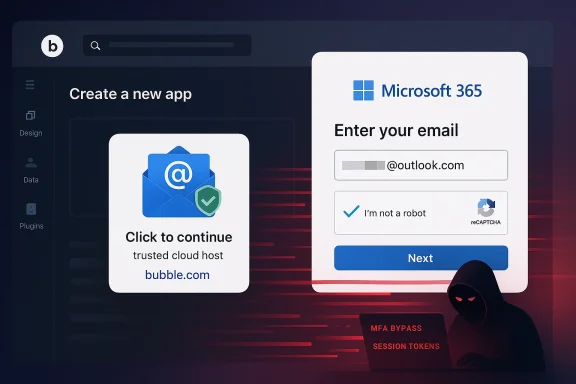
Cybercriminals are increasingly abusing legitimate cloud services to make phishing attacks harder to spot, and the latest example involves Bubble.io, a popular no-code app builder now being used as a launchpad for Microsoft 365 credential theft. The core trick is simple but effective: build a convincing login page on a trusted domain, route victims there from email, and rely on reputation systems to let the message slip through. Security researchers say this kind of abuse is especially worrying because it lowers the technical barrier for attackers while raising the odds that the fake page reaches the inbox in the first place.
Phishing has always evolved by following the path of least resistance, and the current wave is no exception. Once attackers realized that standalone lookalike domains were easier to detect, they shifted toward compromised websites, cloud apps, and trusted SaaS infrastructure that can lend legitimacy to a malicious link. Bubble.io fits that pattern neatly because it lets users build and host apps quickly without writing traditional code, which is exactly the kind of convenience attackers exploit when they want speed, scale, and deniability.
The reported abuse matters because Microsoft 365 remains one of the most valuable credential targets on the internet. A successful login theft can open access to email, file storage, Teams chats, SharePoint libraries, billing data, and internal workflows. For a criminal, that is more than a password; it is a doorway into identity, trust, and sometimes the entire organizational perimeter.
This is not the first time attackers have used legitimate services as a cover. In recent years, researchers have documented abuse of QR codes, internal mail routing features, cloud-based alerts, and other trusted channels to bypass filters and make malicious traffic look routine. The latest Bubble.io case is important because it combines several trends at once: no-code tooling, trusted hosting, fake CAPTCHA or verification interstitials, and phishing kits designed to automate the hardest parts of the scam.
Kaspersky has long warned that phishing is becoming more industrialized, not more amateur. Its recent research on phishing-as-a-service shows a market where subscription kits already support Microsoft 365 theft, 2FA interception, and anti-analysis measures like geofencing or challenge pages. That context helps explain why a Bubble-hosted lure is so dangerous: the platform itself is not the attack, but it can be the delivery layer that makes the attack more successful.
Bubble has also publicly emphasized security features such as encryption, privacy rules, and automated scans, which underscores the tension at the heart of the story. A platform can be secure in the conventional sense and still be abused as an application host by bad actors who understand how to weaponize trust. That is the uncomfortable reality of modern SaaS ecosystems: the same qualities that make them useful to legitimate builders can make them attractive to criminals.
The page itself is built to impersonate Microsoft’s sign-in flow. According to the reporting, some of these pages are hidden behind a Cloudflare check or similar gating layer, which makes automated analysis more difficult and helps the fraud appear more polished to the victim. The result is a login experience that feels ordinary enough to pass a quick glance, especially on a mobile screen or during a rushed workday.
There is also a social-engineering advantage. Victims often assume that if a link points to a recognized platform, the page must be legitimate, especially if the email is already framed as a Microsoft alert or an account verification request. Attackers know that most users do not inspect the full URL string, the hosting domain, or the page’s behavior under the hood.
That is why Kaspersky and others keep stressing that credential theft is not a contained event. A compromised business account can be used to launch internal phishing, invoice fraud, data exfiltration, or ransomware deployment. In other words, the initial phishing page is only the first rung on a ladder that can end in an enterprise incident.
The platform’s value to attackers is not that it is inherently malicious. It is that it sits in a class of services that security teams often treat as low-friction business tools, not high-risk attack surfaces. That makes abuse harder to spot at first glance, especially when a page is tucked under a subdomain or behind a custom domain configured to look like an ordinary business site.
This creates a broader security paradox. The more friction we remove from software creation, the more we empower both builders and abusers. That is not an argument against no-code platforms, but it is a reminder that trust controls have to evolve at the same speed as development tools.
That matters because the cybercrime market rewards reproducibility. If one attacker develops a reliable method to get malicious pages through inbox filters, the technique can be copied, resold, and scaled quickly. The result is a multiplier effect in which a single abuse path becomes an operational template for many others.
This is why a single compromised account can become a company-wide problem. Attackers often use a legitimate mailbox to send follow-on phishing messages that appear to come from a coworker or manager, which dramatically increases click-through rates. If defenders do not move quickly, the attack can shift from external phishing to internal trust abuse in a matter of hours.
That is why security teams need phishing-resistant controls such as hardware-backed authentication, conditional access, and token protection where possible. Even then, organizations should assume that some phishing attempts will reach users, because the email layer is only one part of the chain. Defenses have to be layered or they are brittle.
The practical difference is response speed. A consumer may notice a strange login or a missing email and recover later, but an organization can experience immediate operational disruption. If an attacker uses the account to impersonate leadership or request wire transfers, the incident quickly becomes a financial and reputational problem.
The Bubble abuse story shows how defenders are forced into a difficult tradeoff. If they block all links to a trusted low-code platform, they risk false positives and user complaints. If they allow the domain wholesale, they may let a malicious app through. That is a classic trust inversion problem, and it is becoming more common across cloud services.
Even a simple CAPTCHA-style checkpoint can be enough to break naive scanning or defang a crawler. If the analysis engine cannot get past the gate, it may not see the fake login page beneath it, and the malicious URL can look harmless. That gap is where attackers are placing their bets.
That is exactly why abuse of legitimate platforms is so effective. A trusted hosting domain can do part of the attacker’s job before the victim even opens the link. In security terms, the malicious content is only half the story; the delivery channel is the other half.
The best response is probably not one giant policy change, but a stack of targeted controls. Providers can monitor for login-page impersonation patterns, suspicious redirect chains, repeat abuse signals, and anomalous domain reputation behavior. They can also make it easier for users and defenders to report malicious apps and quickly suspend them when the evidence is strong.
That reputational damage can spill over onto legitimate users, too. Businesses using the platform for internal tools or customer-facing apps may encounter more friction from browsers, filters, and security teams if the ecosystem is tainted by abuse. In that sense, abuse harms both the platform and its honest customers.
The most effective defense is still a combination of technical and human controls. Security teams should train users to check the domain carefully, verify unexpected Microsoft prompts through alternate channels, and report suspicious pages even when they appear to sit on reputable infrastructure. The moment a page asks for credentials, trust should drop sharply.
The real contest will be between platform governance and attacker adaptability. If Bubble and similar services improve detection, shorten abuse response times, and collaborate with security vendors, they can raise the cost of abuse enough to matter. If not, the model will be copied across the no-code and low-code landscape until inbox trust erodes further.
What to watch next:
Source: TechRadar This popular app builder has been hijacked to steal Microsoft account details - here's what we know
 Background
Background
Phishing has always evolved by following the path of least resistance, and the current wave is no exception. Once attackers realized that standalone lookalike domains were easier to detect, they shifted toward compromised websites, cloud apps, and trusted SaaS infrastructure that can lend legitimacy to a malicious link. Bubble.io fits that pattern neatly because it lets users build and host apps quickly without writing traditional code, which is exactly the kind of convenience attackers exploit when they want speed, scale, and deniability.The reported abuse matters because Microsoft 365 remains one of the most valuable credential targets on the internet. A successful login theft can open access to email, file storage, Teams chats, SharePoint libraries, billing data, and internal workflows. For a criminal, that is more than a password; it is a doorway into identity, trust, and sometimes the entire organizational perimeter.
This is not the first time attackers have used legitimate services as a cover. In recent years, researchers have documented abuse of QR codes, internal mail routing features, cloud-based alerts, and other trusted channels to bypass filters and make malicious traffic look routine. The latest Bubble.io case is important because it combines several trends at once: no-code tooling, trusted hosting, fake CAPTCHA or verification interstitials, and phishing kits designed to automate the hardest parts of the scam.
Kaspersky has long warned that phishing is becoming more industrialized, not more amateur. Its recent research on phishing-as-a-service shows a market where subscription kits already support Microsoft 365 theft, 2FA interception, and anti-analysis measures like geofencing or challenge pages. That context helps explain why a Bubble-hosted lure is so dangerous: the platform itself is not the attack, but it can be the delivery layer that makes the attack more successful.
Bubble has also publicly emphasized security features such as encryption, privacy rules, and automated scans, which underscores the tension at the heart of the story. A platform can be secure in the conventional sense and still be abused as an application host by bad actors who understand how to weaponize trust. That is the uncomfortable reality of modern SaaS ecosystems: the same qualities that make them useful to legitimate builders can make them attractive to criminals.
How the Attack Works
At a practical level, the scheme is a form of reputation laundering. The attacker creates or hosts a phishing app on a domain that already looks legitimate to mail filters, then sends an email that points victims to that page. Because the destination is not a freshly registered scam domain, some security products are less likely to treat the message as suspicious, and the email lands in the inbox rather than quarantine.The page itself is built to impersonate Microsoft’s sign-in flow. According to the reporting, some of these pages are hidden behind a Cloudflare check or similar gating layer, which makes automated analysis more difficult and helps the fraud appear more polished to the victim. The result is a login experience that feels ordinary enough to pass a quick glance, especially on a mobile screen or during a rushed workday.
Why trusted hosting matters
Most email defenses are tuned to score sender reputation, link reputation, and destination reputation. When the destination is a broadly trusted SaaS domain, the entire equation changes, because a malicious path can inherit some of the trust associated with the parent platform. That does not make the page safe, but it can make it look safer to the systems trying to filter it.There is also a social-engineering advantage. Victims often assume that if a link points to a recognized platform, the page must be legitimate, especially if the email is already framed as a Microsoft alert or an account verification request. Attackers know that most users do not inspect the full URL string, the hosting domain, or the page’s behavior under the hood.
- Trusted domains can reduce the odds that a message is filtered.
- Cloudflare-style interstitials can slow analysis and frustrate bots.
- Fake Microsoft branding increases the chance of credential entry.
- Mobile users are especially vulnerable to visual shorthand and haste.
The credential-harvesting step
Once the victim types in a username and password, the attackers collect the credentials and can try them immediately. In the Microsoft 365 world, that is often only the beginning, because the real prize is access persistence. If the account is protected by weak MFA controls or the criminals can steal session tokens and codes in real time, they may be able to move far beyond a simple password reset scenario.That is why Kaspersky and others keep stressing that credential theft is not a contained event. A compromised business account can be used to launch internal phishing, invoice fraud, data exfiltration, or ransomware deployment. In other words, the initial phishing page is only the first rung on a ladder that can end in an enterprise incident.
Why Bubble.io Is a Useful Abuse Vector
Bubble.io is designed to help people build software quickly, which means it gives users powerful primitives: frontend design, logic, hosting, integrations, and sometimes AI-assisted creation. For legitimate founders and internal teams, that is a productivity win. For criminals, those same primitives can be repurposed into an efficient phish factory with far less work than coding and hosting a bespoke fake portal from scratch.The platform’s value to attackers is not that it is inherently malicious. It is that it sits in a class of services that security teams often treat as low-friction business tools, not high-risk attack surfaces. That makes abuse harder to spot at first glance, especially when a page is tucked under a subdomain or behind a custom domain configured to look like an ordinary business site.
The no-code paradox
No-code platforms compress development time dramatically, which is their selling point. That compression also compresses the time required for abuse, because attackers no longer need a separate hosting stack, a frontend framework, or a deep understanding of deployment pipelines. They can focus on the social engineering and let the platform handle the rest.This creates a broader security paradox. The more friction we remove from software creation, the more we empower both builders and abusers. That is not an argument against no-code platforms, but it is a reminder that trust controls have to evolve at the same speed as development tools.
Why attackers like lower skill requirements
Phishing kits already let less-skilled criminals launch credible campaigns without building their own infrastructure. Kaspersky’s earlier reporting on phishing-as-a-service showed subscription-based tooling that can mimic Microsoft login pages, intercept 2FA, and automate credential capture. Bubble-hosted phishing pages fit naturally into that ecosystem because they can serve as the hosted endpoint for a kit’s lure page or redirect chain.That matters because the cybercrime market rewards reproducibility. If one attacker develops a reliable method to get malicious pages through inbox filters, the technique can be copied, resold, and scaled quickly. The result is a multiplier effect in which a single abuse path becomes an operational template for many others.
- Faster setup lowers attacker cost.
- Trusted hosting improves deliverability.
- Reusable kits make the technique scalable.
- Low-code tools reduce the skill barrier.
Microsoft 365 Remains the Prize
Microsoft 365 credentials are attractive because they often unlock both identity and data. Email access enables password resets for other services, invoice manipulation, and business process interception. File access can expose contracts, payroll, customer records, or strategy documents, while calendar and chat access can reveal organizational structure and timing.This is why a single compromised account can become a company-wide problem. Attackers often use a legitimate mailbox to send follow-on phishing messages that appear to come from a coworker or manager, which dramatically increases click-through rates. If defenders do not move quickly, the attack can shift from external phishing to internal trust abuse in a matter of hours.
Why MFA is not a silver bullet
Multi-factor authentication remains essential, but the current generation of phishing kits is increasingly designed to work around it. Some kits ask for one-time codes in real time, others capture session cookies, and still others use prompt fatigue or proxy techniques to defeat basic defenses. The problem is not that MFA is obsolete; it is that attackers have adapted to its presence.That is why security teams need phishing-resistant controls such as hardware-backed authentication, conditional access, and token protection where possible. Even then, organizations should assume that some phishing attempts will reach users, because the email layer is only one part of the chain. Defenses have to be layered or they are brittle.
Business impact versus consumer impact
For consumers, a stolen Microsoft account can mean identity theft, loss of personal files, and access to other linked services. For enterprises, the blast radius is far larger because Microsoft 365 is often tied to business communications, compliance data, and downstream SaaS integrations. In a corporate setting, a single compromised mailbox can trigger helpdesk resets, vendor fraud, and lateral movement.The practical difference is response speed. A consumer may notice a strange login or a missing email and recover later, but an organization can experience immediate operational disruption. If an attacker uses the account to impersonate leadership or request wire transfers, the incident quickly becomes a financial and reputational problem.
- Email compromise often leads to password reset abuse.
- File access can expose sensitive business data.
- Teams and SharePoint access widen the attack surface.
- Internal trust makes follow-on scams more effective.
How Security Filters Get Tricked
Modern email security products rely on a blend of reputation, content analysis, URL inspection, attachment scanning, and behavioral signals. That works well against a lot of commodity spam, but it becomes much less reliable when an attacker uses a valid infrastructure layer that is also home to legitimate business traffic. The malicious page may be new, but the domain neighborhood is not.The Bubble abuse story shows how defenders are forced into a difficult tradeoff. If they block all links to a trusted low-code platform, they risk false positives and user complaints. If they allow the domain wholesale, they may let a malicious app through. That is a classic trust inversion problem, and it is becoming more common across cloud services.
The role of interstitials and anti-bot checks
A page hidden behind a Cloudflare challenge or similar gate can frustrate automated analysis tools and sandboxes. It may also cause the page to behave differently depending on geography, browser fingerprint, or visitor type, which makes it harder for defenders to reproduce the exact malicious flow. These anti-analysis techniques are not new, but they are increasingly common in phishing operations because they buy time.Even a simple CAPTCHA-style checkpoint can be enough to break naive scanning or defang a crawler. If the analysis engine cannot get past the gate, it may not see the fake login page beneath it, and the malicious URL can look harmless. That gap is where attackers are placing their bets.
Why deliverability is the real battleground
In many campaigns, the hardest part is not building the fake page. It is getting the message into a victim’s inbox with enough credibility to prompt action. Attackers therefore optimize for deliverability first and page realism second, because a perfect phish seen by no one is useless.That is exactly why abuse of legitimate platforms is so effective. A trusted hosting domain can do part of the attacker’s job before the victim even opens the link. In security terms, the malicious content is only half the story; the delivery channel is the other half.
- Reputation systems can be fooled by legitimate hosting.
- Anti-bot layers can hide the true destination from scanners.
- Geo-fencing can make analysis inconsistent.
- Inbox placement is often more valuable than perfect realism.
What Bubble and Similar Platforms Should Do
Bubble already advertises security features, which is useful but not sufficient in a scenario where the platform itself is being abused as a phishing host. The challenge for low-code providers is to detect abuse without punishing legitimate customers who are building ordinary applications. That means balancing platform openness with stricter abuse detection, faster takedowns, and clearer reporting channels.The best response is probably not one giant policy change, but a stack of targeted controls. Providers can monitor for login-page impersonation patterns, suspicious redirect chains, repeat abuse signals, and anomalous domain reputation behavior. They can also make it easier for users and defenders to report malicious apps and quickly suspend them when the evidence is strong.
A platform-provider playbook
- Detect obvious impersonation of major identity providers.
- Review apps that mimic Microsoft, Google, or banking login flows.
- Flag challenge pages that conceal credential collection forms.
- Accelerate abuse reporting and takedown workflows.
- Share indicators with security vendors when abuse is confirmed.
- Improve transparency around suspended or investigated apps.
Why platform governance matters
No-code services are no longer just developer tools. They are part of the modern internet’s trust fabric, and that makes them part of the security perimeter whether they like it or not. If one platform becomes known as an easy place to host phishing pages, its reputation can suffer beyond the immediate abuse case.That reputational damage can spill over onto legitimate users, too. Businesses using the platform for internal tools or customer-facing apps may encounter more friction from browsers, filters, and security teams if the ecosystem is tainted by abuse. In that sense, abuse harms both the platform and its honest customers.
- Stronger abuse detection helps preserve trust.
- Faster response limits exposure windows.
- Transparency reduces collateral damage.
- Better reporting channels help defenders act quickly.
What Enterprises Should Do Now
Organizations should treat this trend as a reminder that email security alone is not enough. If the link destination can hide behind a trusted service, then the browser and identity layer become the real enforcement points. That means tightening controls around sign-ins, hardening user training, and monitoring for suspicious access immediately after credential entry.The most effective defense is still a combination of technical and human controls. Security teams should train users to check the domain carefully, verify unexpected Microsoft prompts through alternate channels, and report suspicious pages even when they appear to sit on reputable infrastructure. The moment a page asks for credentials, trust should drop sharply.
Practical defensive steps
- Require phishing-resistant MFA where feasible.
- Review conditional access and session token policies.
- Alert on impossible travel and unusual sign-in patterns.
- Block or scrutinize newly introduced low-reputation app hosts.
- Train users to distrust login prompts reached from email.
- Ensure incident response can reset sessions quickly.
- Watch for follow-on mailbox rules, forwarding, or delegate changes.
Consumer guidance still matters
Individuals are not immune just because they do not manage a corporate tenant. Personal Microsoft accounts can still contain email, OneDrive files, subscriptions, and recovery details that feed into other services. If a login page arrives from an unexpected email, the safest move is to navigate to the service directly rather than using the link.- Use direct navigation for sensitive logins.
- Avoid entering credentials from email prompts.
- Verify the exact domain before signing in.
- Enable account alerts and recovery protections.
- Treat CAPTCHA or “verification” screens with skepticism if they arrive by email link.
Strengths and Opportunities
The silver lining is that this story gives defenders a better map of how modern phishing campaigns are evolving. It also shows where policy, platform controls, and user awareness can still make a meaningful difference. If providers and enterprises act on the lesson quickly, they can cut off a technique that thrives on novelty and confusion.- Trusted-service abuse is visible once defenders know what to look for.
- No-code platforms can add abuse telemetry without harming legitimate builders.
- Email security vendors can tune detections around impersonation patterns.
- Identity teams can prioritize phishing-resistant controls for Microsoft 365.
- Security awareness training can emphasize destination checking, not just sender checking.
- Rapid takedown processes can limit the shelf life of malicious apps.
- Cross-vendor sharing can reduce the time between discovery and blocking.
Risks and Concerns
The biggest concern is that successful abuse creates a copycat effect. Once criminals see that Bubble-hosted pages can land in inboxes more reliably, the method can spread through phishing kits and be reused against more targets. The attack surface is also likely to expand as legitimate platforms adopt more AI-assisted creation tools that make harmful pages faster to assemble.- Phishing-as-a-service operators may package this method for resale.
- False positives could lead defenders to block legitimate no-code apps.
- Users may become desensitized to warnings if trusted domains are abused often.
- Multi-factor authentication can be bypassed through real-time phishing or token theft.
- Reputation systems may struggle to keep pace with rapidly created malicious apps.
- Organizations could face internal phishing after the first account compromise.
- Platform trust damage may spill over to honest customers and partners.
Looking Ahead
The most likely near-term outcome is not a single dramatic wave, but steady normalization. As more phishing kits integrate trusted-host delivery and anti-analysis steps, the technique will become one more tool in the attacker’s playbook. That is exactly how these methods usually spread: first as a novelty, then as a reliable commodity, and finally as a default option for less sophisticated criminals.The real contest will be between platform governance and attacker adaptability. If Bubble and similar services improve detection, shorten abuse response times, and collaborate with security vendors, they can raise the cost of abuse enough to matter. If not, the model will be copied across the no-code and low-code landscape until inbox trust erodes further.
What to watch next:
- Expansion of phishing kits that support trusted SaaS hosting.
- Faster takedown workflows from low-code and hosting providers.
- More Microsoft 365 campaigns using fake challenge pages or CAPTCHA gates.
- Increased browser-side and identity-side detection of suspicious sign-ins.
- Security vendor guidance on evaluating links hosted on legitimate app platforms.
Source: TechRadar This popular app builder has been hijacked to steal Microsoft account details - here's what we know