Microsoft’s public attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is an important, product‑scoped inventory signal — but it is not a categorical guarantee that no other Microsoft product contains the same vulnerable GnuTLS code; organizations must treat the attestation as authoritative for Azure Linux while performing artifact‑level discovery and mitigation across all Microsoft images, SDKs, agents and appliances they run.
In January 2024 the security community assigned CVE‑2024‑0553 to a timing side‑channel issue in GnuTLS that was characterized as an incomplete fix for an earlier vulnerability tracked as CVE‑2023‑5981. Multiple downstream vendors and distribution maintainers (Red Hat, Ubuntu, Amazon Linux, SUSE, Oracle Linux and others) published advisories and errata mapping the CVE to packaged GnuTLS releases and distributing patched versions. The core technical observation: response times for malformed ciphertexts in an RSA‑PSK ClientKeyExchange operation differed measurably from legitimate, correctly padded ciphertexts, creating an observable timing channel that could, under the right conditions, leak cryptographic information.
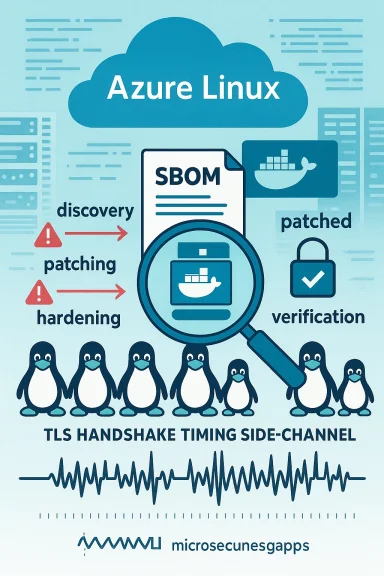
Shortly after those upstream and distro advisories, Microsoft’s Security Response Center (MSRC) published an entry noting that Azure Linux (Microsoft’s cloud-focused Linux distribution family) “includes this open‑source library and is therefore potentially affected.” The MSRC entry also reiterated Microsoft’s transparency commitment and its program to publish machine‑readable CSAF/VEX attestations (a roll‑out the company has tied to a timeline), and promised to update CVE mappings if additional Microsoft products are found to ship the implicated component.
This article explains what CVE‑2024‑0553 actually is, why it was labeled an “incomplete fix,” who is affected, what Microsoft’s statement does and doesn’t mean, how to hunt for the library across Microsoft artifacts, and practical mitigation and verification steps operations teams should take today.
But attestations are only as broad as the inventory that produced them. Modern vendors operate thousands of SKUs and artifacts; mapping every binary and image to every CVE takes time. Consequently:
What to do now — compact checklist:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
In January 2024 the security community assigned CVE‑2024‑0553 to a timing side‑channel issue in GnuTLS that was characterized as an incomplete fix for an earlier vulnerability tracked as CVE‑2023‑5981. Multiple downstream vendors and distribution maintainers (Red Hat, Ubuntu, Amazon Linux, SUSE, Oracle Linux and others) published advisories and errata mapping the CVE to packaged GnuTLS releases and distributing patched versions. The core technical observation: response times for malformed ciphertexts in an RSA‑PSK ClientKeyExchange operation differed measurably from legitimate, correctly padded ciphertexts, creating an observable timing channel that could, under the right conditions, leak cryptographic information.Shortly after those upstream and distro advisories, Microsoft’s Security Response Center (MSRC) published an entry noting that Azure Linux (Microsoft’s cloud-focused Linux distribution family) “includes this open‑source library and is therefore potentially affected.” The MSRC entry also reiterated Microsoft’s transparency commitment and its program to publish machine‑readable CSAF/VEX attestations (a roll‑out the company has tied to a timeline), and promised to update CVE mappings if additional Microsoft products are found to ship the implicated component.
This article explains what CVE‑2024‑0553 actually is, why it was labeled an “incomplete fix,” who is affected, what Microsoft’s statement does and doesn’t mean, how to hunt for the library across Microsoft artifacts, and practical mitigation and verification steps operations teams should take today.
What CVE‑2024‑0553 is — technical summary
The vulnerability in plain terms
- The bug affects GnuTLS, an open‑source TLS/SSL library used by many Linux distributions, system services and userland applications.
- The observable symptom is a timing discrepancy when GnuTLS processes malformed RSA ciphertexts in an RSA‑PSK ClientKeyExchange path. In short: malformed inputs and properly padded inputs are handled with measurably different response times.
- An attacker who can repeatedly interact with a target TLS endpoint and measure timing with sufficient resolution could exploit that channel to infer secret material — for example, partial information from cryptographic operations — eventually turning a timing leak into a confidentiality compromise.
Why it’s an “incomplete fix”
- CVE‑2024‑0553 was issued as a follow‑up after initial fixes for CVE‑2023‑5981 proved insufficient in some code paths or configurations. The label “incomplete fix” means the first corrective changes did not close every observable timing vector, and additional patches or mitigations were required.
- Multiple downstream distributors flagged it and shipped iterative patches; vendors documented which packaged releases include the corrected behavior.
Realistic exploitability and scope
- Timing attacks require repeated, measurable interactions and generally a high degree of timing precision. Practical exploitation is easier when:
- The attacker can measure network responses with low jitter (e.g., in the same cloud region or on the same host network).
- The vulnerable ciphersuite or protocol path (RSA‑PSK in this case) is enabled and actually used by a server.
- The target is not behind substantial noise or latency that would mask microsecond differences.
- While the theoretical confidentiality impact can be high, real‑world exploitation is nontrivial and depends on the environment, enabled ciphers, and network conditions. Nevertheless, vendors treated the issue seriously and pushed updates, because timing channels are a common vector for local and remote cryptographic attacks.
What Microsoft said — parsing the MSRC language
Microsoft’s published CVE entry includes the statement quoted by the user: that Azure Linux includes the implicated library and is therefore potentially affected, and that Microsoft will update CVE attestations if additional products are identified. There are three key takeaways from that messaging:- Product‑scoped attestation (authoritative for Azure Linux). Microsoft has inspected Azure Linux images/build artifacts and verified the presence of the upstream component. That makes Azure Linux a confirmed product in scope for remediation guidance.
- Transparency and VEX/CSAF commitment. Microsoft signaled a procedural promise: as it completes inventories for additional product families, it will publish machine‑readable VEX/CSAF attestations and update CVE mappings. That is useful for automation and security orchestration.
- Not an exclusivity guarantee. The MSRC language is not a statement that no other Microsoft product contains the same library. It is an attestation for Azure Linux only — absence of mention is absence of attestation, not proof of absence.
Is Azure Linux the only Microsoft product potentially affected?
Short answer: No — not necessarily. Longer answer below.What we can say with confidence
- Microsoft publicly attested Azure Linux as a product that carries the vulnerable open‑source library. That factual statement is authoritative for Azure Linux images Microsoft inspected.
- Multiple independent vendor advisories (distribution maintainers like Red Hat, Ubuntu, Amazon Linux and SUSE) also tracked and patched CVE‑2024‑0553, confirming the underlying technical issue and the required package updates.
What we cannot prove remotely (and why you must verify)
- Microsoft’s attestation does not prove that Azure Linux is the only Microsoft product to ever ship GnuTLS. Microsoft has a vast portfolio: cloud VM images, container base images, SDKs, extensions, agents, WSL distributions, appliance images, and partner‑branded marketplace images. Any of those artifacts could, depending on build choices, include GnuTLS.
- Some Microsoft offerings are thin wrappers around third‑party images (for example, marketplace VM images or container roots), and those artifacts may or may not be covered by Microsoft’s internal inventory runs.
- Therefore, customers should assume that other Microsoft artifacts could be carriers until proven otherwise by artifact inspection or authoritative VEX/CSAF attestations.
Practical risk scenarios to consider
- Azure Linux VMs and images: confirmed in scope — patch now.
- Azure Marketplace Linux images (third‑party): may contain GnuTLS; check the specific image vendor and image SBOM.
- Microsoft‑published container base images used in Azure Container Instances or App Service: could carry vulnerable packages depending on the base distribution — treat them as unverified until scanned.
- Windows Subsystem for Linux (WSL) distributions distributed via Microsoft Store: these are distro artifacts (canonical/Ubuntu, etc.) and will include GnuTLS if the upstream distro package includes it. Verify the distro package versions in the WSL instance.
- Microsoft managed services that rely on Linux internals (some infrastructure agents or PaaS components): risk depends on whether the service embeds GnuTLS or a different TLS stack (OpenSSL, SChannel, NSS, etc.).
How to discover GnuTLS presence across Microsoft artifacts (artifact‑level discovery)
The correct operational approach is artifact‑level verification — don’t rely solely on vendor‑level attestations. Here’s a practical checklist and set of techniques to find instances of GnuTLS in Microsoft‑supplied artifacts you run.1) Use package inventory on running systems
- For RPM‑based systems:
- rpm -qa | grep -i gnutls
- dnf list installed gnutls*
- For Debian/Ubuntu based systems:
- dpkg -l | grep -i gnutls
- apt list --installed | grep gnutls
These commands show whether the package is installed in the running image or VM.
2) Inspect container images and base layers
- Export or run an interactive shell in the container and run the package checks above.
- Use image scanners (open source or commercial) to enumerate packages in the image filesystem; modern scanners will flag known CVEs and report fixed package versions.
3) Examine binary dependencies and embedded libraries
- ldd /path/to/binary | grep gnutls
- strings /path/to/binary | grep -i gnutls
Some apps statically link or embed library code. In those cases you may need more advanced binary analysis (symbol tables, ELF analysis) or rebuild/redeploy with updated upstream library.
4) Look at SBOMs and VEX/CSAF attestations
- If Microsoft or the image vendor publishes an SBOM for an image or agent, use that to locate occurrences of gnutls.
- Keep an eye on Microsoft’s machine‑readable VEX/CSAF entries; they are designed to automate inventory matching. But remember: if a product is not in the VEX output, that is not proof the product is clean.
5) Scan code and build scripts in CI/CD
- Check your pipelines for build images and base images that include gnutls in their dependency trees.
- Rebuild images using patched base packages and re‑publish them to your registries.
Mitigation & patching guidance — prioritized, actionable steps
If you run Azure Linux images: prioritize patching. Microsoft’s product attestation specifically signals Azure Linux users to remediate first. Beyond that, follow these steps:- Inventory
- Run the discovery checklist above across all Microsoft images, VMs, container registries, and agents you use.
- Build a simple tracker: artifact name → SHA or version → gnutls present? → patched version available?
- Patch or update packages
- For distribution packages, upgrade to the vendor‑provided patched gnutls package as advised by your distro vendor (Red Hat, Ubuntu, Amazon Linux, SUSE, Oracle Linux, etc.).
- For container images, rebuild images from a patched base or explicitly upgrade the package in the Dockerfile and re‑publish the image.
- For statically linked binaries or appliances, request an updated build from the vendor, or rebuild from source with the patched library.
- Temporary mitigations where immediate patching is impractical
- Disable RSA‑PSK ciphersuites (or PSK usage) in server configuration if your service does not require PSK. Many deployments never use RSA‑PSK; disabling unnecessary ciphers reduces exposure.
- Apply network segmentation and rate limits to reduce the attacker’s ability to obtain high‑quality timing measurements.
- Increase logging and anomaly detection on TLS handshakes to detect unusual, repeated attempt patterns.
- Verify and validate fixes
- After patching, validate that the updated package version is present (rpm/dpkg checks) and that containers were rebuilt and redeployed.
- Run regression tests for TLS interoperability and ensure disabled ciphers do not break legitimate clients.
- Use scanners to confirm CVE‑2024‑0553 no longer reports for the artifact.
- Document and communicate
- Record which artifacts were patched, when, and what versions were deployed.
- If you operate a multi‑tenant environment, notify impacted customers about the mitigation steps and timelines.
Practical commands and checklist for sysadmins (concise)
- Identify installed GnuTLS packages:
- RPM: rpm -qa | grep -i gnutls
- APT: dpkg -l | grep -i gnutls
- Find dynamic dependencies:
- ldd $(which <binary>) | grep gnutls
- Search containers:
- docker run --rm -it <image> /bin/sh -c "apk info | grep -i gnutls" (or use apt/rpm inside image)
- Disable RSA‑PSK ciphers in common servers (conceptual):
- For servers using GnuTLS API-configured ciphers, remove PSK/RSA‑PSK from the cipher list.
- For nginx/Apache/OpenSSL-based services, ensure PSK and RSA‑PSK aren’t enabled in your TLS configuration.
- Rebuild images and redeploy; then confirm updated package:
- rpm -q gnutls
- apt-cache policy libgnutls30
Why vendor attestations matter — and their limits
Vendor attestations like Microsoft’s Azure Linux mapping are powerful because they give customers a precise remediation trigger: a confirmed, product‑scoped signal to patch. Publishing VEX/CSAF data is an industry best practice that enables automated risk management in large estates.But attestations are only as broad as the inventory that produced them. Modern vendors operate thousands of SKUs and artifacts; mapping every binary and image to every CVE takes time. Consequently:
- Treat an attestation as the starting point for remediation for the named product.
- Treat non‑attestation as a lack of inventory coverage, not as clearance.
- Use SBOM generation, image scanning, binary analysis, and CI/CD guardrails to close the remaining blind spots.
A practical incident response playbook for organizations
- Triage
- Confirm whether any externally facing endpoints use Azure Linux images or other Microsoft images you run.
- Run your discovery checklist across all environments.
- Prioritize
- Prioritize public, externally reachable services and high‑value targets (infrastructure that handles keys, secrets, certificates).
- Prioritize artifacts where GnuTLS is dynamically loaded or statically linked.
- Patch
- Apply vendor fixes for the distribution or rebuild images with fixed packages.
- Patch orchestration layers (container registries, image build pipelines) to prevent reintroduction of vulnerable images.
- Harden
- Disable unused ciphers (PSK/RSA‑PSK) and reduce the attack surface.
- Enforce network controls to reduce high‑precision timing measurement opportunities.
- Monitor
- Add detection rules for anomalous handshake patterns or frequent failed handshakes.
- Monitor vendor advisories and Microsoft VEX/CSAF feeds for updates and confirmations about additional product scope.
- Verify and report
- Re‑scan environments and verify remediation.
- If you discover Microsoft‑published artifacts that carry vulnerable GnuTLS but are not in MSRC attestations, report that to Microsoft via coordinated disclosure channels so they can update mappings.
Risks, caveats and unanswered questions
- Exposure estimate uncertainty: timing attacks require high fidelity measurements. In many real‑world deployments — high latency WAN links, network jitter or load balancing — attacks are impractical. Yet in co‑located cloud contexts (same host or same rack), the risk materially increases.
- Vendor coverage lag: while many distributions patched quickly, some downstream images and appliances can lag behind. Marketplace images, third‑party appliances, and embedded devices may still carry vulnerable code.
- Microsoft product surface area: Microsoft has explicitly mapped Azure Linux and committed to expanding VEX/CSAF coverage. However, without an explicit attestation for other Microsoft products, you must assume they remain unverified until proven clean.
- Static linking: some binaries may statically embed GnuTLS code. Those cases require vendor rebuilds; a simple package update on the host will not remedy a statically linked vulnerable binary.
Final analysis and recommendations
CVE‑2024‑0553 is a notable timing side‑channel issue in GnuTLS that required iterative fixes across the ecosystem. Microsoft’s public attestation that Azure Linux includes the implicated library is an important operational signal that simplifies remediation for customers who use that distribution. However, that attestation should not be treated as a universal safety net for every Microsoft image, agent or SDK.What to do now — compact checklist:
- If you run Azure Linux images: patch immediately using the vendor guidance and rebuild any dependent containers or images that originate from Azure Linux base images.
- Run artifact‑level discovery for all Microsoft‑provided images, appliances and agents you operate. Use SBOMs, image scanners and simple package queries to find gnutls instances.
- Disable PSK/RSA‑PSK ciphersuites where they are not required, as a defense‑in‑depth measure until all artifacts are patched.
- Rebuild and redeploy containers and statically linked binaries only from known good sources that incorporate the patched library.
- Track Microsoft’s VEX/CSAF outputs and vendor advisories; update your asset inventory accordingly and report any unattested Microsoft artifacts that are discovered to be carriers.
Source: MSRC Security Update Guide - Microsoft Security Response Center