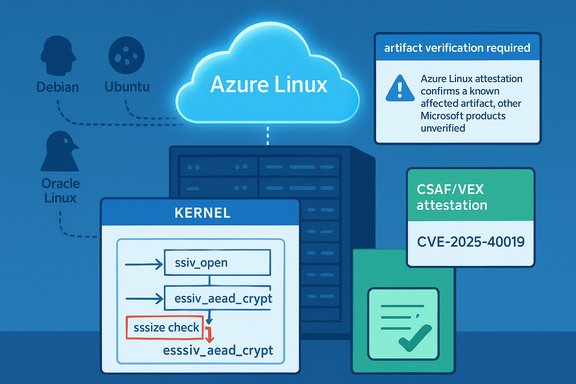
Microsoft’s terse note that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it’s a product‑scoped attestation, not proof that no other Microsoft product can contain the same vulnerable code. The upstream fix for CVE‑2025‑40019 addresses a correctness check in the Linux kernel crypto ESSIV AEAD path (move the ssize check to the start of essiv_aead_crypt so decryption and in‑place encryption paths are validated), and multiple distribution trackers confirm the change and map it into vendor kernel updates.
CVE‑2025‑40019 is a Linux‑kernel vulnerability in the crypto: essiv code path. The upstream patch moves a check on the size (ssize) to the start of essiv_aead_crypt so the check runs for decryption and in‑place encryption as well as the previously covered paths. This is a defensive correctness fix intended to prevent malformed inputs from bypassing a bounds/size validation; distributors classify the issue as a robustness/availability risk and have published kernel package updates that incorporate the upstream commits. Evidence for the technical change appears in the kernel stable tree and is reflected in Debian, Ubuntu, Oracle Linux and other vendor trackers. Microsoft’s MSRC entry (the sentence the user quoted) follows a new, more explicit supply‑chain transparency model: Microsoft began publishing machine‑readable CSAF/VEX attestations for product‑level third‑party component inventories (starting its rollout with Azure Linux). Microsoft’s statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is an attestation of what Microsoft has checked so far; Microsoft also committed to update CVE/VEX records if other Microsoft products are later found to ship the same component. That procedure — attest product families as their inventories complete — is central to interpreting the advisory correctly.
The correct operational posture is to treat the Azure Linux attestation as an authoritative “yes” for that product, and to treat all other Microsoft artifacts as unverified until checked. Use the verification checklist, patch promptly where the check shows exposure, and incorporate Microsoft’s CSAF/VEX feeds into automation to accelerate future triage. Multiple independent vendor trackers and the upstream kernel commits confirm the ESSIV ssize fix; administrators should follow a practical verify‑patch‑validate loop and demand vendor attestations or backports for managed/third‑party images when those artifacts are in use.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑40019 is a Linux‑kernel vulnerability in the crypto: essiv code path. The upstream patch moves a check on the size (ssize) to the start of essiv_aead_crypt so the check runs for decryption and in‑place encryption as well as the previously covered paths. This is a defensive correctness fix intended to prevent malformed inputs from bypassing a bounds/size validation; distributors classify the issue as a robustness/availability risk and have published kernel package updates that incorporate the upstream commits. Evidence for the technical change appears in the kernel stable tree and is reflected in Debian, Ubuntu, Oracle Linux and other vendor trackers. Microsoft’s MSRC entry (the sentence the user quoted) follows a new, more explicit supply‑chain transparency model: Microsoft began publishing machine‑readable CSAF/VEX attestations for product‑level third‑party component inventories (starting its rollout with Azure Linux). Microsoft’s statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is an attestation of what Microsoft has checked so far; Microsoft also committed to update CVE/VEX records if other Microsoft products are later found to ship the same component. That procedure — attest product families as their inventories complete — is central to interpreting the advisory correctly. Short answer to the user’s question
- No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable open‑source library. It is the only Microsoft product Microsoft has publicly attested to include the library for this CVE at the time of the advisory. Absence of a VEX/CSAF attestation for other Microsoft products is not proof those products are free of the vulnerable code; it means Microsoft has not (yet) published a product‑level inventory result for them. Treat the Azure Linux attestation as authoritative for Azure Linux and treat other Microsoft artifacts as unverified until Microsoft or you confirm otherwise.
Why that wording matters — attestation vs. exclusivity
Microsoft’s phrasing intentionally distinguishes two things:- An attestation that it inspected and mapped the Azure Linux build(s) and found the implicated upstream component — this is a concrete, machine‑readable record you can trust for that product family.
- A promise to expand the attestation set if additional Microsoft products are discovered to ship the same component — this signals ongoing inventory work rather than a blanket company‑wide scan.
What “includes the library” actually means technically
Linux kernel code is an artifact‑level property. Whether a given Microsoft product “includes” a specific upstream kernel file or driver depends on:- The exact kernel version / upstream commit range used to build that artifact. (Upstream commits fixing CVE‑2025‑40019 are present in the stable trees referenced by distributors.
- The kernel configuration (CONFIG_* flags) used in the build — features can be compiled in, built as modules, or omitted entirely.
- Packaging choices and downstream backports — vendors sometimes apply fixes or backports selectively. Distribution security trackers (Debian, Ubuntu, Amazon Linux, Oracle Linux) have published mappings for which releases are fixed and which are pending.
Cross‑verification of the technical claim
Independent vendor trackers and upstream kernel commits corroborate the technical narrative:- Debian’s security tracker and Ubuntu’s security notices document CVE‑2025‑40019 and list affected/fixed package versions, matching the upstream patch description.
- Oracle’s Linux CVE page and Amazon’s ALAS listing reflect the same remediation note and map fixes to their kernel advisories.
- CVE aggregators and CVE details pages point to the kernel stable commits that implement the ssize recheck in essiv_aead_crypt. Those git commits are the canonical evidence the fix landed in upstream trees.
Practical impact and threat model
CVE‑2025‑40019 is, in practice, a correctness/robustness fix in a kernel crypto path rather than a clear remote code execution worm. Public trackers and vendor advisories classify it as a local attack / availability or stability risk when the vulnerable code path is exercised.- Attack vector: local or guest‑adjacent operations that trigger essiv AEAD operations (for example, encrypted block devices, filesystems that use ESSIV, or other kernel crypto consumers). Exploitability: low for remote unauthenticated attacks, but it’s still a kernel memory/validation fix worth patching promptly.
How to verify whether a Microsoft artifact in your environment is affected
The only reliable way to determine exposure is artifact‑level verification. Below are practical checks you can run on running systems and offline images. These steps assume administrative access to the images/hosts.On a running Linux host (Azure VM, WSL, on‑prem)
- Check the running kernel version:
- uname -r
- Then map that kernel version against vendor advisories (Debian/Ubuntu/Oracle/Amazon/your distro) for CVE‑2025‑40019.
- Inspect the kernel configuration to see if ESSIV/crypto AEAD options are present:
- zcat /proc/config.gz | grep -i ESSIV
- or grep -i essiv /boot/config-$(uname -r)
If the relevant crypto options are absent, the artifact likely does not include the code path. If present, further mapping is required. - Search for relevant modules or symbols:
- modinfo <module> (if the crypto subsystem in question is modular)
- grep -R "essiv" /lib/modules/$(uname -r) (search module sources/metadata)
- Check package changelogs for CVE mapping:
- Debian/Ubuntu: apt changelog linux-image-$(uname -r) | grep -i 40019
- RPM systems: rpm -q --changelog kernel | grep -i 40019
Vendor changelogs will often list CVE IDs or the kernel git commit integrated. - For WSL2:
- Use wsl --status on Windows to see the WSL kernel version and “Kernel version” reported, then run uname -r inside a WSL shell to confirm the live kernel. WSL uses a Microsoft‑built kernel and thus requires separate verification.
- For Azure Marketplace or custom images:
- Pull the image, boot a test instance, and perform the checks above. Don’t assume base image labels guarantee absence — verify the built kernel and module list.
Offline image or package inspection
- Extract the kernel image or initramfs from the image and inspect its configuration for CONFIG_* flags and search the kernel vmlinux or modules for essiv symbols. This is how to determine presence without booting. If you manage a build pipeline, check SBOMs and the build artifact commit hash against the upstream kernel git commit referenced in public advisories.
Recommended remediation and operational playbook
- Prioritize patching for hosts that actually include and execute the ESSIV path (per the verification checklist above). For Azure Linux SKUs Microsoft has attested, treat remediation as high‑priority.
- Apply vendor/distribution kernel updates that include the upstream fix. Reboot into the patched kernel (kernel fixes require reboot). Vendor trackers (Debian, Ubuntu, Oracle, Amazon Linux) list fixed package versions and timelines; use those to plan rollouts.
- For WSL2 on managed endpoints, ensure WSL kernel updates are applied (wsl --update) or that any custom WSL kernel used by your organization has been rebuilt with the patched upstream commit. Use wsl --status and uname -r to validate kernel version.
- For Azure Marketplace images, custom VM images, AKS node pools or managed images: verify image provenance and request updated images from image publishers if they have not yet published patched builds. If Microsoft later attests additional product families, incorporate that data into your automation.
- For slow‑update appliances or firmware, open support cases with the vendor and demand a backport or official statement. If the vendor cannot confirm a fix, isolate the appliance from untrusted network segments where feasible.
- Validate post‑patch by re-running representative workloads that exercise the affected code paths and by reviewing kernel logs for Oops or KASAN traces. If you reproduced the issue in test before patching, reproduce again after patch to confirm the fix.
Detection and monitoring — signals that matter
- Kernel Oops/KASAN messages referencing crypto/essiv or related AEAD internals.
- Unexpected kernel oopses or crashes during crypto operations (for example, disk encryption operations).
- Unexpected behavior during in‑place encryption operations or decryption failure paths.
If you see these signals on hosts with the suspect kernel build, prioritize those hosts for immediate patching.
Strengths and limitations of Microsoft’s CSAF/VEX attestation model
Strengths:- Deterministic automation: product‑level VEX/CSAF entries let organizations automate triage for named artifacts (Azure Linux in this case). Microsoft’s approach gives Azure Linux operators a clear, machine‑readable “Known Affected / Under Investigation / Fixed” signal to drive remediation.
- Transparency commitment: publishing CSAF/VEX encourages faster, predictable remediation and reduces noisy, ambiguous CVE alerts when an artifact is clearly out of scope.
- Phased coverage: attestations are published as inventories complete. A product‑level attestation for Azure Linux is not a guarantee that other Microsoft artifacts (WSL kernels, azure‑tuned kernels, marketplace images, device images) were scanned or do not include the same upstream code. Absence of attestation equals “not yet attested,” not “not present.”
- Hidden carriers: statically linked or embedded uses of third‑party code, vendor images repackaging upstream kernels, and internal appliance images might still carry the vulnerable code even if the vendor’s public attestation doesn’t mention them yet.
- Automation pitfalls: relying solely on a single vendor attestation without artifact verification can leave gaps. Do not treat VEX omission as a green light; use it as one authoritative signal among others.
Concrete checklist for administrators (actionable)
- Inventory: list all Azure VMs, Marketplace images, custom images, AKS node pools, WSL installations and any Microsoft‑published Linux kernels you run.
- Verify: run the artifact checks above (uname -r, /boot/config, package changelogs, module searches).
- Patch: apply vendor kernel updates that include the upstream commit(s) and reboot.
- Validate: rerun representative workloads and confirm no crypto‑path oopses/logs remain.
- Communicate: for managed images and third‑party Marketplace images, open support channels and demand rebuilds or a VEX/CSAF attestation.
- Automate: ingest Microsoft’s CSAF/VEX files (and vendor advisories) into your vulnerability management so Azure Linux attestations are handled automatically while other artifacts remain in a manual verification queue.
Unverifiable claims and cautionary notes
- Microsoft’s attestation statement reflects the inventory status at publication time. If you see Microsoft’s advisory for Azure Linux and observe no mention of WSL or other SKUs, that absence is not independent proof they don’t contain the vulnerable code — it only means they have not yet published attestations for those products. Microsoft has explicitly committed to updating VEX entries when additional products are identified. Treat any claim of “only Azure Linux is affected” as provisional until additional attestations or independent artifact checks confirm exclusivity.
- If you require an immediate, authoritative answer for a given Microsoft artifact (for example, a specific Marketplace appliance or a WSL kernel version in your fleet), do not wait for vendor attestations — perform the artifact checks listed in this article and open vendor support cases where necessary.
Conclusion
Microsoft’s MSRC telegraf that “Azure Linux includes this open‑source library and is therefore potentially affected” is a precise, valuable signal: it documents the inventory result for a named product family and helps Azure Linux operators prioritize action. However, it is not an exclusionary statement that other Microsoft products cannot include the same upstream code; many Microsoft artifacts ship or operate Linux kernels and thus require per‑artifact verification.The correct operational posture is to treat the Azure Linux attestation as an authoritative “yes” for that product, and to treat all other Microsoft artifacts as unverified until checked. Use the verification checklist, patch promptly where the check shows exposure, and incorporate Microsoft’s CSAF/VEX feeds into automation to accelerate future triage. Multiple independent vendor trackers and the upstream kernel commits confirm the ESSIV ssize fix; administrators should follow a practical verify‑patch‑validate loop and demand vendor attestations or backports for managed/third‑party images when those artifacts are in use.
Source: MSRC Security Update Guide - Microsoft Security Response Center