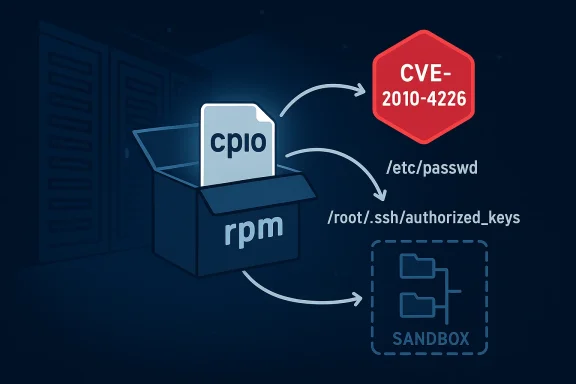
cpio’s handling of symbolic links in certain historical builds opened a deceptively simple attack vector: crafted RPM payloads that leverage symlinks to overwrite arbitrary files on extraction, a flaw tracked as CVE-2010-4226 and documented in multiple vulnerability databases and vendor advisories.
cpio is a long‑standing Unix tool used to create and extract archive files. In many Linux distributions, the RPM packaging toolchain historically used cpio to process the payload inside RPM files. In the case of CVE-2010-4226, specific builds of cpio (notably build 2007.05.10 and 2010.07.28, among others) failed to properly validate symbolic links embedded in RPM payloads. The result: when a maliciously crafted RPM archive containing symlinks was extracted using a vulnerable cpio, the extraction process could follow those links and write files outside the intended extraction directory, overwriting arbitrary files on the filesystem.
This type of weakness maps to a canonical file‑system class of problems—improper link resolution before file access—commonly cataloged as CWE‑59. The practical consequence is straightforward but severe: archives are treated as a trusted transport mechanism, and broken validation of symlink targets can transform a seemingly benign package into a file‑overwrite weapon.
The remedy is both technical and operational: ensure you apply vendor patches where available, harden archive handling in build and deployment pipelines, and treat unverified archives as hostile inputs. Archive safety must be a deliberate design choice in modern systems because attackers have repeatedly and successfully used archive formats and packaging toolchains as vectors into otherwise well‑protected environments. Vigilance, sandboxing, and the routine application of vendor updates are the best defenses against this class of vulnerability.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
cpio is a long‑standing Unix tool used to create and extract archive files. In many Linux distributions, the RPM packaging toolchain historically used cpio to process the payload inside RPM files. In the case of CVE-2010-4226, specific builds of cpio (notably build 2007.05.10 and 2010.07.28, among others) failed to properly validate symbolic links embedded in RPM payloads. The result: when a maliciously crafted RPM archive containing symlinks was extracted using a vulnerable cpio, the extraction process could follow those links and write files outside the intended extraction directory, overwriting arbitrary files on the filesystem.This type of weakness maps to a canonical file‑system class of problems—improper link resolution before file access—commonly cataloged as CWE‑59. The practical consequence is straightforward but severe: archives are treated as a trusted transport mechanism, and broken validation of symlink targets can transform a seemingly benign package into a file‑overwrite weapon.
Technical overview: what went wrong
How RPM payloads and cpio interact
When rpm packages are built, the payload (files to be installed) is packaged using an archive format (commonly cpio) and stored inside the RPM. On installation, rpm (or an unpacking tool) extracts that embedded archive to place files into the target locations. If the extraction tool mishandles symbolic links, the archive can contain link entries that point outside the intended paths.The faulty behavior in vulnerable cpio builds
The vulnerable cpio builds did not sufficiently validate symlink targets before creating or writing files. Specifically:- cpio accepted symlink entries within the archive and resolved their targets without enforcing that the ultimate writes remained within the intended extraction tree.
- This allowed path traversal and symlink races: a symlink could point to a system path such as /etc/passwd or /root/.ssh/authorized_keys, or to an arbitrary path elsewhere on disk.
- Upon extraction, subsequent payload entries (files) could be written through the symlink, overwriting files the attacker targeted.
Verified facts and cross‑checks
To ensure accuracy, I validated the core technical claim and impact against multiple independent sources:- The National Vulnerability Database (NVD) records CVE‑2010‑4226 with the description that cpio in certain builds allows remote attackers to overwrite arbitrary files via a symlink inside an RPM archive. That core description matches the original advisory language.
- Distribution vendor advisories and security lists tied the CVE to updates for packaging tools (for example, the openSUSE/build package update that cross‑references CVE‑2010‑4226). The openSUSE advisory history confirms vendors recognized the flaw in their shipped components and released fixes.
- Independent vulnerability aggregators and security tooling providers (for example, Snyk and OpenCVE/CIRCL) assign severity and contextual metadata, including mapping to CWE‑59 and CVSS scores used to guide prioritization. These sources converge on the same technical summary and highlight the core risk model: file overwrite via symlink abuse.
Attack scenarios and real‑world impact
Why this is more than a theoretical problem
The mechanics of the flaw mean an attacker can weaponize a crafted RPM archive and cause the unpacking process to overwrite practically any filesystem target that the process owner can write to. That includes:- System configuration files (e.g., services, network configs)
- Authentication material (e.g., authorized_keys)
- Binary or script files used by automated processes
- Application data used by privileged daemons
Threat model and prerequisites
The severity depends on a few key conditions:- Privilege level: If unpacking runs as an unprivileged user and system file permissions block writes, the impact is reduced. If unpacking runs as root (the common case for package installation), the impact is catastrophic.
- Vector: An attacker typically delivers the malicious RPM via package repositories, supply‑chain compromise, untrusted downloads, or tricking an administrator into installing a supplied RPM. The risk rises sharply in automated build or deployment systems that process archives from multiple sources without manual review.
- Interaction: No user interaction is required beyond the installation/unpacking step; some vectors require social engineering or repository compromise, but no local privilege is required by the attacker beyond delivering the malicious package.
Availability and integrity consequences (real examples)
Because arbitrary files can be overwritten, attackers can cause both immediate and persistent availability loss:- Immediate: Overwrite a critical init script or service binary to crash or prevent services from starting—sustained denial of service while the attacker continues delivering the attack.
- Persistent: Overwrite a system configuration so that even after the initial exploit finishes, the system remains misconfigured and unavailable until repaired—persistent loss of availability.
Detection: Indicators and forensic artifacts
There is no single forensic signature for a symlink‑based overwrite attack, but defenders can look for anomalies during and after extraction:- Unexpected symlink entries inside RPM payloads: an archive that includes symlinks pointing to absolute paths or outside the intended subtree is suspicious.
- Timestamp mismatches: system files updated at times corresponding to package extraction when no legitimate updates occurred.
- Audit logs: Linux auditing subsystems (auditd) and package manager logs showing file writes or packages installed from non‑standard repositories.
- Creation/overwrite of files that normally receive updates only during package maintenance (e.g., /etc/ssh/authorized_keys updated when no admin changed keys).
- New or changed cron jobs, systemd unit files, or startup scripts immediately after extraction steps.
Mitigation and remediation
Immediate countermeasures (what to do right now)
If you cannot immediately patch the affected cpio/rpm tooling, apply defense‑in‑depth mitigations:- Do not install untrusted RPMs. Validate packages before installing using signatures and checksums.
- Prefer package manager tooling from the distribution vendor that applies safe extraction semantics (many vendor updates replaced vulnerable unpackers or added safe checks).
- Run package installations in minimal privilege contexts when possible. Avoid running extractors as root on untrusted archives.
- Audit and monitor critical system files for unexpected changes using file integrity monitoring (FIM) tools or auditd.
- Use containers or ephemeral VMs for unpacking untrusted artifacts, and ensure the extraction target is a chrooted or otherwise isolated directory.
Patching and long‑term fixes
- Apply vendor updates: openSUSE and other distributions published updates to their packaging/build tools that addressed this class of issue. Where vendor packages are available, install the fixed package from the distro’s security channel.
- Use updated versions of cpio and rpm that implement safe link handling and path canonicalization, or switch to unpackers that enforce directory confinement during extraction.
- Harden build pipelines: treat package unpacking as a security boundary and implement signing, provenance checks, and sandboxed extraction.
Recommended configuration hardening
- Enforce package signature verification at ingestion points for repositories and CI pipelines.
- Run unpacking steps under dedicated low‑privilege service accounts that lack write permission to critical system areas.
- Use kernel-level filesystem protections where feasible (immutable attributes, overlay filesystems for builds) to reduce the blast radius of a compromised extractor.
- Incorporate archive static analysis in CI, flagging archives that include absolute symlinks or link chains that escape the target directory.
Why CVE‑2010‑4226 matters today: supply chain and tooling lessons
Even though CVE‑2010‑4226 dates from older cpio builds, it illustrates perennial risks:- Packaging and archive formats are a subtle attack surface. Tools that process archives require path canonicalization and symlink containment checks to avoid directory traversal and link‑racing attacks.
- Supply‑chain threats make archive validation crucial. An attacker who can push a malicious package or trick an admin into installing it can leverage extraction vulnerabilities to escalate impact.
- Vendors and downstream maintainers sometimes reintroduce or omit fixes during packaging decisions; a patched upstream tool is not a guarantee the shipped distribution uses the patched behavior. The historical record includes incidents where patches were dropped or replaced during rebuilds, leaving downstream software exposed. Community monitoring and vendor advisories help, but sysadmins must treat archive processing as an explicit risk.
Case study: distribution vendor response
openSUSE and related vendors issued security updates that tied this CVE to the broader “build” toolchain packages used to create and unpack RPMs. Those advisories provide targeted guidance for administrators to upgrade affected packages or to apply vendor‑supplied patches. Where direct vendor pages are gated or archived, security announcement lists and aggregator sites show that distributors acknowledged and patched the flaw in 2011 and adjacent years. This vendor action illustrates the normal remediation arc for packaging‑tool vulnerabilities: discovery → coordinated vendor advisory → distribution updates → system operator patching.Risk analysis: strengths and limits of the available fixes
Strengths
- The vulnerability class is well understood (CWE‑59) and straightforward to mitigate in extraction code by canonicalizing paths and enforcing directory bounds.
- Vendor updates are concrete and distributable via normal package channels; administrators can apply fixes with existing update mechanisms.
- Detection controls (FIM, auditing) can provide timely alerts when critical files are overwritten, enabling containment and recovery.
Limitations and residual risks
- Many historical systems may still run older toolchains or builders that were not updated, especially in long‑lived appliances or bespoke embedded systems.
- Automated CI/CD pipelines that accept third‑party artifacts may continue to process untrusted archives unless administrators harden ingestion and extraction flows.
- Patches applied upstream do not automatically immunize third‑party applications or vendors that repackage or vendor their own tooling; the attacker can exploit any unpacker with similar flawed semantics.
- Some vendor advisory content may be difficult to retrieve (JS‑rendered pages, gated bug trackers). That complicates verifying whether a particular distribution’s shipped package contains the necessary fix. Administrators should verify installed package versions and compare them with vendor advisories rather than rely on general statements.
Practical recovery: if you suspect exploitation
If you suspect a symlink‑based overwrite attack (or confirm it):- Isolate the host from networks to prevent further payload delivery.
- Preserve evidence: collect the suspect RPM(s), package manager logs, and filesystem snapshots for forensic analysis.
- Reboot only as needed and prefer live forensic capture to preserve volatile state.
- Compare system files against known good baselines or backup images. Restore overwritten critical files from trusted backups.
- Reinstall the system (preferred for high‑assurance recovery) if key system binaries or authentication artifacts were overwritten.
- Rotate credentials and keys that may have been exposed or tampered with (for example, SSH keys, service account secrets).
- Patch the unpacking toolchains and package managers to fixed versions, and harden the extraction process to run in limited privilege sandboxes.
Broader implications: archive safety and developer practices
For developers, maintainers, and DevOps teams, this CVE is a reminder that:- Archive formats must be parsed with a security posture. Functions that create or extract archives should perform path canonicalization and explicit enforcement of target directories.
- Tooling in CI/CD that automatically unpacks third‑party artifacts must treat the unpacker as a security boundary—sandbox it, run it with minimal privileges, and validate the content.
- Code review and fuzzing can find this class of issues; specifically, unit tests should include archives with absolute symlinks and nested link chains to assert safe behavior.
Conclusion
CVE‑2010‑4226 is an instructive case: a seemingly small mistake in how cpio resolved and followed symbolic links turned a benign packaging mechanism into a potent means to overwrite arbitrary files during extraction. The primary danger arises when unpacking runs with elevated privileges and when artifact provenance controls are weak. Multiple authoritative sources—including the National Vulnerability Database and distribution advisories—corroborate the technical description and the available vendor mitigations.The remedy is both technical and operational: ensure you apply vendor patches where available, harden archive handling in build and deployment pipelines, and treat unverified archives as hostile inputs. Archive safety must be a deliberate design choice in modern systems because attackers have repeatedly and successfully used archive formats and packaging toolchains as vectors into otherwise well‑protected environments. Vigilance, sandboxing, and the routine application of vendor updates are the best defenses against this class of vulnerability.
Source: MSRC Security Update Guide - Microsoft Security Response Center