Microsoft’s brief advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑scoped inventory statement, not a technical guarantee that no other Microsoft product can contain the same vulnerable code. In short: Azure Linux is the only Microsoft product Microsoft has publicly attested so far, but that attestation is deliberately scoped and limited; any Microsoft artifact that ships a Linux kernel build containing the Qualcomm PDR driver (or a backport of the vulnerable code) could also be a carrier until proven otherwise.
CVE‑2024‑43849 was assigned to a concurrency/locking issue in the Qualcomm PDR (power/domain/rail) area of the Linux kernel — described in upstream commit messages as a race or potential deadlock resolved by taking the appropriate mutexes around shared state such as
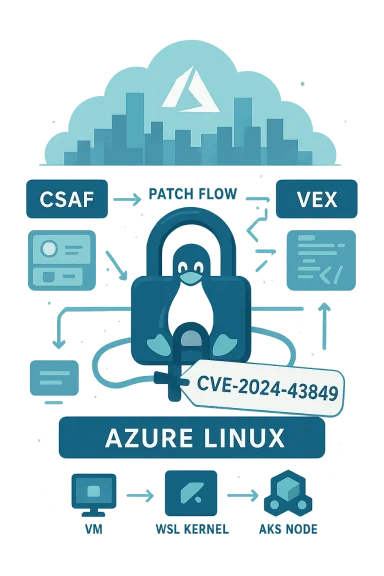
Microsoft’s Security Response Center (MSRC) published a short product statement for this CVE that reads effectively as: Azure Linux includes this open‑source library and is therefore potentially affected. That sentence is a deliberate, machine‑readable inventory claim: it confirms Azure Linux was inspected and found to include the implicated upstream component. Microsoft also says it will update the CVE/VEX mapping if it discovers additional Microsoft products that ship the same upstream code.
Historically, upstream fixes for such issues are small and low surface‑area; vendors typically backport the change into stable kernel trees quickly. That makes remediation operationally straightforward — but time‑sensitive. If a patched package is not yet available for an artifact, apply compensating controls (isolation, module blacklisting where acceptable, and constrained access) and plan an immediate patch window.
However, there are practical limitations:
The clock on operational exposure starts when images and kernels that include the vulnerable code remain in service; the fastest way to reduce your blast radius is targeted inventory, prioritized patching for attested products (Azure Linux), and immediate artifact verification for all Microsoft‑distributed kernel artifacts you use.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑43849 was assigned to a concurrency/locking issue in the Qualcomm PDR (power/domain/rail) area of the Linux kernel — described in upstream commit messages as a race or potential deadlock resolved by taking the appropriate mutexes around shared state such as locator_addr. The upstream fix protects the sensitive data path by correctly serializing access, preventing a kernel thread from blocking or deadlocking under certain sequences of operations. The vulnerability’s practical impact is primarily availability-oriented: under exploited or pathological conditions the kernel could deadlock or hang, producing denial‑of‑service for affected hosts.Microsoft’s Security Response Center (MSRC) published a short product statement for this CVE that reads effectively as: Azure Linux includes this open‑source library and is therefore potentially affected. That sentence is a deliberate, machine‑readable inventory claim: it confirms Azure Linux was inspected and found to include the implicated upstream component. Microsoft also says it will update the CVE/VEX mapping if it discovers additional Microsoft products that ship the same upstream code.
What Microsoft’s attestation actually means
Product‑scoped inventory, not exclusivity
When MSRC states a named product “includes” a component, that is an attestation of presence for that product family. It is not an exhaustive scan of every Microsoft binary, image, kernel build, Marketplace artifact, or developer bundle. Microsoft’s phrasing and its public rollout of CSAF/VEX attestations are intentionally phased: the company is starting with Azure Linux and will add other product attestations as inventories complete. Readers should therefore understand presence attested ≠ only place where the code exists.Why vendors publish product-scoped attestations
Large vendors ship thousands — sometimes millions — of distinct artifacts, images, and compiled binaries. Automated inventorying and backtracing a kernel driver to every published image is operationally heavy. Vendors commonly publish attestations for named product families as they close out those inventories; the attestation for a single product is meant to be actionable for customers who run that product, while the vendor continues to expand coverage. Microsoft explicitly committed to publishing machine‑readable VEX/CSAF attestations beginning in October 2025; this CVE entry follows that model.Why Azure Linux being named does not prove exclusivity
- The vulnerable code lives in upstream Linux kernel sources (drivers under the Qualcomm area). Any product that ships a Linux kernel binary built from an upstream tree that predates the fix — and that included the Qualcomm PDR code path — can include the same defect.
- Microsoft publishes multiple kernel‑based artifacts: Azure Marketplace images, Azure‑tuned kernels, WSL2 distributed kernels, AKS node images, and other management or telemetry images. Each compiled kernel must be checked individually for the presence of the vulnerable commit range and for local backports.
- Absence of a VEX attestation for a product is an absence of attestation, not evidence of absence. Until Microsoft or another authoritative inventory declares a product Not Affected, defenders should treat un‑attested Microsoft artifacts as unverified.
Where the same vulnerable code commonly appears (attack surface analysis)
The technical blast radius of a kernel driver CVE is defined by three concrete factors: the upstream commit range, the kernel configuration (the driver must be present/compiled in), and any vendor backports. These produce a variety of carriers within a vendor ecosystem:- Azure Marketplace VM images and curated base images — some images run vendor‑built kernels or distribution kernels that may include the driver.
- Microsoft‑distributed kernel binaries such as the WSL2 kernel image — a single kernel image used widely by developer hosts or CI agents can propagate a vulnerable driver across many endpoints.
- AKS node images or other managed node images that include a kernel build.
- Container images or appliances that embed a kernel or ship kernel modules. Even if userland does not contain the driver, container hosts running on vulnerable kernels may exhibit risk patterns.
- Internal build artifacts, CI images, or partner images redistributed via Marketplace — these can inherit kernel snapshots used at build time.
Practical, prioritized checklist for defenders (24–72 hour response)
- Prioritize Azure Linux systems
- Immediately inventory any VMs, AKS node pools, or other workloads running Azure Linux images and plan to apply Microsoft’s Azure Linux package updates or swap to patched Marketplace images as they become available. Microsoft’s attestation makes Azure Linux the high‑confidence remediation target.
- Run artifact discovery across Microsoft artifacts in your estate
- Search image registries, CI artifacts, VM images, and Marketplace base images for kernel versions and module lists.
- Query WSL2 kernel binaries distributed to developers and CI agents; confirm whether the WSL kernel build in your environment contains the Qualcomm PDR driver and whether it includes the upstream fix.
- Use binary and source‑level matching
- If you can obtain the upstream patch or the commit ID that fixed the deadlock, search for those function names, commit hashes, or file diffs in your kernel sources, packaged kernel source tarballs, and in /lib/modules and system.map in your images. This is the most reliable verification method.
- Short‑term mitigations while you patch
- Schedule reboots to pick up updated kernels or modules where patch packages exist.
- Consider temporary kernel module blacklisting where safe — note this can break device functionality; validate in staging.
- Isolate hosts that are high‑exposure (multi‑tenant VMs, build servers, CI runners) behind network controls; reduce local attack surface.
- Prepare a remediation playbook
- Map which teams own each artifact, who can deploy kernel updates, and your rollback strategy.
- Test vendor patches (or backports) in staging before broad deployment, especially when GPUs or specialized hardware are present.
Technical verification steps (artifact‑level detail)
- Collect kernel version strings and module lists from every Linux host and image under management (uname -r, lsmod, and inspect /lib/modules).
- Correlate kernel versions to upstream commit ranges and stable branch backports; vendor advisories and upstream stable trees list the git commits associated with the fix.
- If you maintain SBOMs for VM images and containers, map SBOM entries to the kernel version or package that contains the Qualcomm PDR code. Where SBOMs are absent, treat artifacts as unknown and add them to your discovery queue.
- Look for the driver name and related symbols (e.g., soc:qcom pdr, pdr_* symbols, or the specific function that was corrected around
locator_addrlocking). - Search compiled kernel images for known function names or commit hashes when available (strings/system.map grep).
- Use vendor advisories or upstream commit IDs as ground truth for binary matching.
Operational risk and exploitability — what to expect
Kernel driver deadlocks and concurrency defects are typically local or adjacent attack vectors: they are powerful for causing denial of service and can be triggered by local unprivileged users, misbehaving devices, or specific device interactions (hotplug, power management sequences, etc.). The practical exploitation path for CVE‑2024‑43849 is consistent with other Qualcomm PDR fixes: it requires the relevant driver code to be present and a triggering sequence that can provoke the contentious lock ordering or shared state access. For cloud operators, multi‑tenant hosts or shared build runners are higher priority to remediate because they have the greatest exposure to untrusted code paths.Historically, upstream fixes for such issues are small and low surface‑area; vendors typically backport the change into stable kernel trees quickly. That makes remediation operationally straightforward — but time‑sensitive. If a patched package is not yet available for an artifact, apply compensating controls (isolation, module blacklisting where acceptable, and constrained access) and plan an immediate patch window.
Cross‑verification and evidence you should gather
When you make remediation decisions, cross‑verify each assertion with at least two independent artifacts:- The upstream Linux kernel commit(s) or stable‑tree cherry‑picks that implement the fix (these are the canonical technical artefacts).
- Vendor advisories and distribution security trackers for package versions and backports.
- If available, Microsoft’s VEX/CSAF attestation for Azure Linux (the MSRC entry) and any subsequent product updates in the CVE mapping.
Recommended timeline and escalation path
- Immediate (hours)
- Inventory Azure Linux hosts and apply emergency updates if Microsoft published them.
- Scan image registries, WSL kernels used internally, and CI/CD base images for the driver’s presence.
- Short term (24–72 hours)
- Enforce mitigations: isolate high‑risk hosts, schedule reboots to pick up patches, and, where safe, blacklist the module in low‑risk environments.
- Coordinate with vendor/product teams owning Marketplace images, WSL distributions, or internal images for rebuilds with patched kernels.
- Medium term (1–2 weeks)
- Rebuild and redeploy container images and appliances that used vulnerable base images.
- Reconcile SBOMs and adopt reproducible build practices to reduce future discovery time.
- Longer term
- Integrate MSRC VEX/CSAF outputs into automated triage and ticketing systems as Microsoft expands its attestations.
- Improve artifact discovery so kernel-centric CVEs are rapidly matched to all shipped kernel binaries and images.
Strengths and limits of Microsoft’s current approach
Microsoft’s public attestation practice — naming Azure Linux as a confirmed carrier for a given upstream component — has clear strengths: it reduces noise for Azure Linux customers, creates an authoritative starting point for remediation, and supports automation through VEX/CSAF. Microsoft also committed to updating the CVE mapping if additional products are discovered to include the same code, which is a helpful transparency commitment.However, there are practical limitations:
- Phased attestations leave many artifacts in an unverified state until inventories complete.
- Customers who rely entirely on vendor attestations without running artifact‑level scans risk missing carriers in Marketplace images, WSL kernels, or other Microsoft‑distributed binaries.
- Kernel CVEs require artifact‑level checks (kernel build/config/backports) that a single product attestation cannot substitute for.
Concrete examples of overlooked carriers (illustrative)
- WSL2 kernels distributed to developer desktops: a single vulnerable WSL kernel binary can expose thousands of developer hosts if it includes the affected driver.
- Azure Marketplace images or AKS node images created before the upstream fix and rebuilt without the vendor patch.
- Internal CI images built from an Azure Linux base image captured before the fix was applied.
Closing assessment and recommended call‑to‑action
To answer the original question succinctly and precisely:- Strictly literal to Microsoft’s publication: Yes, Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the affected open‑source component referenced by CVE‑2024‑43849.
- Operationally and prudently: No, Azure Linux is not necessarily the only Microsoft product that could be affected. Any Microsoft product or image that ships a Linux kernel build containing the Qualcomm PDR driver (or that was built from an upstream kernel tree predating the fix) could carry the vulnerability until verified. Treat other Microsoft artifacts as unverified and prioritize artifact‑level scanning and remediation.
- Patch Azure Linux systems first and verify MSRC updates for product mappings.
- Run targeted discovery across WSL kernels, Azure Marketplace images, AKS node images, and any in‑house images built from Azure Linux bases.
- Use binary/source matching against the upstream fix commit to confirm presence or absence.
- Apply compensating controls (isolation, scheduling, blacklisting where safe) while you remediate.
The clock on operational exposure starts when images and kernels that include the vulnerable code remain in service; the fastest way to reduce your blast radius is targeted inventory, prioritized patching for attested products (Azure Linux), and immediate artifact verification for all Microsoft‑distributed kernel artifacts you use.
Source: MSRC Security Update Guide - Microsoft Security Response Center