Microsoft’s public attestation that Azure Linux “includes this open‑source library and is therefore potentially affected” should be read exactly that way: an authoritative, product‑level mapping for Azure Linux — not a categorical statement that no other Microsoft product can or does include the vulnerable OpenSSL code tied to CVE‑2022‑4304. Microsoft has explicitly committed to expand the CVE/VEX mappings if further internal inventories find additional affected Microsoft artifacts, but operators must not treat a single attestation as proof of global absence elsewhere in Microsoft’s product portfolio.
Background / Overview
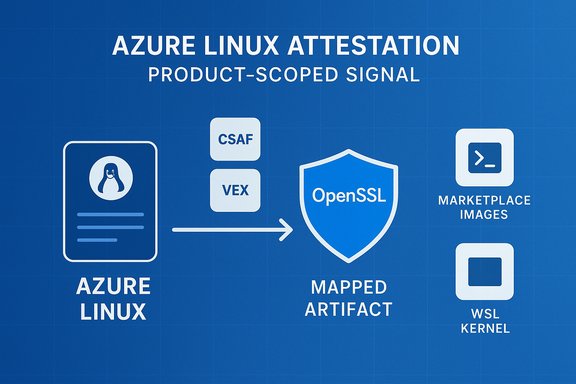
CVE‑2022‑4304 is a timing‑oracle side‑channel in OpenSSL’s RSA decryption code that can, under the right circumstances, enable a Bleichenbacher‑style attack to recover plaintext from many trial decryptions. The bug affects multiple OpenSSL branches (1.0.2, 1.1.1 and 3.0.x families) and vendors published fixes in the appropriate releases; operators were advised to update to OpenSSL 3.0.8, 1.1.1t or equivalent patched packages. Microsoft’s Security Response Center (MSRC) took a pragmatic, machine‑readable approach to third‑party CVE mapping by starting its CSAF/VEX rollout with Azure Linux: Microsoft published a VEX/CSAF attestation showing Azure Linux contains the implicated OpenSSL component and is therefore potentially affected, and it pledged to update the CVE record if additional Microsoft products are later found to ship the vulnerable library. That published attestation is product scoped — a statement about the inventory Microsoft has completed for that product family.Independent distributors and vendors (Ubuntu, Red Hat, SUSE, Oracle, AWS, etc. tracked CVE‑2022‑4304, issued distribution patches and, in many cases, documented remediation dates and fixed package versions. These independent records give operators multiple cross‑checks for technical details and remediation timelines beyond the vendor attestation.
What Microsoft actually said — a precise reading
Microsoft’s wording around CVE mappings for third‑party components follows a consistent template: publish what we have validated and commit to expand the published mapping as inventory work completes across more product families. In practice this means:- When MSRC says “Azure Linux includes this open‑source library and is therefore potentially affected,” Microsoft is reporting the outcome of a completed inventory for that distribution family. The VEX/CSAF file published for the CVE maps the vulnerable upstream component to Azure Linux SKUs so customer automation can react deterministically.
- When MSRC adds “If impact to additional products is identified, we will update the CVE,” that is a commitment to expand the attestation if and when Microsoft’s internal pipelines identify other Microsoft artifacts (images, kernels, binaries) that ship the same vulnerable component. It is not a denial that other Microsoft artifacts could ever include the component; it is simply a statement about current, validated scope.
Why “Azure Linux only” is the wrong operational question
Technically speaking, whether any Microsoft product includes a given open‑source library is a function of build‑time provenance and per‑artifact configuration. There are multiple concrete reasons a single product attestation does not equal exclusivity:- Build‑time variability: Different images, kernels or product builds can include or omit the same upstream library based on compile flags, packaging choices, or inclusion policies. Presence is a per‑artifact property, not a per‑vendor monolith.
- Statically linked binaries: Many services and appliances ship statically compiled OpenSSL or other binaries. Updating a system package does not remove a statically embedded vulnerable OpenSSL binary inside an appliance image; those artifacts must be rebuilt and redeployed.
- Multiple Microsoft distribution surfaces: Microsoft publishes many distinct artifacts — Azure Linux images, linux‑azure (kernel) packages, Marketplace VM images, AKS node images, curated container images, WSL kernels and agent binaries — each of which must be inventoried independently. Any of them might carry OpenSSL in the affected version.
- Marketplace and partner images: Third‑party or partner images hosted in the Azure Marketplace are often built and maintained by external vendors; they may carry older or unpatched libraries even if Microsoft’s own Azure Linux images are updated. Treat Marketplace images as distinct vendor artifacts to be validated.
Realistic exposure model for CVE‑2022‑4304
CVE‑2022‑4304 is a remote timing‑oracle that requires the attacker to send a very large number of trial ciphertexts and measure processing time accurately. Its real‑world exploitability depends on several conditions:- The vulnerable OpenSSL implementation must be used to perform RSA decryption on attacker‑controlled ciphertexts (for example, during TLS negative path, or when a service accepts RSA‑encrypted blobs).
- The attacker needs the ability to send many trial requests and measure response timing precision across the network.
- Environment noise, network jitter, and modern mitigations (constant‑time code paths, blunting of timing variance) make large‑scale exploitation non‑trivial in many setups.
Cross‑validation: independent sources you should consult
When a major third‑party vulnerability is involved, rely on multiple vendor channels for confirmation:- OpenSSL’s official security advisory (technical description and fixed OpenSSL releases).
- Distribution security pages (Ubuntu, Red Hat, SUSE, Oracle) that track which packaged releases are fixed and when.
- Product vendor and CISA advisories where the vulnerability appears in embedded or ICS products (some vendors published tailored mitigation guidance).
- Microsoft’s machine‑readable CSAF/VEX attestation for Azure Linux (useful for automation and image inventory).
Practical verification checklist — what to check in Microsoft environments
To reduce risk and avoid over‑reliance on a single attestation, implement this pragmatic checklist across your Microsoft‑hosted estate:- Inventory images and artifacts
- List all Azure VM images, Marketplace images, custom images and AKS node pools you run.
- Identify WSL kernels and any Microsoft‑published kernels used on endpoints.
- Track container images (curated Azure ML images, curated framework images) and check their base OS and OpenSSL versions.
- Detect packaged and embedded OpenSSL
- On Linux hosts: check package manager for openssl versions.
- Debian/Ubuntu: dpkg -l | grep openssl
- RHEL/SUSE: rpm -qa | grep openssl
- Inspect container image layers for /usr/lib or /usr/local/ssl and run openssl version inside ephemeral containers.
- Search for statically linked OpenSSL binaries: strings /path/to/binary | grep -i 'OpenSSL' and look for version tags.
- On Linux hosts: check package manager for openssl versions.
- Check Microsoft‑published VEX/CSAF files (automate this)
- Consume MSRC’s CSAF/VEX attestation for the CVE to learn which Azure Linux SKUs and component IDs Microsoft has mapped. Treat that data as authoritative for Azure Linux automation.
- Prioritize remediation
- Patch systems to the fixed OpenSSL releases recommended by OpenSSL and distributions (for example, OpenSSL 3.0.8 or later for the 3.0 branch).
- Rebuild and redeploy any statically linked binaries or vendor images that include vulnerable OpenSSL rather than assuming OS package updates suffice.
- For marketplace/third‑party images, open support cases with the image publisher and request rebuilds or patched releases if the vendor does not publish one promptly.
- Add runtime mitigations where immediate patching is hard
- Rate‑limit and throttle decryption endpoints to reduce the feasibility of high‑volume trial ciphertext attacks.
- Use network segmentation and WAF fronting to prevent unauthenticated access to decryption endpoints.
- Log and monitor for anomalous request patterns that match trial‑and‑measure exploitation models.
Commands and quick checks (operational ready‑to‑use)
- Check openssl version on a host:
- openssl version -a
- Inspect container image for OpenSSL:
- docker run --rm image:tag openssl version || true
- Find statically linked OpenSSL in binaries:
- strings /usr/bin/mybinary | grep -i 'OpenSSL' || true
- For Azure image inventories:
- Use your cloud asset inventory (resource graph, image registry) to list all VM images and tags; cross‑reference SKUs with MSRC VEX attestation for deterministic mapping.
Strengths in Microsoft’s approach — and remaining gaps
Strengths:- Microsoft’s publication of machine‑readable CSAF/VEX attestations for Azure Linux provides a deterministic automation signal that simplifies triage and prioritization for customers running those images. That’s a meaningful step toward supply‑chain transparency.
- Publishing an explicit commitment to update CVE mappings when new product impact is found makes Microsoft’s process auditable and predictable rather than opaque.
- The attestation is phased: starting with Azure Linux reduces initial uncertainty for that product but leaves a window where other Microsoft SKUs may be un‑mapped publicly. Customers must verify other Microsoft artifacts they run instead of assuming safety.
- Statically linked binaries and third‑party marketplace images create a “long tail” that requires vendor coordination and rebuilds — OS package updates alone are insufficient for these cases.
- Timing‑oracle vulnerabilities like CVE‑2022‑4304 can be noisy to detect in production; detection strategies need tuned signatures, rate metrics, and behavioral baseline analysis to spot large‑scale trial patterns.
Recommended remediation timeline and priorities
- Immediate (0–7 days)
- Map and patch all known Azure Linux images you run using Microsoft’s VEX as a starting signal. Apply vendor patches and reboot where needed.
- Identify any externally exposed services that perform RSA decryption and apply rate limits or traffic filtering.
- Short term (7–30 days)
- Inventory Marketplace and third‑party images; open vendor support cases and schedule rebuilds for images that include vulnerable OpenSSL.
- Scan for statically linked OpenSSL binaries and schedule rebuilds with patched OpenSSL versions where found.
- Medium term (30–90 days)
- Update CI/CD toolchains to use fixed OpenSSL releases and enforce rebuilds for any previously built artifacts that included vulnerable code.
- Automate ingestion of MSRC VEX/CSAF feeds to keep product‑level mappings current and reduce manual triage overhead.
When absence of evidence is not evidence of absence — a caution
Microsoft’s Azure Linux attestation is valuable and reduces uncertainty for Azure Linux customers, but absence of other Microsoft product entries in a VEX file is not proof those products are inherently safe. There are multiple technical pathways — different build trees, static linking, marketplace images, third‑party vendors — that can cause the same vulnerable library to appear in other artifacts long after a vendor publishes a single product attestation. Operators should assume a conservative posture: verify artifacts and automate VEX ingestion rather than relying on a single vendor statement.If you cannot confirm absence through artifact inspection, assume potential exposure and prioritize mitigations for externally facing endpoints that perform RSA decryption.
Final assessment for WindowsForum readers
- Short answer: Azure Linux is the only Microsoft product Microsoft has publicly attested as including the vulnerable OpenSSL component for CVE‑2022‑4304 at the time of the attestation, but it is not the only Microsoft surface that could conceivably ship the vulnerable library. Treat the Azure Linux attestation as authoritative for that product, and continue to inventory and verify other Microsoft artifacts you run.
- Tactical action: Inventory, detect, rebuild, and patch. Use MSRC’s CSAF/VEX attestation as an automation input for Azure Linux images, but do not stop your verification at the VEX boundary — check marketplace images, container images, statically linked binaries, and any other Microsoft‑distributed artifacts in your environment.
- Technical verification: cross‑check vendor advisories (OpenSSL, distro trackers), Microsoft’s VEX files, and your own artifact inventories to make deterministic decisions.
Microsoft’s transparency step — publishing CSAF/VEX mappings and promising to expand product coverage — materially improves customers’ ability to automate and prioritize remediation. That improvement is real and useful. However, the operational reality of software supply chains and static linking means that the single attestation is an important signal, not a comprehensive guarantee. Treat it as the first stop in a short, methodical verification and remediation workflow that closes the remaining gaps in your estate.
Source: MSRC Security Update Guide - Microsoft Security Response Center