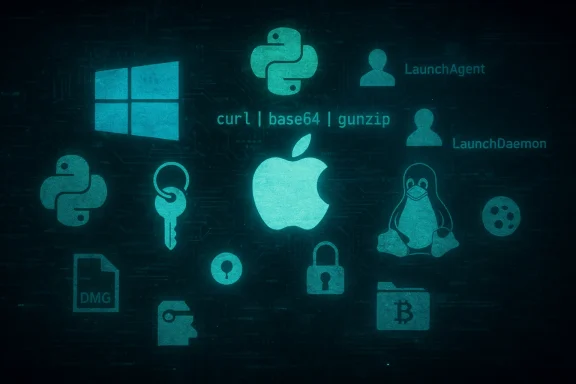
Infostealers have quietly slipped the Windows-only frame that long defined them, evolving into a cross-platform menace that targets macOS, Linux, and Windows environments alike — and increasingly leverages high-level languages, trusted platforms, and native utilities to steal credentials and secrets at scale.
The infostealer economy — malware whose primary objective is to harvest credentials, cookies, session tokens, crypto wallets, and developer secrets — has matured into a diversified toolkit for financially motivated actors and opportunistic cybercriminals. Over the last year the tradecraft has shifted in three important ways: a visible pivot to macOS-focused campaigns, widespread use of Python-based stealers to simplify cross-platform attacks, and platform abuse where attackers weaponize trusted services (messengers, document tools, install utilities) to reach victims and evade detection.
These changes matter because they remove many of the historical friction points for attackers. Where Windows-centric defenses and signature detection once slowed mass credential theft, attackers now combine social engineering, fileless techniques, living-off-the-land execution, and legitimate cloud services to blend in with normal traffic. For defenders, the result is higher noise, lower signal, and greater risk of account takeover, supply-chain compromise, and immediate financial theft through crypto wallet extraction.
The practical takeaway is simple but urgent: treat macOS and Python workloads as first‑class attack surfaces, assume that trusted platforms can be abused, and prioritize controls that remove credential exposure (MFA, secret rotation, key protection) and that detect the minimal but telling artifacts of modern stealers (suspicious interpreter renames, living‑off‑the‑land command chains, transient archives followed by egress). The cost of inaction is immediate and concrete: account takeover, drained wallets, and the loss of developer and customer trust can happen in minutes once an infostealer slips past the front door.
Source: Microsoft Infostealers without borders: macOS, Python stealers, and platform abuse | Microsoft Security Blog
 Background
Background
The infostealer economy — malware whose primary objective is to harvest credentials, cookies, session tokens, crypto wallets, and developer secrets — has matured into a diversified toolkit for financially motivated actors and opportunistic cybercriminals. Over the last year the tradecraft has shifted in three important ways: a visible pivot to macOS-focused campaigns, widespread use of Python-based stealers to simplify cross-platform attacks, and platform abuse where attackers weaponize trusted services (messengers, document tools, install utilities) to reach victims and evade detection.These changes matter because they remove many of the historical friction points for attackers. Where Windows-centric defenses and signature detection once slowed mass credential theft, attackers now combine social engineering, fileless techniques, living-off-the-land execution, and legitimate cloud services to blend in with normal traffic. For defenders, the result is higher noise, lower signal, and greater risk of account takeover, supply-chain compromise, and immediate financial theft through crypto wallet extraction.
macOS in the crosshairs: why Macs no longer enjoy obscurity
The new macOS playbook
macOS-targeted stealers no longer arrive as exotic, bespoke binaries. Instead, the playbook blends social engineering with native macOS behaviors:- Malicious or impersonating DMG installers that mimic legitimate apps and ship unsigned App bundles.
- “ClickFix”-style web pages that coax users into copying terminal commands (curl | base64 -d | gunzip workflows) or into accepting fake installers.
- Fileless execution using AppleScript / osascript, JavaScript for Automation (JXA), and native utilities to enumerate Keychain, browser stores, and developer artifacts.
- Use of legitimate cloud hosting (static page hosts, cloud storage) to stage payloads and clean up traces after exfiltration.
Notable macOS campaigns and techniques
Recent campaigns have been observed using a small set of delivery lures and techniques that repeat across multiple families:- Disk image (DMG) installers branded as AI tools, productivity apps, or updaters that drop a macOS stealer into /Applications or run postinstall scripts that add LaunchAgents / LaunchDaemons.
- Copy‑paste Terminal instructions: web pages auto‑populate the clipboard with a one‑liner that mounts a remote DMG or pipes a remote payload into a shell command. Those commands frequently chain curl with base64 decoding and decompression to minimize disk footprint.
- AppleScript and JXA for credential harvesting and process automation — attackers script the UI to read browser password stores or to access items in the Keychain when permissions are granted.
Python-based stealers: rapid development, easy cross-platform reach
Why Python is attractive to attackers
Python lowers the bar for building and porting infostealers. Benefits for attackers include:- Cross-platform runtime compatibility (Windows, macOS, Linux).
- Rich ecosystem of libraries for browser automation, HTTP clients, and parsing utilities.
- Simple obfuscation and packing techniques (pyinstaller, UPX, or packaging into signed wrappers).
- Ease of integrating into commodity tooling (Telegram, cloud storage, steganography channels).
Case study: PXA Stealer and its ecosystem
A multi-stage, Python-centric family observed in recent months demonstrates these trends. Typical elements include:- Initial access via phishing archives or malicious PDF attachments.
- A downloader that extracts or invokes a Python payload (sometimes disguised as signed binaries, or packed with legitimate apps to sideload malicious DLLs).
- Persistence via Registry Run keys or scheduled tasks on Windows; or cron/LaunchAgent style persistence on macOS/Linux.
- Data collection from browsers, file stores, and wallet extensions.
- Exfiltration to command-and-control channels that leverage legitimate services (e.g., Telegram) to avoid easy network blocking and to benefit from resilient hosting and encryption.
Platform abuse: weaponizing popular apps and utilities
Attackers increasingly exploit trusted platforms for both delivery and propagation. Two examples have emerged as particularly concerning.WhatsApp as a propagation vector (Eternidade Stealer)
WhatsApp — because of its global reach and user trust — is now being automated to deliver malware at scale. The observed pattern:- An initial VBScript or small stub drops a Python-based automation component that leverages WhatsApp Web automation libraries (for example, WPPConnect or similar APIs).
- The Python worm logs into WhatsApp Web from the host (or hijacks an active session), harvests the contact list, and sends personalized messages with malicious attachments or links to all contacts.
- A secondary payload installer (MSI or EXE) then delivers a credential stealer (examples include Delphi-based stealers such as Eternidade), which monitors for banking or crypto wallet windows and exfiltrates the captured credentials.
- The worm-like behavior amplifies infections through trust relationships (contacts are far more likely to click a received file) and spreads rapidly inside social graphs.
Malicious installer masquerades (Crystal PDF and similar lures)
Malvertising, SEO poisoning, and social engineering continue to lure victims to fake installers. Tactics include:- Deceptive installers masquerading as PDF editors, utilities, or AI tools — often pushed via sponsored ads or poisoned search results.
- Bundled payloads that establish persistence via scheduled tasks or LaunchAgent entries.
- Covert browser hijacking to read AppData/Roaming storage for cookies, session data, and credential caches.
Detection, prevention, and response — prioritized guidance
Modern infostealers succeed by mixing technical stealth with human deception. Defenders should build layered controls that address both.High-priority mitigations (immediate)
- Enable cloud‑delivered protections and real‑time telemetry in your endpoint protection product. Cloud ML and behavior analytics catch many evasive, previously unseen samples.
- Run EDR in block mode so suspected malicious artifacts are stopped and remediated automatically.
- Turn on tamper protection and restrict local admin rights to prevent attackers from disabling defenses or creating AV exclusions.
- Enforce multi‑factor authentication (MFA) on all accounts; require hardware or phishing‑resistant second factors for privileged accounts and developer tokens.
- Block or inspect outbound traffic to new/suspicious domains and flag POST requests to newly registered hosts used for credential exfiltration.
macOS‑specific hardening
- Educate users against copy‑paste Terminal workflows and against running unsigned DMG installers from search results or ads.
- Monitor and alert on suspicious Terminal invocations, particularly command chains that include curl | base64 -d | gunzip, osascript usage, or calls to mount_hfs/attach/diskutil with unusual flags.
- Restrict and log access to Keychain items; treat elevated keychain access prompts as high‑risk events in managed fleets.
- Use device management tooling (Jamf, Munki, or MDM) to enforce allow‑listing of installers and to manage accessibility/screen recording permissions.
Windows and cross‑platform mitigations
- Harden against LOLBIN abuse (mshta, certutil, rundll32) by applocker or script block policies; log elevated script downloads.
- Detect renamed interpreters and suspicious parent-child process relationships (svchost.exe executing a Python runtime, for example).
- Block or monitor service endpoints used for exfiltration (Telegram Bot endpoints, cloud pages hosting payloads).
- Detect transient staging behavior: ZIP/archives created in /tmp, %TEMP%, or ephemeral directories followed by outbound transfers.
Hunting and triage playbook (quick steps)
- Isolate suspected hosts from the network to prevent lateral spread and worm propagation.
- Capture volatile memory and process lists; look for interpreters named to masquerade as system processes.
- Audit scheduled tasks, Run keys, LaunchAgent/LaunchDaemon entries, and recent disk image mounts.
- Search for recent use of living-off-the-land binaries (mshta, certutil, osascript) and for suspicious command chains in process history.
- Rotate any secrets that could have been exposed: passwords, API keys, developer tokens, and repo deploy keys — but only after collecting forensics from a known‑clean device.
- Hunt for exfiltration indicators: POST/PUT requests to new domains, creation of ZIPs in ephemeral folders, or outbound connections to Telegram / cloud hosting domains.
Rapid containment for platform‑abuse chains (WhatsApp / installers)
- If a host is suspected of running a WhatsApp automation worm, temporarily disable WhatsApp Web sessions by forcing logout from known sessions and prompting users to re-authenticate using secondary devices not connected to the compromised host.
- Revoke and rotate any stored tokens (browser cookies, single‑device session tokens) immediately if browser credential extraction is suspected.
- Block the installer file hashes and the hosting domains at the network perimeter and inform users about the specific lure (Crystal PDF, Fake AI installer, etc.) to prevent re‑infection.
Incident response: secret rotation and recovery priorities
When an infostealer incident is confirmed, act with the following priority order:- Contain: isolate infected endpoints, take network segments offline if necessary to prevent worm propagation.
- Preserve evidence: collect memory images, process trees, and disk snapshots before remediation steps that could destroy artifacts.
- Credential triage and rotation:
- Reset passwords and rotate keys for accounts accessed from compromised endpoints (user accounts, cloud console credentials, SSH keys).
- Revoke refresh tokens and re‑issue OAuth client secrets where applicable.
- Force logout for web sessions and require fresh MFA challenges.
- Rebuild where persistence cannot be trusted: for devices with complex persistence (DLL sideloading, inflated loader chains, or Kerberos ticket theft), reimaging is often the only way to guarantee full remediation.
- Post‑mortem: review how the initial access happened (malvertising click, phishing email, SEO poisoning) and update user training, ad-blocking or filtering rules, and endpoint allow-lists to reduce future risk.
Critical analysis: where defenders must raise the bar
Microsoft and other vendors have produced practical detections and hunting queries mapped to modern telemetries. That coverage is a strong baseline, but defenders should be aware of the limits and residual risks.- Detection vs. prevention: Many of the new stealth techniques (fileless pipelines, living‑off‑the‑land execution, and automation of legitimate platforms) are designed to bypass signature-based prevention. Relying solely on AV signatures will not suffice.
- Supply chain and hosting abuse: Attackers increasingly ride on legitimate cloud hosting (static pages, GitHub pages, CDN edges) for payload staging and GitHub or email for dead‑drop C2 resolution. Network allowlists alone are insufficient; content‑ and behavior‑based inspection is required.
- Mac blind spots: Historically, enterprise tooling and operational playbooks focused on Windows. The rising macOS threat requires parity in telemetry collection, managed device controls, and user education.
- Human factors remain the weak link: ClickFix-style instructions and personalized messaging (especially on social platforms like WhatsApp) exploit trust and muscle memory. Technology can reduce risk, but targeted user education and friction in high‑risk flows (e.g., blocking terminal copy‑paste from browsers) are important defenses.
- Developer secrets: Stealers that target dev environments and build artifacts pose a large supply‑chain risk. A stolen deploy key or CI secret can escalate a single endpoint compromise into source‑code or infrastructure compromise.
- Some campaign‑specific technical details and attribution chains reported in public coverage are evolving. When seeing claims about specific C2 domains, hashes, or actor languages, treat them as operational intelligence subject to change and verify with your threat‑intelligence feeds and telemetry before actioning blocklists. Never assume a single external report is definitive; cross‑check with multiple reputable sources and internal telemetry.
Practical checklist for IT teams (prioritized)
- Turn on cloud‑delivered protection in endpoint protection and make sure EDR is in block mode.
- Enforce MFA everywhere; require phishing‑resistant second factors for privileged and developer accounts.
- Harden macOS fleet: restrict unsigned DMG installs, monitor osascript and terminal operations, and enforce MDM policies.
- Apply least privilege: remove local admin rights from standard users and enable tamper protection on endpoint agents.
- Monitor outbound egress: flag POSTs to newly created domains and inspect archives created in /tmp or %TEMP% that are immediately transferred out.
- Secure developer workflows: rotate CI tokens regularly, use ephemeral short‑lived credentials, and adopt secret scanning in repos.
- Block known malicious artifacts and hosting domains in network and proxy controls — but validate each indicator against current telemetry to avoid blocking benign services.
- Run simulated phishing and malvertising awareness training that covers new lures (copy‑paste Terminal commands, fake AI installers, WhatsApp attachments).
Conclusion
Infostealers without borders represent an evolution of a familiar threat: the same fundamental motive — steal credentials and monetize access — but executed across platforms, languages, and ecosystems. Attackers have weaponized convenience and trust: a copy‑paste Terminal command, a cloud‑hosted DMG, or a hijacked WhatsApp session now serve as entry points. Defenders must respond in kind — by unifying telemetry across Windows, macOS, and Linux; by shifting from signature-first defenses to behavior and context; and by combining technical controls with targeted user friction and education.The practical takeaway is simple but urgent: treat macOS and Python workloads as first‑class attack surfaces, assume that trusted platforms can be abused, and prioritize controls that remove credential exposure (MFA, secret rotation, key protection) and that detect the minimal but telling artifacts of modern stealers (suspicious interpreter renames, living‑off‑the‑land command chains, transient archives followed by egress). The cost of inaction is immediate and concrete: account takeover, drained wallets, and the loss of developer and customer trust can happen in minutes once an infostealer slips past the front door.
Source: Microsoft Infostealers without borders: macOS, Python stealers, and platform abuse | Microsoft Security Blog