Microsoft’s public advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is a product‑level inventory attestation — it confirms Azure Linux images were found to contain the vulnerable Linux kernel component behind CVE‑2025‑37915, but it is not a technical proof that no other Microsoft product or distributed artifact could also include the same vulnerable code. ps://www.microsoft.com/en-us/msrc/blog/2025/10/toward-greater-transparency-machine-readable-vulnerability-exploitability-xchange-for-azure-linux)
Background / Overview
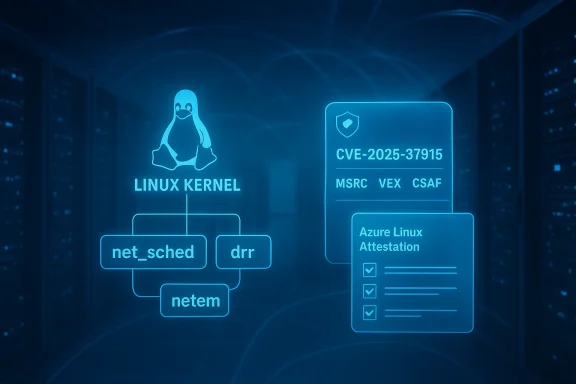
CVE‑2025‑37915 is a Linux‑kernel vulnerability in the traffic‑control subsystem (net_sched) that affects the DRR (Deficit Round Robin) queuing discipline when a netem qdisc is used as a child. The bug arises when a netem child makes the parent qdisc’s enqueue callback reentrant; in the DRR implementation this reentrancy can cause the same classifier/class to be added twice to the active list, producing memory corruption in kernel memory structures. The defect was fixed upstream by checking whether the class is already active before adding it again.The vulnerability is not a network‑level remote exploit in the classic sense: it requires local capability to manipulate traffic-control qdiscs and to create the specific parent/child configuration (DRR + netem) that triggers reentrancy. That said, the impact is serious because kernel memory corruption can lead to reliability problems, integrity failures, or privilege escalation depending on the execution context and surrounding kernel state. Multiple distros and vendors have tracked the CVE and published advisories or fixes for affected kernel streams.
Microsoft’s short MSRC wording — the phrasing you quoted — is an important transparency signal: it documents the inventory conclusion Microsoft has reached for a (Azure Linux). But it is not an assertion of exclusivity; Microsoft has also said it will update the CVE/VEX/CSAF mapping if impact to additional Microsoft products is identified. In practice that means Azure Linux is a confirmed hit for Microsoft’s inventory team, and other Microsoft products remain subject to per‑artifact verification.
What exactly is CVE‑2025‑37915? (technical summary)
The vulnerable code path
- Subsystem: net_sched (Linux traffic control).
- Component: drr (Deficit Round Robin) queuing discipline.
- Trigger: a netem child qdisc that causes the parent enqueue path to be reentrant.
- Symptom: the same classifier/class can be added to the active list twice, which leads to memory corruption in kernel list structures and inconsistent state.
- Fix: avoid adding a class to the list if it is already active (check cl_is_active before list-add).
Attack surface and exploitability
- Local access required: an attacker (or local process) must be able to create or manipulate qdiscs (traffic‑control configurations), so remote network exposure alone is not enough without some way to run local code or privileged operations on the host.
- Complexity: non‑trivial; triggering the exact sequence requires specific qdisc configuration and timing (reentrancy).
- Potential severity: memory corruption in kernel code can escalate into denial of service (kernel panic, crash) or, in some cases, privilege elevation if exploited in a crafted environment. The commonly published CVSS vectors place this in the local attack vector category with significant impact on integrity/availability.
Is Azure Linux the only Microsoft product d?
Short answer: No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable library or be affected. Azure Linux is, however, the only Microsoft product Microsoft has publicly attested (so far) to contain the implicated upstream component for this CVE. That attestation is authoritative for Azure Linux images and is the reason Microsoft instructs customers to treat Azure Linux instances as in‑scope for remediation. Microsoft has also committed to update machine‑readable VEX/CSAF attestations if additional Microsoft products are discovered to carry the same code.Why this distinction matters:
- A product‑scoped attestation (for example “Azure Linux includes this component”) documents the outcome of a finished inventory exercise for that product family.
- It does not (and practically cannot) certify exclusivity across all Microsoft artifacts, because many Microsoft offerings are assembled from upstream components at build time and those same components can appear in multiple places: WSL2 kernels, Azure Marketplace VM images, custom kernel builds used by AKS/containers, CBL‑Mariner derivatives, or other internal build artifacts.
- Therefore, while Azure Linux is confirmed, the presence or absence of the vulnerable code in other Microsoft products requires separate artifact inspection or an explicit additional attestation from MSRC.
Practical implications for IT teams and administrators
If you run Azure Linux images
- Treat Microsoft’s attestation as definitive: Azure Linux images are confirmed to include the vulnerable upstream component and should be patched or remediated according to Microsoft’s published updates and VEX/CSAF guidance. Microsoft’s VEX rollout improves automation and machine‑readable triage, but patching remains the operational step.
If you run other Microsoft artifacts that use Linux kernels
Do not assume immunity. Take these steps:- Inventory: identify where Linux kernels or kernel modules are present across your Microsoft‑distributed artifacts (WSL2 kernels, Azure Marketplace images, AKS node images, container host images, CBL‑Mariner‑derived components).
- Kernel version check: compare running or distributed kernel versions against the distributions’ CVE advisories that list the affected kernel streams and fixed versions. Public trackers show which kernel versions were affected and where vendors have issued fixes.
- Artifact scanning: where possible, examine the actual artifact (kernel package, kernel config, compiled module) for evidence of the vulnerable code path, or use vendor/machine‑readable attestations (VEX/CSAF) to confirm scope.
- Patch or replace: if an artifact includes an affected kernel stream, apply the vendor patches or rebuild images with the fixed kernel and redeploy.
Operational commands and checks (conceptual)
- Confirm kernel version: run a kernel‑version check on hosts and images to map to vendor advisories.
- Inspect qdisc usage: look for configurations that use drr with netem child qdiscs; if you are not using such combinations the immediate exploit surface is smaller, though the kernel still contains the bug until patched.
- For images: check packaged kernel versions (package metadata) or checksum the kernel artifact against upstream builds if your supply chain allows.
How vendors and distributions have treated CVE‑2025‑37915
Multiple vendor advisories and distribution trackers list the vulnerability, affected kernel ranges, and provide patched kernel package versions or stable commit references. For example, Red Hat, Amazon Linux (ALAS), and other vendors tracked the bug and issued advisories and fixes for affected kernel streams. Public vulnerability databases and vendor advisories provide the precise fixed package versions you should map against your installed kernels.Independent tracking (e.g., security vendors and vulnerability databases) has also summarized the technical cause and the upstream remediation, which helps operators cross‑verify vendor bulletins. Use at least two independent sources when planning remediation to ensure you apply the correct kernel stream and package for your environment.
Recommended remediation plan (step‑by‑step)
- Confirm exposure
- Identify hosts and images that run Linux kernels (Azure Linux, WSL2 kernels, AKS node images, Azure Marketplace images, CBL‑Mariner derived artifacts).
- Check the exact kernel package versions against vendor CVE advisories and distribution trackers for CVE‑2025‑37915.
- Prioritize by risk
- Hosts that allow local untrusted code execution (multi‑tenant hosts, containers that grant qdisc management capabilities, developer machines) should be highest priority.
- Systems that have DRR + netem qdisc configurations in production (networking hosts, traffic shapers) are higher risk.
- Patch
- Apply vendor‑supplied kernel updates or rebase images to kernel builds that include the upstream fix.
- If immediate patching is impossible, consider temporary mitigations (see below).
- Mitigate (temporary measures)
- Avoid using netem as a child qdisc of drr where possible until patched; remove or replace the configuration in affected hosts.
- Limit local privileges that allow qdisc manipulation; restrict who can create qdisc configurations or run privileged networking commands.
- Verify
- After patching, validate that kernel packages are updated and that the fix is present in the running kernel (package metadata or boot logs).
- Re‑scan images and hosts with your standard vulnerability management tooling and ensure the CVE is marked remediated by your telemetry.
- Monitor vendor attestations
- Track MSRC VEX/CSAF outputs for updates if Microsoft expands the attestation to include other products.
- Watch vendor security advisories for any reclassifications or additional mitigations.
Why Microsoft’s worusion — and how to interpret it
Microsoft’s one‑line mapping style — “Azure Linux includes this open‑source library and is therefore potentially affected” — is deliberately concise because it aims to be an authoritative inventory signal for a named product set. However, it does not mean:- that Azure Linux is the only Microsoft product that could contain the vulnerable upstream code; or
- that other Microsoft images or artifacts have been exhaustively checked and cleared.
This pattern — product‑scoped attestation, not exclusivity — is common across vendors that publish supply‑chain inventory results. Treat the vendor attestation as a starting point for triage rather than a comprehensive inventory of every possible binary or kernel Microsoft may distribute.
What defenders should communicate to stakeholders
- To engineering: prioritize patching of Azure Linux images and any other managed images that package the affected kernel streams. Validate deployments and rolling upgrades to avoid introducing regressions.
- To security operations: update detection and inventory systems to flag unpatched kernel versions and qdisc configurations that combine DRR + netem on hosts that are reachable to untrusted users.
- To leadership: explain that Microsoft’s attestation confirms Azure Linux only for now; broader exposure of Microsoft artifacts requires per‑artifact checks or further attestations from MSRC. Microsoft’s commitment to ble VEX/CSAF attestations streamlines this process going forward.
Known limitations and unverifiable areas
- We can definitively say Microsoft has attested Azure Linux as including the implicated upstream code; we cannot definitively say which other Microsoft products include or do not include the vulnerable code unless Microsoft publishes an attestation listing them or the artifacts are inspected directly. That is an operational — not a technical — constraint.
- The precise exploitability on a given host depends on kernel build options, distribution backports, and local configuration (for example, whether netem is present and whether DRR is configured), so assertions about “exploitability in the wild” must be qualified by per‑host evidence. Treat claims that “this is trivially exploitable remotely” with caution unless an authoritative proof‑of‑concept has been published and verified.
Final assessment: what you should take away
- Azure Linux is confirmed by Microsoft to include the vulnerable upstream kernel component for CVE‑2025‑37915; that product should be considered in‑scope for remediation actions.
- Azure Linux is not necessarily the only Microsoft product that could be affected. The MSRC attestation is product‑scoped; other Microsoft artifacts (WSL2 kernels, Azure Marketplace images, AKS/VM images, CBL‑Mariner derivatives) could contain the same upstream code and must be validated independently or via Microsoft’s future VEX/CSAF updates.
- Operational action: inventory your kernels and images, map installed kernel streams to vendor advisories for CVE‑2025‑37915, apply the upstream or vendor patches, and temporarily avoid DRR+netem configurations on hosts where patching cannot be immediate.
- Monitor Microsoft’s machine‑readable attestations (VEX/CSAF) and vendor advisories for updates that expand product scope or provide additional remediation guidance. This new transparency step from MSRC will help automate triage, but it does not replace artifact‑level verification.
If you want a short checklist to run right now:
- Query your inventory for hosts/images running Linux kernels matching the affected streams.
- For Azure Linux hosts, apply Microsoft’s recommended kernel updates immediately (treat them as high priority).
- For other Microsoft images (WSL2, AKS, Marketplace), either verify via Microsoft VEX/CSAF output or inspect the artifact directly before declaring them unaffected.
Source: MSRC Security Update Guide - Microsoft Security Response Center