB client VFS paths). The underlying problem is a refcount lifecycle bug in the cifs client data structure — the code previously attempted to rely on refcount increments in a dumper/resume path and that logic could misbehave under rare races, producing either refcount leaks or incorrect reference sequences that ultimately lead to kernel memory leaking or stability problems. The upstream fix removes the refcount dependency in the dumper path and uses a cookie mechanism instead to support safe dump resumption.This is a kernel reliability/availability issue rather than a standard remote code execution primitive; the primary risk is denial‑of‑service or memory exhaustion in multi‑tenant or untrusted local contexts where the vulnerable code path can be exercised. Multiple distribution advisories and kernel trackers have mapped the upstream commits and classified the practical impact accordingly.
Why Microsoft’s wording matters — attestation vs. exclusivity
Microsoft’s statement that “Azure Linux includes the open‑source library and is therefore potentially affected” is best read as an authoritative attestation for Azure Linux specifically: Microsoft inspected Azure Linux artifacts, found the component, and published a machine‑readable VEX/CSAF declaration reflecting that inventory result. That is valuable for automation and for security teams that run Azure Linux images.However, the phrasing does not mean Microsoft has scanned every Microsoft product or that other Microsoft artifacts are proven clean. The VEX/CSAF rollout is phased; the initial coverage focused on Azure Linux and Microsoft pledged to update CVE entries and attestations if additional products are identified as carriers of the same code. Practically, absence of an attestation for another product is absence of attestation, not evidence of absence of the vulnerable component.
Which Microsoft products might also plausibly include the affected code
Because CVE‑2025‑40103 is a bug in the Linux kernel source tree (the CIFS/SMB client code), any Microsoft product that ships or runs a Linux kernel binary built from an upstream tree containing the vulnerable commit range and with the relevant SMB/CIFS client functionality compiled in can be a potential carrier. The following Microsoft artifacts are the most plausible places to check:Azure Linux (explicitly attested)
- Microsoft has already attested Azure Linux as including the implicated code and therefore Azure Linux images should be treated as in‑scope for remediation until Microsoft marks them fixed in the VEX/CSAF feed. This is the authoritative “yes” for Azure Linux customers.
Linux kernels Microsoft builds or distributes
- linux‑azure / Azure‑tuned kernels: Some Azure VM SKUs run Azure‑tuned kernels packaged or published by Microsoft. If those kernel builds include the vulnerable SMB client code, they are potentially affected.
- CBL‑Mariner artifacts and derived images: CBL‑Mariner is Microsoft’s internal Linux distribution lineage and forms the basis for many Azure Linux host/container artifacts. If Microsoft’s Mariner‑based kernels included the code, related images could also be carriers.
Windows Subsystem for Linux (WSL / WSL2)
- WSL2 ships a Microsoft‑built Linux kernel that Microsoft publishes and updates independently. The WSL kernel’s configuration and releases are public; if a WSL kernel build contains the vulnerable commit and the SMB client functionality is enabled, WSL2 hosts could be affected until the kernel is patched and redistributed.
Azure Marketplace images, AKS nodes, curated images, and Marketplace appliances
- Marketplace images and AKS node images are often created from vendor kernels or Azure‑tuned kernels. Whether these images are affected is a per‑image question. The image publisher or Microsoft’s marketplace entry may need to be checked; Microsoft’s attestation for Azure Linux does not automatically cover third‑party Marketplace images.
Container images and static binaries
- Container images that do not ship a kernel are not directly “affected” at the container userland level, but if they run on a host kernel that is vulnerable, the service can be impacted by the host’s exposure. Similarly, statically linked or vendor‑compiled artifacts that embed kernel‑adjacent code are a separate risk model and must be verified on a per‑artifact basis.
Practical implications for defenders and operators
The operational takeaway is straightforward but requires discipline: treat Microsoft’s VEX/CSAF attestation as authoritative only for the products it names, and perform artifact‑level verification for everything else.- If you run Azure Linux images, prioritize patching and follow Microsoft’s published updates immediately — the VEX/CSAF attestation is the vendor’s definitive signal for that product.
- For other Microsoft‑supplied kernels or images (WSL2, linux‑azure, AKS nodes, Marketplace images), do not assume safety just because those products are not named in the VEX feed yet. Inspect kernels and image provenance.
- For containerized workloads, check the host kernel version and configuration rather than only the container’s userland packages. A vulnerable host kernel can expose containerized services to availability risks.
Concrete verification steps (recommended)
- Check the kernel version on hosts: uname -r and cross‑reference the kernel tree and patch level to determine if the vulnerable commit range is present.
- Inspect kernel configuration: check /boot/config-$(uname -r) for
CONFIG_CIFS,CONFIG_CIFS[I]STATS, or other relevantCONFIG[/I]*flags that enable the CIFS/SMB client paths. If the feature is absent, the attack surface may be reduced. - Query loaded modules: lsmod for cifs modules and verify module build IDs to map to patched package versions.
- Use vendor SBOM/VEX: consume Microsoft’s CSAF/VEX files where available to automatically map CVE status to product artifacts.
- For WSL2: check the WSL kernel release tag on the Windows host and apply kernel updates or a custom kernel where necessary.
Immediate mitigations while patching
- Restrict untrusted local access on multi‑tenant systems and aggressively control who can execute operations that interact with CIFS/SMB client code.
- Unload the cifs module if it is not required for the host workload (modprobe -r cifs), recognizing that this may break functionality for services that legitimately rely on CIFS.
- Apply network/ACL mitigations to limit exposure of SMB endpoints where feasible until kernels are updated and systems rebooted.
Strengths and benefits of Microsoft’s new VEX/CSAF approach
- Machine‑readable attestations simplify automation: SOCs and patch management systems can ingest VEX/CSAF to drive deterministic triage and reduce false positives. Microsoft’s initial focus on Azure Linux provides an actionable signal for cloud customers.
- Improved transparency: publishing product‑level mappings clarifies which Microsoft SKUs were inspected and which remain under inventory, improving accountability and traceability.
Risks and limitations of the current approach
- Phased rollout can create an illusion of completeness. Organizations may see Azure Linux listed and mistakenly assume all Microsoft artifacts are safe; that is not what the attestation guarantees. Security teams must continue to inventory and verify all Microsoft artifacts they run.
- Third‑party and Marketplace images remain a blind spot unless their publishers provide similar attestations or SBOMs. Operators should not assume Marketplace artifacts are covered by Microsoft’s Azure Linux attestation unless explicitly stated.
- Static linking and embedded components: vendor‑built images or appliances that embed upstream code (or statically link userland components) can escape automated kernel‑level mapping and require manual verification.
Recommended short‑term remediation checklist
- Patch and reboot all Azure Linux hosts per Microsoft guidance (highest priority).
- Inventory Microsoft‑supplied kernels (linux‑azure, WSL2 kernels, CBL‑Mariner derivatives) and map versions against the upstream fix list.
- For Windows endpoints with WSL2: confirm kernel release and update WSL kernel packages where Microsoft has issued a fix.
- For AKS/node pools and Azure VMs: verify the guest image and kernel source (linux‑azure vs. vendor kernels) and patch node pools where necessary.
- If patching is delayed: restrict access to SMB services, unload cifs modules on hosts that do not require them, and apply process isolation to reduce local attacker exposure.
How to interpret Microsoft statements going forward
Microsoft’s documentation and the VEX/CSAF feed are authoritative for the products they name; security teams should consume those artifacts to automate triage. But a practical security posture also requires artifact‑level checks — kernel configs, loaded modules, SBOMs and image provenance — across all Microsoft or third‑party images in use. Microsoft has committed to expanding its attestations as inventory work completes, but until that mapping is complete, the safe operational stance is to treat un‑attested Microsoft artifacts as unverified rather than cleared.Conclusion — direct answer to the question
No — Azure Linux is not necessarily the only Microsoft product that includes the open‑source library and is therefore potentially affected by CVE‑2025‑40103. Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the implicated Linux kernel component, and therefore it is explicitly in‑scope per Microsoft’s VEX/CSAF mapping. However, because the vulnerability lives in the Linux kernel source tree, any Microsoft product that ships or runs a Linux kernel built from an affected upstream version — including linux‑azure kernels, Microsoft’s CBL‑Mariner artifacts, WSL2 kernels, AKS/VM images, and marketplace images — could plausibly carry the same vulnerable code until those artifacts are separately inventoried and attested or otherwise verified patched. Treat Microsoft’s attestation as definitive for the named product (Azure Linux) and as an invitation to verify other Microsoft artifacts in your environment.Caveat: Specific presence of the vulnerable code in any particular Microsoft product other than Azure Linux requires either a Microsoft VEX/CSAF attestation for that product or direct artifact inspection (kernel version, config, SBOM); absent that, claims of presence are unverifiable and must be treated cautiously.
Further reading and continuous monitoring should include Microsoft’s VEX/CSAF feed for updates, your distro/vendor advisories, and kernel stable trees to identify the exact patched commits and backports applicable to your deployments.
Source: MSRC Security Update Guide - Microsoft Security Response Center