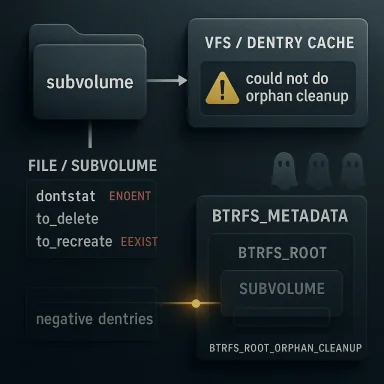
CVE-2026-31519 is a classic example of a small-looking filesystem bug producing a very awkward operational failure mode. In Btrfs, a subvolume can wind up with a broken dentry state where directory listings show a name that cannot be stat’d, deleted, or cleanly replaced, and the kernel may emit the ominous message “could not do orphan cleanup -2” during lookup. The result is not just annoyance: administrators can get stuck between
This CVE is rooted blem. The report describes a case where a newly created subvolume did not have
The user-visible failure is nasty becausubvolume is there, but not really there. A directory entry can be present in the parent directory listing, yet attempts to stat it fail, deletion returns
The timing detail is what makes the bug interesting. The reporoot may have been created long before the first meaningful
From an administrator’s point of view, this is e case. A broken subvolume dentry can block deletion, confuse automation, and make filesystem cleanup jobs fail in ways that look like corruption even when the on-disk metadata is mostly intact. The bug can also present as a hard-to-explain operational trap: the subvolume appears in one tool, disappears in another, and only recovers after a cache invalidation or other intervention that changes lookup behavior.
The fact that Microsoft’s advisory portal surfaced the issue is also a reminder that Linux filesystem Ch enterprise vulnerability workflows far beyond the traditional kernel community. The NVD record says the CVE was newly received from kernel.org on April 22, 2026, and the Microsoft entry mirrors that publication path, even though the underlying issue is entirely in Linux Btrfs code. That matters for mixed-platform shops: the visibility layer may be Microsoft, but the remediation path is still kernel backporting and vendor coordination.
That failure mode is not just confusing; it is self-reinforcing. Once the VFS caches a negative dentry, later operations may continue to hit the wrong state until the cache is dropped. The report explicitly notes that dropping thtigate the issue, which is a strong sign the problem lives at the intersection of lookup caching and Btrfs internal cleanup state rather than in a permanently damaged tree. In other words, the filesystem is not necessarily wrecked, but the namespace has drifted out of sync with reality.
Why
The report also explains that there were no orphan items for the subvolume, and the subvolume was otherwise healthy-looking, which helps rule out the obvious explanations. That means the lookup code was not reacting to a half-deleted root, but to stale internal state. Th that can survive casual inspection because the on-disk tree looks normal while the in-memory lifecycle flags are subtly wrong.
The report makes a strong case that this is what happened. The subvolume was created earlier, but the meaningful first orphan cleanup call occurred later, after the object had already been exposed to the dentry cache. If anything then caused the dentry to be re-evaluated, lookup could invoke orphan cleanup for the first time in a state that no longer matched the object’s actual lifetime. That m the door to the false-negative interpretation and the resulting negative dentry.
This is a good reminder that many filesystem bugs are really lifecycle bugs. The code did not merely forget a flag in some abstract sense; it forgot to mark the root as having crossed a state boundary at the exact moment the VFS began treating it like a real directory entry. In kernel code, those boundaries matter because a missed transition can ripple into orphan handling, deletion semantics, and even transaction behavior.
This kind of bug is especially frustrating in production because it can look like intermittent corruption. An operator may see one tool fail, another tool succeed after some unrelatedhird tool behave differently after a reboot. The real issue is not random corruption but a stale namespace cache anchored to the wrong lifecycle assumption.
The delayed-ip subtle. The report says ordered extent creation uses
It also helps explain why the problem can persist for some time before becoming visible. A root may behave normally across many operations, then suddenly fail after a cache eviction or unrelated memory pressure event changes the order in which delayed references are released. That makes the CVE more dangerous from an operations perspective, because it is *predictably unpred depends on narrow timing windows rather than a single deterministic path.
That kind of fix is often the best possibk. It does not change external APIs, it does not invent a new recovery model, and it does em redesign. It simply restores the intended invariant so the rest of the code can trusin. Those are the patches that stable maintainers usually like because they are cally obvious.
That is why a bug like thwhile without looking dramatic. It is not a classic crash bug or memory safety issue. It is an accounting and lifecycle mismatch that only becomes visible when the exact combination of cache state and cleanup timing lines up badly. That makes the CVE operationally important even though the patch itself is small.
Consumer systems are less likely to encounter the bug in day-to-day use, but they are not immune. Anyone running a Btrfs-based desktop, lab machine, or home server with subvolume-heit the edge case if the right dentry and cleanup timing occurs. The differenceystems are more likely to expose the issue at scale, where rare races becomtable over time.
The fact that NVD had not yet assigned a CVSS score at the time of publication should not lull anyone into treating the bug as low priority. The description itself is enough to show that the issue can strand a valid subvolume in an inconsistent state and interfere woperations. In operational terms, that can be enough to break management workflows even if the issue does not map neatly to a traditional exploitation story.
There is also a genuine maintenance opportunity here for distribution vendors and OEMs. Bugs like this are easy to dismiss because they do not sound like headline-grabbing exploitation paths, but they can still generate expensive support incidents when subvolume workflows are central to storage management. Clear backports and concise advisories help prevent small kernel bugs from becoming big operaThe fix is narrow and backportable.
There is also the risk of patch lag. Even when a fix is published upstream, dotake time to ship a corrected kernel, and appliances may remain exposed longer than generic servers. For enterprise users, that lag is often the real exposure window, because the production kernel is the vendor backport, not the upstream commit.
Another concern is that bugs of this style can hide adjacent assumptioissue is found, maintainers often discover related lifetime or cleanup bugs nearn this CVE implies a wider catastrophe, but it does mean the patch should be treated as part of an ongoing hardening effort rather than as an isolated one-off.
It is also worth watching for vendor advisories that map the CVE to package versions and backport status. Linux filesystem CVEs often become operationally relevant only when a distro or appliance vendor confirms exactlxed. Without that mapping, defenders are left inferring exposure from mainline commit history, which is useful but not always enough for production triage.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
ENOENT, EEXIST, and even transaction abort behavior until the dentry cache is cleared or the filesystem is otherwise recovered. The published fix is narrow but important: set BTRFS_ROOT_ORPHAN_CLEANUP during subvolume creation so the root is treated consistently from the beginning of its lifetime. s has always been one of Linux’s most ambitious filesystems, combining checksumming, snapshots, subvolumes, send/receive, and copy-on-write semantics into a single coherent design. That richness gives it flexibility, but it also means the filesystem has a deep state machine under the hood, and small lapses in lifecycle bookkeeping can surface as strange user-visible behavior. Subvolumes are especially sensitive because they are not just directories in the ordinary sense; they are roots of separate Btrfs trees with their own internal rules, and the kernel has to keep their VFS dentries, inode state, and orphan cleanup logic aligned.This CVE is rooted blem. The report describes a case where a newly created subvolume did not have
BTRFS_ROOT_ORPHAN_CLEANUP set at creation time, even though later lookup paths expected that flag to be present before running orphan cleanup. That matters because the flag is effectively a one-way marker: once btrfs_orphan_cleanup() runs and sets it, the root is not supposed to re-enter that same first-time cleanup path again. If the initial create path fails to mark the root appropriately, later lookups can make inconsistent assumptions about the subvolume’s state.The user-visible failure is nasty becausubvolume is there, but not really there. A directory entry can be present in the parent directory listing, yet attempts to stat it fail, deletion returns
ENOENT, and recreation returns EEXIST. In the report’s words, the system can end up in a state where the subvolume seems healthy, not half-deleted, and not obviously damaged, yet the dentry cache and cleanup machinery disagree about what exists. That sort of split-brain metadata state is exactly the kind of thing that makes filesystems hard to debug and easy to underestimate.The timing detail is what makes the bug interesting. The reporoot may have been created long before the first meaningful
btrfs_orphan_cleanup() call occurs, which means the root can sit around in the dentry cache without having been marked as already cleaned. Later, when lookup finally triggers orphan cleanup, the failure path can return -ENOENT, and the VFS may splice a negative dentry into the cache for what is actually a valid subvolume. That is a textbook example of how a one-bit bookkeeping mistake can cascade into a persistent namespace error.
 Why this matters to operators
Why this matters to operators
From an administrator’s point of view, this is e case. A broken subvolume dentry can block deletion, confuse automation, and make filesystem cleanup jobs fail in ways that look like corruption even when the on-disk metadata is mostly intact. The bug can also present as a hard-to-explain operational trap: the subvolume appears in one tool, disappears in another, and only recovers after a cache invalidation or other intervention that changes lookup behavior.The fact that Microsoft’s advisory portal surfaced the issue is also a reminder that Linux filesystem Ch enterprise vulnerability workflows far beyond the traditional kernel community. The NVD record says the CVE was newly received from kernel.org on April 22, 2026, and the Microsoft entry mirrors that publication path, even though the underlying issue is entirely in Linux Btrfs code. That matters for mixed-platform shops: the visibility layer may be Microsoft, but the remediation path is still kernel backporting and vendor coordination.
- The problem is a lifecycle inconsistency, not a flashy memory-corruption bug.
- The visible symptom is a **broken subbehaves inconsistently under lookup and deletion.
- The kernel error string
could no2is a strong diagnostic clue. - The fix is conceptually simple: mark the subvolume root earlier, at create tilure Mode
btrfnd from there callsbtrfs_orphan_cleanup(). When that cleanup returns-ENOENT, the lookup code can convert the result into a negative dentry viad_splice_alias(NULL, dentry)`, which then poisons subsequent operations on the same name. In practice, the namespace ends up asserting that a real subvolume does not exist, even though it clearly still does.That failure mode is not just confusing; it is self-reinforcing. Once the VFS caches a negative dentry, later operations may continue to hit the wrong state until the cache is dropped. The report explicitly notes that dropping thtigate the issue, which is a strong sign the problem lives at the intersection of lookup caching and Btrfs internal cleanup state rather than in a permanently damaged tree. In other words, the filesystem is not necessarily wrecked, but the namespace has drifted out of sync with reality.
Why ENOENT becomes dangerous here
ENOENT is normally a harmless “not found” result. In this case, though, it is being returned from a code path that is expected to be a first-time orphan cleanup check, not a genuine proof that the subvolume absent. That distinction is crucial. The error is not telling users that the subvolume has been deleted; it is telling the lookup layer that cleanup failed in a way that should not have been interpreted as absence.The report also explains that there were no orphan items for the subvolume, and the subvolume was otherwise healthy-looking, which helps rule out the obvious explanations. That means the lookup code was not reacting to a half-deleted root, but to stale internal state. Th that can survive casual inspection because the on-disk tree looks normal while the in-memory lifecycle flags are subtly wrong.
ENOENThere is a failure-path artifact, not a proof the subvolume is gone.- A negative dentry can make a valid subvolume look absent to later operations.
- The issue is recoverable in the sense that cache invalidation can change behavior.
- The namespace and the filesystem metadaeing with each other.
Root Cause Analysis
The key technical observation isleanup()itself setsBTRFS_ROOT_ORPHAN_CLEANUPwithtest_and_set_bit()`, so ionly once per root. That design makes sense: once cleanup has run, the filesystem shoung the same setup logic on every lookup. But if subvolume creation does not set the bwindow where the root exists, appears valid, and yet still looks uninitialized to the later lookup path.The report makes a strong case that this is what happened. The subvolume was created earlier, but the meaningful first orphan cleanup call occurred later, after the object had already been exposed to the dentry cache. If anything then caused the dentry to be re-evaluated, lookup could invoke orphan cleanup for the first time in a state that no longer matched the object’s actual lifetime. That m the door to the false-negative interpretation and the resulting negative dentry.
Why the create path matters
The fix lands at creation time because that is the earliest point where the root’s lifetime becomes externally visible.create_subvol() uses d_instantiate_new(), but the report says it does not set BTRFS_ROOT_ORPHAN_CLEANUP. That omission is the heart of the bug. Once the subvolume is inserted into the dentry cache without the bit set, the system has already committed to a namleanup state is incomplete.This is a good reminder that many filesystem bugs are really lifecycle bugs. The code did not merely forget a flag in some abstract sense; it forgot to mark the root as having crossed a state boundary at the exact moment the VFS began treating it like a real directory entry. In kernel code, those boundaries matter because a missed transition can ripple into orphan handling, deletion semantics, and even transaction behavior.
- The bugion failure** in root initialization.
BTRFS_ROOT_ORPHAN_CLEANUPshould have been established before the root became cache-visible.- The create path and the lookup path were operating with different assumptions.
- The filesystem’s internal invariants were technically consistent, but temporally wrong.
Dentry Cache and Negative Lookup
One of the most important parts of the report is the emphasis on the dentry curns-ENOENT, the VFS may cache that result as a negative dentry, whhe general case but disastrous if the “not found” verdict is false. In this CVE, the stale root ine exactly that: the cache learns the wrong answer and keeps repeating it until cachat explains why deleting the subvolume can fail while creating something new over the sameThe cache believes the name is already associated with an existing object and also that the object is not valid in the way the caller expects. Those contradictory answers are a strong signal that the lookup path has become detached from the actual subvolume state.Why cache invalidation helps
The report says the bug can be mitigated by dropping the dentry cache, after which deleting the subvolume can succeed. That points toward a lookup-layeistent on-disk inconsistency. It also shows how brittle the failure is: a purely in-memory representation can block administrative actions even when the underlying structure is still repairable.This kind of bug is especially frustrating in production because it can look like intermittent corruption. An operator may see one tool fail, another tool succeed after some unrelatedhird tool behave differently after a reboot. The real issue is not random corruption but a stale namespace cache anchored to the wrong lifecycle assumption.
- The VFS dentry cache turns a transient misread into a persistent bad answer.
- Negative dentries are useful normally, but dangerous when the lookup result is wrong.
- Cache invalidation can hide the bug without actually fixing the root namespace bugs often feel “haunted” to administrators.
Races and Timing Windows
The published description spends a lot of effort explaining why the problem is not just a simple missing flag. It describes two potential race windows: one around writeback and unlink, and another around lookup and delayediput() behavior. Those races matter because thes where a subvolume’s dentry can become evictable or re-evaluated while its inode sthich makes the stale cleanup flag reachable at exactly the wrong moment.The delayed-ip subtle. The report says ordered extent creation uses
igrab() on the inode, aked and closed while those references remain, iput() in __dentry_kii_count without triggering eviction. That can free the child dentry and leave the subvolume dentry in a state where it becomes evictable while the inode is still alive, which is precisely the kind of timing-sensitive condition that can expose a latent lifecycle bug.Why this is hard to test
These are not the kind of issues that a simple smoke test will catch. They require a particular interleaving of lookup, dentry eviction, delayed cleanup, and subvolume or inode lifetime transitions. That is es diagrams and detailed phase breakdowns: the bug lives in the seams between code paths, not in any single function.It also helps explain why the problem can persist for some time before becoming visible. A root may behave normally across many operations, then suddenly fail after a cache eviction or unrelated memory pressure event changes the order in which delayed references are released. That makes the CVE more dangerous from an operations perspective, because it is *predictably unpred depends on narrow timing windows rather than a single deterministic path.
- Delayed
iput()behavior can leave the inode alive while the dentry state changes. - The failure is sensitive to cache eviction and reference-count choreography.
- This is the kind of bug that tends to evade ordinary QA.
Why the Fix Is Small but Important
The fix is to set `BTRFS_Ruring subvolume creation, which is conceptually modest but structurally meaningful. It aligns the root’s metadata state with the fact that the subvolume is now a real namespace object, so later lookup does not have to infer whether orphan cleanup has already happened. In other words, the patch closes the gap between creation and first lookup.That kind of fix is often the best possibk. It does not change external APIs, it does not invent a new recovery model, and it does em redesign. It simply restores the intended invariant so the rest of the code can trusin. Those are the patches that stable maintainers usually like because they are cally obvious.
What this says about Btrfs maintenance
aintenance lesson here: Btrfs often fails not because the storage model is fundamentally broken, but because the number of state transitions is so large that one path falls out of sync with the others. Subvolumes, orphans, dentries, delayed references, and lookup caching each have legitimate rules of their own. The challenge is making sure the transitions between them are made in the right order every time.That is why a bug like thwhile without looking dramatic. It is not a classic crash bug or memory safety issue. It is an accounting and lifecycle mismatch that only becomes visible when the exact combination of cache state and cleanup timing lines up badly. That makes the CVE operationally important even though the patch itself is small.
- The patch restores the intended invariant at subvolume creation time.
- Itp cleanup from misclassifying a valid subvolume.
- The change is small, but the consequences of omitting it were wide-ranging.
- This is the kind of fix that tends to backport cleanly into stable kernels.
Enterprise and Consumer Impact
For enterprise operators, the practical concern is not just filesystem hygiene; it is workflow disruption. A broken subvolume dentry can block scripted maintenance, break cleanup tools, confuse orchestration, and create false algrity. If the subvolume is part of a larger storage workflow, the failure can propagate into backup, snapshot, or provisioning automation that assumes the namespace is trustworthy.Consumer systems are less likely to encounter the bug in day-to-day use, but they are not immune. Anyone running a Btrfs-based desktop, lab machine, or home server with subvolume-heit the edge case if the right dentry and cleanup timing occurs. The differenceystems are more likely to expose the issue at scale, where rare races becomtable over time.
Why scale matters
In a small environment, a user may siches, and move on. In a fleet, the same bug can become a recurring operational automation layer repeats the failing lookup path thousands of times. That is how a correctness flaw turns into a support burden: not through brilliance from an attacker, but through repetition and scale.The fact that NVD had not yet assigned a CVSS score at the time of publication should not lull anyone into treating the bug as low priority. The description itself is enough to show that the issue can strand a valid subvolume in an inconsistent state and interfere woperations. In operational terms, that can be enough to break management workflows even if the issue does not map neatly to a traditional exploitation story.
- Enterprise fleets are more likely to amplify rare races into visible incidents.
- Consumer systems may see it less often, but still depend on the same vulnerable code path.
- The absence of a CVSS score is not a signal that the issue is harmless.
can matter as much as overt system failure.
Strengths and Opportunities
The strongest aspect of this disclosure is its clarity. The report ties together the user-visible symptom, the kernel error path, the dentry-cache effect, and the lifecycle bug in a way that gives operators a real mental model for triage. That makes it easier to identify whether a system is affected anidation or patching is the right next step.There is also a genuine maintenance opportunity here for distribution vendors and OEMs. Bugs like this are easy to dismiss because they do not sound like headline-grabbing exploitation paths, but they can still generate expensive support incidents when subvolume workflows are central to storage management. Clear backports and concise advisories help prevent small kernel bugs from becoming big operaThe fix is narrow and backportable.
- The root cause is well enough understood to ghe symptom is distinctive, which helps triage.
- The bug teaches a useful lesson about lifecylesystem code.
Vendor patching can eliminate a class of support headache
Risks and Concerns
The biggest concern is underestimationframed as a cleanup-state issue rather than a memory-safety problem, some teams may decide it is not urgent. That would be a mistake for systems that rely heavily on Btrfs subvolumes, snapshot-driven workflows, or automated filesystem maintenance, where a broken dentry can block normal operations and create cascading errors.There is also the risk of patch lag. Even when a fix is published upstream, dotake time to ship a corrected kernel, and appliances may remain exposed longer than generic servers. For enterprise users, that lag is often the real exposure window, because the production kernel is the vendor backport, not the upstream commit.
Operational concerns to keep in mind
A subvolume that appears present but cannot be managed is a dangerous kind of inconsistency because it resists simple administratinly workaround is cache clearing or a more i, operations teams may end up with a service interruption even iftill intact. That is why correctness bugs in cleanuattention.Another concern is that bugs of this style can hide adjacent assumptioissue is found, maintainers often discover related lifetime or cleanup bugs nearn this CVE implies a wider catastrophe, but it does mean the patch should be treated as part of an ongoing hardening effort rather than as an isolated one-off.
- Teams may misclassify the issue as a harmless housekeeping problem.
- Vendor backports may lag behind the published kernel fix.
- The bug can disrupt automation even when no data loss is obvious.
- Cache state can mask the underlying problem untfails.
- Similar lifecycle bugs may exist in nearby Btrfs paths.
What to Watch Next
The immediate question is how quickly the fix propagates through stable Linux trees and vendor kernels. The NVD entry shows the issue was freshly published on April 22, 2026, and the linked stable commit references indicate that the patch has already remediation stream. For most real-world users, the decisive factor will be whether their distribution has pulled in that stable fix rather than whether the original kernel.org patch exists somewhere upstream.It is also worth watching for vendor advisories that map the CVE to package versions and backport status. Linux filesystem CVEs often become operationally relevant only when a distro or appliance vendor confirms exactlxed. Without that mapping, defenders are left inferring exposure from mainline commit history, which is useful but not always enough for production triage.
Practical things to monitor
- Whether your distribution kernel includes the
BTRFS_ROOT_ORPHAN_CLEANUPcreation-time fix. - Whether Btrfs subvolume workflows in your environment show broke- Whether cleanup scripts or provisioning tools hit
ENOENTandEEXISTin- Whether vendor advisories provide explicit build numbers orWhether additional Btrfs cleanup-path bugs appear in nearby maintenannger-term story is that this CVE reinforces a familiar truth about filesystemsbugs are often not the loudest ones, but the ones that quieionship between what the cache believes and what the on-disk structure actually is. Btrfs continues to evolve, and this fix is a reminder that even a single missing state bit can tilt the balance between a working namespace and a stubbornly broken one. The good news is that this is the kind of bug kernel maintainers know how to fix, and the published patch looks precisely targeted enough to reduce risk without broad collateral damage.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center