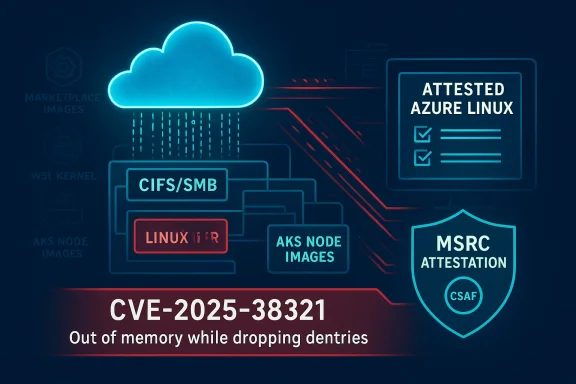
Microsoft’s short MSRC attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate for CVE‑2025‑38321 — but it is a product‑scoped inventory statement, not a proof that no other Microsoft product or image could contain the same vulnerable kernel code.
CVE‑2025‑38321 is an upstream Linux kernel fix that addresses a robustness and logging deficiency in the CIFS/SMB code path: under low‑memory conditions, the function close_all_cached_dirs() can fail to move dentries to a separate list for safe dput() after locks are dropped. The upstream change adds an explicit error message and avoids continuing to loop over tcons after a failing allocation, because further kmalloc() attempts in the same low‑memory context are likely to fail as well. The practical manifestation is noisy kernel logs (for example, “Dentry still in use”) and, in constrained environments, stability and availability problems when unmounting CIFS shares.
Multiple independent vulnerability trackers and vendor advisories record this as a medium‑severity, availability‑oriented issue (CVSS ≈ 5.5) and point to the upstream commits that implement the change and improved logging behavior. Those vendor trackers include SUSE, Red Hat summaries, and public CVE aggregators; cloud distro advisories such as Amazon Linux also map the CVE to specific package releases and remediation status.
Why this matters operationally
Two important clarifications you must take fromtation, not exclusivity: the MSRC line confirms Microsoft inspected Azure Linux and found the component. It is not a guarantee that other Microsoft images, kernels, or products do not also include the same upstream code. The statement should be read as “we checked Azure Linux and it’s affected” rather than “only Azure Linux could ever be affected.”
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑38321 is an upstream Linux kernel fix that addresses a robustness and logging deficiency in the CIFS/SMB code path: under low‑memory conditions, the function close_all_cached_dirs() can fail to move dentries to a separate list for safe dput() after locks are dropped. The upstream change adds an explicit error message and avoids continuing to loop over tcons after a failing allocation, because further kmalloc() attempts in the same low‑memory context are likely to fail as well. The practical manifestation is noisy kernel logs (for example, “Dentry still in use”) and, in constrained environments, stability and availability problems when unmounting CIFS shares.Multiple independent vulnerability trackers and vendor advisories record this as a medium‑severity, availability‑oriented issue (CVSS ≈ 5.5) and point to the upstream commits that implement the change and improved logging behavior. Those vendor trackers include SUSE, Red Hat summaries, and public CVE aggregators; cloud distro advisories such as Amazon Linux also map the CVE to specific package releases and remediation status.
Why this matters operationally
- The affected code sits in kernel filesystem logic that runs at the highest privilege level; even if the fix is primarily to add a clearer error path and to bail early, kernel path failures can cause service instability or denial‑of‑service in production workloads that mount CIFS/SMB volumes.
- The presence (or absence) of the vulnerable or patched code is an artifact‑level property: it depends on which upstream commits are present in a given kernel build, what kernel configuration options were used, and whether the vendor backported patches into a stable kernel branch. That means identical‑looking product names can ship kernels with different vulnerabilities depending on the build pipeline and timing.
What Microsoft actually said — and how to read it
Microsoft’s public FAQ language on MSRC CVE pages commonly includes a short attestation sentence that reads in effect: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” That single sentence is an inventory statement: Microsoft examined the Azure Linux distribution and confirmed the upstream code mapped to the CVE is present in those images, so Azure Linux images are a confirmed remediation priority. Microsoft also states it began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE pages if impact to additional products is identified.Two important clarifications you must take fromtation, not exclusivity: the MSRC line confirms Microsoft inspected Azure Linux and found the component. It is not a guarantee that other Microsoft images, kernels, or products do not also include the same upstream code. The statement should be read as “we checked Azure Linux and it’s affected” rather than “only Azure Linux could ever be affected.”
- Phased transparency: Microsoft’s CSAF/VEX rollout is product‑by‑product. Azure Linux was an early and obvious target for this inventory work because Microsoft maintains and publishes those builds; other product families (Marketplace images, WSL kernels, AKS node images, appliance kernels, embedded images) require separate inventory work and may be attested later — or may remain unlisted until Microsoft finds them and updates the CVE mapping.
Short answer to the user’s question
No — Azure Linux is not necessarily the only Microsoft product that could includsource code referenced by CVE‑2025‑38321. Azure Linux is the only Microsoft product Microsoft has publicly attested (so far) to include the affected kernel component for this CVE, but that attestation is deliberately scoped and not a categorical proof that no other Microsoft product ships the same kernel sources or compiled modules. Treat Azure Linux as a confirmed carrier and other Microsoft artifacts as unverified until proven otherwise.Why you cannot infer “only Azure Linux” from MSRC wording
There are several concrete technical and operational reasons a single‑product attestation canal exclusivity:- Large vendors ship many artifacts. Each VM image, container base image, Marketplace appliance, managed node image (AKS), WSL2 kernel, and agent bundle is its own build pipeline. The same upstream kernel sources can be included in many separate artifacts depending on the kernel commit snapshot and configuration used to build that artifact. Microsoft produces multiple Linux‑flavored artifacts and kernel builds that may independently include the CIFS/SMB code.
- Presence depends on build-time choices. For a given artifact to be practically vulnerable it must:
- Include the upstream CIFS/SMB source file in the kernel tree used by that build,
- Compile that code as built‑in or as a loadable module, and
- Expose a runtime scenario where the code path can be exercised (for example, a workload that mounts CIFS shares or loads the module). Absent any one of those factors, an artifact is not practi if its source tree contained the file.
- Tooling and packaging duplication. Microsoft’s internal developer tooling, package managers (for example, vcpkg or other Microsoft‑maintained packaging), or automated build pipelines can re‑use the same upstream artifacts in multiple product families. That duplication means a single vulnerable open‑source library can propagate to many places unless explicitly tracked and remediated everywhere.
Where to look beyond Azure Linux (practical inventory checklist)
If you operate mixed estates that include Microsoft‑published artifacts, treat the followis plausible carriers and verify them explicitly:- Azure Marketplace VM images and partner Marketplace appliances (any Marketplace VM image that embeds a Linux kernel). These images can be independently built and might include older kernel snapshots.
- WSL2 kernel binaries distributed with Windows builds or optional WSL updates. These kernels are maintained and shipped by Microsoft; whether they include the vulnerable code depends on kernel version and CONFIG options used.
- AKS node images and curated node pools (both Microsoft‑managed and customer‑managed node images). Node images use kernels chosen at build time; different AKS SKUs may carry different kernel versions or backports.
- Azure SDKs, agents, and management tooling that include or bundle Linux artifacts (for example, management VM images used by Azure services, monitoring agents with packaged runtime images).
- Any Microsoft‑published container base images or curated images used on Azure App Services, Functions, or container registries.
- Baked‑in vendor appliances or partner VM images that Microsoft distributes via Marketplace but that were built by third parties (they can embed vulnerable kernel builds).
Detection and verification: practical steps for operators
Below are pragmatic steps you can follow to determine whether an artifact in your fleet carries the vulnerable code and to remediate.- Identify Azure Linux instances and apply Microsoft updates first.
- Why: MSRC attested Azure Linux; it is therefore a confirmed remediation priority. Apply the kernel package or image updates Microsoft published for the distribution as soon as possible.
- Inventory kernel versions across your estate.
- Command hints (examples you can run on Linux hosts): run uname -a, inspect /boot for kernel version strings, and record package versions via rpm -qa | grep kernel or dpkg-query -W 'linux-image*'.
- Compare discovered kernel versions against vendor advisories that map fixed commits or CVE patches to specific kernel releases. SUSE, Red Hat and AWS ALAS advisories typically include the package names and fixed versions.
- Check kernel config and compiled-in features.
- Why: vulnerabilities in kernel subsystems are only exposed when the relevant code is built into or available as a module. For CIFS/SMB, inspect kernel config for CONFIG_CIFS or related CIFS/SMB config options (zcat /proc/config.gz | grep -i cifs).
- If the CIFS code is compiled as a module, list loaded modules (lsmod) and check for cifs, smb, or related module names.
- Scan images and containers with SBOM and binary scanning tools.
- Use SBOM generation (Syft, cyclonedx) and binary scanners (Trivy, Grype) against filesystem images and container images to detect the presence of vulnerable package versions or kernel artifacts.
- For Marketplace images and tarball images, extract and analyze /boot and /lib/modules for kernel versions and module names.
- Check WSL kernels and AKS node images.
- WSL: Confirm the kernel version shipped with the Windows build or the optional WSL kernel used by your users. If you manage WSL images centrally, capture and inspect the kernel binary for version strings.
- AKS: Query node image SKUs and verify their kernel versions against upstream and vendor advisories.
- Inspect Marketplace images and partner appliances.
- Treat Marketplace artifacts as black boxes until you can extract their filesystem and inspect kernel packages and /lib/modules. If you cannot alter the Marketplace image, contact the publisher for SBOMs or VEX/CSAF attestation.
- Prioritize remediation by exposure and impact.
- Remediate Azure Linux images immediately (attested).
- For other artifacts, triage based on whether they mount CIFS shares, run SMB‑facing services, or otherwise exercise the code path in question — these are highest priority.
- Document and track with VEX/CSAF data and SBOMs.
- Record which artifacts you found affected and whether vendors have published VEX/CSAF attestations or SBOMs. Keep an audit trail for compliance and incident response.
Remediation and mitigation advice
- Patch promptly: when a vendor provides a fixed kernel package or backport, apply it and schedule reboots if required. For Azure Linux, follow Microsoft’s published update guidance.
- Workload isolation: limit access to SMB/CIFS endpoints and avoid mounting untrusted CIFS shares on critical hosts until patched.
- Resource hardening: ensure hosts have memory and OOM safeguards (cgroup limits, reservations) for workloads that interact with network file systems to reduce the probability of low‑memory allocation failures that triggered the observable behavior.
- Detection telemetry: add kernel log monitoring rules that detect the specific “Out of memory while dropping dentries” and “Dentry still in use” messages — these errors indicate the code pthe system experienced the low‑memory condition the upstream patch targeted. Use existing log aggregation tools to alert on such kernel messages.
Trade‑offs and residual risks
- Patching kernel code often requires reboots. For high‑availability workloads this introduces operational downtime; weigh livepatch availability (offered by some vendors) versus full kernel updates and scheduled reboots.
- Attestation lag: vendor VEX/CSAF attestations are valuable but rolled out product‑by‑product. While Microsoft’s attestation for Azure Linux increases transparency for that product, the attestation rollout will lag for other products — this lag creates a residual verification burden for customers with heterogeneous estates.
- False sense of security: assuming “no attestation = no impact” is dangerous. Absence of a published MSRC attestation for a product simply means Microsoft has not yet published the inventory result for that product; it does not prove the artifact is safe.
- It is possible that some Microsoft artifacts beyond Azure Linux already contain the fix (for example, because their pipelines backported the patch); it is also possible some artifacts remain vulnerable. At the time of writing, Microsoft’s public mapping explicitly names only Azure Linux for this CVE, and Microsoft said it will update CVE pages should additional products be identified. Until Microsoft publishes a formal VEX/CSAF mapping for other product families, any claim that a particular Microsoft product is affected or unaffected must be verified by artifact inspection or by Microsoft’s updated attestation.
How vendors and trackers corroborate the technical facts
This CVE is tracked across multiple independent sources that corroborate the upstream change and its intent:- SUSE’s CVE summary documents the same described behavior and the upstream remediation actions (improved logging and bail‑out on allocation failure).
- Public CVE aggregators and distro advisories (cvefeed, OpenCVE, Rapid7) list the CVSSv3 score, provide timelines, and reference the kernel.org commits that implemented the fix. Those kernel.org commits are the primary evidence that the upstream change landed in stable kernel branches.
- Cloud vendor advisories (for example, Amazon Linux ALAS) list which AMI/kernel streams they consider affected and whether a fix is available in their distribution streams — useful when you run those specific cloud images.
Recommended reconnaissance commands and checks (concise)
Use these as a starting checklist when you perform artifact verification (examples are illustrative — adapt to your environment):- On a Linux host:
- uname -a (capture kernel version)
- zcat /proc/config.gz | grep -i cifs (check kernel config)
- lsmod | egrep 'cifs|smb' (detect loaded modules)
- journalctl -k | egrep -i 'Out of memory while dropping dentries|Dentry still in use' (find relevant kernel log entries)
- On image artifacts and containers:
- Extract /boot and /lib/modules from the image and inspect package or versiate an SBOM (Syft) and run vulnerability scanners (Trivy/Grype) against image tarballs.
- For WSL/AKS/Marketplace images:
- Request the SBOM or VEX/CSAF attestation from the image publisher when possible.
- If you cannot get an SBOM, spin an ephemeral VM from the image and run the same kernel/version checks above.
Bottom line and practical takeaways
- Microsoft’s MSRC text for CVE‑2025‑38321 correctly identifies Azure Linux as a product that includes the implicated open‑source kernel code and is therefore potentially affected; that gives Azure Linux customers a clear, immediate remediation priority.
- That attestation is product‑scoped, not exclusive. Absence of a similar attestation for another Microsoft product is absence of attestation, not proof of absence. Customers must not treat a single‑product attestation as a universal safety guarantee for other Microsoft artifacts.
- The practical defensive action is twofold:
- Immediately patch and remediate Azure Linux images you manage (attested affected).
- Perform artifact‑level discovery and scanning across other Microsoft‑published images, WSL kernels, AKS nodes, Marketplace appliances, and any agent/bundled images you run to validate whether they include the vulnerable kernel code or a fixed backport — don’t assume they are safe until you verify.
Source: MSRC Security Update Guide - Microsoft Security Response Center