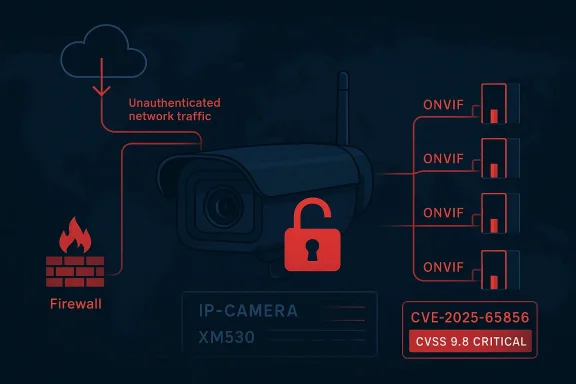
The latest CISA advisory on the Hangzhou Xiongmai Technology Co., Ltd XM530 IP Camera is not a routine firmware notice; it is a critical authentication-bypass disclosure that can let unauthenticated attackers reach sensitive device information and live video streams. CISA says the affected firmware is V5.00.R02.000807D8.10010.346624.S.ONVIF_21.06, ties the issue to CVE-2025-65856, and rates it 9.8 Critical under CVSS 3.1. The advisory also notes that Xiongmai has not responded to CISA’s attempts to coordinate mitigation, which leaves defenders with the familiar but uncomfortable combination of a high-severity bug and little vendor guidance. XM530 disclosure fits a pattern that security teams have seen repeatedly in network cameras and other edge devices: the attack surface is often far larger than buyers assume, and the security model is only as strong as the weakest exposed endpoint. In this case, the problem is not merely a buggy web page or a single misconfigured service. CISA says the ONVIF implementation fails to enforce authentication on 31 critical endpoints, which means the device’s control plane and data plane may both be exposed to remote abuse.
That detail mattersno longer simple point devices. They are now part of the broader enterprise perimeter, often tied into physical security, facility monitoring, remote support workflows, and cloud or VMS integrations. When a camera can be queried without authentication, the issue is not just privacy leakage. It can become a foothold into operational intelligence, network reconnaissance, and potentially broader surveillance of a facility’s layout and activity patterns.
CISA places the affected device in the *s sector and says it is deployed worldwide, which is exactly the kind of footprint that turns a niche product issue into a systemic exposure. The company headquarters location is listed as China**, but the risk is global because the vulnerable product is not constrained to one region or one market segment. That combination—broad deployment, high privilege, and unauthenticated access—has been the recurring recipe behind many camera-related incidents over the past several years.
There is also a broader industry lesson here. Camera vendors nteroperability to make products easier to integrate, but interoperability can become a liability if security checks are applied unevenly across endpoints. A device can look compliant at the feature level while quietly missing authentication on the very interfaces that matter most. That is why advisories like this one should be read as architecture warnings, not just product notices.
CISA’s summary is unusually direct: successful exploitatiacker to bypass authentication and access sensitive information on the device. In the detailed vulnerability text, CISA says unauthenticated remote attackers can access sensitive device information and live video streams because the ONVIF implementation does not enforce authentication on critical endpoints. That is classic CWE-306 Missing Authentication for Critical Function territory, and it maps cleanly to the type of risk that defenders should treat as immediate.
The practical consequence is that defenders should not assume there is one easy blocklist rule or one small patch point. If ndled inconsistently, then the exposed surface may include status queries, device metadata, streaming functions, and possibly administrative operations. Even if the advisory highlights live video and sensitive information, the broader lesson is that unauthenticated control surfaces often create a path to more than one kind of abuse.
That makes the issue especially uncomfortable for organizations that think of cameras as passive devices. In reality, cameras often sit on trusted subnets, have predior, and are monitored less rigorously than servers or endpoints. Those are exactly the conditions under which a 9.8-rated flaw can remain exposed long enough to matter.
The bigger risk is that a camera is often trusted by design. Security teams may allow it through firewalls, exempt it from strict endpoint controls, or leave it reachable from internal management segments because “it’s only videoaccepts unauthenticated requests is no longer a passive sensor. It becomes an intelligence source for an adversary, and in some environments it can become a pivot point for lateral movement.
That is why ONVIF-related advisories often carry outsized weight. A camera vendor may think in terms of a single firmware build, but defenders have to think in terms of exposed services, trust zones, and operational exposure. A flaw in an ONVIF endpoint is often a flaw imption that its video network is somehow less interesting than the rest of its environment.
This is where defense-in-depth stops being a slogan and becomes an architectural requirement. Even if the camera itself is vulnerable, segmentation, firewalling, and remote-access restrictions can reduce the chance that a remote attacker finds it in the first place. That is consistent with CISA’s advice to minimize exposure, isossets, and use more secure remote access methods when necessary.
The hard part is that camera fleets are rarely managed with the same discipline as laptops or servers. They may be installed by different vendors, integrated over time, and left running through multiple refresh cycles. That means a product like the XM530 can be present in more places than the central IT team realizes, especially if it sits behind a third-party monitoring pll integrator.
That is why even small deployments should treat the adviera is not just a camera once it sits on a network and becomes reachable over standard management and streaming interfaces. It becomes a data source, and in some cases a surveillance risk for the very people who installed it to increase security.
It also changes the risk calculus for procurement and lifecycle management. Organizations increasingly need to ask not only whether a crates well, but whether the vendor has a credible security-response process. A device family with a critical authentication-bypass issue and limited public coordination will inevitably look less attractive than one with clear fix commitments.
That means the core question is not “Will Xiongmai issue a better statement?” but “Can we reduce reachability today?” For many organizations, the answer should start with segmentation, then proceed n to any firmware or lifecycle decisions that can be validated in their environment.
Organizations should also remember that VPNs are only as safe as the devices behind them. CISA’s wording is careful here: VPNs can be useful, but they are not magic. If a user or vendor can reach a vulnerable camera through a secure tunnel, the t the attacker to the flaw more reliably.
hould monitor next
The XM530 advisory is a reminder that the most dangerous device on a network is often the one everyone assumester. Once authentication disappears from critical functions, the camera is no longer just a sensor; it is an exposed information system with a front row seat to the facility. The right response is not panic, but urgency: find every affected unit, close the easiest paths in, and treat video infrastructure as a serious part of the security perimeter before someon
Source: CISA Hangzhou Xiongmai Technology Co., Ltd XM530 IP Camera | CISA
That detail mattersno longer simple point devices. They are now part of the broader enterprise perimeter, often tied into physical security, facility monitoring, remote support workflows, and cloud or VMS integrations. When a camera can be queried without authentication, the issue is not just privacy leakage. It can become a foothold into operational intelligence, network reconnaissance, and potentially broader surveillance of a facility’s layout and activity patterns.
CISA places the affected device in the *s sector and says it is deployed worldwide, which is exactly the kind of footprint that turns a niche product issue into a systemic exposure. The company headquarters location is listed as China**, but the risk is global because the vulnerable product is not constrained to one region or one market segment. That combination—broad deployment, high privilege, and unauthenticated access—has been the recurring recipe behind many camera-related incidents over the past several years.
There is also a broader industry lesson here. Camera vendors nteroperability to make products easier to integrate, but interoperability can become a liability if security checks are applied unevenly across endpoints. A device can look compliant at the feature level while quietly missing authentication on the very interfaces that matter most. That is why advisories like this one should be read as architecture warnings, not just product notices.
 What CISA Found
What CISA Found
CISA’s summary is unusually direct: successful exploitatiacker to bypass authentication and access sensitive information on the device. In the detailed vulnerability text, CISA says unauthenticated remote attackers can access sensitive device information and live video streams because the ONVIF implementation does not enforce authentication on critical endpoints. That is classic CWE-306 Missing Authentication for Critical Function territory, and it maps cleanly to the type of risk that defenders should treat as immediate.Why the 31 endpoints matter
The number of affected endpoints is the most telling part of the advisked URI might be dismissed as a coding mistake; dozens of unauthenticated routes suggest a systemic access-control failure. That usually means the product’s security assumptions were weak at design time, or that authentication enforcement was bolted on in a way that left too many exceptions.The practical consequence is that defenders should not assume there is one easy blocklist rule or one small patch point. If ndled inconsistently, then the exposed surface may include status queries, device metadata, streaming functions, and possibly administrative operations. Even if the advisory highlights live video and sensitive information, the broader lesson is that unauthenticated control surfaces often create a path to more than one kind of abuse.
Why CVSS 9.8 is appropriate
A 9.8 score is not reserved for cosmetic flaws. It reflects a remotely exploitable weakness with no privileginteraction, and potentially complete compromise of confidentiality, integrity, and availability. CISA’s vector string—AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H—is the standard shorthand for a problem that can be reached over the network and can have severe consequences if exploited.That makes the issue especially uncomfortable for organizations that think of cameras as passive devices. In reality, cameras often sit on trusted subnets, have predior, and are monitored less rigorously than servers or endpoints. Those are exactly the conditions under which a 9.8-rated flaw can remain exposed long enough to matter.
Why This Camera Family Is a Bigger Deal Than It Looks
The XM530 line sits in a part of the market where affordability, mass deployment, and feature breadth tend to outrun securit not unique to Xiongmai, but it is a familiar pattern across low-cost IP cameras: broad compatibility is prioritized, and authentication consistency becomes a secondary concern. In a product that exposes ONVIF functionality, that tradeoff can become visible to any attacker who knows how to enumerate the right endpoints.Authentication failures are not “just” privacy bugs
It is tempting to frame camera exposure as a confidentiality issue only. That is too narrow. A camera that leaks live streams can reveal schedules, guae entrances, manufacturing activity, or customer behavior. In a commercial facility, that information can help an attacker plan physical intrusion, social engineering, or follow-on cyber activity.The bigger risk is that a camera is often trusted by design. Security teams may allow it through firewalls, exempt it from strict endpoint controls, or leave it reachable from internal management segments because “it’s only videoaccepts unauthenticated requests is no longer a passive sensor. It becomes an intelligence source for an adversary, and in some environments it can become a pivot point for lateral movement.
ONVIF is convenient, but convenience cuts both ways
ONVIF is useful because it standardizes how cameras and video systems discover, configure, and stream media. The problem is that standardization can make exploitation scalable. If the same inteoyed across many devices, a weakness in one vendor’s implementation can become a repeatable technique across an entire product class.That is why ONVIF-related advisories often carry outsized weight. A camera vendor may think in terms of a single firmware build, but defenders have to think in terms of exposed services, trust zones, and operational exposure. A flaw in an ONVIF endpoint is often a flaw imption that its video network is somehow less interesting than the rest of its environment.
Operational Impact for Enterprises
For enterprises, this advisory should be read as both a cyber risk and a physical-security risk. The most obvious impact is unauthorized access to live video streams and device metadata, but the indirect impacts may be more consequential. Once an anal camera feeds, they gain a real-time map of building activity, access routines, and blind spots.Security teams should think in layers
The first layer is exposure: is the camera reachable from the internet, from guest networks, from poorly segmented internal zones, or from third-party monitoring systems? The second layer is trust: do building management systems, VMS platforms, or integrators assume theted when it may not be? The third layer is blast radius: what else can be reached from the same network path if the camera is compromised or abused?This is where defense-in-depth stops being a slogan and becomes an architectural requirement. Even if the camera itself is vulnerable, segmentation, firewalling, and remote-access restrictions can reduce the chance that a remote attacker finds it in the first place. That is consistent with CISA’s advice to minimize exposure, isossets, and use more secure remote access methods when necessary.
Operational teams will feel the pain first
Facilities and security operations teams may not have the luxury of delaying action until a convenient maintenance window. Cameras are often embedded in workflows that support incident response, safety monitoring, and compliance. If one of those devices is exposed, the organization may need to balance remety, and that makes inventory accuracy critical.The hard part is that camera fleets are rarely managed with the same discipline as laptops or servers. They may be installed by different vendors, integrated over time, and left running through multiple refresh cycles. That means a product like the XM530 can be present in more places than the central IT team realizes, especially if it sits behind a third-party monitoring pll integrator.
Consumer and Small-Business Exposure
For consumers and small businesses, the issue may appear less dramatic, but that is mostly because the environment is simpler—not because the exposure is smaller. A vulnerable camera on a home or small-office network can still leak video, reveal routines, and expose sensitive premises. If the device is reachable through port forwarding, remote adminnfigured router, the attack surface becomes much larger than the owner expects.Why small environments are often easier to abuse
Small environments usually have weaker segmentation, fewer monitoring tools, and less disciplined change control. That means a camera left on the default network can quietly stay exposed for years. If the device is one of several connected gadgets sharing the same subnet, an attacker may not even need to target it directly; they may simply scan and collect what is also a practical trust issue. Home users and small businesses often assume cameras are “plug-and-play” products with security handled by the vendor. That assumption fails hard when the advisory says unauthenticated attackers can reach sensitive data through critical endpoints. In other words, the device may be functioning exactly as designed while still being insecure by default.The likely real-world consequence
For cogn of trouble may never be a dramatic compromise. It may be subtle exposure: streams viewed by someone who should not be watching, configuration metadata accessed from outside the local network, or the device showing up in reconnaissance scans. Those quieter failures are important because they are often the precursor to larger abuse.That is why even small deployments should treat the adviera is not just a camera once it sits on a network and becomes reachable over standard management and streaming interfaces. It becomes a data source, and in some cases a surveillance risk for the very people who installed it to increase security.
What the Vendor Situation Means
CISA states that Hangzhou Xiongmai Technology Co., Ltd. has not responded to requests to work with CISA on mitigatove the vendor has no internal response plan, but it does mean defenders cannot rely on a coordinated public fix timeline from the advisory itself. In practical terms, that shifts the burden back to customers.Why vendor silence matters
When a product vendor is engaged and responsive, organizations can often plan aroudation, and rollout guidance. When the vendor is not actively coordinating, the security team has to assume less certainty and more manual effort. That raises the importance of local controls, especially where patching options are unclear or delayed.It also changes the risk calculus for procurement and lifecycle management. Organizations increasingly need to ask not only whether a crates well, but whether the vendor has a credible security-response process. A device family with a critical authentication-bypass issue and limited public coordination will inevitably look less attractive than one with clear fix commitments.
What customers should infer carefully
It would be a mistake to assume that no public mitigation means no mitigation exists at all. But it wait passively for a vendor notice when the advisory already says the device is known affected. The safest inference is that customers should act as if exposure reduction is now their primary defense.That means the core question is not “Will Xiongmai issue a better statement?” but “Can we reduce reachability today?” For many organizations, the answer should start with segmentation, then proceed n to any firmware or lifecycle decisions that can be validated in their environment.
Defensive Priorities
CISA’s guidance is straightforward and remains the right starting point: minimize network exposure, isolate control-system devices and remote devices behind firewalls, and use VPNs or similarly secure remote methods when necessary. Those recommendatibut that is because the simplest attack path is often the one that gets exploited first.Immediate actions defenders should take
- Identify every XM530 instance, including devices deployed by integrators or subcontractors.
- Confirm whether any camera is reachable from the internet or from broad Restrict ONVIF and video access to approved management or monitoring segments only.
- Review firewall rules, port forwards, and vendor remote-support paths.
- Monitor for suspicious requests, unexpected viewing activity, or anomalous endpoint access.
Why segmentation still wins
Segmentation is not a cure-all, but it is the most reliable compensating control when the product itself is weak. Cameras should not sit on the same network as user workstations, and they certainly should not be exposed to the internet just to make remote viewConvenience is not the same thing as access control, and this advisory is a reminder of that distinction.Organizations should also remember that VPNs are only as safe as the devices behind them. CISA’s wording is careful here: VPNs can be useful, but they are not magic. If a user or vendor can reach a vulnerable camera through a secure tunnel, the t the attacker to the flaw more reliably.
Strengths and Opportunities
The strongest positive in this disclosure is that the affected version is clearly identified, the vulnerability type is precise, and the mitigation path starts with familiar controls. That makes the issue actionable even before a vendor patch becomes part of the conversation. It also creates a useful forcing function for organizations that hamera inventory, segmentation, or remote-access cleanup.- The affected firmware version is explicitly named.
- The vulnerability class is easy to understand and prioritize.
- The advisory provides immediate exposure-reduction guidance.
- Security teams can use it to verify camera inventory accuracy.
- Netwovements will help beyond this single device.
- Remote-access review may uncover other legacy exposures.
- The event can strengthen procurement scrutiny for future camera buys.
Risks and Concerns
The main risk is underestimation. Because the product is a camera, some administrators may mentally downgrade the issue from “critical infrastructure risk” to “another IoT patch.” That would be a mistake. An unauthenticated route into a live video device can expose sensitive facilities data, support reconnaissance, and undermine physical securityt are hard to unwind later.- Cameras are often over-trusted on internal networks.
- ONVIF exposure can be broader than teams realize.
- Live video leaks can aid both cyber and physical intrusion.
- Inventory gaps make remediation slower than exploitation.
- Third-party access paths may remain open longer than intended.
- Small deployments may lack any meaningful monitoringse increases uncertainty and delays.
Looking Ahead
The next thing to watch is whether Xiongmai publishes a public remediation path, whether customers receive clear firmware guidance, and whether more product lines under the same platform inherit the same authentication weakness. That matters because camera vulnerabilities often begin with one advisory and then expand as researchers test adjacent models or related firmware branches.hould monitor next
- Vendor firmware or configuration guidance for XM530 variants.
- Any indication of public proof-of-concept activity.
- Signs that the same ONVIF weakness affects adjacent devices.
- Third-party VMS or integrator guidance on blocking exposure.
- Internal audit results showing whether any cameras remain internet-facing.
The XM530 advisory is a reminder that the most dangerous device on a network is often the one everyone assumester. Once authentication disappears from critical functions, the camera is no longer just a sensor; it is an exposed information system with a front row seat to the facility. The right response is not panic, but urgency: find every affected unit, close the easiest paths in, and treat video infrastructure as a serious part of the security perimeter before someon
Source: CISA Hangzhou Xiongmai Technology Co., Ltd XM530 IP Camera | CISA