Microsoft’s short, product‑scoped statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is an inventory attestation for a single product, not a technical guarantee that no other Microsoft product or image can contain the same vulnerable REXML code; defenders must therefore treat Azure Linux as a confirmed remediation priority while performing artifact‑level discovery across all Microsoft‑supplied images and binaries.
Ruby’s REXML library is a widely used XML processing library that ships in many Ruby runtimes and can be vendored into applications and packages. When a vulnerability like CVE‑2024‑39908 (a denial‑of‑service condition in REXML) is disclosed, vendors that ship Linux distributions, cloud marketplace images, container base images, runtime bundles, or compiled artifacts must determine whether their published products include the affected component and whether an update or mitigation is required.
Microsoft’s Security Response Center (MSRC) published a concise product‑level attestation for this class of third‑party CVEs: Microsoft has mapped the vulnerable upstream component into the Azure Linux distribution and therefore lists Azure Linux as potentially affected. Microsoft also notes that it began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE mappings if additional Microsoft products are discovered to ship the same open‑source library.
This factual sentence — helpful, clear, and concise — is the core of the confusion for many operators: does naming Azure Linux mean it is the only Microsoft product that contains REXML? The short, operational answer is: No — not necessarily; Azure Linux is the product Microsoft has completed inventorying and attested to, but absence of a VEX/CSAF entry for other Microsoft artifacts is an absence of attestation, not proof of absence.
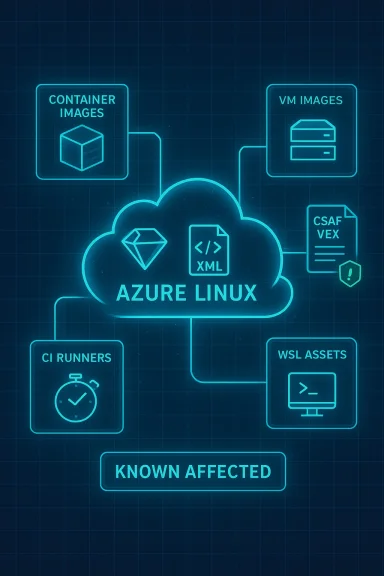
However, that wording is deliberately narrow. It confirms the presence of the upstream library in a named product and the vendor’s commitment to transparency via CSAF/VEX — it does not assert that other Microsoft products, Marketplace images, container images, WSL kernels, GitHub runner images, or vendor appliances are free of the same code. Microsoft’s VEX rollout started with Azure Linux and is being expanded product‑by‑product; the company pledges to update CVE records if impact to additional products is found. Treat the attestation as a positive confirmation for Azure Linux and as a promise that more mappings will appear over time.
That statement should not be read as a technical certificate of exclusivity. Absent a VEX/CSAF entry for another Microsoft product, treat that product as unverified rather than Not Affected. The correct operational posture is to prioritize Azure Linux for immediate remediation if you run it, while simultaneously conducting artifact‑level discovery and scanning across Marketplace images, container registries, CI runners, WSL artifacts, and any Microsoft‑distributed agents you use. Microsoft has committed to updating CVE mappings if more products are found to include the vulnerable component; in the meantime, defenders must assume possible exposure beyond the single attested product and verify accordingly.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Ruby’s REXML library is a widely used XML processing library that ships in many Ruby runtimes and can be vendored into applications and packages. When a vulnerability like CVE‑2024‑39908 (a denial‑of‑service condition in REXML) is disclosed, vendors that ship Linux distributions, cloud marketplace images, container base images, runtime bundles, or compiled artifacts must determine whether their published products include the affected component and whether an update or mitigation is required.Microsoft’s Security Response Center (MSRC) published a concise product‑level attestation for this class of third‑party CVEs: Microsoft has mapped the vulnerable upstream component into the Azure Linux distribution and therefore lists Azure Linux as potentially affected. Microsoft also notes that it began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVE mappings if additional Microsoft products are discovered to ship the same open‑source library.
This factual sentence — helpful, clear, and concise — is the core of the confusion for many operators: does naming Azure Linux mean it is the only Microsoft product that contains REXML? The short, operational answer is: No — not necessarily; Azure Linux is the product Microsoft has completed inventorying and attested to, but absence of a VEX/CSAF entry for other Microsoft artifacts is an absence of attestation, not proof of absence.
What Microsoft’s wording actually means
Product‑scoped attestation, not exclusivity
When MSRC writes that “Azure Linux includes this open‑source library and is therefore potentially affected,” that is an authoritative claim about the builds Microsoft inspects and maintains for the Azure Linux distribution. For anyone running the Azure‑published images, that statement is actionable: those images contain the upstream component in question and should be patched or otherwise mitigated according to vendor guidance.However, that wording is deliberately narrow. It confirms the presence of the upstream library in a named product and the vendor’s commitment to transparency via CSAF/VEX — it does not assert that other Microsoft products, Marketplace images, container images, WSL kernels, GitHub runner images, or vendor appliances are free of the same code. Microsoft’s VEX rollout started with Azure Linux and is being expanded product‑by‑product; the company pledges to update CVE records if impact to additional products is found. Treat the attestation as a positive confirmation for Azure Linux and as a promise that more mappings will appear over time.
Why this distinction matters
- Large vendors produce thousands of artifacts. A single upstream library can appear in many places: container base images, Marketplace VM images, hosted CI/CD runners, telemetry agents, SDKs, and sample images. A product attestation for one artifact is not an exhaustive inventory of every other artifact the vendor ships.
- Build‑time choices, backports, and vendoring matter. Whether a given Microsoft image or binary is actually vulnerable depends on how that artifact was built: which packages were included at build time, whether the library was vendored or shaded, and whether the vendor applied upstream fixes or backports.
- Absence of a published VEX entry = unverified. Until Microsoft publishes a CSAF/VEX statement for a product, defenders should treat that product as unverified rather than Not Affected. The security posture should assume possible exposure and verify via scanning or SBOM/SCA evidence.
How REXML/CVE‑2024‑39908 could appear across Microsoft artifacts
REXML and similar Ruby libraries can be introduced into an environment in several common ways. Any of these vectors can make an otherwise unrelated product a potential carrier of the vulnerability.Typical carriers
- Ruby runtimes and system packages included in Linux distributions and images (for example, as part of a distro’s default packages).
- Vendor or partner Marketplace images and appliances that bundle application stacks (web apps, monitoring agents, automation tooling) written in Ruby.
- Container base images (system or language images) that include a Ruby interpreter or gems in their layers.
- CI/CD runner images (hosted build agents or published virtual‑environment images), which often contain Ruby tooling to support build pipelines.
- Vendor‑published binaries or agents that bundle a Ruby interpreter and gems statically (vendoring the library inside the package).
Examples inside the Microsoft ecosystem to check immediately
- Azure Marketplace VM and appliance images (both Microsoft‑curated and partner‑published images).
- Azure Container Registry images and other container images published or recommended by Microsoft.
- WSL (Windows Subsystem for Linux) images and the WSL kernel/runtime artifacts Microsoft publishes or curates.
- GitHub‑hosted runner images (GitHub is a Microsoft company) and any published virtual environments used for Actions or Azure DevOps hosted agents.
- Any Microsoft‑distributed agent, telemetry collector, or support tool that might embed a Ruby runtime.
Practical triage: what defenders must do now
The practical security posture we recommend follows a prioritized, artifact‑centric approach. Microsoft’s Azure Linux attestation tells you where to start — not where to stop.Immediate (first 24–72 hours)
- Prioritize Azure Linux images. If you run Azure Linux VMs, container nodes, or Marketplace images based on Azure Linux, treat those images as in‑scope and apply vendor updates or rebuild images using patched packages as soon as Microsoft publishes them. The MSRC attestation is authoritative for those images.
- Identify exposure in your estate. Inventory where Ruby and REXML might be present: container registries, VM images, build agents, live VMs, and CI/CD runners. Use your existing asset inventory, image catalog, and package management metadata.
- Run targeted scans. Use SCA tools, image scanners, and runtime detectors to look for the exact REXML package name/version or signature in images and binaries. Prioritize the artifacts listed above (Marketplace images, published containers, hosted runner images).
Secondary (days 3–14)
- Examine SBOMs and VEX/CSAF data. Where available, consume SBOMs, vendor CSAF/VEX attestations, or machine‑readable inventories to determine whether a given product is Known Affected, Not Affected, Under Investigation, or Fixed. Microsoft began publishing VEX/CSAF attestations in October 2025; consume those signals as they appear.
- Patch build images and CI runners. If your pipelines use hosted or vendor‑published runners or base images that include Ruby, rebuild those runners with the patched REXML or with Ruby versions that include the fix. This prevents future artifacts from being compiled with the vulnerable library.
- Detect and mitigate runtime exposure. For live services that cannot be immediately patched, consider runtime mitigations (e.g., input validation, rate limiting untrusted XML inputs, and service isolation) to reduce the likelihood and impact of a denial‑of‑service condition.
Longer term (weeks to months)
- Build artifact‑level attestations into procurement and dev processes. Require SBOMs for third‑party images and insist on VEX/CSAF attestations or equivalent inventory data from suppliers where possible. This reduces the time between vulnerability disclosure and your ability to triage.
- Automate verification. Incorporate automated SCA and image scanning into CI/CD, and fail builds if a vulnerable component appears in any image layer or produced artifact. Use reproducible build practices when possible.
- Maintain layered defenses. Combine artifact‑level hygiene with runtime protections — container limits, resource quotas, and observability — to limit the impact of DoS‑type defects even when libraries are present.
How to verify other Microsoft artifacts (concrete checklist)
- Query your image catalog for Ruby runtimes, gems, and Ruby package manager metadata. Look for REXML listed in gem manifests or in installed package lists.
- Scan container layers for files matching Ruby gem metadata (.gemspec, vendor/gems/*, or gem directories).
- Inspect build pipelines and CI runner images for installed Ruby versions or gem bundles.
- Request SBOMs or VEX attestations from vendors or image publishers; cross‑check any Microsoft VEX/CSAF entries Microsoft publishes for the CVE as they become available. Microsoft’s VEX program began with Azure Linux in October 2025 and will expand; use those attestations as a machine‑readable source of truth when present.
- For any compiled or packaged binary, use strings and file‑type analysis to detect embedded Ruby interpreters or vendored gems (watch for frozen gem directories packaged inside application archives).
Risks, strengths, and the limits of vendor attestations
Notable strengths of Microsoft’s approach
- Transparency through VEX/CSAF: Publishing machine‑readable attestations is a meaningful improvement for customers who need automated signals to prioritize remediation. Microsoft’s staged rollout (starting with Azure Linux) provides an authoritative starting point for customers that run those images.
- Actionable product‑level guidance: Identifying a specific product (Azure Linux) as a confirmed carrier gives operators an immediate remediation target rather than leaving them guessing which of many images might be affected.
Risks and limitations to be aware of
- Attestation is not exhaustive: A vendor naming a product is a statement of what they have finished inventorying, not a global guarantee about all artifacts they ship. Assuming exclusivity from that wording exposes you to unseen risk in other Microsoft‑supplied or partner images.
- Supply‑chain transitivity: The same library can appear transitively through vendor build images, third‑party appliances, or shared CI runners. That transitivity means an unscanned artifact can become a vulnerability carrier even if the vendor has patched a different product family.
- Timing and cadence of updates: Upstream fixes and downstream packaging cadences differ across distributions and images. A patched upstream release does not equal immediate patched binaries in every downstream vendor product; operators must verify package versions in the images they run.
Clear, pragmatic recommendations
- Treat Microsoft’s MSRC attestation for Azure Linux as a high‑confidence start point — patch Azure Linux images first if you run them.
- Do not assume other Microsoft products are safe until Microsoft publishes a VEX/CSAF attestation for them or until you verify them yourself. Absence of a statement is not proof of absence.
- Perform immediate artifact‑level discovery across Marketplace images, container registries, CI runners, and any Microsoft‑distributed agents. Use SCA and image scanners to find REXML occurrences.
- Leverage SBOMs and request VEX/CSAF attestations for third‑party images you depend on; require such attestations for high‑risk or internet‑facing artifacts.
- Harden runtime controls (resource quotas, request limits, input validation) to reduce the impact of potential denial‑of‑service bugs while patching proceeds.
Conclusion
Microsoft’s one‑line MSRC statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate and useful: it identifies an authoritative remediation target and fits into Microsoft’s broader move toward machine‑readable CSAF/VEX attestations that began in October 2025.That statement should not be read as a technical certificate of exclusivity. Absent a VEX/CSAF entry for another Microsoft product, treat that product as unverified rather than Not Affected. The correct operational posture is to prioritize Azure Linux for immediate remediation if you run it, while simultaneously conducting artifact‑level discovery and scanning across Marketplace images, container registries, CI runners, WSL artifacts, and any Microsoft‑distributed agents you use. Microsoft has committed to updating CVE mappings if more products are found to include the vulnerable component; in the meantime, defenders must assume possible exposure beyond the single attested product and verify accordingly.
Source: MSRC Security Update Guide - Microsoft Security Response Center