Microsoft’s brief advisory language — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate for the product it names, but it is not an exclusive statement that no other Microsoft product could include the same vulnerable code; in short: Azure Linux is the only Microsoft product Microsoft has publicly attested contains the implicated upstream component so far, but absence of a public attestation does not prove other Microsoft artifacts are unaffected.
The item tracked as CVE‑2023‑52733 concerns an upstream Linux kernel fix described as a potential buffer overflow in the s390 decompression code — the short technical description: “s390/decompressor: specify __decompress() buf len to avoid overflow.” Upstream kernel maintainers implemented a targeted change to ensure the decompressor is given an explicit output buffer length so it cannot write past the intended area; multiple downstream trackers and OSV entries list the upstream fix and the kernel versions that received it.
At the same time, the CVE record for CVE‑2023‑52733 in public databases was later marked “Rejected” by the assigning authority: the NVD entry now shows the CVE ID as rejected or withdrawn by its CVE Numbering Authority. That administrative status means the canonical CVE entry is not treated as an active, vendor‑backed identifier in the same way as a normal CVE record, although the underlying upstream patch and advisory text remain publicly visible in kernel trees and distributor advisories.
Microsoft’s Security Response Center (MSRC) practice over the last two years has been to publish short product‑scoped attestations when its inventory work confirms that a particular Microsoft‑branded Linux artifact includes an upstream component addressed by an upstream fix. Those short advisories commonly say something like “Azure Linux includes this open‑source library and is therefore potentially affected,” and Microsoft has stated it will expand CVE or VEX/CSAF mappings if other Microsoft products are found to ship the component. That phrasing is precise: it as a known carrier, but it does not automatically guarantee exclusivity across the entire Microsoft portfolio.
The long‑term security benefit comes from two complementary practices:
CVE‑level administration, upstream kernel commits, vendor mapping and product attestations each carry different operational meanings. For defenders the practical question is not whether Microsoft has named Azure Linux — it is whether your specific hosts or images run a kernel binary that includes the unpatched code path. Treat Microsoft’s Azure Linux attestation as authoritative for Azure Linux images, then verify other Microsoft artifacts in your estate using kernel versions, kernel configs, and vendor SBOM/VEX attestations. If you cannot verify, assume a conservative remediation posture: update or replace the artifact with a vendor‑patched build.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The item tracked as CVE‑2023‑52733 concerns an upstream Linux kernel fix described as a potential buffer overflow in the s390 decompression code — the short technical description: “s390/decompressor: specify __decompress() buf len to avoid overflow.” Upstream kernel maintainers implemented a targeted change to ensure the decompressor is given an explicit output buffer length so it cannot write past the intended area; multiple downstream trackers and OSV entries list the upstream fix and the kernel versions that received it.At the same time, the CVE record for CVE‑2023‑52733 in public databases was later marked “Rejected” by the assigning authority: the NVD entry now shows the CVE ID as rejected or withdrawn by its CVE Numbering Authority. That administrative status means the canonical CVE entry is not treated as an active, vendor‑backed identifier in the same way as a normal CVE record, although the underlying upstream patch and advisory text remain publicly visible in kernel trees and distributor advisories.
Microsoft’s Security Response Center (MSRC) practice over the last two years has been to publish short product‑scoped attestations when its inventory work confirms that a particular Microsoft‑branded Linux artifact includes an upstream component addressed by an upstream fix. Those short advisories commonly say something like “Azure Linux includes this open‑source library and is therefore potentially affected,” and Microsoft has stated it will expand CVE or VEX/CSAF mappings if other Microsoft products are found to ship the component. That phrasing is precise: it as a known carrier, but it does not automatically guarantee exclusivity across the entire Microsoft portfolio.
What “Azure Linux attested” actually means — unpacking the jargon
Product‑scoped attestation vs. exclusivity
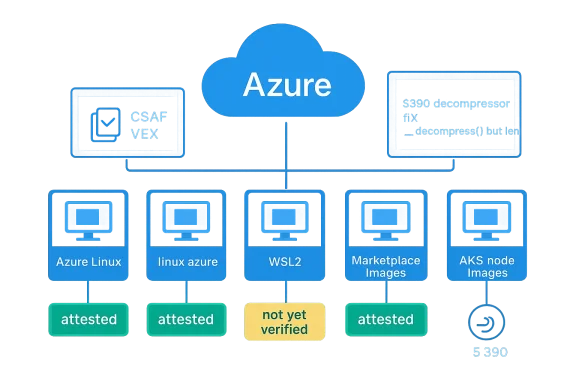
When Microsoft says “Azure Linux includes this open‑source library and is therefore potentially affected,” read that as an inventory statement about that product family — not a blanket negative for all other Microsoft artifacts. In plain language:- Affirmative for Azure Linux: Microsoft has completed an inventory check for the Azure Linux images it ships and confirmed the upstream code in question is present there.
- Non‑affirmative for other artifacts: Microsoft has not necessarily completed the same inventory for every kernel artifact it ships (for example, WSL2 kernels, linux‑azure kernels baked into specific VM SKUs, kernels in Marketplace VM images, AKS node images, partner appliances, or embedded kernels inside other products). Until Microsoft issues a similar attestation for those artifacts — or until end users can independently verify via SBOM/VEX/CSAF or by inspecting kernel versions and configs — those artifacts should be treated as not yet verified rather than definitively clean.
Why vendors single out one distro or image
There are pragmatic reasons why vendors call out one distribution or image first:- Distributors often operate a prioritized patch-and-attest workflow. A cloud provider (or a vendor) will inventory the images they publish most broadly — e.g., the canonical Azure Linux images — and publish VEX/CSAF attestations for those artifacts first.
- Linux kernel exposure depends on kernel configuration and build choices. The same upstream source code does not always end up in every kernel binary; kernel subsystems and drivers are enabled or disabled at compile time. So a vendor attestation that a given image contains the component is valuable operationally, but it cannot prove that a different image — built with different config or kernel version — is free of the same code path unless explicitly checked.
What the record shows for CVE‑2023‑52733
Administrative status: Rejected/Withdrawn CVE record
Public vulnerability trackers indicate CVE‑2023‑52733 was entered to track a kernel change but later the CVE record was marked “Rejected” by the CNA. That administrative status is recorded in the NVD entry and in several CVE aggregators. Rejection of a CVE identifier is an administrative outcome and does not erase the upstream code change or its security rationale; it simply signals that the assigning authority removed or withdrew the CVE entry for bookkeeping reasons. Researchers and downstream vendor advisories still reference the kernel fix by commit and by vendor advisories.Upstream technical fix and affected kernel ranges
Upstream kernel maintainers applied surgical commits to the s390 decompressor to specify the __decompress() output length and thus bound writes. Open‑source vulnerability indexes and OSV/GSD entries list the commit(s) that fixed the issue and identify one or more stable kernel versions that include the fix (for example, fixes landed on stable branches such as 5.15.95 and 6.1.13 in distributor mappings). Those kernel fixes are the authoritative technical artefact you should check against when deciding whether a particular kernel binary is patched.Downstream vendors and distro status
Several Linux distributions and downstream trackers listed the same upstream description and mapped the fix into their advisories; SUSE, some Ubuntu trackers and vendor advisories, and cloud distro tracking pages registered the upstream change and declared status for their kernels. This corroboration from multiple maintainers is how defenders can cross‑check the real world impact and patch availability.Is Azure Linux the only Microsoft product that could be affected?
Short answer: No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested to include the implicated upstream component for this advisory, but other Microsoft‑distributed artifacts may also ship the same upstream code depending on their kernel versions and build configuration. Treat Microsoft’s Azure Linux attestation as an authoritative inventory statement for that product family, and treat the absence of attestations for other artifacts as “not yet checked” rather than “not affected.”Why this distinction matters for defenders
- Large enterprises and cloud operators do not run only one Microsoft image. You may have WSL2, Azure Marketplace images, Linux kernels embedded into appliance images, linux‑azure kernels baked into VM SKUs, or custom images built from Microsoft published sources.
- Kernel configuration varies. The vulnerable code path in the kernel will only be present if the kernel was built with the relevant subsystem/drivers enabled — something that differs between kernels even from the same vendor.
- Microsoft has committed to publishing machine‑readable CSAF/VEX attestations for Azure Linux and to update CVEs if additional products are identified. That is helpful, but it is an incremental transparency step rather than a warranty that no other Microsoft product contains the code.
Practical, actionable guidance (how to verify and mitigate across your estate)
Below are concrete steps defenders and platform operators should follow now. These are ordered so you can run quick checks first and escalate to deeper verification if needed.- Inventory the kernels and images you run
- List all Microsoft‑supplied Linux artifacts in use: Azure Linux images, linux‑azure kernels, WSL2 kernels on developer machines, Marketplace images, AKS node images, and partner/appliance images that bundle Microsoft kernels.
- If you use configuration management or an asset database, filter for images with “Azure”, “linux‑azure”, “WSL2”, or vendor strings indicating Microsoft origins.
- Identify kernel versions and build identifiers
- For each host or image, capture the kernel version string (uname -r) and, where possible, the full package release (e.g., distro kernel package version).
- Map those versions against the upstream kernel commits or the stable kernel versions that contain the fix (the upstream mapping to fixes was published in kernel trees and in OSV/GSd indexers). If a kernel version is equal to or newer than a fixed stable release (for example those stable branches that merged the fix), it is likely patched.
- Check kernel configuration for the relevant subsystem (deeper check)
- If you have access to the kernel config (usually /boot/config-<version>), grep for the specific subsystem or driver options that would enable the s390 decompressor code path.
- If the options are disabled, the binary may never carry the vulnerable path even if the kernel source had that code in it.
- Validate against vendor SBOM/VEX/CSAF data
- Where Microsoft has published machine‑readable VEX/CSAF attestations for Azure Linux, consume those attestations to confirm which components are present and whether a given artifact is marked “known affected”, “not affected”, or “fixed”. Microsoft has signaled an ongoing roll‑out of CSAF/VEX for Azure Linux; use those attestations for artifact‑level confirmation when available.
- Patch and/or replace images
- If your kernels are identified as vulnerable (or you cannot conclusively prove a kernel is not shipping the problematic code path), plan to update to patched kernel packages provided by the distro or by Microsoft for Azure Linux. Where vendor patches are unavailable, consider rebuilding or replacing the image with an updated, vendor‑patched image.
- Monitor Microsoft CVE/VEX updates
- Microsoft has committed to update CVE/VEX entries if additional products are found to be impacted. Subscribe to MSRC advisories for the relevant artifact families (Azure Linux, linux‑azure, WSL) and consume updated CSAF/VEX data as it appears.
Risk analysis: what to worry about and what not to overreact to
Realistic threat surface
- The s390 decompressor flaw is architecture‑specific (s390 is IBM mainframe architecture). For many organizations that run x86_64 or arm64 workloads, the immediate practical exposure is limited. However, the underlying pattern — that an upstream kernel change can alter decompression semantics and unexpectedly write past buffers — is the kind of subtle kernel‑level issue that justifies careful inventory and patch management for any kernel family you run. The public trackers and OSV entries document the architecture and the fix clearly.
- Local‑access requirement: multiple trackers indicate the attack vector is local (AV:L) and requires low to moderate privileges to exploit, so remote exploitation without an intermediate step is unlikely. Still, kernel vulnerabilities with local exploitability can be combined into chained attacks in multi‑tenant or exposed environments, so do not ignore them.
Administrative oddities: what “Rejected” CVE means in practice
- The “Rejected” CVE administrative status complicates automated tooling that expects to find a normal CVE descriptor. Many downstream vendors and trackers nonetheless reference the upstream patch and treat the change as a real security fix. Security teams should not treat the administrative rejection as a sign the problem never existed; instead, treat the kernel patch and distributor advisories as the primary technical source. Cross‑checking with the kernel commit and distro advisories is the correct defensive posture.
Microsoft’s transparency posture — improvement but not a guarantee
- Microsoft’s shift to publishing CSAF/VEX attestations (announced as a phased rollout beginning with Azure Linux) is a measurable transparency improvement: machine‑readable attestations make it possible to programmatically confirm artifact scope. But a VEX for Azure Linux does not substitute for explicit attestations for other Microsoft artifacts — defenders must still individually verify other Microsoft kernels in their environment until an attestation is published for each artifact.
Recommended communications for security teams and sysadmins
- Tell operators the short, defensible truth: “Microsoft confirmed Azure Linux images include the upstream code addressed by this upstream kernel fix. Microsoft has not yet attested or published the same mapping for every Microsoft artifact; we will treat all Microsoft‑supplied kernels in our environment as ‘not yet verified’ until we can confirm via kernel version, kernel config, or vendor VEX/CSAF.”
- Use the checklist above to triage your fleet quickly: inventory images, capture kernel versions, consult vendor advisories and the OSV/GSd references for the fixed commits, and patch or swap images where necessary.
- If you run multi‑tenant or IBM mainframe (s390) infrastructure, prioritize those hosts for verification since the upstream description implicates the s390 decompressor most directly.
Why defenders should care about per‑artifact attestations going forward
Microsoft’s practice of mapping a CVE or upstream kernel fix to a specific Microsoft product is operationally useful: it tells you which Microsoft images have been inventory‑checked and gives you a target for patching. But the IT reality is more complex: enterprise environments run dozens or hundreds of images, kernels and appliance bundles, and attackers don’t limit themselves to the single artifact a vendor calls out.The long‑term security benefit comes from two complementary practices:
- Vendors publishing detailed, machine‑readable SBOM/VEX attestations for each artifact they publish, and updating them promptly when new upstream fixes appear. Microsoft’s stated commitment to CSAF/VEX for Azure Linux is a step in this direction, but defenders need those attestations for every artifact in their dependency tree.
- Consumers maintaining an accurate, queryable asset inventory that links running images to vendor attestations and to the exact kernel version and config in use. When asset inventories and artifacts are both machine‑readable, automated cross‑checks can reliably answer “is this host affected?” without manual guesswork.
Bottom line (concise)
- Azure Linux is the only Microsoft product Microsoft has publicly attested as including the implicated upstream kernel component for this advisory; that attestation matters operationally for Azure Linux customers, but it is not an exclusive guarantee that no other Microsoft product contains the same code.
- CVE‑2023‑52733 as a CVE identifier is marked “Rejected” by the CNA in public CVE/NVD records, but the upstream kernel fix and downstream distributor advisories exist and should be the technical reference when verifying whether a specific kernel is patched. Do not let the administrative “Rejected” label create complacency.
- Operational action: inventory Microsoft kernel artifacts in your environment, map kernel versions and configs against the upstream fixed commits or distributor advisories, consume Microsoft VEX/CSAF attestations for Azure Linux when available, and patch or replace images that cannot be verified as patched.
Appendix — quick reference of authoritative sources to consult
- NVD record (CVE administrative status): consult the NVD entry for the CVE identifier to confirm administrative metadata.
- Upstream kernel commits and stable merges: check the kernel stable trees and the OSV/GSd entries for the commits that fix the decompressor behavior and the stable kernel versions that contain the fix.
- Downstream distributor advisories (SUSE, Ubuntu, Amazon, etc.): these vendor pages show how distributions mapped the upstream fix into their packages and whether your distro kernel packages are affected.
- Microsoft MSRC product attestation practice and CSAF/VEX roll‑out: Microsoft’s advisories for later Linux CVEs reflect the “Azure Linux includes this open‑source library…” language and the company’s plan to publish CSAF/VEX attestations for Azure Linux; use those attestations when available to confirm artifact scope.
CVE‑level administration, upstream kernel commits, vendor mapping and product attestations each carry different operational meanings. For defenders the practical question is not whether Microsoft has named Azure Linux — it is whether your specific hosts or images run a kernel binary that includes the unpatched code path. Treat Microsoft’s Azure Linux attestation as authoritative for Azure Linux images, then verify other Microsoft artifacts in your estate using kernel versions, kernel configs, and vendor SBOM/VEX attestations. If you cannot verify, assume a conservative remediation posture: update or replace the artifact with a vendor‑patched build.
Source: MSRC Security Update Guide - Microsoft Security Response Center