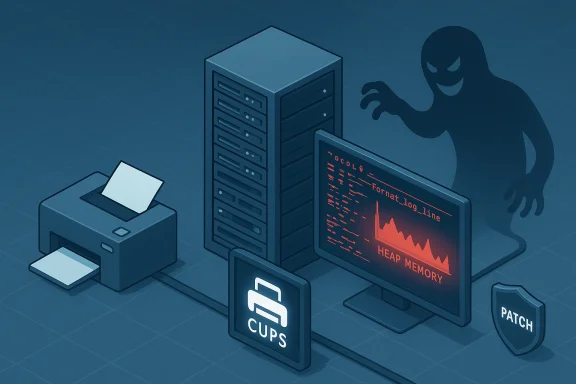
OpenPrinting's CUPS contained a heap buffer overflow that can be triggered when administrators run the daemon with logging set to DEBUG, allowing a remote attacker to repeatedly crash the printing service and, in some cases, sustain a full denial-of-service condition against printing resources.
CUPS (Common UNIX Printing System), maintained by the OpenPrinting project, is the de facto printing stack on most Linux distributions, many BSD flavors, and historically macOS systems. In mid‑2023 security researchers and vendor trackers documented a heap-based buffer overflow in the CUPS logging path — specifically inside the function named
Multiple independent vulnerability databases and vendor advisories describe the same technical root cause: an over‑write of heap memory when the logging subsystem builds a line that is longer than the buffer allocated for that entry. Because the flaw is reachable via network‑facing interfaces (CUPS typically listens on port 631) and does not require credentials if the server is exposed, it is classed as a remote denial‑of‑service (DoS) vulnerability with an availability impact only — the attacker crashes the service rather than exfiltrating data or gaining code execution in known public reports.
The vulnerable path:
At the heart of the issue is the
Because crashes require only crafted input and a reachable CUPS with
Flag any claims of privilege escalation or remote code execution as unverified unless accompanied by a public, peer‑reviewed exploit and vendor confirmation. Heap corruptions are complex and platform‑specific; a crash is a known outcome, while code execution is not established publicly for this specific CVE.
Two important caveats remain for defenders:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CUPS (Common UNIX Printing System), maintained by the OpenPrinting project, is the de facto printing stack on most Linux distributions, many BSD flavors, and historically macOS systems. In mid‑2023 security researchers and vendor trackers documented a heap-based buffer overflow in the CUPS logging path — specifically inside the function named format_log_line — that can be exercised when cupsd.conf has the LogLevel (or loglevel) set to debug. The vulnerability affects upstream CUPS releases through and including 2.4.2, and vendor advisories and CVE authorities assigned the identifier CVE-2023-32324 to the issue.Multiple independent vulnerability databases and vendor advisories describe the same technical root cause: an over‑write of heap memory when the logging subsystem builds a line that is longer than the buffer allocated for that entry. Because the flaw is reachable via network‑facing interfaces (CUPS typically listens on port 631) and does not require credentials if the server is exposed, it is classed as a remote denial‑of‑service (DoS) vulnerability with an availability impact only — the attacker crashes the service rather than exfiltrating data or gaining code execution in known public reports.
Why this matters: scale and attack surface
CUPS is almost everywhere—in data centers, desktop fleets, thin-client setups, print servers, and networked multifunction printers that embed Linux. That ubiquity turns any remotely exploitable CUPS bug into a high‑impact operational problem for IT teams responsible for availability and regulatory continuity.- Many organizations enable verbose or debug logging on purpose for troubleshooting or audit reasons. That single administrative choice materially alters exploitability.
- CUPS is often reachable from internal networks and sometimes inadvertently exposed to wider networks through misconfiguration, cloud images, or legacy print-sharing configurations.
- Print servers are shared infrastructure; a single exploited printer host can deny printing to many users and services, and repeated crashes can complicate recovery (dangling locks, corrupted job queues, or broken spooler state).
LogLevel debug — can convert a relatively innocuous code defect into a remotely exploitable reliability failure.Technical anatomy of CVE-2023-32324
The vulnerable path: format_log_line
At the heart of the issue is the format_log_line routine used by CUPS to assemble the textual representation of log entries when the daemon records events. When logging runs at DEBUG level, CUPS outputs verbose contextual information and may format potentially very long strings into the log buffer. In vulnerable releases the implementation did not sufficiently bound checks when copying or concatenating string pieces into the heap‑allocated log buffer. A specially crafted network request (for example, with overlong header fields or data that get placed into logable fields such as usernames, printer names, job attributes, or IP/DNS strings) can cause the formatter to write past the allocated chunk, clobber heap metadata, and trigger a crash or process termination.Trigger conditions
Two elements are required for reliable exploitation:- CUPS version: the upstream CUPS implementation in versions up to 2.4.2 contains the buggy
format_log_linebehavior. - Logging level: the
cupsd.confconfiguration must set logging atLogLevel debug(case-insensitive). Normal/default logging levels such asinfoorwarndo not produce the same long formatted lines and therefore are not broadly exploitable in the same way.
debug temporarily and forget to revert it—the vulnerability is particularly consequential.Impact profile
Based on public advisories and vulnerability databases, the primary and confirmed impact is Availability: an attacker can cause CUPS to crash, leading to denial of printing services. There are no confirmed widespread reports showing escalation to code execution or data corruption beyond process termination at time of disclosure; however, heap corruptions can be complex and may have distribution‑dependent outcomes, so cautious defenders should not assume only a clean crash in every environment.How attackers could weaponize this (attack scenarios)
Attackers do not need privileged access to make this bug effective. Below are representative attack scenarios defenders should treat as realistic.- Internal saboteur or lateral movement: An attacker who can reach the internal print server (common in compromised user workstations or jump hosts) can repeatedly send maliciously crafted IPP/HTTP requests to trigger the overflow while
LogLevelisdebug, causing persistent downtime. - Internet‑exposed print server: Organizations that have accidentally exposed CUPS to the internet (or that host print services in cloud networks without proper filtering) risk remote adversaries scanning for port 631 and triggering the crash condition.
- Automated DoS: An attacker can script a lightweight, high‑frequency request pattern that forces repeated crashes or prevents the service from recovering reliably (for example, by racing restarts or consuming spooler resources).
Verification and cross‑checks (what the trackers report)
Multiple independent vulnerability trackers and vendor advisories corroborate the core facts: a heap buffer overflow informat_log_line, affected CUPS versions through 2.4.2, and exploitation requiring LogLevel debug.- National vulnerability databases and major OS vendors annotated the CVE entry and issued fixes in downstream packages for their distributions.
- Some aggregation services report a CVSS v3 score in the mid‑5 range (medium), while others rate it higher (7.x). This variance arises from differing interpretations of attack complexity and control requirements (e.g., network reachability versus privileges). Defenders should consult their vendor or distribution advisories for the canonical severity and fixed package versions for their platform.
Detection: how to spot vulnerable systems and exploitation attempts
Quick inventory checks
Run these checks on Linux hosts (commands are examples; adapt to your distro and environment):- Check installed CUPS version:
cupsd -v
or
Code:rpm -q cups # RHEL-based systems dpkg -l cups # Debian/Ubuntu systems - Check the configuration for
LogLevel:
grep -i 'LogLevel' /etc/cups/cupsd.conf || grep -i 'loglevel' /etc/cups/cupsd.conf - Check if CUPS is listening on a network interface:
ss -ltnp | grep 631
LogLevel set to debug are the highest‑priority for remediation.Indicators of attempted exploitation
- Repeated crashes of
cupsdin system logs (journalctl logs, /var/log/messages, or syslog) with stack traces or "segfault" messages near logging routines. - Core dumps referencing C or C++ functions associated with logging or string formatting.
- Rapid restarts or supervisor churn of the cups service.
- Unexpected network connections to port 631 from untrusted IPs; spikes in traffic targeting IPP/HTTP endpoints.
Mitigation and remediation: immediate and long‑term steps
Immediate (emergency) actions — do these first
- Reduce logging to safe levels: If you cannot patch immediately, change
LogLevelfromdebugtoinfoorwarn(or comment out theLogLevelline to use defaults). Then restart thecupsservice. This eliminates the trigger condition and is a low‑impact change in most cases.
Code:sudo sed -i 's/^[ \t]*LogLevel[ \t].*/LogLevel info/i' /etc/cups/cupsd.conf sudo systemctl restart cups - Restrict network exposure: Block access to TCP/UDP port 631 except from trusted hosts and networks. Use firewalls (iptables/nftables/ufw/host firewall rules, or cloud security groups) to limit exposure.
- Isolate compromised hosts: If you detect exploitation, isolate the server and preserve forensic artifacts (logs, core dumps) for analysis.
Patching and long‑term remediation
- Apply vendor patches: Upgrade CUPS to a version that contains the fix; vendors issued distribution package updates after the CVE. Use your platform's package manager (apt, yum/dnf, zypper, pacman, etc.) and confirm that the installed package version is listed as fixed by your vendor advisory.
- Restart and validate: After upgrading, restart
cupsand confirm the service is stable under normal traffic. ConfirmLogLevelis as intended. - Harden configuration:
- Avoid leaving
LogLevel debugenabled in production. Use it only for short troubleshooting windows. - Disable remote administration unless necessary.
- Use access control lists inside
cupsd.confto limit who can submit jobs or query printers. - Add process constraints: Apply
systemdlimits (Restart= on failures, but avoid aggressive restart loops), and consider sandboxing with AppArmor or SELinux policies and limiting the privileges of thecupsdprocess. - Monitoring and alerting: Add checks that alert on unexpected
cupsdcrash counts, high connection rates on port 631, or configuration changes to/etc/cups/cupsd.conf.
Practical recovery considerations
- CUPS job queues and spool directories can be in inconsistent states after crashes. Verify spooler health and remove problematic queue files only after diagnosis.
- If you must keep
LogLevel debugfor an extended troubleshooting window, do it on an isolated host or for a controlled time window with network restrictions and close monitoring. - Test patch rollouts in staged environments before wide production deployment to ensure distribution package backports play nicely with local printer drivers and filters.
Proof‑of‑concepts, exploit availability, and public risk
Public reporting around CVE-2023-32324 documents the vulnerability, but as of the last public ground‑truth checks there are no widely‑distributed, verified proof‑of‑concept (PoC) exploit kits that demonstrably enable remote code execution in the wild. Several vulnerability aggregators and advisories discuss exploitability and supply technical reproduction hints, but defenders should assume that simple crash vectors are trivial to craft given the publicly available technical description.Because crashes require only crafted input and a reachable CUPS with
LogLevel debug, the risk of denial‑of‑service exploitation is tangible even without a polished PoC. Attackers need not publish polished exploit code to cause disruption; script kiddies and automated scanners can and will reproduce a crash with minimal effort once the trigger fields and formatting behavior are known.Flag any claims of privilege escalation or remote code execution as unverified unless accompanied by a public, peer‑reviewed exploit and vendor confirmation. Heap corruptions are complex and platform‑specific; a crash is a known outcome, while code execution is not established publicly for this specific CVE.
Risk assessment and prioritization
When prioritizing work, use the following decision matrix:- High priority (patch immediately): servers with CUPS <= 2.4.2 that are network‑reachable beyond a tightly controlled management network, or any print server running
LogLevel debug. - Medium priority: desktops or devices with CUPS <= 2.4.2 that are only reachable from local, authenticated networks but are part of shared infrastructure.
- Lower priority: systems that already use CUPS versions newer than 2.4.2, or systems where
debuglogging is not enabled and network access is fully restricted.
LogLevel debug to be enabled to be trivially exploitable, systems with conservative logging settings are less likely to be impacted. Nonetheless, because logging configuration can be changed inadvertently or temporarily during troubleshooting, assume any system lacking an up‑to‑date vendor patch and with CUPS present is potentially at risk.Lessons for system administrators and architects
- Treat logging level changes as configuration changes with security implications. Make
LogLevel debuga temporary, documented, and time‑boxed action. - Maintain an asset inventory that includes print servers and their network exposure. Print systems are often overlooked in patch cycles.
- Use host firewalls or segmentation to reduce the blast radius of services that don’t need to be internet‑reachable.
- Subscribe to vendor security advisories for your distribution and apply security updates for utility components like CUPS promptly—these are common, shared libraries and services that do not receive attention until an incident occurs.
Timeline and vendor responses (concise)
- The vulnerability was publicly assigned CVE‑2023‑32324 and documented in June 2023.
- Distribution vendors (e.g., mainstream Linux distributions) published security advisories and backported fixes into their CUPS packages in the months following disclosure.
- Advisories converged on the same mitigation advice: apply vendor updates and avoid
LogLevel debugon production systems.
Final recommendations — checklist for immediate action
- Inventory hosts running
cupsand note versions. - If
cupsis <= 2.4.2: - If you cannot patch immediately, set
LogLeveltoinfoor higher and restart the service. - Restrict port 631 to trusted networks.
- Plan and apply vendor-recommended package updates at the earliest maintenance window.
- Implement monitoring to detect
cupsdcrashes, unusual port 631 traffic, and configuration changes to/etc/cups/cupsd.conf. - Harden service context with AppArmor/SELinux policies and minimal privilege runtime patterns.
Closing analysis: risks, strengths, and open questions
CVE‑2023‑32324 is a textbook demonstration that simple configuration choices can drastically alter exposure to defects in foundational services. The vulnerability’s strengths, from the defender perspective, are that it is narrowly scoped (log formatting) and that an obvious, pragmatic mitigation exists (disabledebug logging and patch). The risks lie in its ubiquity and triviality: many environments temporarily enable verbose logging, administrators forget to revert changes, and print servers are frequently reachable from multiple network segments.Two important caveats remain for defenders:
- Heap corruptions can produce diverse outcomes on different platforms. Treat any heap‑overflow vulnerability as potentially more serious than a mere crash; prioritize fixes and validation.
- Public severity scores vary; do not rely on a single CVSS number. Base operational priority on exposure and configuration specifics in your environment.
LogLevel debug, and deploy vendor fixes. That combination reduces both the likelihood and impact of exploitation and restores resilience to a service that, while often overlooked, is central to daily business operations.Source: MSRC Security Update Guide - Microsoft Security Response Center