Microsoft Defender Experts have uncovered a coordinated developer‑targeting campaign that uses malicious Next.js repositories and recruiting‑style technical assessments as the initial lure, turning routine developer actions—opening a project in Visual Studio Code, starting a dev server, or booting a backend—into reliable paths for in‑memory JavaScript execution and staged command‑and‑control. (microsoft.com)
The attack cluster described by Microsoft leverages familiar developer workflows and trusted developer platforms to hide malicious activity inside otherwise normal project artifacts. Attackers seeded multiple repository families with repeatable naming patterns (for example, Cryptan, JP‑soccer, RoyalJapan, SettleMint) and near‑duplicate variants (v1, master, demo, platform, server) so that naive or rushed hands on a corporate developer machine would run into the trap naturally. By pivoting on shared file placement, loader structure, and repository conventions, analysts expanded a small set of telemetry hits into a broader set of related repositories and staging infrastructure. (microsoft.com)
This behavior sits squarely inside a larger trend: threat actors increasingly use Node.js and JavaScript runtimes as a delivery and execution vector, because Node is ubiquitous among developers and often runs with access to sensitive artifacts, credentials, and build systems. Microsoft has previously warned about malicious use of Node.js runtimes and supply‑chain compromises that weaponize developer tooling and package ecosystems.
By mapping developer workflows to concrete detection signals, applying strict workspace trust and attack surface reduction, and operationalizing identity and session remediation, organizations can reduce the likelihood that a single recruiting‑style repo will become the entry point to a broader compromise. The Microsoft findings are a clear call to action: prioritize developer‑centric visibility and treat the developer workstation as a first‑class element of enterprise security. (microsoft.com)
Source: Microsoft Developer-targeting campaign using malicious Next.js repositories | Microsoft Security Blog
 Background / Overview
Background / Overview
The attack cluster described by Microsoft leverages familiar developer workflows and trusted developer platforms to hide malicious activity inside otherwise normal project artifacts. Attackers seeded multiple repository families with repeatable naming patterns (for example, Cryptan, JP‑soccer, RoyalJapan, SettleMint) and near‑duplicate variants (v1, master, demo, platform, server) so that naive or rushed hands on a corporate developer machine would run into the trap naturally. By pivoting on shared file placement, loader structure, and repository conventions, analysts expanded a small set of telemetry hits into a broader set of related repositories and staging infrastructure. (microsoft.com)This behavior sits squarely inside a larger trend: threat actors increasingly use Node.js and JavaScript runtimes as a delivery and execution vector, because Node is ubiquitous among developers and often runs with access to sensitive artifacts, credentials, and build systems. Microsoft has previously warned about malicious use of Node.js runtimes and supply‑chain compromises that weaponize developer tooling and package ecosystems.
How the campaign works: three developer‑centric execution paths
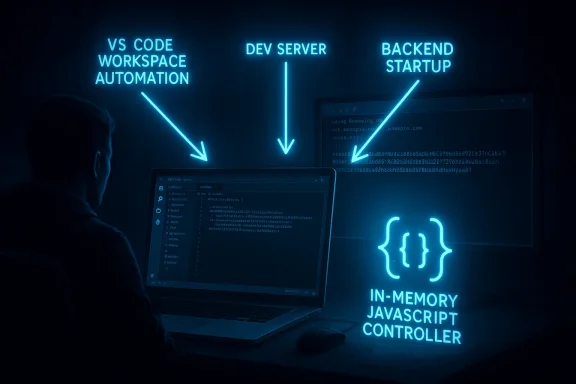
Microsoft’s analysis reveals three primary entry vectors, each designed to trigger during normal developer activity yet all converging to the same outcome: runtime retrieval and in‑memory execution of attacker‑controlled JavaScript that transitions into a multi‑stage C2 (command‑and‑control) flow. The campaign places redundancy in the attack surface so that if one execution path is blocked, another will likely succeed. (microsoft.com)1) Visual Studio Code workspace automation (folder open → execute)
- Malicious repositories include a .vscode/tasks.json configured with runOn: "folderOpen". When a developer opens the workspace and trusts the folder, VS Code executes the task automatically.
- A companion fallback — an obfuscated JavaScript blob processed during workspace initialization — exists in some variants to cover environments that restrict tasks.
- Both approaches fetch a JavaScript loader from attacker‑controlled staging hosted on PaaS platforms (observed Vercel domains) and execute it with Node.js, after which the loader begins beaconing to persistent C2 servers. (microsoft.com)
2) Build‑time / dev‑server execution (npm run dev → trojanized asset runs)
- Trojanized application assets—commonly a modified jquery.min.js or other library file—contain obfuscated loader code that decodes a base64 URL, retrieves an on‑demand loader from a staging endpoint, and executes it in memory with Node.
- This path executes when a developer runs the local dev server (npm run dev, next dev, etc.), providing an alternative trigger when editor automation is disabled or refused. (microsoft.com)
3) Backend startup / module import (server boot → env exfiltration + RCE)
- Malicious loader logic is embedded in backend modules or route files that run during server initialization or at require‑time.
- Repositories commonly include a .env value containing a base64‑encoded endpoint (for example, AUTH_API=<base64>) and a server route that decodes the endpoint, posts process.env to the remote endpoint, and executes returned JavaScript via dynamic compilation (new Function(...)(require)), enabling in‑memory remote code execution.
- This path exfiltrates environment variables (cloud keys, DB credentials, API tokens) and hands attackers an interactive foothold inside the server process. (microsoft.com)
The staged C2 design: registration, controller, and in‑memory tasking
Microsoft’s telemetry shows a clear two‑stage architecture:- Stage 1 — Lightweight registrar / bootstrap: retrieved at runtime and executed by Node.js, the Stage 1 script profiles the host, polls a registration endpoint at a fixed cadence, and can execute bootstrap JavaScript returned by the server. The registrar establishes a durable instanceId used in later polling. (microsoft.com)
- Stage 2 — Persistent controller and tasking loop: Stage 1 hands off to a separate Stage 2 controller that communicates with a different C2 API/IP set. Stage 2 runs as a long‑lived control loop, polling for messages[] arrays of JavaScript tasks, rotating identifiers, honoring kill switches, and piping server‑supplied JavaScript into Node via STDIN to execute tasks in memory. The controller also implements error reporting, retry logic, and process tracking. Observed workflows include directory browsing endpoints and a staged upload protocol (upload → uploadsecond → uploadend) to transfer selected files. (microsoft.com)
Indicators and artifacts observed
Microsoft published a consolidated list of observed infrastructure and repository artifacts that defenders should treat as high‑priority telemetry:- Vercel‑hosted staging domains used for loader delivery and staging (examples observed in telemetry include price‑oracle‑v2.vercel.app and other vercel.app endpoints).
- C2 servers on specific IPv4 addresses and HTTP endpoints used for registration, tasking, discovery, and uploads (observed use of ports such as 3000, and endpoints like /api/handleErrors, /api/reportErrors, /hsocketNext, /upload, etc.).
- Repository artifacts and filenames used as execution triggers: next.config.js, .vscode/tasks.json, scripts/jquery.min.js, server/routes/api/auth.js, server/controllers/collection.js, .env.
- SHA‑256 / SHA‑1 file hashes cataloged during analysis. (microsoft.com)
Why developer workflows are an attractive attack surface
- High‑value data on developer machines. Source code, environment files (.env), cloud keys, and local credential caches are common on developer endpoints. A single compromise can provide the keys to build and deploy systems or direct access to cloud resources.
- Trusted automation and convenience. Editors like Visual Studio Code encourage automation to improve developer productivity. Actions that run on folder open, recommended extensions, and task automation are convenience features that, when abused, yield immediate execution.
- Less rigorous scrutiny. Developers routinely clone repositories, install dependencies, and run dev servers on machines not hardened to the same degree as production servers. This inconsistency creates an exploitable gap.
- In‑memory execution and living‑off‑the‑land tactics. Using Node and standard developer tooling reduces forensic artifacts and bypasses controls that look for signed binaries or disk‑based malware.
Critical analysis: strengths, weaknesses, and gaps in Microsoft’s findings
Strengths of Microsoft’s analysis
- Telemetry‑driven scope expansion. Microsoft correlates process and network telemetry with repository artifacts and naming patterns, enabling the discovery of related repositories not directly observed in initial logs. This pivot methodology is practical and repeatable for defenders hunting similar activity. (microsoft.com)
- Clear mapping of execution paths. The three‑path breakdown (VS Code, dev server, backend) provides actionable detection points that align with developer behavior and can be mapped to EDR, network, and code scanning telemetry. (microsoft.com)
- Operational-level IOCs and hunting queries. Microsoft supplies concrete DeviceNetworkEvents and DeviceProcessEvents queries, C2 endpoints, and filenames to accelerate enterprise hunting. These are valuable starting points to triage and contain incidents at scale. (microsoft.com)
Risks and limitations
- Reliance on platform reputation for rapid blocking is fragile. Because attackers use mainstream PaaS (Vercel) and legitimate project scaffolding, defenders relying solely on domain/IP reputation or static allowlists risk either missing the attack (if allowlisted) or producing excessive false positives (if blocked). The attackers intentionally blend into developer workflows and hosting ecosystems. (microsoft.com)
- Behavioral blind spots in developer environments. Developer machines are frequently exempted from stringent controls (for performance or tooling compatibility), which reduces visibility and increases dwell time when compromises occur. Microsoft’s recommendations target this, but operational adoption can be slow.
- Supply‑chain and social engineering overlap. This campaign sits in a gray area between malicious repositories and trojanized packages or cloned starter projects. Detecting intent inside a repository without running it is nontrivial and may require more aggressive code provenance and SBOM practices. Prior incidents in the JavaScript ecosystem (for example, supply‑chain compromises like Shai‑Hulud) show how easily developer workflows can be weaponized at scale.
- Potential for false negatives in detection rules. Attackers used base64 encoding, obfuscation, and dynamic compilation patterns (new Function, piping into node -) to evade static detection. Unless telemetry tracks suspicious Node child processes, unusual command lines, and repeated short‑interval C2 polling, Stage 1 beaconing can be missed. Microsoft’s hunting queries help but require mature telemetry ingestion to be effective. (microsoft.com)
Practical detection and response playbook
The following prioritized steps reflect Microsoft’s guidance and best practices for responding to an active or suspected compromise of this type:- Contain and scope immediately:
- Identify initiating process trees for Node.js/Code.exe that show short‑interval polling to unknown endpoints.
- Isolate affected developer endpoints from sensitive networks and credential caches.
- Hunt across the fleet using behavioral signals:
- Search DeviceNetworkEvents for Node processes contacting vercel.app domains or the listed endpoints (/api/handleErrors, /hsocketNext, /upload, etc.).
- Search DeviceProcessEvents for Node invocations that include eval/new Function/readFile patterns or detached child Node interpreters that read from STDIN. (microsoft.com)
- Perform identity triage and session remediation:
- Because env exfiltration is observed, treat all tokens and browser sessions used on impacted endpoints as potentially compromised.
- Rotate cloud credentials, revoke refresh tokens, and force re‑authentication for service principals and CI identities where feasible. Use Entra risk detection and session controls to prioritize actions. (microsoft.com)
- Apply immediate prevention controls:
- Enforce Visual Studio Code Workspace Trust defaults and review .vscode/tasks.json and workspace automation before granting trust.
- Apply attack surface reduction rules to block execution of obfuscated scripts and unknown Node child interpreters on Windows endpoints.
- Keep cloud‑delivered antivirus and SmartScreen enabled to reduce exposure from malicious download paths. (microsoft.com)
- Harden long‑term developer posture:
- Minimize secrets on developer workstations; prefer short‑lived tokens and local secret managers that do not store plain text .env entries.
- Segment build and deployment infrastructure from developer workstations.
- Integrate repository scanning and SBOM checks into CI to detect suspicious file placement, obfuscated assets, or encoded endpoints. Microsoft and other vendors provide agentless scanning tools to identify risky packages pre‑execution.
Recommendations for defenders and platform owners
- Enforce Workspace Trust by default in enterprise VS Code deployments and require a security review for cloned external repositories used for assessments or interviews.
- Extend EDR coverage to flag Node.js processes exhibiting:
- Repeated network polling to unfamiliar domains within short intervals.
- Execution of dynamic code constructs (new Function, eval) sourced from network responses.
- Detached Node interpreters consuming STDIN (node -) spawned from other Node processes.
- Work with PaaS providers and trust platform abuse reports. Attackers leveraging mainstream hosting (Vercel) need to be tracked and takedown requests coordinated to reduce active staging infrastructure.
- Incorporate repository provenance checks (commit signatures, author verification) for any externally sourced assessment projects and implement CI pre‑merge scanning to detect trojanized assets. The Shai‑Hulud supply‑chain incident demonstrates the value of these steps.
Hunting queries and operational artifacts to prioritize
Microsoft provides Sentinel / Defender hunting queries that map directly to the attack behavior—use them as templates to tune to your environment:- Node.js fetching remote JavaScript from untrusted domains (vercel.app, oracle‑v1‑beta, etc.). (microsoft.com)
- Detection of next.config.js dynamic loader behavior (readFile → eval) during next dev/next build. (microsoft.com)
- Repeated short‑interval beaconing to C2 endpoints (/api/errorMessage, /api/handleErrors). (microsoft.com)
- Detection of detached child Node interpreters invoked with a trailing "-" (node -). (microsoft.com)
- Network patterns using the staged upload workflow endpoints: /upload, /uploadsecond, /uploadend. (microsoft.com)
Final assessment: what this campaign means for enterprise security
This campaign is a timely reminder that developer machines are not just endpoints—they are high‑value gateways. Attackers increasingly weaponize convenience, reuse legitimate platforms for staging, and prefer in‑memory techniques to reduce forensic footprints. Microsoft’s detailed telemetry and hunting guidance give defenders concrete detection vectors, but effective defense requires organizational changes:- Treat developer workstations as a critical attack surface with strict controls, monitoring, and credential hygiene.
- Reduce the human trust surface when onboarding external code—never allow automated execution features (workspace tasks, install scripts) without review.
- Invest in cross‑telemetry detection: correlate EDR, process telemetry, network flows, and identity events to shorten detection time and limit blast radius.
By mapping developer workflows to concrete detection signals, applying strict workspace trust and attack surface reduction, and operationalizing identity and session remediation, organizations can reduce the likelihood that a single recruiting‑style repo will become the entry point to a broader compromise. The Microsoft findings are a clear call to action: prioritize developer‑centric visibility and treat the developer workstation as a first‑class element of enterprise security. (microsoft.com)
Source: Microsoft Developer-targeting campaign using malicious Next.js repositories | Microsoft Security Blog