The short, operational answer is: No — Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the upstream ATM/atmtcp code tied to CVE‑2025‑38185, but that attestation is product‑scoped and is not a technical guarantee that no other Microsoft artifact could also carry the same vulnerable code. Microsoft’s MSRC wording is an explicit inventory statement for Azure Linux; it is useful and authoritative for customers who run Azure Linux images, but defenders should treat other Microsoft‑supplied kernels and images as unverified until they are individually confirmed, patched, or marked Not Affected. / Overview
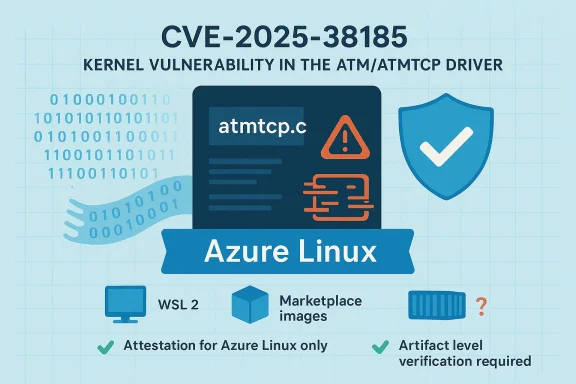
CVE‑2025‑38185 is an in‑tree Linux kernel vulnerability in the ATM (Asynchronous Transfer Mode) TCP driver — specifically a defect in atmtcp’s send path (atmtcp_c_send()) that fails to properly handle socket buffers (skb) with invalid lengths. The practical consequence reported in upstream trackers is memory-handling errors and leaked kernel resources (skb and socket state) under certain failure conditions, which produce availability and stability problems and may enable denial‑of‑service when triggered by a local user or guest.
Public vulnerability aggregators and distro trackers list the issue as medium severity (CVSS ~5.5) and show the upstream fix merged into the stable kernel trees; downstream maintainers packaged backports into their released kernel builds. Several tracker pages and advisories reiterate that this is an upstream kernel fix (i.e., “drivers/atm/atmtcp.c”), not an application library patch, and that remediation is to install updated kernel packages or apply the upstream patch.
On its CVE page for CVE‑2025‑38185 Microsoft’s Security Response Center (MSRC) published a short product attestation: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” That sentence signals two concrete things:
Microsoft’s product‑scoped VEX/CSAF attestation program is an important step toward better software supply‑chain transparency, and its Azure Linux disclosures are operationally valuable. But defenders still must do the hard work of inventory verification and rapid remediation across the diverse set of Microsoft artifacts they operate. Treat the Azure Linux attestation as a definitive starting point — and treat any un‑attested Microsoft artifact as “needs verification” until proven otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE‑2025‑38185 is an in‑tree Linux kernel vulnerability in the ATM (Asynchronous Transfer Mode) TCP driver — specifically a defect in atmtcp’s send path (atmtcp_c_send()) that fails to properly handle socket buffers (skb) with invalid lengths. The practical consequence reported in upstream trackers is memory-handling errors and leaked kernel resources (skb and socket state) under certain failure conditions, which produce availability and stability problems and may enable denial‑of‑service when triggered by a local user or guest.
Public vulnerability aggregators and distro trackers list the issue as medium severity (CVSS ~5.5) and show the upstream fix merged into the stable kernel trees; downstream maintainers packaged backports into their released kernel builds. Several tracker pages and advisories reiterate that this is an upstream kernel fix (i.e., “drivers/atm/atmtcp.c”), not an application library patch, and that remediation is to install updated kernel packages or apply the upstream patch.
 What Microsoft actually said — and what that means
What Microsoft actually said — and what that means
On its CVE page for CVE‑2025‑38185 Microsoft’s Security Response Center (MSRC) published a short product attestation: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” That sentence signals two concrete things:- Microsoft inspedistribution artifacts and found the implicated upstream kernel component mapped to the CVE; Azure Linux images are therefore a Known Affected product to prioritize for remediation.
- Microsoft also announced a phased program to publish machine‑readable CSAF/VEX attestations (the rollout be, and said it will update CVE mappings if additional Microsoft products are identified as carriers. That is a process commitment to expand transparency over time.
Why “attested for Azure Linux” does not equal “only Azure Linux”
Large vendors ship hundreds or thousands of independently built artifacts (VM images, custom kernels, container base images, marketplace images, appliance images, developer SDKs, and more). Whether a particular artifact is vulnerable depends on three verifiable, artifact‑level facts:- The upstream source snapshot or kernel commit used to build the artifact (did the vulnerable commit exist in that tree?).
- The build-time kernel configuration (was the ATM subsystem and atmtcp compiled in or built as a module?).
- Any vendor backports or local patches applied after the upstream fix (was the fix backported or not?).
Technical anatomy of the bug (concise, verifiable)
- Symptom: atmtcp_c_send() accesses skb->data after an insufficient length check; when skb->len == 0 the code path can leak the skb and the associated socket (vcc) because dev_kfree_skb() is not invoked and sk_wmem_alloc adjustments are not reverted. The correct behavior implemented upstream is to free invalid SKBs and undo the accounting changes to avoid leaks and memory corruption.
- Attack vector: local (an unprivileged local process or guest that can open and write to ATM sockets), not remotely exploitable in a default network stack without local access. The impact is primarily availability (resource exhaustion or kernel instability) rather than straightforward remote RCE.
- Fix and mitigation: upstream kernel patches adjust atmtcp_c_send() to detect invalid skb lengths, free them properly, and revert accounting changes; downstream remediation is to install updated kernels containing those upstream merges. Multiple stable kernel branches received fixes and distributors published updated packages.
Cross‑checking the claim: independent evidence
I cross‑checked the CVE and the Microsoft attestation against independent sources to build a defensible picture:- The OSV and Rapid7 vulnerability pages contain the same technical summary of the atmtcp defect and list the upstream fix path (drivers/atm/atmtcp.c) and symptom traces. These pages confirm the nature of the bug and the remediation approach.
- Aggregators and cloud vendor trackers (for example, the Amazon Linux ALAS page and other CVE tracking databases) enumerate the CVE and show vendor remediation statuses; these pages corroborate that the vulnerability was assigned to the Linux kernel ATM subsystem and that distributors have patched stable branches.
- Microsoft’s own public messaging (the MSRC CVE entry and the CSAF/VEX rollout wording) was summarized and explained in Microsoft‑focused advisory writeups and inventory analyses contained in the uploaded briefing material — those same briefings highlight the product‑scoped nature of MSRC’s Azure Linux attestation. That internal analysis explains why a product attestation is operationally useful but not exhaustive.
How to determine whether your Microsoft artifacts are affected — a practical checklist
Because the vulnerability lives in kernel code and whether it affects you depends on the artifact, perform artifact‑level checks. Below are step‑by‑step actions defenders and system administrators should take now.1. For Linux VMs (Azure Linux and other Linux images)
- Check your kernel package version and vendor advisory to see whether it corresponds to a patched kernel release (consult distro advisories and the kernel stable changelogs).
- If you control the kernel binary on the VM, inspect /boot/config-$(uname -r) and search for ATM options (CONFIG_ATM / CONFIG_ATM_TCP). If ATM support is neither built-in (‘y’) nor modular (‘m’), the atmtcp code is not present. Use:
- grep -i 'CONFIG_ATM' /boot/config-$(uname -r)
- If modules are supported, check for atm/atmtcp modules:
- lsmod | grep -i atm
- find /lib/modules/$(uname -r) -type f -name 'atmtcp.ko' -o -name 'atm*.ko'
- If an ATM module is present and you are not using ATM functionality, consider blacklisting the module or removing it from images until an updated kernel is installed. Use modprobe -r to remove and blacklist via /etc/modprobe.d/*.conf.
2. For WSL2 (Windows Subsystem for Linux)
- WSL2 can use Microsoft’s distributed kernel (source hosted in the microsoft/WSL2‑Linux‑Kernel repository) or a custom kernel specified via .wslconfig. The WSL2 Microsoft kernel is built with a tailored config; many WSL kernels intentionally disable rarely used subsystems to minimize attack surface. You can check the WSL kernel configuration (if present) in the repo or on the running WSL instance via /proc/config.gz. If you use the default Microsoft kernel, inspect Microsoft/config‑wsl or the running kernel config to see whether CONFIG_ATM or CONFIG_ATM_TCP is set. (github.com)
- If you or your users run a custom WSL kernel, rebuild it with CONFIG_ATM unset or ensure the kernel version includes upstream fixes.
3. For container images and Marketplace images
- Containers inherit the host kernel, but container images can include userland tools that interact with kernel modules. For any container base image Microsoft publishes or that you rely on, scan the image contents for kernel modules or for package lists that reference the ATM driver package (if the image bundles kernel modules). Use image scanning tools (Trivy, Clair, etc.) and arrange to rebuild and push patched base images quickly.
- For Marketplace VM images and appliances: verify the kernel versions shipped with those images and check Microsoft’s Marketplace advisory / image notes;attested them explicitly, treat them as unverified and apply the same kernel and module checks as for VMs.
4. For managed services / hosted environments
- If you run multi‑tenant workloads (for example, containers or guest VMs in shared infrastructure), prioritize patching hosts and images where the ATM subsystem is present, and work with Microsoft support if you rely on Microsoft-managed host kernels or images (ask for explicit VEX/CSAF attestations or remediation timelines).
Immediate mitigations and long‑term remediation
- Apply vendor kernel updates as soon as validated patches are released for your distribution or image (updating the kernel is the canonical fix). Upstream commit merges are available in stable trees — coordinate with your distro vendor or image provider to obtain tested packages.
- If you cannot update immediately, remove/blacklist the atm/atmtcp kernel module when it is not required:
- echo "blacklist atmtcp" > /etc/modprobe.d/blacklist-atmtcp.conf
- systemctl restart or reboot as appropriate to prevent the module from loading.
- Note: do this only if you are certain your woon ATM functionality.
- For WSL2 users: switch to a WSL kernel configuration that omits ATM support or apply a patched WSL kernel if Microsoft publishes one. The WSL repo and .wslconfig mechanism let administrators manage custom kernels. (github.com)
- For large fleets, automate detection with configuration management and inventory tooling: record kernel versions, /boot/config values, and presence of ATM modules; treat any Microsoft artifact that is not explicitly attested as “needs verification.”
Critical analysis of Microsoft’s messaging and the operational imps approach — publishing a product‑scoped attestation for Azure Linux and rolling out machine‑readable CSAF/VEX files — is a notable improvement for supply‑chain transparency. That attestation gives Azure Linux customers a clear, high‑confidence remediation target and an authoritative starting point for action. The commitment to expand VEX/CSAF and to update CVE mappings when other products are discovered to include the same upstream component is politically and operationally the right move for a vendor of Microsoft’s scale.
But thereand risks to be aware of:- Attestation scope vs. blast radius: A product‑scoped attestation is correct for the product named, but it is not the same as a comprehensive inventory of a company’s entire artifact catalog. Customers that assume “not named = safe” are at risk of missing exposures in WSL kernels, curated base images, Marketplace images, or other Microsoft-made artifacts that reuse or repackage the same upstream code. Operational triage must therefore include independent artifact-level checks.
- Patch cadence and backports: Vendors frequently backport security fixes into long‑lived kernel branches. Your exposure is determined by whether the specific kernel build that shipped with your image contains the fix, not merely by the CVE number. That means defenders should check vendor advisories to confirm if a particular build was patched or not.
- Residual supply‑chain complexity: Microsoft supplies many different images and kernels; until the rs all product families, defenders must combine vendor attestations with local inventory scans to get a complete picture. The most pragmatic posture is to accept Microsoft’s attestation for Azure Linux and simultaneously assume other Microsoft artifacts are unverified until proven otherwise.
Actionable checklist (what to do in the next 72 hours)
- Identify all Azure Linux instances and apply Microsoft’s kernel updates or image replacements immediately. Azure Linux is a known affected family; prioritize it.
- Inventory Microsoft‑supplied artifacts in your environment:
- WSL2 instances where the default Microsoft kernel is used.
- Azure Marketplace images and appliances.
- Container base images published or adopted from Microsoft.
- Any custom VM images built from CBL‑Mariner/Azure Linux packages.
Use scripts to collecfig-$(uname -r), and lsmod outputs. - For each artifact, verify whether ATM support is present (CONFIG_ATM / CONFIG_ATM_TCP) or whether an atmtcp module exists. If present and you cannot patch immediately, blacklist the module.
- Subscribe to vendor advisories (Microsoft MSRC, distro security trackers) and your internal change control to get notified when Microsoft publishes additional VEX attestations or patches for other p. For WSL users: if you rely on WSL in developer or build pipelines, constrain the WSL kernel or force a custom kernel build without ATM code until a patched Microsoft kernel is confirmed. (github.com)
Final verdict and risk posture
- Short verdict: Azure Linux is the only Microsoft product Microsoft has publicly attested to include the ATM/atmtcp code relevant to CVE‑2025‑38185. That attestation is authoritative for Azure Linux and should be treated as the immediate remediation priority.
- Operational caveat: Attested ≠ exclusive. The only safe interpretation of MSRC’s wording is that Azure Linux was inspected and flagged; it is not a guarantee that WSL kernels, linux‑azure kernels, Marketplace images, container images, or other Microsoft artifacts do not carry the same upstream code. Organizations must perform artifact‑level verification for any Microsoft‑supplied images or kernels they run.
- Practical defense: Patch Azure Linux immediately, run the kernel/module checks documented above for all Microsoft artifacts in your environment, and automate detection so you can find other carriers rapidly. Blacklist the ATM module where possible as a temporary mitigation.
Microsoft’s product‑scoped VEX/CSAF attestation program is an important step toward better software supply‑chain transparency, and its Azure Linux disclosures are operationally valuable. But defenders still must do the hard work of inventory verification and rapid remediation across the diverse set of Microsoft artifacts they operate. Treat the Azure Linux attestation as a definitive starting point — and treat any un‑attested Microsoft artifact as “needs verification” until proven otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center